What Is a Light Client Bridge?
Learn what a light client bridge is, how it verifies cross-chain state on-chain, why it is more trust-minimized, and where its assumptions still matter.
Introduction
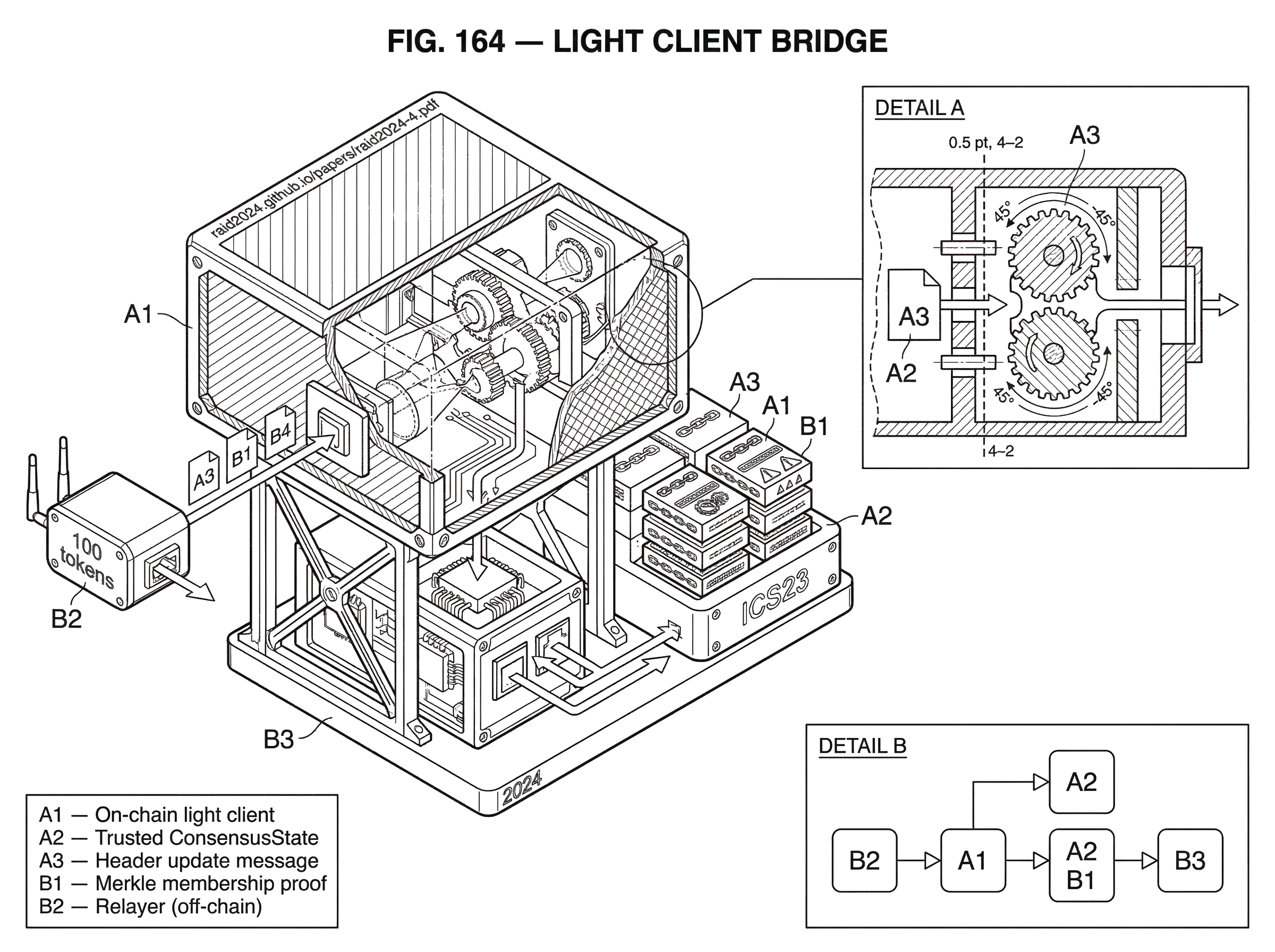
light client bridge is the name for a bridge that verifies another chain’s state cryptographically instead of trusting a separate validator committee or multisig to attest that something happened. That sounds like a small implementation detail, but it changes the basic trust model of bridging. In a committee bridge, the destination chain asks, in effect, “Do these bridge operators say the event on the source chain is real?” In a light client bridge, it asks a harder and better question: “Can this event be proved from the source chain’s own consensus and state commitments?”
That distinction exists because bridging has a fundamental problem. Blockchains do not natively share state. Ethereum does not automatically know what happened on a Cosmos chain; a Cosmos chain does not automatically know what finalized on Ethereum; Solana does not directly inherit another chain’s history. If a user locks tokens on one chain and expects assets, messages, or control on another, the destination chain needs some way to decide whether the source-chain event is genuine. A light client bridge is one answer to that problem: bring just enough of the source chain’s verification logic onto the destination chain so that the destination can check proofs for itself.
The appeal is obvious. If it works, the bridge can inherit much more of the source chain’s own security rather than introducing a fresh trust layer made of bridge signers. But the word if matters. Light client bridges are powerful precisely because they are mechanically strict: they depend on consensus-specific verification rules, correct proof formats, proper initialization, timely updates, and relayers that keep the client live. They reduce one class of trust assumptions, but they do not make interoperability magically assumption-free.
How does a light client bridge verify state instead of trusting bridge operators?
| Model | Verifier | What is trusted | Typical failure mode | Best for |
|---|---|---|---|---|
| External attestation | Validator set or multisig | Bridge operators' signatures | Key compromise or collusion | Fast multi-chain rollout |
| Light client | On-chain light client | Source chain consensus | Stale client or bugs | Trust-minimized security |
| Optimistic / fraud-proof | Off-chain watchers and challenges | Watchers to detect fraud | Missed fraud detection | Lower on-chain cost |
Most bridge designs are trying to answer the same question: did some event really happen on another chain? For a token bridge, the event might be “100 tokens were locked in this contract.” For a general messaging bridge, it might be “this packet was committed under this path” or “this call was authorized and executed.” The destination chain must not accept that claim just because a user says so. It needs evidence.
There are two broad ways to get that evidence. The simpler way is to appoint external verifiers (a multisig, validator set, MPC network, or committee) and accept their signatures as the truth source. This is operationally convenient, which is why it is common, but it creates a new security perimeter. If enough signers are corrupted, compromised, or fooled, the bridge can mint or release assets that were never really backed. Incidents like the Ronin compromise make the mechanism vivid: if a threshold of bridge validators can be captured, forged withdrawals can follow.
A light client bridge takes the opposite approach. Instead of trusting who says the event happened, it verifies whether the event is included in the source chain’s committed state, using a light client of that source chain on the destination chain. This is why some literature calls the model native verification. The destination chain keeps a compact, trusted view of the source chain (usually recent headers or consensus states) and checks inclusion proofs against that view. If the proof is valid and the light client accepts the source-chain updates that led to that state root, the destination chain can act.
The compression point is this: a light client bridge replaces bridge-operator trust with source-chain verification. The bridge is no longer primarily secured by a separate attestation network. It is secured by the correctness of the embedded light client, the validity of the submitted proofs, and the security assumptions of the source chain’s own consensus.
What does an on-chain light client store and verify?
The phrase light client can sound hand-wavy, so it helps to make it concrete. A full node re-executes and stores enough information to independently track the whole chain. A light client keeps only the minimum trusted information needed to verify future updates and authenticate specific pieces of state.
In IBC’s model, this minimum is described as a pairing of a validity predicate and a trusted state. The trusted state is often called a ConsensusState: a compact view of the source chain at some height that contains enough information to validate later updates. The validity predicate is the verification algorithm that decides whether a relayed update (usually a header or client message) is acceptable. Together, they let the destination chain say: given a state I already trust, does this new state follow according to the source chain’s consensus rules?
That is why IBC defines clients as on-chain light clients. An IBC client tracks another blockchain’s consensus states and the proof specifications needed to verify proofs against them. The details vary by client type. A Tendermint-based client stores things like the latest trusted height, trust parameters, validator-set commitments, timestamps, and proof specs. An Ethereum beacon-chain light client tracks finalized headers and current or next sync committees. These are different concrete mechanisms, but they serve the same function: establish a compact verification root that later proofs can anchor to.
The key thing a reader might otherwise miss is that a light client does not usually prove every transaction directly. It proves a chain of claims. First, “this newer header is valid given what I already trust.” Then, “this state root inside that trusted header is authoritative.” Then, “this value or non-value exists at this state path under that root.” The bridge works because those claims compose.
How does a light client bridge move a lock or packet from one chain to another?
A light client bridge has an off-chain component and an on-chain component, and they play different roles. The off-chain component is usually a relayer. The relayer is not supposed to be trusted for correctness; it is mainly trusted for delivery. It watches the source chain, gathers updates and proofs, and submits them to the destination chain. The on-chain component is the verifier: the light client plus the bridge logic that consumes verified state.
A simple narrative makes the mechanism clearer. Imagine a user locks tokens on Chain A and wants a representation or action on Chain B. Chain A records that lock event in state. Because blockchain state is committed by a Merkle root or similar commitment in a block header, that lock record is not just an application-level fact; it is also part of the chain’s cryptographically committed state.
A relayer sees this and submits two kinds of evidence to Chain B. First, it may need to update Chain B’s on-chain light client for Chain A by providing a new header or client message. Chain B checks that update using Chain A’s consensus-specific rules. If the update is accepted, Chain B now trusts a newer commitment root from Chain A. Second, the relayer submits a proof that the lock record exists at the relevant state path under that trusted root. If the proof verifies, Chain B can mint wrapped tokens, release escrow, execute a message, or acknowledge a packet.
Notice what the relayer cannot do if the system is working correctly. It cannot fabricate a lock record, because the proof would not match the trusted root. It cannot fabricate the trusted root, because the light client would reject an invalid header update. It cannot simply assert “trust me”; it has to provide cryptographic evidence that composes all the way back to a previously trusted state.
This is exactly how IBC is structured. Chains commit data to well-defined paths, relayers monitor those paths and submit the data plus proof, and on-chain light clients interpret and verify the proof bytes. Connections in IBC exist to establish that each side is using the correct light client for the other side, after which cross-chain verification can proceed on top of that trust anchor.
Why do proof formats and Merkle proofs matter for light client bridges?
The bridge’s safety does not come just from “having a light client.” It comes from the combination of a trusted consensus state and a proof system that correctly binds application data to that state. In many systems this proof is a Merkle proof, or a chain-specific variant of one.
Suppose the source chain’s block header commits to a root R. A proof of membership says, in effect, “if you hash this key-value pair upward through these sibling nodes using this exact tree rule, you get R.” Then the destination chain can trust that the key-value pair really was in source-chain state at that height. A proof of non-membership says the opposite: this key was absent under that root. Both matter. Bridges often need to prove not only that a packet exists, but also that an acknowledgement or receipt does not yet exist.
In the Cosmos ecosystem, ICS23 provides a generic binary representation for Merkle proofs meant for IBC and light-client verification. That standardization matters because proof verification is brittle. A proof format must specify the hashing rules, path encoding, leaf structure, and ordering assumptions precisely enough that two implementations cannot “verify” different things. ICS23 explicitly supports existence and non-existence proofs, but it also imposes constraints: supported stores must be lexicographically ordered, and some database designs (including tries that do not keep the key in the leaf, such as Ethereum’s Patricia trie) do not fit neatly without custom handling.
This is a good place to separate fact from intuition. The fact is that proof bytes are often passed to the client implementation as opaque bytes, and the client is responsible for interpreting and verifying them correctly. The intuition is that a proof is only meaningful relative to a verifier that understands exactly what structure produced it. So “proof verification” is not a generic checkbox. It is consensus- and state-model-specific code, and errors there can be fatal.
How do different consensus models change light client bridge verification?
| Consensus type | Verification root | Finality model | Client complexity | Common risk |
|---|---|---|---|---|
| Tendermint (BFT) | Signed headers + validator set | Deterministic BFT finality | Moderate validator-set updates | Validator equivocation |
| Beacon (Ethereum) | Finalized headers + sync committee | Sync-committee aided finality | High aggregate-signature logic | Limited slashing/accountability |
| Probabilistic (PoW/PoS) | Block headers + confirmation depth | Probabilistic confirmations | Policy-based confirmation thresholds | Reorgs and long-range attacks |
The phrase light client bridge can sound like a single design pattern, but in practice it is a family of designs. The invariant is always the same (verify source-chain state on the destination chain with minimal trust) yet the mechanism depends heavily on the source chain’s consensus and finality model.
For chains in the Tendermint family, the light client checks whether new headers are correctly signed by an appropriate validator set, whether trust periods and unbonding assumptions are respected, whether timestamps make sense, and whether there is evidence of equivocation or other misbehaviour. The IBC Tendermint client specification defines persistent fields such as chainID, trustLevel, trustingPeriod, unbondingPeriod, latestHeight, frozenHeight, maxClockDrift, and proofSpecs. A relayer submits a header that includes not just the new signed header but also a trusted height and trusted validator information to update from. The client verifies that transition before accepting the new consensus state.
For Ethereum’s beacon chain, the light-client mechanism looks different because Ethereum’s post-merge consensus exposes different verification hooks. The Altair light-client sync protocol uses sync committees: subsets of validators whose aggregate signatures attest to beacon headers for constrained verifiers. A light client stores finalized headers and current or next sync committees, and it accepts updates when committee participation crosses a supermajority threshold. Initialization also requires a trust anchor: a trusted block root and a Merkle proof that the supplied sync committee matches the beacon state for that header.
These two examples illuminate the same principle from opposite ends. The bridge is “trust-minimized” only to the degree that its on-chain verifier faithfully encodes the source chain’s real safety conditions. There is no chain-agnostic shortcut that works equally well for all architectures. Deterministic-finality BFT chains, probabilistic-finality chains, and committee-based light-client protocols all require different validity predicates and different operational choices about when a state is safe enough to bridge against.
Misbehaviour, freezing, and why safety often means stopping
A light client bridge needs not only an update rule but also a failure rule. If the source chain exhibits misbehaviour that the client can detect, the safe response is often to stop trusting new updates. In IBC, every light client is expected to have a misbehaviour predicate. If misbehaviour is detected, the client should be frozen so that future consensus states cannot be generated from it.
This can feel unsatisfying at first. Why should a bridge react to trouble by halting? Because the bridge’s job is not to remain available at all costs; its first job is to avoid accepting contradictory histories. If a client can prove that two conflicting headers at the same height would both have been accepted, then the host chain has learned something important: its verification root is no longer trustworthy. Continuing as if nothing happened would be worse than pausing.
The Tendermint client specification makes this concrete. Misbehaviour can consist of two conflicting headers at the same height that the light client would have considered valid, or of certain timestamp inconsistencies. Once such evidence is accepted, the client freezes. That means a light client bridge is often safer than committee bridges because it fails conservatively. Instead of asking users to trust that operators will self-report a consensus failure, it encodes a rule that can stop the bridge automatically when contradictory evidence appears.
But there is a cost. Recovery is not fully automatic. Some situations may require governance, manual intervention, or a trusted reset path to reinitialize or unfreeze the client. That is not a bug in the abstract idea; it reflects a deeper truth that no bridge can algorithmically resolve every upstream consensus crisis without assumptions. Sometimes the honest answer is that trust has to be re-established, not merely computed.
Do relayers need to be trusted in a light client bridge, and what do they actually do?
A common misunderstanding is that light client bridges remove off-chain actors. They do not. They change what those actors are allowed to do.
Relayers are still necessary because blockchains do not spontaneously import each other’s headers and proofs. In IBC, relayers are the “physical” connection layer: they watch state on each chain, construct the appropriate datagrams, and submit them to the counterparty chain. In a light client bridge, relayers usually deliver client updates, membership proofs, acknowledgements, and timeout information.
The right way to think about relayers is that they are couriers, not judges. If a relayer goes offline, becomes lazy, or censors certain packets, the bridge may stall or time out. That is a liveness problem. If a relayer lies about source-chain state, the proofs should fail verification. That is why light client bridges can tolerate untrusted relayers for safety while still depending on them operationally.
This distinction matters in practice. IBC documentation notes that relayer failure can cause timeouts and, in some channel configurations, closures. Ordered channels are especially sensitive because if a packet times out, later packets may become blocked. So while light client bridges sharply reduce custodial trust, they still need robust relay infrastructure, multiple operators, and good incentives if they are to remain usable.
What applications and transfers do light client bridges support?
The mechanism is general because what the destination chain verifies is just source-chain state. That can represent many application-level facts.
Token transfers are the most familiar use. A chain can verify that assets were escrowed, burned, or otherwise committed on another chain, then mint or release corresponding assets locally. This is how many people first encounter the idea of a bridge.
But the more interesting use cases go beyond wrapped assets. In IBC, the same light-client-based verification model underlies packet delivery for fungible token transfers, NFT transfers, and interchain accounts. The application layer can remain relatively clean because the transport and authentication layer handles client, connection, and proof verification. That modularity is important: once a chain can verify another chain’s state transitions and storage proofs, “bridging” becomes a broader interoperability primitive for messages, acknowledgements, account control, and state-dependent application logic.
This is also why light client bridges matter even when no asset is being wrapped. They are a way to let one chain make stateful decisions based on another chain’s cryptographically proved state without introducing a separate committee as a universal translator.
When do light client bridges fail or become unsafe?
The strongest marketing line about light client bridges is that they inherit the source chain’s security. That is directionally true, but incomplete.
First, they inherit the source chain’s assumptions, not some abstract notion of perfect security. If the source chain can finalize conflicting histories, suffer a 51% or long-range attack, or present ambiguous main-chain identification, the bridge can be fooled to the same extent as the light client. Research surveys on bridge security emphasize this directly: inclusion-proof bridges depend on the source chain’s consensus assumptions, and practical mitigations often require waiting for the full confirmation depth appropriate to that chain. For probabilistic-finality chains, “safe enough to bridge” is a policy choice layered on top of consensus statistics, not a universal constant.
Second, light client state can become stale. An outdated client may reject valid updates, fail to detect current reality, or in badly designed systems enable unsafe behavior if confirmation assumptions are mishandled. Some client types are time-sensitive by design. Tendermint-style clients, for example, depend on trusting periods and unbonding periods; if updates stop for too long, the client may no longer be safely updatable.
Third, the implementation burden is real. The most secure bridge design on paper is not always the one most widely deployed because every supported chain may require a different verifier, proof format, and set of operational heuristics. That is one reason many production bridges have historically chosen external verification instead. The trade-off is not hard to see: committee bridges are easier to extend across many chains, while light client bridges are harder to implement correctly but avoid the central weakness of signer-based custody.
Fourth, bugs in verification code remain bugs. A light client bridge can fail catastrophically if its proof verifier, update logic, or chain-specific assumptions are wrong. The Wormhole exploit was not a light-client-bridge failure specifically, but it is still instructive: the verification path itself is a critical attack surface. If account validation, proof interpretation, or header checks are flawed, cryptographic design does not save a flawed implementation.
When should projects use ZK light clients and what are the trade-offs?
| Approach | On-chain cost | Trust model | Implementation complexity | Best for |
|---|---|---|---|---|
| On-chain verification | High gas cost | On-chain consensus verification | Moderate verifier code | Chains tolerating high gas |
| ZK light client | Low verification gas | Proofs of source-consensus | High prover and circuit work | EVM chains with gas limits |
| Committee / proxy bridge | Low gas cost | Trust in operators | Low engineering effort | Quick multi-chain coverage |
One recurring obstacle is cost. On some chains, especially EVM chains, verifying another chain’s headers and proofs directly on-chain can be expensive. That has pushed developers toward ZK light clients, which keep the same high-level trust goal but change the computational strategy.
The idea is straightforward. Instead of verifying every consensus step directly in the destination contract, an off-chain prover generates a Zero-Knowledge Proofs that the source-chain header transition is valid according to the required rules. The destination chain verifies the succinct proof, which is much cheaper than re-running the full verification logic on-chain. Projects such as Tendermint ZK light clients for Solidity follow this model: a prover generates a proof for header validity, a relayer submits it, and the contract verifies that proof plus any remaining state membership proofs.
This does not change the bridge’s fundamental purpose. It is still a light client bridge because the destination chain is still verifying source-chain state cryptographically rather than trusting a committee. What changes is the performance profile and engineering split between off-chain proving and on-chain verification.
The limitation is also straightforward: ZK versions add proving infrastructure, circuits, and new implementation complexity. So they trade direct verification cost for prover complexity. That can be an excellent trade in some environments, but it is not free.
Light client bridge vs committee (multisig) bridge: what's the trust difference?
It is useful to end the comparison cleanly. A canonical bridge is often the bridge endorsed or operated by a protocol or ecosystem as the default path for moving assets or messages. That tells you something about social legitimacy or protocol integration. It does not by itself tell you the verification model.
A light client bridge is defined by how it verifies. If it verifies another chain’s state through an on-chain light client and proofs, it is a light client bridge whether or not it is considered canonical by any community. Conversely, a bridge can be canonical and still rely on a multisig or external validator set.
So the right comparison is not “official” versus “unofficial.” It is cryptographic verification versus external attestation. Light client bridges sit on the cryptographic side of that line.
Conclusion
A light client bridge exists because cross-chain systems need a way for one blockchain to accept facts about another without blindly trusting a new set of intermediaries. Its central move is simple but profound: run a compact verifier of the source chain on the destination chain, update that verifier with source-chain-consistent headers, and accept cross-chain actions only when they can be proved against trusted source-chain state.
That gives light client bridges their distinctive strength. They do not ask users to trust bridge operators as the ultimate source of truth. They ask the destination chain to check the source chain’s own commitments and consensus evidence directly.
The price is complexity. Every supported chain needs the right client logic, the right proof rules, safe initialization, timely updates, and careful handling of misbehaviour and liveness. So the memorable version is this: a light client bridge is not a bridge with no trust; it is a bridge that tries to place trust where it already belongs: in the source chain’s consensus, verified on-chain.
How do you move crypto safely between accounts or networks?
Light Client Bridge should make you slower and more deliberate before moving assets between networks or accounts on Cube Exchange. Confirm the trust model, destination, and settlement path before you send funds.
- Identify the source network, destination network, and exact asset you plan to move.
- Review the trust assumption or bridge design issue that Light Client Bridge highlights before you initiate the transfer.
- Double-check the destination address, network selection, and expected settlement path.
- Send a small test transfer first when the amount is meaningful, then continue only after the transfer settles as expected.
Frequently Asked Questions
A light client bridge verifies events by running a compact verifier of the source chain on the destination chain and accepting only cryptographic proofs anchored to that verifier, whereas committee/multisig bridges accept attestations from an external set of signers; the former replaces bridge-operator trust with source-chain verification while the latter introduces a new validator trust perimeter.
On-chain light clients keep a compact trusted state (often called a ConsensusState) and a validity predicate: they store things like a latest trusted height, validator-set commitments or sync committees, timestamps and proof specs, and they verify header updates plus Merkle-style inclusion/non-inclusion proofs against that trusted state.
Relayers are required for liveness but are untrusted for correctness: they courier headers and proofs to the destination chain, and if they lie the client’s cryptographic verification should reject the submission, but if they go offline or censor packets the bridge can stall or time out.
If a client detects provable misbehaviour (for example two conflicting headers at the same height), the safe response is typically to freeze the client so it stops accepting updates; recovery often requires governance or a trusted reset rather than an automatic restart.
Proof format matters because a proof only means anything relative to a verifier that understands the exact hashing rules, path encoding and leaf layout; standards like ICS23 enforce constraints (e.g., lexicographic stores, leaves containing keys) and warn that some state models, such as Ethereum’s Patricia trie, don’t fit ICS23 without custom handling.
Light client bridges inherit the source chain’s consensus assumptions and failure modes - they are as vulnerable to attacks tied to that consensus (e.g., long‑range, 51% or probabilistic finality ambiguities) as the source chain itself, so safe bridging often requires chain-specific confirmation policies.
ZK light clients replace expensive on-chain consensus verification with an off-chain prover that produces a succinct Zero-Knowledge Proofs of header/transition validity; this lowers on-chain cost but adds prover infrastructure, circuit complexity, and implementation risk.
Channel ordering affects liveness: ordered channels are especially sensitive because relayer failure or packet timeouts can block later packets and cause channel closure, so relayer availability and timeout handling are operationally important for bridge usability.
Related reading