What Is Slashing?
Learn what slashing is in proof-of-stake consensus, how it punishes validator equivocation, and why it matters for security and finality.
Introduction
Slashing is the rule in many proof-of-stake systems that destroys part of a validator’s stake when the validator can be shown to have broken consensus rules. At first glance this can seem harsh, even strange: why should a blockchain need punishment at all? The answer is that proof of stake replaces the physical cost of mining with an economic bond, and a bond only works if it can actually be taken away.
That is the central idea. In proof of work, attacking the chain usually means burning real-world resources such as electricity and hardware time. In proof of stake, the system asks validators to lock capital instead. If that capital is never meaningfully at risk, then signing conflicting histories can become too cheap. Slashing exists to make some forms of cheating, especially equivocation such as double-signing, observably punishable.
This is why slashing matters far beyond validator operations. It is part of the security model of modern consensus itself. In systems such as Ethereum, slashable voting rules are tied directly to economic finality: the network can treat some decisions as costly to reverse precisely because validators that contradict themselves can lose stake. In other systems, such as Cosmos and Polkadot, slashing also disciplines downtime or duplicate signing, though the exact offenses and penalty formulas differ.
The key thing to keep in mind is simple: slashing is not just a penalty schedule. It is the mechanism that makes a stake-based promise credible.
Why do proof-of-stake systems punish validators?
A consensus protocol is trying to solve a narrow but difficult problem: many machines must converge on one shared history, even when some participants are faulty or adversarial. In proof of stake, validators help choose that history by proposing blocks, voting on them, or both. The protocol wants those actions to reveal real preference. If a validator can safely endorse every competing history at once, those votes stop meaning what they are supposed to mean.
This is the old “nothing at stake” worry that early proof-of-stake designs had to confront. If producing a vote is cheap, why not vote on all forks and collect rewards whichever branch wins? From the validator’s private perspective, signing twice can look like free optionality. From the network’s perspective, that behavior is corrosive: it weakens fork choice, makes double-spends easier to attempt, and undermines any claim that votes express committed support for one chain.
The first important response was conceptual. Rather than asking validators to merely act honestly, the protocol can define a narrow set of statements that must never both be signed by the same validator. If a validator signs two incompatible statements, anyone who sees both signatures can submit them as evidence. The system then automatically penalizes the offender. This was the core insight behind Ethereum’s early Slasher proposal: make conflicting commitments visible across forks, and make that visibility economically actionable.
That proposal was not identical to modern Ethereum, and it relied on a hybrid design with a small proof-of-work component. But the lasting idea was deeper than any one design: forks are tolerable only if contradictory validator behavior is both detectable and expensive. Slashing turned that principle into a mechanism.
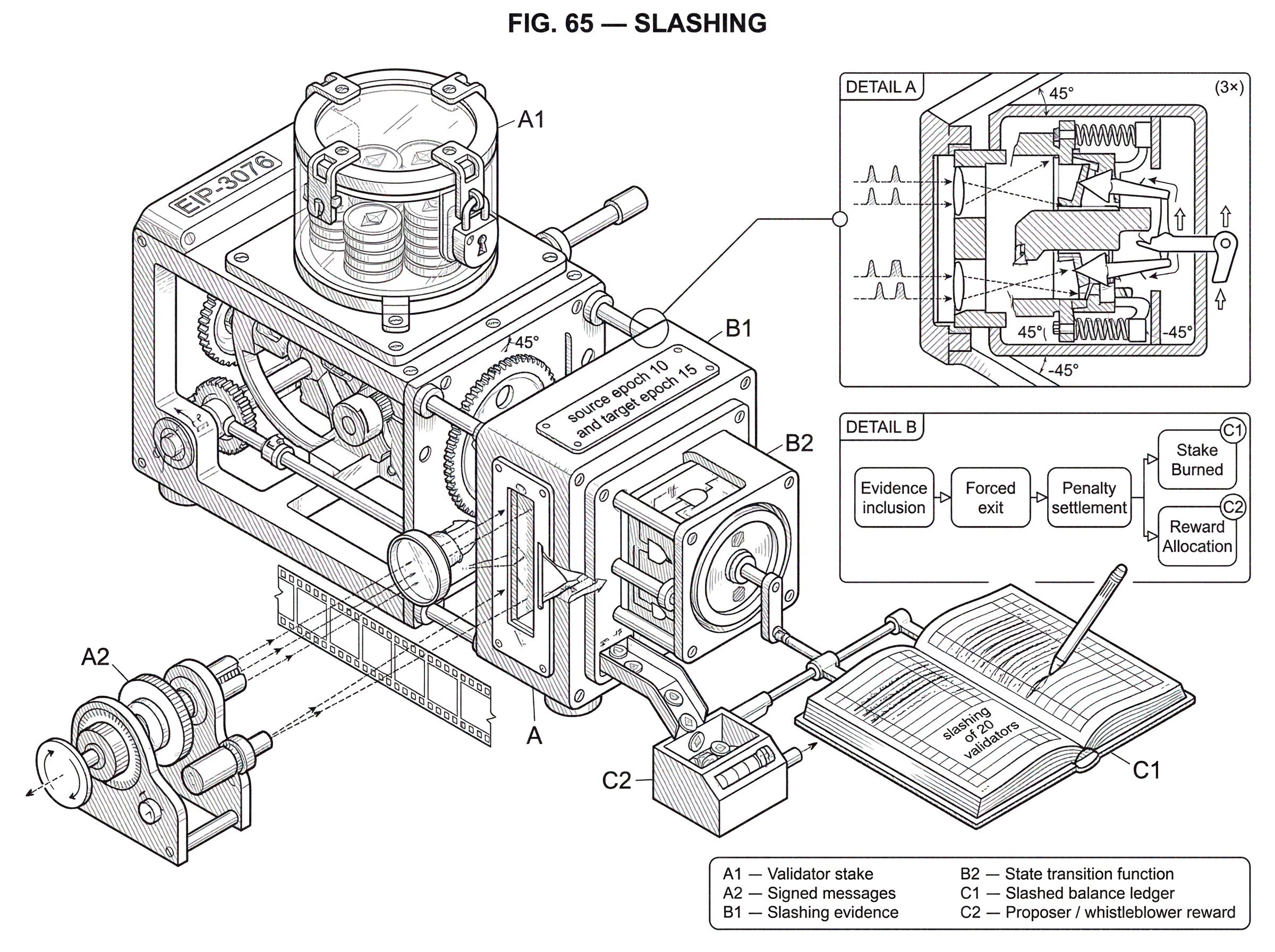
How does slashing work: bond, incompatible messages, and on-chain evidence?
Every slashing system has local details, but the underlying structure is usually the same.
A validator first posts or locks stake. That stake is the bond that backs the validator’s future messages. The protocol then defines some messages as mutually incompatible. Finally, it specifies a way to prove the incompatibility on-chain. Once the proof is accepted, the state transition applies penalties automatically.
This structure matters because it separates honest mistakes or downtime from provable contradictions. Slashing is usually reserved for behavior that can be demonstrated from signed messages themselves. That makes enforcement objective. The chain does not need to infer intent; it only needs to verify that the same key signed two statements that cannot both be valid under the protocol’s rules.
A useful analogy is a security deposit attached to a notarized declaration. The deposit is not there to motivate vague good behavior. It exists so that if you submit two contradictory notarized claims, anyone can bring both documents forward and trigger forfeiture. The analogy explains why slashing depends on signatures and evidence. It fails, however, in one important way: blockchains can encode the forfeiture rules directly into consensus, so enforcement is automatic rather than institutional.
This is also why slashing is narrower than “all bad validator behavior.” Some failures are punished in other ways. A network might reduce rewards for inactivity, temporarily jail a validator, or exclude it from future participation. Slashing is typically reserved for cases where the protocol can point to a compact cryptographic proof of misbehavior and say, with high confidence, this validator contradicted itself.
Which validator actions are typically slashable across chains?
| Offense | Evidence | How detected | Typical penalty | Why slashable |
|---|---|---|---|---|
| Proposer double-sign | Two different signed headers | Compare headers' signatures | Immediate slash and exit | Breaks single-block-per-slot rule |
| Attester double vote | Two attestations same target epoch | Attestations included on-chain | Proportional slash and exit | Undermines checkpoint finality |
| Surround vote | Attestation that surrounds another | Epoch source/target comparison | Proportional slash and exit | Violates Casper FFG invariants |
| Downtime | Missed blocks over window | MissedBlocks counter / window | Jailing and possible slash | Harms liveness and availability |
| Delayed historical double-sign | Old conflicting block signatures | Late-arriving evidence submission | Often single capped slash | Avoids repeated punishment for one fault |
The common thread across slashable offenses is equivocation: a validator says two incompatible things to the network.
In Ethereum’s beacon-chain consensus, there are two major evidence types. A proposer slashing proves that the same validator signed two different block headers for the same slot. Mechanically, the evidence contains the two signed headers; the protocol checks that they come from the same proposer and slot, that they differ, and that the validator is currently slashable. If those checks pass, the validator is slashed.
An attester slashing proves an incompatible pair of attestations. The consensus spec defines two important cases. A double vote means a validator made two different attestations with the same target epoch. A surround vote means one attestation’s source and target epochs surround another’s. These rules come from Casper FFG and are not arbitrary bookkeeping. They are crafted so that violating them threatens the structure that finality depends on. If validators could make such contradictory votes without cost, finalized history would be much less meaningful.
A worked example makes this clearer. Imagine a validator has already attested to a checkpoint path with source epoch 10 and target epoch 15. Later, perhaps because it is running two uncoordinated clients, it signs another attestation with source epoch 9 and target epoch 16. That second vote “surrounds” the first. The problem is not merely that the votes are different. It is that together they allow the validator to support conflicting checkpoint structures in a way the finality gadget explicitly forbids. Once both signed attestations are visible, any block proposer can include attester-slashing evidence, and the protocol can penalize the validator without needing to guess what the operator intended.
Other chains use different offense sets because their consensus machinery differs. Cosmos SDK chains distinguish between double-signing and downtime. Double-signing is a classic equivocation fault with stake at risk. Downtime is a liveness fault, detected through missed blocks over a sliding window, and may trigger slashing plus jailing depending on chain parameters. Polkadot treats equivocation in BABE, GRANDPA, or BEEFY as slashable, and computes the slash as a percentage that grows with how many validators offended relative to the active set. Solana’s public staking FAQ describes slashing more conditionally, as a punitive destruction of stake for malicious actions, noting that slashing is not automatic in the same always-on way.
So the surface rules vary, but the principle is stable: slash when a validator’s own signed messages prove a consensus-threatening contradiction, and sometimes also for attributable liveness faults if the chain chooses that design.
How are slashing penalties applied and calculated?
| Stage | When applied | Immediate effect | Purpose | Typical size |
|---|---|---|---|---|
| Evidence inclusion | On valid evidence in block | Validator marked slashed | Prove and record offence | Minimum fixed fraction |
| Forced exit | Same processing as inclusion | Initiate validator exit | Prevent more signing | N/A (functional) |
| Delayed proportional charge | At withdrawable epoch processing | Additional balance deduction | Price correlated mass-slashes | Scales with recent slashed stake |
| Reporter reward | When slash is included | Proposer/whistleblower paid | Incentivise evidence reporting | Small fraction of slashed stake |
The intuitive story is “cheat and lose stake,” but real protocols usually make slashing a multi-stage process rather than a single fine.
Ethereum is a good example. When valid slashing evidence is processed, the protocol calls a state transition function that does several things together. The validator is forced to exit. It is marked as slashed. Its withdrawability is delayed. Its effective balance is recorded in a slashing-tracking vector. An immediate minimum penalty is applied to its balance. And rewards are allocated to the actor who included or reported the evidence, via proposer and whistleblower reward logic in the spec.
The reason for this layered design is that slashing is trying to achieve more than punishment. It also wants containment and credible accounting. Ejecting the validator prevents continued participation by a proven offender. Delaying withdrawal keeps stake in reach long enough for later penalties to be assessed. Recording slashed balance over time lets the protocol impose a larger penalty if many validators are slashed in the same broad window.
That last part is crucial. In Ethereum, the later proportional or correlation penalty scales with the amount of stake slashed around the same time. The mechanism expresses an important idea: an isolated operator mistake and a coordinated attack are not equally dangerous to the network, so they need not be priced the same. If only a tiny amount of stake is slashed, the extra penalty can be small and may even round down in some cases. If a large fraction of stake is slashed together, the penalty rises sharply. Here is the mechanism in plain language: the protocol sums recently slashed balances, multiplies by a slashing multiplier, caps the result by total active stake, and later charges each slashed validator a share proportional to its effective balance.
Polkadot uses the same broad philosophy in a different mathematical form. For equivocations, the slash percentage grows with x / n, where x is the number of offenders and n is the active validator set size, through the formula min((3 * x / n)^2, 1). The exact curve is protocol-specific, but the design logic matches Ethereum’s: punish correlated failures much more severely than isolated ones.
Cosmos introduces a different nuance with its tombstone cap for double-sign faults. Because some evidence can arrive late, a misconfigured validator could in principle be shown to have double-signed multiple historical blocks. Rather than slash repeatedly without bound for what is operationally one underlying mistake, the tombstone mechanism limits punishment so the validator is only slashed once for that class of fault. This is a modeling choice, not a universal law. It reflects a judgment about fairness, delayed evidence, and operational reality.
How does slashing support economic finality?
The phrase economic finality can sound abstract until you connect it to what slashing actually prices.
Finality means there comes a point when reversing history is not just unlikely but meaningfully constrained. In proof-of-work systems, finality is usually probabilistic: the deeper a block is buried under cumulative work, the more expensive it becomes to reorganize. In proof-of-stake systems with slashing, finality can also be economic: if reverting a finalized state would require validators to sign contradictions that are slashable, then the reversion has an explicit cost in destroyed stake.
This does not mean slashing makes rollback impossible. It means the protocol can attach a well-defined loss to the validators who would have to participate in such a rollback. That is a stronger claim than “honest validators probably won’t do it.” It is closer to “to do it, validators must burn something substantial and publicly attributable.”
That is why Ethereum’s attestation slashing rules are tied so tightly to Casper FFG. The protocol is not punishing arbitrary rule-breaking. It is protecting the invariant that finalized checkpoint votes cannot be contradicted without leaving cryptographic evidence of the contradiction. Slashing is what turns that invariant into capital at risk.
Why is whistleblowing required to enforce slashing?
A slashing rule is only useful if evidence can reliably get on-chain.
This was explicit even in the early Slasher design. There, double-signing evidence had to be published within a specified window to destroy the offender’s reward and grant part of it to the reporter. That design choice reveals a general truth: slashing is not only about defining bad behavior; it is also about creating incentives for other participants to surface proofs of that behavior quickly.
Ethereum’s consensus spec includes proposer and whistleblower reward logic when a validator is slashed. In practice, explainers note that the proposer currently receives the relevant reward flow, even though the code conceptually separates whistleblower and proposer shares. The exact reward plumbing matters less than the economic purpose. You want the network to contain enough participants who would rather collect a bounty for exposing equivocation than ignore it.
This creates a subtle dependency. Slashing assumes the chain can process evidence in time and that block space, censorship resistance, and client implementations make reporting feasible. If evidence inclusion were routinely blocked, the deterrent would weaken. So slashing is not just a local penalty function; it depends on the broader system being able to carry proofs from observers into state transitions.
When and how does slashing fail in practice (operator mistakes)?
In theory, slashing sounds like punishment for malicious validators. In practice, many slashes come from operator mistakes.
This is the first thing smart readers often underestimate. A validator can be slashed not because its operator intended to attack the network, but because two machines accidentally sign with the same key, a failover setup activates incorrectly, or a client migration loses signing history. The protocol cannot distinguish “malicious equivocation” from “incompetent equivocation” once both signed messages exist. It only sees conflicting signatures.
This is why slashing protection became a serious operational discipline, especially on Ethereum. EIP-3076 defines a standard interchange format for validator signing history so operators can move between clients without creating accidental conflicts. The logic is straightforward: the new signer must know what the old signer already signed, otherwise it may innocently produce a message that is slashable relative to history it cannot see. Lighthouse and other clients therefore maintain a slashing-protection database recording past blocks and attestations, and use it to refuse dangerous signatures.
A concrete failure mode shows why this matters. Suppose an operator runs one validator client, then brings up a replacement client with the same key before cleanly stopping the first, or without transferring signing history. Each instance may think it is behaving correctly from its own partial view. But if both sign attestations for the same target epoch with different data, the network sees only a double vote. The result can be an attester slashing even though the “attack” was really a botched migration or failover.
Real incidents have followed exactly this pattern. One Ethereum post-mortem described multiple validator client instances being pointed at a single remote signer without slashing protection enabled, leading to double votes and slashing of 20 validators. Another incident involved disabling a local slashing-protection database to improve performance; after production restarts, validators signed a second version of the same blocks and 75 validators were slashed. The lesson is uncomfortable but important: consensus rules are unforgiving because they have to be. Operational softness would reopen the very ambiguity slashing is meant to close.
What's the difference between protocol slashing and client slashing protection?
It helps to distinguish the protocol mechanism from the operator safeguard.
Slashing is the consensus-level punishment rule. It defines offenses, evidence, and state transitions. Slashing protection is the client-side system that tries to stop a validator from ever producing slashable signatures in the first place. The former is part of network security. The latter is part of operational safety.
That distinction matters because client-side protection has limits. A local database cannot save you if the same signing key is active in two different machines or datadirs that do not coordinate. It cannot retroactively repair missing history. And recreating a lost protection database without careful waiting and recovery procedures can itself create slashing risk. This is why client docs insist that import and export of protection data happen only while the validator is stopped.
In other words, slashing protection reduces accidental fault, but it does not change the underlying rule that contradictory signatures are punishable. It is a seatbelt, not a rewrite of the traffic law.
Why do different blockchains use different slashing rules and penalties?
| Chain | Offense set | Downtime handling | Penalty scaling | Operator ergonomics |
|---|---|---|---|---|
| Ethereum | Proposer and attester equivocation | Inactivity penalties; slashing for equivocation | Proportional multiplier, delayed charge | Strict; requires slashing protection |
| Cosmos | Double-sign and downtime | Sliding-window misses; jailing plus slash | Tombstone cap for historical double-signs | Configurable; tombstone limits repeats |
| Polkadot | Equivocation in BABE/GRANDPA/BEEFY | Separate liveness rules and jailing | Formula min((3x/n)^2, 1) scales penalty | Governance grace period for reversals |
| Solana | Malicious actions conditional | Slashing not automatic; used after halts | Conditional, not always-on penalties | Less always-on risk; conditional enforcement |
If the purpose of slashing is so clear, why do protocols implement it differently?
Because slashing sits at the intersection of three design choices: what behavior the protocol can prove, how much harm that behavior causes, and how much operator error the system is willing to treat as economically costly. Different chains make different judgments on each axis.
Ethereum emphasizes equivocation tied to finality and fork choice, with delayed exits and proportional penalties that grow in correlated events. Cosmos adds explicit downtime handling and a tombstone cap for delayed-evidence double-sign faults. Polkadot uses offense-specific percentage slashes and even a grace period before an unapplied slash becomes final, allowing governance reversal during that window. Solana’s public documentation presents slashing as a conditional punitive tool rather than the same always-on structure seen in Ethereum’s beacon-chain rules.
These are not cosmetic differences. They reflect different assumptions about evidence timing, validator set structure, social recovery, and the balance between deterrence and operator ergonomics. What is fundamental is the bond-backed punishment for provable fault. What is conventional is the exact offense list, formula, timing, and fund destination.
Conclusion
Slashing is the mechanism that makes proof of stake more than voting by cheap talk. A validator locks capital, the protocol defines contradictions that must never both be signed, and anyone who proves such a contradiction can trigger automatic punishment.
That simple structure carries a lot of weight. It is what gives stake-based consensus a way to price equivocation, support economic finality, and make contradictory votes costly instead of free. But it also means validator operations must be disciplined: many real slashes come not from grand attacks, but from duplicated keys, bad failover, and missing signing history.
The shortest version to remember tomorrow is this: slashing is how a proof-of-stake network turns “I promise this history is valid” into a promise backed by money.
What should I check about slashing before trading, depositing, or staking?
Understand what to check about slashing before you trade, deposit, or stake. Confirm whether the chain punishes equivocation or downtime, the size and timing of penalties, and any withdraw/unbond delays that affect liquidity. Use Cube Exchange to fund and execute the relevant deposit, trade, or staking flow once those protocol checks are complete.
- Fund your Cube Exchange account with fiat or transfer a supported crypto to the exact deposit network and address shown to avoid cross-chain loss.
- Read the asset’s consensus and staking notes (on-chain docs or Cube’s asset details): note whether the chain slashes for double-signing or downtime, the typical slash sizes, and the withdraw/unbonding delay that affects liquidity.
- If you plan to stake on-chain, verify the validator’s slashing-protection practices and recent uptime/incident history before delegating; prefer validators with an exported slashing-protection record or documented failover procedures.
- For trading or transfers, wait for the chain-specific finality/confirmation threshold shown in the deposit flow before considering funds final, then open the market or submit the transfer; use a limit order for volatile assets to control execution price.
Frequently Asked Questions
Slashing ties a validator’s messages to a locked bond and defines pairs of signed messages that cannot both be valid; anyone who publishes the two conflicting signatures on-chain presents objective evidence and the protocol automatically destroys part of the offender’s stake, so equivocating becomes a directly payable cost rather than cheap optionality.
The canonical slashable class is equivocation (double-signing/conflicting votes), but implementations vary: Ethereum distinguishes proposer and attester slashings (double and surround votes), Cosmos treats double‑signing and downtime (with tombstone caps), Polkadot slashes equivocations in its consensus components and uses offender‑count formulas, and Solana documents slashing as conditional rather than always automatic.
Penalties are multi‑stage: the validator is ejected, marked slashed, withdrawability is delayed, an immediate minimum penalty is applied, and additional proportional penalties can be levied later based on recently slashed stake (Ethereum’s proportional/correlation scaling and Polkadot’s offender‑count formula illustrate the principle that correlated failures are punished much more severely than isolated mistakes).
Many real slashes result from operator mistakes - running multiple active signing instances, failed client migrations, or lost signing history - and slashing protection is a client‑side database/format (e.g., EIP‑3076, client slashing DBs) that blocks creating slashable signatures but cannot protect against the same key being active on two uncoordinated machines.
Slashing does not make finality absolute; it makes reversal economically costly by ensuring that validators would have to produce publicly attributable, slashable contradictions to revert finalized history, but it does not make rollbacks impossible in every scenario.
Reporting (whistleblowing) is essential because evidence must reach the chain to trigger penalties; protocols reward proposers/whistleblowers for including slashing evidence, and if evidence inclusion is delayed or censored the deterrent is weakened.
Chains disagree on offence lists, penalty curves, timing, and mitigation (e.g., tombstone caps or governance grace periods) because designers trade off what misbehaviour is provable, how damaging it is considered, and how much accidental operator error should be economically punished; the core idea - bonded stake at risk for provable contradictions - remains constant.
Some chains delay applying a slash or delay withdrawability so the protocol can contain penalties and allow for proportional accounting; Polkadot, for example, places slashes into an unapplied state with a governance grace period (27 days) before final application, and Ethereum delays withdrawals and records slashed balances to compute later proportional penalties.
Client‑side slashing protection lowers accidental risk but is not a substitute for safe operational practices: the protection is local and requires stopping the validator to import/export histories, so high‑availability setups must ensure keys are never active simultaneously or otherwise coordinate signing history to avoid creating slashable duplicates.
Related reading