What is Bridge Relay?
Learn what a bridge relay is, how it moves cross-chain messages and proofs, why bridges need it, and how relay trust assumptions shape security.
Introduction
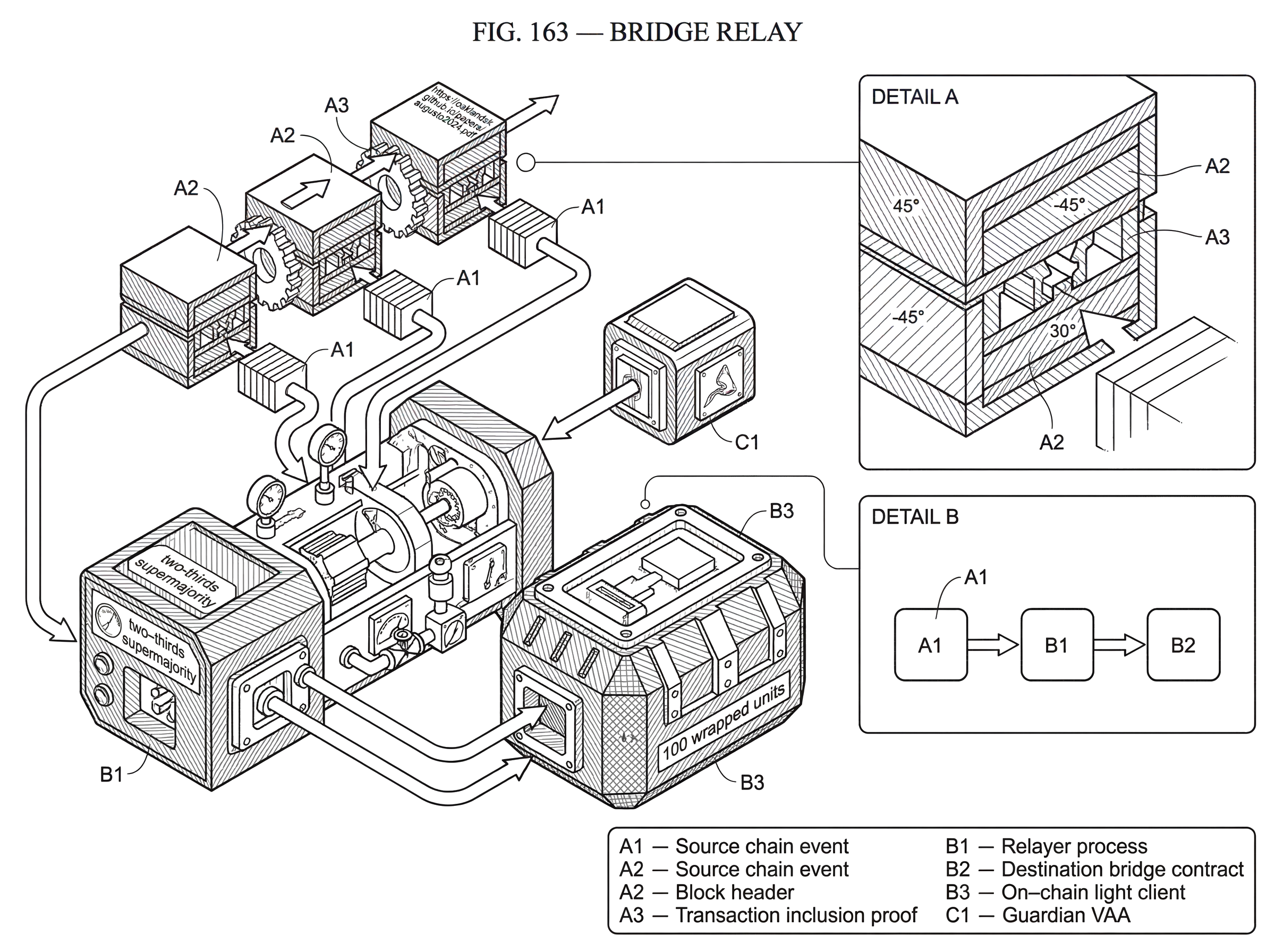
bridge relay is the off-chain process that carries messages, proofs, or attestations from one blockchain to another so a bridge can actually function. That sounds almost trivial at first: if two chains can verify each other, why is a relay needed at all? The answer is that verification and transport are different jobs. A chain may know how to check a proof from another chain, but it usually does not reach out over the network, scan foreign blocks, assemble the right data, and pay to submit that data on its own.
This is why bridge design often has a surprising split. The security logic may live on-chain, in light clients, validators, endpoints, or verification contracts. But the liveness logic (noticing that something happened on chain A and causing chain B to process it) often lives off-chain in a relayer. If no relayer shows up, many bridges remain safe in a narrow sense, but they stop being useful.
That distinction is the key to understanding the topic. A bridge relay is not necessarily the thing that decides whether a cross-chain message is valid. In many designs, it is the thing that delivers the evidence needed for some other component to make that decision. In other designs, especially attestation-based bridges, the relay role blends into a committee or worker network that both observes events and produces signed approval objects. Either way, the relay sits at the boundary between chains and turns a possible cross-chain action into an actual one.
Why do bridges need a relayer to move messages between chains?
A blockchain is very good at reaching consensus about its own state. It is not naturally good at learning new facts about some other blockchain. Even when a destination chain has a contract or module capable of verifying foreign headers or signatures, someone still has to provide the raw material: the relevant block header, transaction proof, attestation, or message payload.
That is the relay problem. Suppose a user locks tokens on chain A to mint or unlock corresponding tokens on chain B. Chain B should only act if the lock event on chain A really happened and is final enough to trust. But chain B does not continuously poll chain A, index its events, build inclusion proofs, and submit transactions to itself. A relay fills that gap. It watches chain A, identifies bridge-relevant events, packages whatever the bridge mechanism requires, and transmits that package to chain B.
This is why relays are best understood as a form of delivery infrastructure rather than merely “middleware.” Their central invariant is simple: the destination chain should receive enough information to decide whether to accept a cross-chain event. The exact information varies by bridge architecture. In a light-client-style system, the relayer may submit headers and Merkle proofs. In an oracle-plus-relayer design, one service may provide block headers while another provides transaction proofs. In a committee bridge, the relayer may deliver a signed attestation like a multisignature message approval.
The important consequence is that relay is a role, not a single universal implementation. Different ecosystems give it different names and split the work differently, but the recurring mechanism is the same: observe, package, submit.
How does a bridge relay work: observe, package, and submit evidence?
At the most abstract level, a bridge relay does three things.
First, it observes source-chain state. That usually means listening for specific contract events, module state changes, packet commitments, or emitted messages. In IBC, relayers scan chain state for packets, acknowledgements, and client updates. In Wormhole, Guardians observe on-chain messages and sign them once enough of them agree. In LayerZero’s original oracle-plus-relayer model, the relayer fetches a proof for a specific source-chain transaction.
Second, it packages the relevant evidence into the format expected by the destination chain. That packaging step is where bridge architectures differ most. The payload may be a raw message, a Merkle inclusion proof, a block header, a validator-signed attestation, or some combination. This is not cosmetic encoding work. The package determines what the destination chain can verify and therefore what trust assumptions the bridge is making.
Third, it submits the package to the destination chain in an executable transaction. This means the relayer also pays fees, chooses timing, handles retries, and deals with operational failures such as RPC outages or reorg-sensitive timing. In many real deployments, this third step is where “the bridge is down” actually shows up: not because verification broke, but because no healthy relayer is getting valid messages on-chain.
A concrete example makes the mechanism clearer. Imagine an application on chain A sends a cross-chain instruction to chain B saying, in effect, “credit this user with 100 wrapped units.” The bridge contract on chain A emits an event or stores a packet commitment. A relayer notices this event, fetches the proof that the event or packet is included in finalized chain A state, and creates a transaction on chain B containing the message and proof. Chain B’s bridge contract checks that the proof matches a header or attestation it trusts. If the check passes and the message has not already been processed, chain B executes the credit. The relayer did not decide that the transfer was legitimate; it delivered the evidence that allowed chain B to decide.
Why are relayers implemented off‑chain instead of inside blockchains?
It is natural to ask why a relay is usually off-chain rather than built directly into the consensus protocol of each chain. The first reason is architectural. Blockchains are deliberately narrow machines: they execute deterministic state transitions on local data that validators can reproduce. Continuously reaching into another chain’s networking layer, parsing its blocks, and dynamically fetching proofs would break that model or make it much heavier.
The second reason is economic. Submitting every possible cross-chain update on-chain would be expensive, and not every update matters to every application. An off-chain relayer can choose which messages to forward, batch work, wait for stronger finality, retry failed submissions, and optimize for cost.
The third reason is portability. Systems like IBC are designed as abstractions that many ledgers can implement. The chain only needs the verification logic and state machine rules. The actual transport can be provided by external processes. Cosmos documentation is explicit here: relayers are the “physical” connection layer of IBC, and chains rely on off-chain relayers to communicate. That makes relayers operationally replaceable and allows many relayers to serve the same channels, but it also means cross-chain liveness depends on someone running them.
This tradeoff is easy to miss. Off-chain relaying usually improves modularity but moves liveness into operations. A bridge may remain cryptographically sound while becoming practically unusable because the relayer fleet is poorly run, under-incentivized, censored, or simply offline.
How do relayers operate in light‑client bridges (for example, IBC)?
| Responsibility | Delivered | Who verifies | Operator concern | Failure symptom |
|---|---|---|---|---|
| Observe | event or packet detection | destination light client | RPC and index reliability | missed or delayed relays |
| Package | headers and inclusion proofs | on-chain light client | correct proof format | verification rejections |
| Submit | on-chain transaction | bridge contract execution | fees, timing, retries | stuck or failed execution |
The cleanest place to see the relay role is a Light Client Bridge. Here the destination chain runs a light client of the source chain. That light client can verify headers and, from those headers, verify proofs about specific state or events. In principle, this is close to an ideal trust model because the destination chain checks source-chain facts directly rather than trusting a committee to summarize them.
But a light client does not eliminate the relay. It changes what the relay must deliver. Instead of saying “trust me, this event happened,” the relayer says “here is the header update and here is the proof; verify it yourself.”
IBC is the best-known example. The protocol separates transport-and-authentication infrastructure from application behavior. Its transport layer establishes secure connections and authenticates packets, while application modules define what those packets mean, such as token transfers or interchain accounts. The relayer sits outside both chains, monitoring open paths, submitting client updates so each chain can track the counterparty’s consensus state, and relaying packets, acknowledgements, and timeout information. Each side uses the light client of the other chain to verify incoming messages quickly.
That yields an important mental model: in a light-client bridge, the relayer is untrusted for correctness but trusted for availability. If it submits a false proof, the on-chain light client should reject it. If it submits nothing, the protocol cannot progress. This is a much narrower trust role than “trusted validator,” but it is still a real dependency.
A practical consequence is that relayers often do more than packet forwarding. In IBC tooling such as rly or Hermes, the relayer can also create clients, connections, and channels; the objects that make communication possible in the first place. So the relay role spans both ongoing message delivery and some of the setup workflow. Operators also configure which channels to relay, what RPC endpoints to use, how keys are managed, and how telemetry is exposed. The mechanism is cryptographic; the system is operational.
How do oracle‑plus‑relayer architectures split verification work?
Some bridge systems split verification inputs across multiple off-chain actors. LayerZero’s original design is a good illustration. There, the destination chain receives two complementary pieces of evidence: an Oracle provides the block header, and a Relayer provides the proof for the specific source transaction. The destination-side validator checks that the proof matches the header.
The point of this split is not redundancy in the everyday engineering sense. It is a security decomposition. If the header source and the proof source are independent and non-colluding, then neither one alone can forge a valid message. The relayer cannot invent a transaction proof that matches an unrelated header, and the oracle cannot make an absent transaction appear in a proof it does not control.
This gives the relayer a more specific job than in a generic message courier model. It fetches proof(t) for some source transaction t, stores or prepares it off-chain, and later delivers that proof to the destination when the matching header is available. In this architecture, “bridge relay” means not merely forwarding payload bytes but supplying the inclusion evidence that binds a payload to real source-chain execution.
The limitation is equally clear. The security argument depends on the independence of the oracle and relayer. That independence may be assumed socially or organizationally, but the protocol may not be able to enforce it. So the relay’s trust profile is no longer only about liveness. It becomes part of a paired trust assumption: validity holds unless the verification actors collude.
What role do relayers play with attestation/guardian‑based bridges (e.g., Wormhole)?
Not every bridge asks the destination chain to verify source-chain state directly. Many systems instead rely on an external validator, guardian, or committee network that observes source-chain events and signs an attestation saying, effectively, “this message is approved.” The destination chain verifies the committee signature threshold rather than a native source-chain proof.
Wormhole is a clear example. Its Guardians observe messages emitted by contracts, and once a two-thirds supermajority agrees, they produce a VAA, or Verifiable Action Approval. A VAA is Wormhole’s core cross-chain messaging object: a deterministically derived body plus guardian signatures in the header. Since a VAA has no inherent destination, any chain’s core contract can verify it as authentic; if a particular destination action is intended, relayers are responsible for delivering the VAA to that chain.
This changes the relay’s job again. The heavy verification work has already been compressed into the attestation. The relay now primarily moves the signed object to where it needs to be consumed. In some systems the committee and the relay are operationally distinct; in others they are tightly coupled. But the underlying logic remains the same: the destination acts because it trusts the attestation mechanism.
The tradeoff is straightforward. Attestation-based bridges are often easier to deploy across heterogeneous chains than full light-client verification, because verifying a committee signature threshold is simpler than embedding many different consensus verifiers on-chain. But this convenience concentrates risk in the attestation network and its key management. Research surveying bridge incidents found a large share of stolen funds came from designs secured by intermediary permissioned networks with weak cryptographic key operations. The Ronin breach is the cautionary example: attackers obtained control of enough validator keys to forge withdrawals. That was not a relay bug in the narrow software sense. It was a failure of the trust structure that the relay system depended on.
How do relaying, verification, and execution differ in cross‑chain flows?
A common source of confusion is that “relay” can refer to several adjacent actions that happen in sequence. It helps to separate three layers.
The first layer is observation and evidence movement: seeing an event on chain A and delivering proof or attestation to chain B. That is the core relay role.
The second layer is verification: checking headers, proofs, signatures, or committee attestations. In a light-client system, this is mostly on-chain verification logic. In a committee bridge, it is signature-threshold verification against an accepted guardian or validator set.
The third layer is execution: after a message is accepted as valid, actually calling the destination application logic. Some protocols separate this explicitly. LayerZero documentation, for example, distinguishes verification services and execution workers, and emphasizes permissionless execution once a message is verified. Wormhole also has an executor framework separate from Guardian signing.
These distinctions matter because they create different failure modes. A message can be correctly relayed but fail verification. It can be verified but not executed because no one pays gas or triggers the final call. Or it can be observed but never relayed at all. If someone says “the bridge relayer failed,” the precise question is: which stage stopped making progress?
What use cases do relayers enable beyond simple token transfers?
The most visible use is token bridging, but that is only the simplest case. A relay can carry arbitrary byte-encoded messages in systems that support general message passing. In IBC, the same transport can support fungible token transfers, NFTs, interchain accounts, and other application-layer behaviors because the relay is moving authenticated packets, not just “coin transfer” instructions. LayerZero presents a similar general-purpose messaging model for omnichain applications. Wormhole VAAs can likewise represent more than asset movement.
This broader view matters because it explains why bridge relays are infrastructure rather than niche middleware for wrapped assets. Once a system can authenticate cross-chain messages, applications can use relays for remote execution, state synchronization, governance signaling, account control, liquidity orchestration, or query-response patterns. The relay is the courier for cross-chain intent.
At the same time, the application changes what the relay must optimize for. Asset transfers care intensely about replay protection, finality assumptions, and custody correctness. Interchain accounts care about ordered delivery and deterministic execution. General messaging systems care about payload flexibility and destination execution semantics. The relay role is stable, but the operational requirements around it shift with what is being carried.
What trust and finality assumptions affect relay security and liveness?
The most important thing a smart reader might misunderstand is this: a bridge relay is not inherently trustless, and it is not inherently centralized either. Its trust properties come from the verification architecture around it.
If the destination chain independently verifies source-chain proofs with a correct light client, then the relayer mainly affects liveness. If the destination chain accepts signatures from a fixed committee, then the relay inherits the security of that committee. If validity depends on two off-chain actors being independent, as in oracle-plus-relayer designs, then the relay is part of a non-collusion assumption. So asking “can I trust the relayer?” is too coarse. The better question is: what bad outcome becomes possible if the relayer lies, goes offline, censors, or colludes?
Finality assumptions also matter. A relay that forwards messages from a chain before those messages are economically or cryptographically final can create inconsistencies. Wormhole’s VAA documentation notes that reorgs can lead to different VAAs for what appears to be the same message identifier until finality is reached. This is not a Wormhole-specific oddity; it is a generic cross-chain problem. A relay must choose when an observed source event is stable enough to act on.
Operational assumptions matter just as much as protocol assumptions. Relayers need RPC access, keys, monitoring, retry logic, fee funding, and often telemetry. Cosmos relayer tooling includes channel filters, configuration management, and production guidance such as disabling debug servers. Hermes exposes Prometheus metrics. OpenZeppelin’s relayer tooling emphasizes monitoring, automation, access control, and service status because the practical problem is not only “can this message be verified?” but also “will my system keep delivering transactions reliably and safely?”
Finally, there is the censorship and incentives question. Many protocols allow multiple relayers to serve the same path or destination, which improves redundancy. IBC explicitly allows many relayers to serve channels. But permissionless participation does not by itself ensure that someone is economically motivated to relay every message promptly. Fee markets, application subsidies, or vertically integrated operators often fill that gap in practice.
How do relay roles differ across IBC, LayerZero, Wormhole, and XCM?
| Model | Relay delivers | Trust assumption | Best for | Main risk |
|---|---|---|---|---|
| Light-client | headers and inclusion proofs | on-chain verification; relay for liveness | high-integrity transfers | liveness dependency |
| Oracle + Relayer | transaction proofs | non-collusion with oracle | lower verifier cost | oracle‑relayer collusion |
| Attestation (committee) | signed attestations | committee key security | heterogeneous chains | key compromise |
| IBC / XCM | authenticated packets and client updates | on-chain light clients verify | general-purpose messaging | operational liveness |
Looking across ecosystems helps isolate the core idea from local terminology. In IBC, the relayer monitors packet commitments and client states and submits protocol messages so on-chain light clients can verify them. In LayerZero’s original architecture, the relayer fetches transaction proofs while a separate oracle supplies headers. In Wormhole, a relayer transports signed VAAs produced by Guardians to the destination chain for verification and execution. In XCM-based systems, the format for cross-consensus messaging is defined separately from any single universal relay protocol, which means transport and relay designs are implementation-specific even though the message semantics are standardized.
These are not superficial differences. They show that “bridge relay” is best defined functionally: the agent that causes authenticated cross-chain information to move from source context to destination context. Sometimes the authentication is native proof verification. Sometimes it is a committee attestation. Sometimes the work is split among multiple off-chain services. But without the relay layer, interoperability remains a specification rather than a live system.
What are the main security, correctness, and availability risks of relayers?
| Risk | Affects | Typical cause | Mitigation |
|---|---|---|---|
| Key compromise | fund withdrawals | poor key management | multisig or threshold keys |
| Proof mishandling | message integrity | incorrect finality handling | validation tests and retries |
| Relayer downtime | cross-chain liveness | unpaid fees or outages | redundant relayers; fee markets |
| Governance centralization | bridge trust boundary | narrow operator control | transparent governance; decentralization |
Because relayers sit between chains, they collect several kinds of risk in one place.
There is security risk when relayers hold keys, sign attestations, or operate inside validator or guardian networks. The Ronin incident shows what happens when bridge operation depends on a small quorum whose key security and organizational boundaries are weaker than assumed.
There is correctness risk when relayers mishandle proofs, target the wrong finality threshold, fail to respect ordering, or interact incorrectly with destination verification logic. Even if funds are not stolen, a relay bug can cause stuck messages, duplicate submissions, or failed execution.
There is availability risk because many cross-chain systems depend on off-chain processes for liveness. A healthy light client on-chain does nothing if no one updates it or submits packets.
And there is governance risk when the set of accepted relayers, guardians, or verification workers is controlled by a narrow group or can be changed opaquely. In some architectures this is explicit and unavoidable; in others the protocol is open but practical operation still clusters around a few providers.
Bridge history suggests that the largest losses often come not from the abstract message format, but from concentrated trust and brittle operations around relaying and attestation. That is why bridge design cannot be judged only by its whitepaper verification story. You also have to ask who runs the relay, how many of them there are, what keys they control, what happens if they disappear, and what exactly the destination chain accepts from them.
Conclusion
A bridge relay is the off-chain delivery mechanism that turns cross-chain verification rules into actual cross-chain communication. Its job is to watch one chain, gather the right evidence, and submit that evidence to another chain in a form the destination can verify and act on.
The simplest way to remember it is this: a bridge’s verifier decides; the relayer makes the decision reachable. In strong designs, the relay is untrusted for correctness and only needed for liveness. In weaker or more convenience-oriented designs, the relay becomes part of the trust boundary itself. That difference is where most of bridge architecture really lives.
How do you move crypto safely between accounts or networks?
Move crypto safely between chains by confirming the exact asset, network, and destination before you send funds. Use Cube Exchange to hold and move assets you control: fund your Cube account, confirm the correct chain and token contract, and then initiate the transfer or withdrawal using the destination network you verified.
- Verify the asset and network: check the token symbol and copy the destination contract or token address (for ERC‑20-like tokens) and the exact chain network (e.g., Ethereum Mainnet vs. an L2).
- Send a small test transfer first (e.g., 0.1–1% of the amount) to the destination address and confirm it arrives and is usable on the target chain.
- Wait for chain‑specific finality: monitor required confirmations or finality checkpoints (for example, many EVM chains use 12+ confirmations; finality rules vary by chain) before sending the remaining balance.
- Fund fees and retry logic: ensure your Cube account or source wallet has native token gas for the destination chain and enough to pay any bridge or relayer fees, then submit the full transfer and monitor until the destination acknowledges the receipt.
Frequently Asked Questions
Because blockchains do not actively fetch or package foreign state for themselves: a relayer watches the source chain, assembles the required proof or attestation, and submits it to the destination so the destination can verify and act on the event.
It depends on the architecture: in light‑client systems a missing relayer typically only breaks liveness (messages stop being delivered) because the on‑chain verifier still enforces correctness; in attestation or committee designs a compromised or malicious relayer/guardian set can enable forged actions because the destination trusts their signatures or attestations.
Relays are usually off‑chain because embedding continuous cross‑chain network polling and proof assembly into every chain would bloat consensus engines, be costly to run on‑chain, and hurt portability; off‑chain relayers let operators batch, retry, and optimize for cost while keeping verification logic on chain.
A relayer's core job is observation and evidence movement: it observes source events, packages the right proof or attestation for the destination, and submits it as a transaction; verification (checking proofs or signatures) and final execution of the destination application are separate stages that may be on‑chain or provided by other workers.
Relay packaging varies by design: it can be headers plus Merkle proofs for light clients, a transaction inclusion proof paired with a header in oracle+relayer splits, or a signed attestation/VAA produced by a guardian committee that the relayer simply delivers to the destination.
Common failure modes are security (key or guardian compromise), correctness bugs (wrong proof formatting, reorg timing, ordering mistakes), availability (no relayer running or RPC outages), and governance concentration (few parties controlling accepted relayers or keys).
Multiple relayers can serve the same channel for redundancy (IBC explicitly allows it), but permissionless participation alone does not guarantee timely delivery because economic incentives, fee markets, or application subsidies are often needed to motivate prompt relaying.
There is no single industry‑wide payment model: some relayers are paid by explicit fees or fee markets, some are subsidized by applications or vertically integrated operators, and many documentation sources note incentives and censorship‑resistance are open operational questions rather than solved protocol features.
Relayer operators need reliable RPC endpoints, keys and key management, monitoring, retry and batching logic, fee funding, and configuration for which channels/paths to serve; community tools like Hermes and the Cosmos rly project provide operator tooling and metrics but detailed HA/runbook practices remain a practical concern.
Related reading