What Is NEAR?
Learn what NEAR is, why it exists, and how its sharded proof-of-stake design, Nightshade architecture, and account model aim to scale blockchain apps.
Introduction
For the token explainer, see NEAR.
NEAR is a layer-1 blockchain designed to make decentralized applications fast enough, cheap enough, and simple enough to use at internet scale. That sounds like a familiar ambition because many smart-contract platforms want the same thing. What makes NEAR worth understanding is the way it tries to solve the problem mechanically: it does not just promise lower fees or better tooling, but reorganizes how the network processes state through sharding, while also redesigning the account model so users are not forced into the roughest parts of typical crypto UX.
The basic tension NEAR is addressing is easy to state. A blockchain becomes harder to use as it becomes more decentralized, because every node verifying everything creates a bottleneck. But if you relax verification too much, you stop getting the security properties that made the blockchain useful in the first place. NEAR exists in that gap. It is a proof-of-stake network that tries to preserve a single shared chain and coherent state transition logic while splitting the actual work across the network.
If you remember one idea, remember this: NEAR is trying to scale by making the chain look logically unified while making the underlying work physically partitioned. That is the core of its sharding design, called Nightshade, and much of the rest of the protocol makes more sense once that clicks.
Why does NEAR use sharding to scale blockchains?
A general-purpose blockchain has to do three things at once. It has to agree on transaction ordering, execute those transactions, and let users and applications interact with the results in a way that feels predictable. On simpler chains, each validator or full node may process essentially the same global workload. That keeps the model conceptually clean, but it means throughput is bounded by what a single machine, or at least a single verification path, can handle.
That is fine when usage is small. It becomes a problem when the chain is supposed to host games, social apps, payments, markets, AI agents, or anything else that generates many small actions from many users. If every increase in usage pushes fees up or slows confirmations down, the chain has not really solved for mainstream applications; it has only shifted scarcity around.
NEAR’s answer begins from a first principle: not every participant needs to execute every piece of state, as long as the network can still agree on one valid overall history. That suggests sharding. But sharding is not only a throughput trick. It creates new problems around data availability, cross-shard communication, and the risk that a small group assigned to a shard could misbehave or be attacked. So the hard part is not saying “split the network into pieces.” The hard part is doing that without turning the protocol into a set of loosely connected mini-chains.
Is NEAR a layer‑1 proof‑of‑stake blockchain?
At the highest level, NEAR is a layer-1 blockchain. That means it is the base network itself, not a rollup or appchain settling to another chain. Applications deploy contracts directly to NEAR, users hold NEAR accounts, and validators secure the protocol through staking.
The security model is proof of stake. Validators lock up NEAR tokens to participate in block production and validation. The protocol documentation describes validators as the independent participants who process transactions and secure the network. Delegators can stake with validators, which means the security budget comes from economic exposure rather than proof-of-work computation. That is the direct reason NEAR presents itself as more energy-efficient than proof-of-work systems: the network is paying for capital at risk, not for continuous energy burn.
This does not make security automatic. Proof of stake still depends on incentives, validator participation, and slashing or removal for malicious behavior. NEAR’s documentation states that dishonest validators can be removed and their staked tokens burned. The exact operational details matter to validators and delegators, but the conceptual point is simpler: the chain is secure to the extent that enough stake follows the protocol and enough misbehavior can be detected and punished.
NEAR’s validator set is also not flat in responsibility. Its documentation distinguishes between the top validators responsible for producing and validating blocks and chunks, and other validators that can act as chunk validators with lower hardware requirements. That reflects the protocol’s sharded design: different participants can take on different slices of the work without every participant having to carry the full state burden.
How does Nightshade sharding work on NEAR?
| Model | Single logical chain? | Per-block physical chunks? | Validator workload | Cross-shard semantics |
|---|---|---|---|---|
| Nightshade (NEAR) | Yes | Yes | Per-shard execution | Unified semantics |
| Parallel mini-chains | No | Yes, separate | Each chain full execution | Weaker atomicity |
| Full replication (no sharding) | Yes | No | All nodes full work | Strong atomicity |
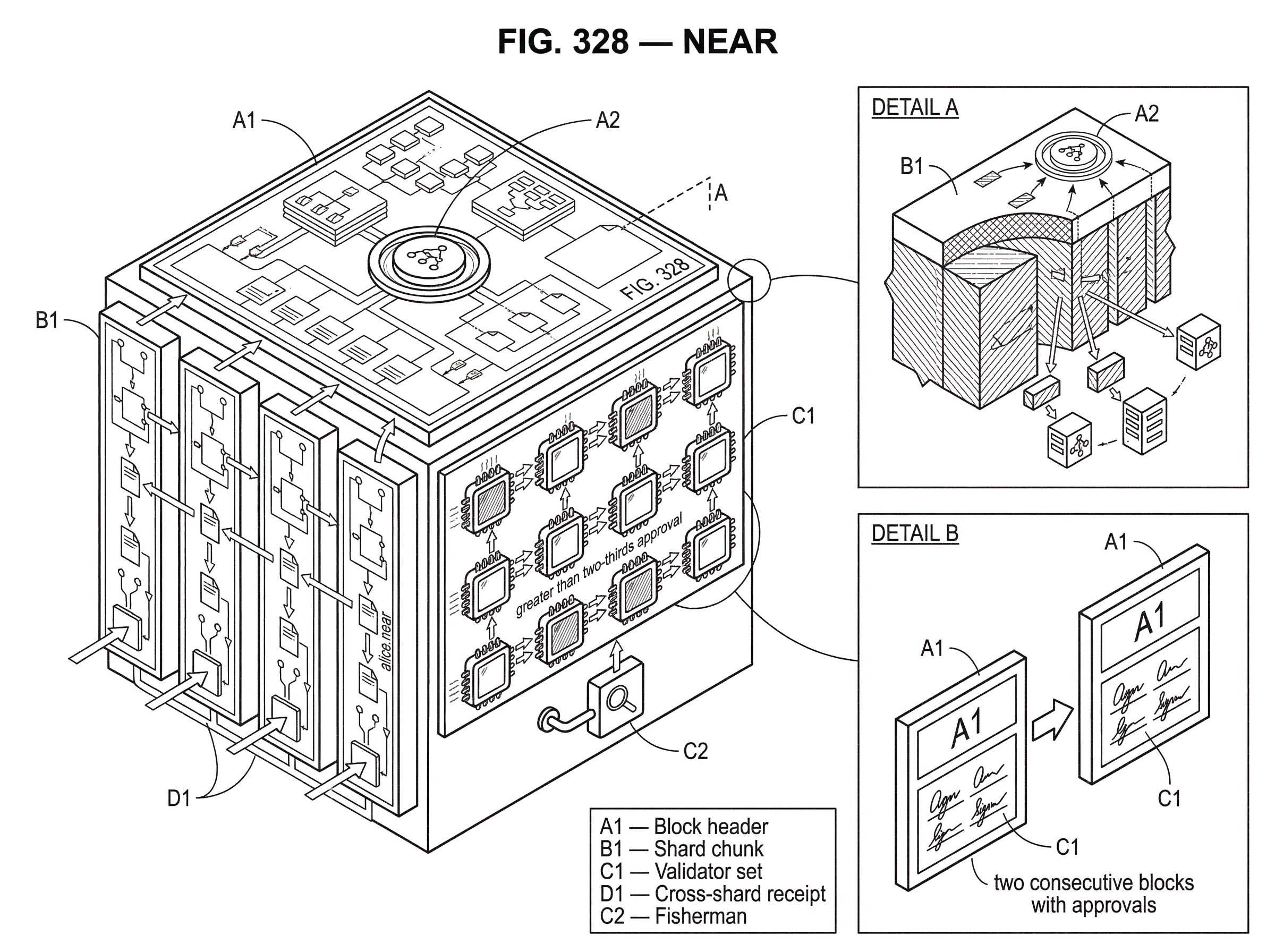
The most important technical idea in NEAR is Nightshade, the protocol’s sharding architecture. Many people hear “sharded blockchain” and imagine several semi-independent chains stitched together by a coordinator. That is not quite the model here. In Nightshade, the system is modeled as one logical blockchain, where each block contains the transactions and state transitions for all shards, but the block is physically split into per-shard chunks.
That distinction matters. Logically, there is still one canonical chain and one fork-choice process. Physically, no participant has to download the full state and full contents for every shard. Instead, participants maintain and validate the shard state relevant to their role. So the protocol is trying to get the best of both worlds: a unified chain for consensus and application semantics, and partitioned execution for scalability.
Here is the mechanism in ordinary language. Suppose the network is divided into shards, each responsible for a portion of the global state. For a given block, each shard has a corresponding chunk containing that shard’s transactions and state transition information. Those chunks together represent the full logical contents of the block. A validator assigned to one shard does not need to execute every other shard’s transactions in detail. But the chain as a whole still advances as one sequence of blocks.
This is the idea that makes NEAR different from a simple “many chains in parallel” picture. Applications can still reason about being on one network, and consensus still selects one chain history. The scaling gain comes from reducing how much any one validator must directly process.
The tradeoff is that once work is partitioned, the protocol must make it hard to hide bad data or invalid state transitions inside a shard. That is why the Nightshade design pays so much attention to data availability and validity challenges.
How does NEAR ensure data availability and validity in sharding?
| Mechanism | Purpose | Bandwidth cost | When used |
|---|---|---|---|
| Erasure coding | Prevent data withholding | Extra parts distribution | On chunk publish |
| Fisherman challenges | Prove invalid chunks | Bounded proof size | Within challenge window |
| Intermediate state roots | Enable succinct proofs | Small header overhead | Embedded in chunks |
| Fast cross-shard receipts | Improve UX latency | Rollback risk | Applied immediately |
A sharded chain breaks if chunk producers can publish commitments to data without making the actual data obtainable. In that case, the network might agree to blocks whose shard contents cannot be reconstructed or checked. Nightshade addresses this with an erasure-coding approach. A chunk producer takes a shard chunk, erasure-codes it into parts, distributes those parts across block producers, and commits to them with a Merkle root. The point of erasure coding is that the network does not need every copy of the chunk to survive; enough parts can reconstruct the original data.
That mechanism is about more than redundancy. It is a way to prevent data withholding from becoming an invisible attack. If honest participants can recover the chunk from distributed parts, they can validate it, challenge it, and preserve the chain’s safety assumptions.
Validity is handled through a fisherman-style challenge model in the Nightshade design. A fisherman is a participant who maintains a shard’s state and can challenge an invalid chunk during the challenge window. The whitepaper describes a way to make these challenges succinct by including intermediate state roots inside chunks. Instead of proving an entire shard history wrong all at once, a challenger can point to a bounded piece of the transition and provide the relevant state data plus Merkle proofs.
The reason this matters is practical. A validity system is only useful if honest participants can actually afford to use it. If challenging fraud required downloading huge histories and posting enormous proofs, the right to challenge would exist mostly on paper. By bounding how much state a transaction segment can touch for challenge purposes, NEAR tries to make shard validity enforceable by more than the largest operators.
This does not eliminate complexity. The Nightshade design acknowledges tradeoffs. For example, fast cross-shard receipts can be applied before the challenge period fully closes, which improves responsiveness but means an invalid source chunk discovered later can force rollback of dependent state. That is a real engineering compromise: better latency in the normal case, more complicated recovery in rare adversarial cases.
How does consensus and finality work on NEAR?
Sharding explains how work is divided, but the network still needs to agree on which chain is the chain. NEAR’s consensus specification describes a heaviest-chain approach with approvals from block producers, together with a Doomslug-derived finality rule.
The useful intuition is that the protocol separates two questions that people often blur together. The first question is, “Which block should the network build on right now?” That is a fork-choice question. The second is, “When can users treat a block as final and not realistically reversible?” That is a finality question. NEAR’s design uses approvals and chain weight for the first, while the formal finality rule gives a concrete answer for the second.
The protocol defines two approval types: endorsements, which refer to a specific previous block hash, and skips, which refer to a previous height when a block at some height is skipped. This asymmetry is not cosmetic. The specification explicitly notes that endorsements and skips cannot simply be unified without breaking safety or liveness. In other words, the network needs a way to keep moving when producers have divergent local views, but it also needs signatures to mean specific enough things that equivocation can be identified.
A block producer for a height can produce a block only once it has approvals from block producers representing more than two-thirds of stake for that target height. Near epoch boundaries, there are additional rules so the handoff between validator sets does not create unsafe transitions. The broad pattern is familiar from Byzantine fault tolerant proof-of-stake systems: greater than two-thirds approval is the threshold that supports safety, and conflicting final histories imply that more than one-third of stake must have signed inconsistently.
NEAR’s finality rule is notably concrete. A block becomes final when there are two consecutive blocks on top of it with consecutive heights in the chain view under consideration. Formally the spec defines this relative to a chain extension, but the intuition is simple: once the chain has built two proper steps on top of a block under the approval rules, that block is treated as final.
This should be understood carefully. Finality here is not magic immunity from all imaginable faults; it is a statement conditioned on the protocol assumptions. The spec’s safety theorem says that if two conflicting blocks were both final, more than one-third of block producers in some epoch must have issued conflicting signatures. So finality is as strong as the assumption that less than one-third of stake behaves Byzantine.
NEAR marketing materials also make strong low-latency finality claims. Those are useful directional signals, but they depend on conditions and measurement choices. The protocol specification is the firmer foundation: the chain is built to reach fast confirmation and finality under normal network conditions because approval collection and block progression are designed to move quickly, but exact latency numbers should be treated as operational claims rather than timeless protocol truths.
How does NEAR process cross‑shard activity in practice?
Imagine a game on NEAR with many users trading items, minting assets, and updating profiles at the same time. On a non-sharded chain, every validator would need to process the whole stream of activity. If usage spikes, the entire network competes over one execution lane.
On NEAR, that activity is distributed across shards according to where the relevant state lives. A shard responsible for one subset of accounts produces a chunk for the current block containing the transactions that affect its state. Another shard does the same for a different subset. Those chunks are separate in physical handling, but together they form the logical contents of one block in the chain.
Now suppose a player action in one shard creates a receipt that another shard must consume. NEAR can propagate that cross-shard effect without pretending the two shards are independent universes. The destination shard can apply the receipt quickly rather than waiting through a long global settlement ceremony. That helps the application feel responsive. But the protocol design also recognizes a cost: if the originating chunk is later proven invalid during the challenge process, dependent effects may need to be rolled back. The user experience is faster because the protocol is willing to optimize for the honest case while keeping a validity backstop.
That is a recurring NEAR pattern. The chain is not trying to avoid all complexity by slowing everything down to the safest possible pace. It is trying to confine complexity inside protocol mechanisms so applications can get lower latency and higher throughput.
Why does NEAR focus on named accounts, access keys, and usability?
A blockchain can be technically elegant and still fail if ordinary users cannot survive the interface. NEAR is unusually explicit about this problem. Its developer-facing materials emphasize named accounts, access keys, social login options, low fees, and account abstraction features.
Named accounts are the easiest place to see the design philosophy. Instead of forcing every user interaction to begin from a long hexadecimal address, NEAR accounts can look like alice.near. That does not change the underlying need for cryptographic control, but it changes how identity is presented. The protocol is saying that human-readable naming is not a cosmetic extra; it is part of making a smart-contract platform usable outside specialist circles.
Access keys deepen that idea. A NEAR account can authorize different keys with different permissions, which makes it possible to separate broad account control from narrower application-specific actions. The practical consequence is that applications can offer smoother flows without asking users to expose their master authority every time. This is part of why NEAR often talks about account abstraction and simpler onboarding. The real mechanism is not just “better UX” in the abstract; it is a more flexible account model.
This also explains how NEAR can support claims about hiding wallets, bridges, or token friction behind chain abstraction and intents in newer product framing. The homepage language is ambitious, especially where it says users need no wallets, no bridges, and no tokens. That should not be read as the laws of blockchain economics disappearing. Someone still signs, routes, executes, and pays costs somewhere in the system. But the direction is clear: NEAR wants the protocol and surrounding infrastructure to absorb more of the complexity that users normally see directly.
What types of applications and languages run on NEAR?
NEAR is a smart-contract platform, so the direct answer is: developers build applications that need persistent on-chain state, programmable asset logic, and user accounts. The official materials point developers to Rust and JavaScript smart contracts, and NEAR also highlights its broader tooling ecosystem.
The language choice matters because developer adoption is often limited less by raw protocol performance than by the distance between existing engineering habits and the target platform. Supporting JavaScript alongside Rust is a usability choice aimed at widening the set of builders who can write contracts without first crossing a large language barrier.
NEAR also connects to neighboring ecosystems rather than pretending they do not exist. Aurora provides an EVM-compatible environment associated with NEAR, allowing Ethereum-style applications and tooling to run with lower-fee, higher-performance assumptions tied to NEAR infrastructure. That is important conceptually. It means NEAR is not only betting on native contracts and native accounts; it is also providing a route for teams already shaped by the Ethereum toolchain.
The same pattern appears in interoperability. The Rainbow Bridge is described as a trustless, decentralized Bridge between NEAR and Ethereum, with security assumptions tied to honesty thresholds on both sides. This is the right way to think about bridges in general: not as magical teleportation layers, but as systems whose safety inherits assumptions from multiple chains at once. In NEAR’s case, that means cross-chain usage is part of the ecosystem story, but not free of additional trust boundaries and operational risk.
What is NEAR's strategic focus (AI agents and agentic apps)?
NEAR’s current public positioning leans heavily toward being a platform for AI-native applications and autonomous agents. The official homepage describes NEAR as “The Blockchain for AI,” with agents acting on behalf of users, and the blockchain serving as the backend for identity, trust, and data handling.
The important thing to notice is that this is not a separate protocol from the rest of NEAR so much as a new framing layered on top of the same underlying design choices. If you believe AI agents will need to hold assets, coordinate actions, and transact across systems, then a sharded proof-of-stake chain with flexible accounts and chain abstraction starts to look like fitting infrastructure. NEAR is effectively arguing that the hard part of agentic applications is not only model inference, but verifiable action, ownership, and coordination.
Some of the AI-related claims on the homepage, such as encrypted model execution and verifiable compute, are presented at a high level without enough technical detail there to treat them as fully explained protocol features. So it is better to read them as part of the platform direction than as settled core mechanics on the same footing as Nightshade or the consensus specification.
What are the limitations and trade‑offs behind NEAR's marketing claims?
| Claim | Marketing phrasing | Practical caveat | Implication |
|---|---|---|---|
| Infinite scalability | Infinitely scalable | Coordination and data limits remain | Scales with tradeoffs |
| Fast finality | Very fast finality claims | Depends on network conditions | Latency varies in practice |
| No wallets or tokens | No wallets. No bridges. No tokens | Signing and fee economics still exist | UX hides but does not remove costs |
| Carbon neutrality | Certified carbon-neutral | Depends on offset accounting and assumptions | Claims need independent verification |
NEAR’s official materials make several strong claims: infinite scalability, very fast finality, chain abstraction that removes user friction, environmental superiority, and extensive reliability. These claims point to real design intentions and, in some cases, real protocol mechanisms. But they should not all be treated as equally precise.
For example, “infinitely scalable” is best understood as an aspiration grounded in sharding, not as a literal theorem that no bottlenecks remain. Sharded systems still face coordination costs, data availability constraints, cross-shard latency, and validator assignment questions. Dynamic resharding can improve capacity as load changes, but it does not repeal networking and state management limits.
Likewise, fast finality claims are meaningful only relative to network conditions and the exact layer of finality being measured. And chain abstraction claims like “no wallets, no bridges, no tokens required” usually mean that those components are being hidden or handled by infrastructure, not that cryptographic authorization and fee economics have ceased to exist.
Even the cleaner parts of the protocol have tradeoffs. Nightshade’s challenge-based validity system allows efficient sharded operation, but challenge windows and possible rollbacks mean there is a difference between quick practical responsiveness and irrevocable completion in the strongest sense. That does not make the design unsound. It just means the right mental model is not “NEAR solved scaling once and for all.” The right model is “NEAR chose a set of engineering compromises to make a unified smart-contract chain scale better without giving up verifiability.”
Conclusion
NEAR is a sharded proof-of-stake layer-1 blockchain built around a clear idea: a network can stay logically unified even if the underlying execution work is divided. That is the purpose of Nightshade, and it is the key to understanding why NEAR looks the way it does.
Around that core, NEAR adds fast-approval consensus, a usability-focused account model, developer tooling in familiar languages, and interoperability layers like Aurora and Rainbow Bridge. The result is a network aimed less at crypto purism than at making on-chain applications feel practical.
The shortest accurate summary is this: NEAR exists to make smart-contract infrastructure scale without making users and developers pay the full price of blockchain complexity. Whether it succeeds in every claim is still an empirical question. But the architecture is coherent, and once you see the logic of “one chain logically, many shards physically,” the rest of NEAR starts to make sense.
How do you buy NEAR?
Buy NEAR on Cube Exchange by funding your Cube account and placing a spot order on the NEAR market. The Cube workflow keeps execution on the platform: fund your account, open the NEAR spot market, choose the order type that fits your execution preference, and submit the trade.
- Fund your Cube account with fiat via card or bank transfer, or deposit a supported stablecoin like USDC to your Cube wallet.
- Open the NEAR/USDC (or NEAR/USD) spot market on Cube.
- Choose an order type: use a market order for immediate execution or a limit order to control your entry price and reduce slippage.
- Enter the NEAR amount or the USDC amount to spend, review estimated fees and price impact, then confirm and submit the order.
Frequently Asked Questions
Nightshade models the network as one logical blockchain where each block contains per-shard "chunks"; the chain and fork-choice remain unified, but the physical work is partitioned so validators only need to download and validate the shard state relevant to their role rather than every shard's full state.
NEAR prevents data withholding by erasure‑coding each chunk into many parts, distributing those parts across block producers, and committing to the chunk with a Merkle root so honest participants can reconstruct and validate the chunk from a subset of parts.
A fisherman is a participant who watches shard state and can issue a validity challenge during a challenge window; challenges are made practical by including intermediate state roots and bounded state segments so a challenger can point to a limited transition and provide succinct Merkle proofs rather than redoing vast histories.
A block is considered final after the chain has two consecutive blocks built on top of it under the protocol's approval rules, and this finality guarantee depends on the usual proof‑of‑stake assumption that less than one‑third of stake behaves Byzantine and that approvals require more than two‑thirds of stake for a target height.
Applying cross‑shard receipts quickly improves responsiveness because destination shards can act before long global settlement, but the tradeoff is that if the originating chunk is later proven invalid during the challenge window, dependent effects may need to be rolled back, introducing recovery complexity in adversarial cases.
Named accounts make addresses human‑readable (e.g., alice.near) and access keys let an account grant limited permissions to different keys, enabling smoother onboarding and finer‑grained app interactions without exposing a master key for every operation - these features are intended as concrete account abstraction and usability improvements.
"Infinitely scalable" is an aspirational shorthand: Nightshade and dynamic resharding are intended to increase capacity, but sharded systems still face practical limits such as coordination costs, data‑availability constraints, cross‑shard latency, and validator assignment issues, so scalability is improved but not literally unbounded.
The homepage slogan "No wallets. No bridges. No tokens required." is marketing‑forward and not a literal elimination of on‑chain economics or cryptographic authorization; the available materials do not fully explain how transaction economics and security are handled, so this phrasing is best read as an intent to hide complexity via infrastructure rather than a technical proof that those components no longer exist.
Aurora is an EVM‑compatible environment associated with NEAR to let Solidity/Ethereum tooling run on NEAR infrastructure, while the Rainbow Bridge connects NEAR and Ethereum in a trustless, decentralized way whose safety inherits assumptions from both chains - meaning cross‑chain usage introduces extra trust and operational boundaries rather than eliminating them.
The high‑level docs state that misbehaving validators can be slashed and that different validator roles (e.g., chunk validators vs block producers) exist, but they do not publish exact slashing formulas or full hardware specs inline - operational details and numeric parameters are deferred to dedicated validator/operator documentation and external sites like near‑nodes.io.
Related reading