What is a Bridged Asset?
Learn what a bridged asset is, how lock-and-mint and burn-and-mint work, why backing matters, and where bridged tokens can fail.
Introduction
Bridged asset is the name for a token on one blockchain that represents an asset from another blockchain. The idea matters because blockchains are separate systems: Bitcoin cannot natively move inside Ethereum, and an asset on Ethereum cannot simply appear on Solana or a Cosmos chain by wishful thinking. If users want to trade, lend, collateralize, or spend that value elsewhere, some mechanism has to recreate it in a form the destination chain understands.
That recreation is the heart of the concept. A bridged asset is not usually the original asset traveling between chains in the literal sense. Instead, it is a representation on the destination chain, created because something happened on the source chain: the original asset was locked, escrowed, or burned, and a bridge treated that event as authorization to issue a corresponding token elsewhere. The destination token may look like any other local token (an ERC-20 on Ethereum, an SPL token on Solana, or a chain-specific asset under another standard) but economically it is tied to something outside the chain where it now lives.
This creates both the utility and the risk. The utility is obvious: value becomes usable in places where it otherwise could not go. The risk is subtler: the token you hold is only as sound as the mechanism that says it is backed. A bridged asset is therefore best understood not just as a token, but as a claim. It is a claim that some off-chain or cross-chain process has preserved an invariant: for every unit of the bridged token, there is a valid reason it exists.
Why do bridged assets exist and what problem do they solve?
A blockchain can only directly control assets in its own state. Ethereum validators can verify Ethereum balances and Ethereum contract logic. They do not natively verify Bitcoin UTXOs, Solana program state, or Polkadot runtime events. So when people say they want to “move” an asset across chains, the real problem is this: how can a destination chain safely act as if value arrived from a source chain that it does not directly govern?
A bridged asset solves that problem by turning foreign value into a local token. The destination chain does not need to run the source chain’s full execution environment in the ordinary sense. It only needs some way to accept evidence that a source-chain event happened and was final enough to trust. Once that evidence is accepted, the destination chain can mint or release a token under its own rules.
This is why bridged assets are so common in multichain systems. Applications want assets where the applications are. If a lending market lives on one chain, users want their capital there. If a decentralized exchange on another chain has deeper liquidity, traders want a tradable representation there. If a game, wallet, or payment flow is cheaper on a third chain, users want spending power there. A bridged asset is the mechanism that makes a foreign asset legible to local software.
What does 'backing' mean for a bridged asset?
| Method | Who enforces | Main risk | Best for |
|---|---|---|---|
| Custodial escrow | Central custodian | Custody breach | Broad compatibility |
| Federation / guardians | Multi-signer consortium | Key‑management compromise | Cross‑chain integrations |
| Light-client / proofs | Destination verifies proofs | Complexity & chain limits | Trust‑minimized security |
| Issuer-native burn | Asset issuer attests | Forged or replayed attestations | Single supply across domains |
The most important idea is backing. A bridged asset is credible only if there is a reliable relationship between the token on the destination chain and the asset or state that justifies it on the source side.
In the simplest case, that relationship is one-to-one. If 1 BTC is locked with a custodian or in a bridge-controlled escrow, then 1 unit of a Bitcoin-representing token can be minted elsewhere. If the bridged token is later redeemed, the destination-side token is burned or otherwise invalidated, and the original asset is released. The point is not the token wrapper itself. The point is preserving a supply invariant across systems: the representation should not exist unless the bridge has valid backing for it.
This is where many smart readers initially misframe the concept. They think the key question is whether the bridged asset is “real.” In practice, the better question is: what enforces the accounting relationship? If the bridge uses a custodian, then custody and audits matter. If the bridge uses a federation or guardian set, then signature security matters. If the bridge verifies cryptographic proofs or light-client state, then proof validity and finality assumptions matter. Different bridges answer the same accounting problem in different ways.
A useful analogy is a warehouse receipt. The receipt can circulate and be useful in trade, but only because people believe the warehouse actually holds the goods and will release them on redemption. The analogy explains the economic role of a bridged asset well. Where it fails is that blockchains can automate issuance, redemption, and verification in ways warehouses usually do not. Still, the central insight carries over: the receipt is valuable because of the reserve relation behind it.
How are bridged assets created (lock‑and‑mint vs burn‑and‑mint)?
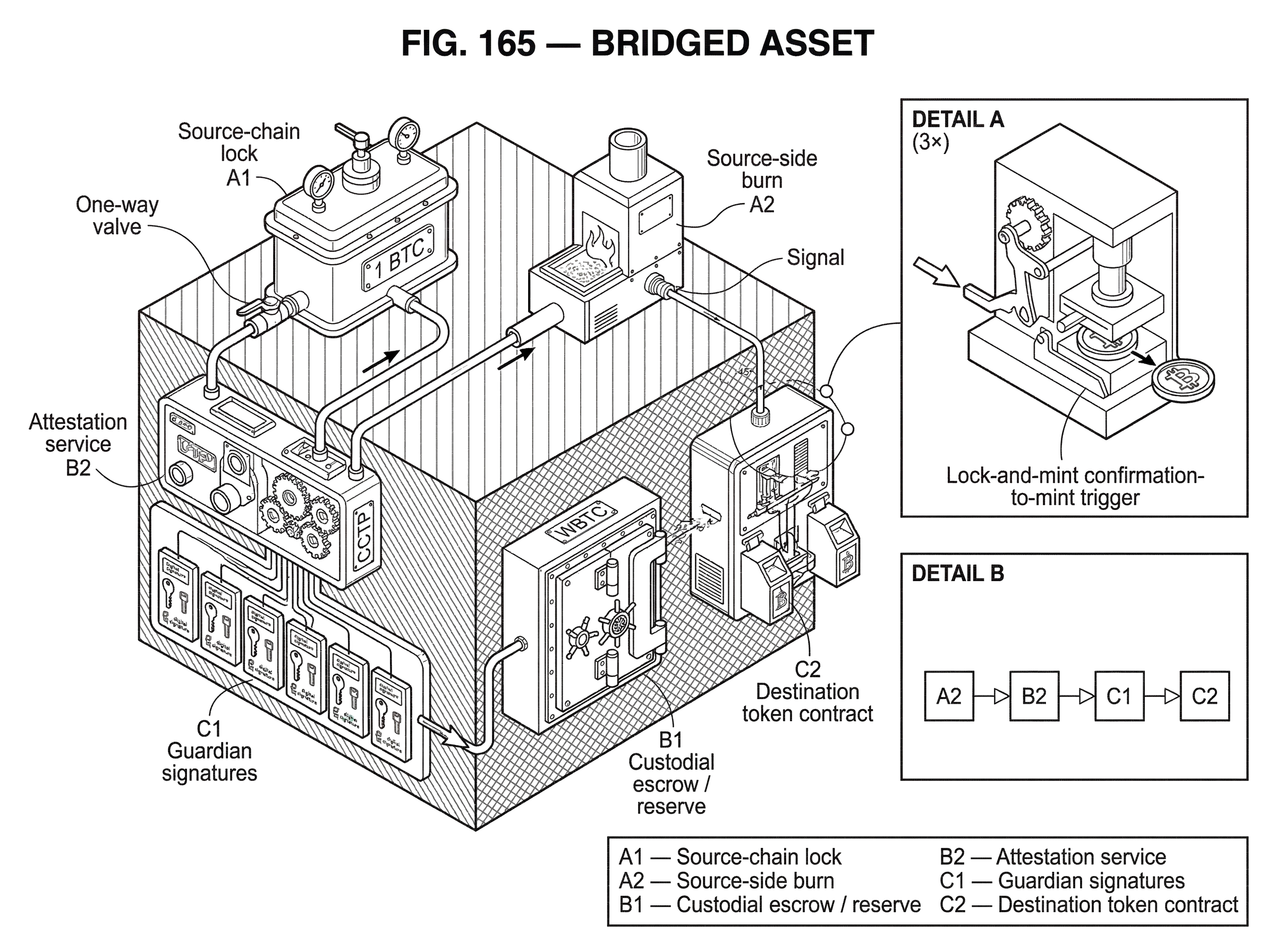
Mechanically, most bridged assets are created using either lock-and-mint or burn-and-mint flows.
In a lock-and-mint design, the original asset is locked on the source chain, and a corresponding token is minted on the destination chain. Ethereum.org describes this as a primary bridging pattern, and it is the one many people first encounter. Suppose a user wants Bitcoin-like value on Ethereum. In a custodial wrapped design such as WBTC, BTC is sent to a custodian-side process, and after the relevant confirmations and approvals, WBTC is minted on Ethereum. The Ethereum token is then usable in wallets, decentralized exchanges, and lending protocols as an ERC-20. It behaves locally like any other ERC-20, but its meaning comes from the fact that BTC is supposed to sit in reserve behind it.
In a burn-and-mint design, the source-side token is destroyed rather than locked, and a corresponding token is minted on the destination chain. This is common when the asset issuer or protocol wants a single circulating supply distributed across multiple chains rather than multiple wrapped forms with separate reserve pools. Circle’s Cross-Chain Transfer Protocol, for example, documents a native burn-and-mint flow for USDC: on the source domain, tokens are burned; a message describing the burn is attested; and on the destination domain, a corresponding amount is minted for the recipient once the message is accepted. Economically, this aims to preserve one asset across domains rather than creating a permanently escrow-backed wrapper.
The distinction matters because it changes where risk concentrates. In lock-and-mint, the escrow or custodian becomes a honeypot. If attackers can steal or falsely unlock the reserve, the destination token may become unbacked. In burn-and-mint, the critical issue is whether the minting authorization can be forged or incorrectly replayed. If an attacker can mint without a real burn, supply discipline breaks in a different way.
How does a bridged token get created on the destination chain? (step‑by‑step example)
Imagine a user holds an asset on Chain A and wants to use it in an application on Chain B. The application on Chain B only understands Chain B’s token standard and state model. It cannot read Chain A and simply decide, on its own authority, that the user should have a balance.
So the user interacts with a bridge on Chain A. If the bridge is using lock-and-mint, the asset is sent into an escrow controlled by the bridge or custodian. If the bridge is using burn-and-mint, the source-side token is destroyed. Either way, the bridge now has a source-chain event that is meant to justify issuance elsewhere. That event is then observed, proven, or attested to according to the bridge’s trust model. On some systems this may involve an external verifier set signing a message. On others it may involve proof verification, relayers, or chain-native consensus evidence.
Once Chain B accepts that evidence, a local token is minted or released to the user. At that point, the token can move through Chain B exactly like other local assets. It can sit in a wallet, serve as collateral, be traded, or be routed through smart contracts. This local composability is why bridged assets are so useful: once the representation exists, most applications do not need to know the full history of how it got there. They simply see a token balance that conforms to the local interface.
But that convenience hides a dependency. The token remains a valid claim only as long as the source-side event was genuine, final, and uniquely consumed. If the source lock is reversed by a reorganization, if the burn was not actually final, if the attestation was forged, or if the message is replayed, then the destination token may exist without legitimate backing. The token looks normal in local code while being economically unsound underneath.
How does source‑chain finality affect bridged asset safety?
A bridged asset depends not only on an event having happened, but on that event being final enough that the destination chain can safely act on it.
This sounds abstract until you see the failure mode. Research on blockchain interoperability points out a simple but important fact: if the source-chain transaction that created the backing later reverts, then the destination-side asset becomes unbacked. That is the bridge version of printing a warehouse receipt and then discovering the goods were never successfully stored after all.
So bridges need a rule for when to trust source-chain events. On some systems that means waiting for a certain number of block confirmations. The WBTC process, as specified in its whitepaper, includes waiting for Bitcoin confirmations before minting and Ethereum confirmations before completing burns for redemption. In Tendermint-style systems, the relevant evidence is tied to commit rules and validator signatures with more immediate finality assumptions. In message-attested systems such as Circle’s CCTP, the protocol defines explicit finality thresholds before the attestation service will sign a message. Different chains have different settlement properties, so a bridge is always making a judgment about what counts as safe enough.
This is one reason bridge design is hard. Fast bridging is attractive, but faster recognition of source events can mean weaker confidence that those events will remain true. The trade-off is not cosmetic. It is directly about solvency.
Trusted vs trust‑minimized bridges: who authorizes minting on the destination?
| Model | Who attests | Trust assumptions | Connectivity | Typical risk |
|---|---|---|---|---|
| Custodial / trusted | Single operator or custodian | Trust operator honesty | High | Custody compromise |
| Federated / guardians | Consortium signers | Majority signer security | High–moderate | Key compromise or collusion |
| Trust‑minimized / light‑client | On‑chain proof verification | Source chain security only | Limited | Implementation complexity |
When a destination chain accepts a bridged asset, it is effectively accepting someone’s answer to the question, “yes, the source-side condition has been met.” The important architectural difference between bridge designs is who gets to answer that question and how that answer is checked.
Ethereum.org frames a useful top-level contrast between trusted and trustless bridges. In trusted bridges, an external set of verifiers, custodians, or operators determines whether the source event occurred and whether minting or release should happen on the destination side. This can be operationally simple and can support broad connectivity, but it adds explicit counterparty assumptions. You are not only trusting the source and destination chains; you are trusting the bridge’s own actors and key management.
In more trust-minimized designs, the bridge tries to rely more directly on the security of the connected chains themselves, often through proof verification, validator-derived evidence, or light-client-like approaches. That reduces some added trust assumptions, but it usually increases complexity and may constrain which chains can be connected efficiently.
This is not a matter of pure ideology. It changes what a bridged asset actually is. A custodial wrapped token is a claim on a custodian or consortium. WBTC is a clear example: the token is defined as an ERC-20 on Ethereum backed 1:1 by Bitcoin, with distinct custodian, merchant, and governance roles. A guardian-signed token bridge such as Wormhole Wrapped Token Transfers depends on Guardian-signed VAAs that authorize minting or release on the destination chain. A protocol like CCTP depends on Circle’s attestation service to confirm burns before destination minting. In each case, the destination token’s credibility comes from a different enforcement mechanism.
Why does a bridged token look local but carry foreign meaning?
One subtle but important point is that a bridged asset is always implemented using the destination chain’s own asset model.
On Ethereum, that usually means an ERC-20 contract. On Solana, it means an SPL token represented through a mint account and token accounts controlled by the local token program. On other systems, the local runtime or token module defines the representation. This is why bridged assets compose so well with local applications: once minted, they are ordinary local assets from the chain’s point of view.
But the fact that the form is local does not make the meaning local. A bridged ETH on Solana, a Bitcoin-backed ERC-20 on Ethereum, or an IBC-transferred token within Cosmos all carry provenance. Their economic identity depends on origin and path, not just ticker symbol. That is why “canonical” versus “wrapped” versus “bridged” can become contentious in ecosystems with multiple competing bridges. Two tokens with similar names may each claim to represent the same source asset but rely on different issuers, reserve models, or verification paths.
The underlying lesson is that token standard compatibility is necessary but not sufficient. A bridged asset is never just bytes in the local format. It is bytes plus a cross-chain liability structure.
Why use bridged assets despite their risks?
Despite the complexity, bridged assets are widely used because the alternative is fragmentation. If each chain could only use assets native to itself, then liquidity, collateral, payments, and application state would remain trapped inside chain boundaries.
Bridged assets let users bring existing value into new execution environments. Bitcoin can participate in Ethereum DeFi through wrapped forms. Stablecoins can circulate across multiple chains without every application depending on the same base layer. Assets can follow users to cheaper execution venues, specialized app chains, or ecosystems with different tooling and user bases. In Cosmos-style interoperability, token transfer standards and relayer mechanisms aim to move fungible assets across chains in a more natively interchain way. In Polkadot-style systems, message formats such as XCM describe the intended cross-consensus actions, while transport and chain-specific interpretation determine whether an asset can actually be represented and used at the destination.
So the practical appeal is not mysterious. Bridged assets are what make a multichain world economically connected rather than a set of isolated ledgers.
How and why bridged assets fail (common attack and failure modes)
The clean story is “lock or burn here, mint there.” The messy reality is that the link can fail in several distinct ways.
The first failure is verification failure: the bridge incorrectly accepts a source event that never happened or was not valid. The Wormhole exploit is a vivid case study. An attacker manipulated VAA verification and fraudulently minted large amounts of wrapped ETH on Solana without the corresponding Ethereum backing. The local token behaved like a valid asset until the missing backing became undeniable. This shows why bridged-asset risk is not just market volatility risk; it is also issuance-integrity risk.
The second failure is finality failure: the bridge accepts a source event too early, and the source chain later reorganizes or otherwise invalidates it. In that case the bridged asset may be technically well-formed on the destination chain yet economically unbacked.
The third failure is custody or key-management failure: the reserve exists in principle, but the parties controlling it are compromised. Research surveying interoperability incidents found a substantial share of stolen funds tied to intermediary permissioned networks and weak cryptographic key operations. This is the operational side of the problem: even if the accounting design looks sound on paper, poor signer security can destroy it.
The fourth failure is governance failure: the actors who can upgrade contracts, add signers, rotate guardians, or reconfigure routes may make mistakes, be captured, or act against holders’ interests. A bridged asset often inherits not just code risk, but organizational risk.
This is why some risk frameworks describe bridge-wrapped assets as liabilities of the bridge. That phrase is useful because it forces the right mindset. If you hold a bridged asset, you are not only exposed to the underlying asset’s price. You are exposed to the bridge’s solvency, operations, and security assumptions for as long as you hold the token.
Lock‑and‑mint vs burn‑and‑mint: practical trade‑offs and security implications
| Mechanism | Source action | Destination action | Main risk | Best for |
|---|---|---|---|---|
| Lock‑and‑mint | Asset locked in escrow | Representative token minted | Reserve theft or mismanagement | Assets without issuer control |
| Burn‑and‑mint | Token burned by issuer | Mint after attestation | Forged or replayed mint messages | Single supply across domains |
It is tempting to think one mechanism is always superior, but the better view is that each mechanism shifts the burden.
Lock-and-mint works well when an original asset cannot be natively reissued on the destination chain, or when the issuer does not control supply across chains. It is broad and intuitive: keep the original in escrow, create a representative token elsewhere. That is why it appears so often for foreign assets entering EVM systems and other DeFi environments. But it concentrates value in escrow and creates explicit reserve management problems.
Burn-and-mint works better when a protocol or issuer wants one coordinated asset across multiple domains. It avoids some wrapped-asset fragmentation and may reduce dependence on large locked pools. But it requires strong guarantees that burns are correctly observed, messages are not replayed, and mint authority cannot be abused. CCTP’s explicit attestation flow and finality thresholds illustrate this design discipline.
There is also a broader pattern emerging in some ecosystems: when possible, developers prefer moving native assets under native issuer control rather than proliferating many third-party wrapped versions. That preference exists because it simplifies the question of who is responsible for the backing. But it does not eliminate trust assumptions; it just relocates them.
What makes a bridged asset ‘canonical’, and does that matter?
Readers often ask whether a bridged asset is the “official” version of an asset on a chain. Sometimes yes, sometimes no, and sometimes the answer depends entirely on local convention.
“Canonical” is not a magical technical property by itself. It usually means that a particular bridge or issuer has become the socially accepted or ecosystem-preferred path for representing the asset. That may happen because the issuer controls mint and burn, because a bridge is deeply integrated into major applications, or because wallets and exchanges default to that version. But another token with the same intended backing may still exist through a different bridge.
So canonicalness is partly a question of governance and ecosystem coordination, not just mechanism. The fundamental question remains the same: which representation has the clearest, strongest, and most trusted redemption and verification path?
Conclusion
A bridged asset is a token on one chain that represents value originating on another chain. Its usefulness comes from making foreign value locally usable, but its safety comes from a stricter condition: the destination token must remain properly backed by a valid, final, and uniquely accounted-for source-side event.
If you remember one thing, remember this: a bridged asset is not just a token format; it is a cross-chain promise. Everything that matters flows from how that promise is enforced, who enforces it, and what happens if the enforcement fails.
How do you move crypto safely between accounts or networks?
To move crypto safely between accounts or networks, always confirm the exact asset, destination network, and required finality before sending. Use Cube to receive or hold funds and to initiate outbound transfers once you have verified network and address details.
- Verify the asset and network by copying the token contract address (for ERC‑20/SPL) or exact chain name and comparing it to the Cube deposit/withdrawal network.
- Fund your Cube account (fiat on‑ramp or supported crypto transfer) or prepare the external wallet that will send the asset, ensuring you select the same network as the destination.
- Check fees and on‑chain gas, and confirm any destination requirements (memo/tag/contract address) before submitting the transaction.
- Send a small test amount first and wait for the bridge or chain’s stated confirmation threshold (e.g., bridge-specified attestation or common heuristics like ~6 BTC confirmations) to credit before sending the remainder.
- After the test clears, send the full amount and monitor the on‑chain transaction ID and Cube’s deposit/withdrawal status until the transfer completes.
Frequently Asked Questions
Lock-and-mint locks or escrows the original asset and mints a representation elsewhere, concentrating risk in the escrow/custodian; burn-and-mint destroys supply on the source and mints on the destination, concentrating risk in the minting/attestation authority and message-observation process.
Because the destination chain acts on evidence of a source-chain event, the event must be final enough that it won't later revert; if a source transaction that justified minting is reorganized or undone, the destination token can become unbacked, so bridges impose finality rules (e.g., waiting for confirmations) to reduce that risk.
Bridged assets commonly fail through incorrect verification (accepting events that never happened), insufficient finality (acting before a source event is irreversible), custody/key-management breaches (compromise of reserve signers), and governance mistakes (upgrades or reconfiguration that harm holders); the Wormhole incident is a concrete example of verification/key-management-related failure.
Trusted bridges rely on external custodians, operator sets, or attestors to assert that a source condition was met, adding counterparty assumptions; trust‑minimized designs try to verify source state more directly (e.g., proofs or light-client‑style evidence) which reduces added trust but increases complexity and connectivity constraints.
‘Canonical’ usually means a representation that the ecosystem has socially accepted - because an issuer or bridge is integrated widely or controls mint/burn - but canonicalness is not a purely technical property and depends on governance, integrations, and which redemption/verification path users trust.
Holding a bridged asset exposes you not only to the underlying asset’s market risk but also to the bridge’s solvency, operational security (key management and relayers), and governance choices - your token is economically a liability of the bridge mechanism until redeemed.
Circle’s CCTP treats configured finality thresholds as effectively two values - any value below 1000 is treated as 1000 and any value above 1000 is treated as 2000 - so integrators should design around those discrete thresholds when expecting attestation-based minting.
Wormhole uses a Guardian set that signs VAAs to authorize transfers, manual transfers must be completed within 24 hours because Guardian Sets can rotate, and destination completion often relies on off‑chain relayers or destination on‑chain TBR availability - so guardian compromise, set-rotation windows, or relayer unavailability are operational attack or failure points.
Because bridged assets are implemented using the destination chain’s token model (ERC‑20, SPL, etc.), they integrate with local applications like any native token, but their economic identity depends on provenance and the bridge’s redemption/verification path, so token standard compatibility alone does not guarantee trustworthiness.
Related reading