What is Message Passing?
Learn what message passing is in blockchain interoperability, how cross-chain messages are verified, and why bridges and omnichain apps depend on it.
Introduction
Message passing is the mechanism that lets one blockchain cause something meaningful to happen on another blockchain without the two chains sharing a single global state. That sounds simple, but it hides the real puzzle: blockchains are built to agree internally, not externally. Ethereum validators do not automatically know what happened on Cosmos. A Solana program cannot just “read” a Polygon contract. If separate chains are supposed to remain sovereign, how can one chain safely react to events on another at all?
The answer is to stop thinking in terms of “chain A accesses chain B” and start thinking in terms of verified claims. A chain does not need the full state of another chain. Usually it only needs a narrowly defined fact: that a packet was committed, that a deposit occurred, that a governance vote passed, that a command was authorized, or that some bytes should be interpreted as instructions. Message passing is the discipline of creating that fact on one chain, transporting evidence about it, and verifying enough of that evidence on another chain to act.
That is why message passing sits underneath so many different interoperability systems. Token bridges use it to say, in effect, “tokens were locked there, so mint or release them here.” Interchain accounts use it to say, “this remote account authorized a call.” Generalized interoperability protocols use it to send arbitrary byte payloads between contracts or applications. Even when a product markets itself as a token bridge, an omnichain app framework, or a settlement network, the core mechanism is often still message passing.
The important thing to understand is that message passing is not a single protocol. It is a pattern with several possible trust models. IBC uses light clients and protocol-defined packets, with a transport layer for connection, authentication, and ordering, plus application layers for packet meaning. Wormhole uses signed attestations called VAAs produced by a Guardian network. Chainlink CCIP exposes arbitrary messaging and programmable token transfer on top of Chainlink’s oracle-style infrastructure. Hyperlane offers general message passing and lets developers choose or customize verification through interchain security modules. Polkadot’s XCM defines a message format and instruction language, while separate transport mechanisms such as XCMP deliver those messages.
The unifying idea is this: cross-chain interoperability works when the destination chain can decide, under its own rules, whether an external message is valid enough to execute.
Why can’t blockchains directly read each other’s state?
Within a single blockchain, applications feel composable because everyone writes into the same state machine. A lending protocol can inspect a token balance because both live inside one execution environment. Across chains, that common memory disappears. Each chain has its own consensus, finality rules, data model, and execution logic. There is no built-in syscall for “ask the other chain what just happened.”
This is the real reason message passing exists. The problem is not merely moving bytes between computers. The internet already solves that. The problem is creating a message that the destination chain can treat as authoritative enough to change state. If a message says “Alice locked 100 tokens on chain A,” then chain B should only mint a representation or trigger an action if it can verify that this claim is legitimate under some agreed mechanism.
From first principles, every message-passing system therefore needs to solve the same three-part problem. It must define what event counts as a message, how that message is transported, and why the destination should trust it. Different systems disagree mainly on the third part.
This is also where many readers first get tripped up. They imagine a cross-chain message as if it were a normal API request. It is not. An API call assumes the receiver can identify and trust the server answering it, or at least defer that problem to TLS, DNS, reputation, or enterprise control. A blockchain cannot casually import trust that way, because the whole point is to make state transitions depend on explicit, verifiable rules. Message passing is therefore less like “calling an API” and more like “presenting a notarized statement to a court that follows strict admissibility rules.” That analogy helps explain why verification matters, but it fails if taken too far: blockchains can automate these rules, while courts rely on human interpretation.
How does cross‑chain message passing work (event → proof → delivery → execution)?
| Stage | Who provides it | Typical evidence | Primary risk | Developer action |
|---|---|---|---|---|
| Event | Origin chain application | Committed state change | insufficient finality | Emit commitment and idempotency |
| Proof | Light client or attester | Merkle proofs or signatures | forged or malformed proofs | Validate proofs strictly |
| Delivery | Relayer / off-chain agent | Submitted packet or tx | relay delay or censorship | Design retries and timeouts |
| Execution | Destination contract/module | Verified payload | logic bugs or replays | Verify first, then execute |
A useful mental model is to see message passing as a four-stage pipeline.
First, something on the origin chain emits a message-worthy event. That might be a packet commitment in IBC, a log observed by a Guardian network in Wormhole, a contract call submitted through CCIP, or an outgoing instruction encoded in XCM. The key point is not the application detail but the invariant: the origin chain must have committed some state that others can later reference.
Second, the system produces or identifies evidence for that event. In light-client systems, the evidence may be a proof against the origin chain’s committed state root together with enough client data to verify finality. In external attestation systems, the evidence may be a quorum of signatures from an intermediary network. In ecosystems that separate message language from transport, the evidence may concern both the validity of the message format and the integrity of the transport path.
Third, someone delivers the message and its evidence to the destination chain. This actor is often a relayer or similar off-chain agent. IBC documentation is explicit that relayers are the “physical” connection layer: they scan chain state, build the required datagrams, and submit them to the counterparty chain. Hyperlane, Wormhole, and other systems likewise depend on off-chain infrastructure to carry messages from where they were produced to where they can be verified.
Fourth, the destination chain verifies and executes. If verification passes, the receiving contract, module, or runtime interprets the payload and applies the intended state transition. If verification fails, it rejects. In a sound design, execution is downstream of verification, not a substitute for it.
That four-stage model explains why “bridge” and “message passing” are related but not identical. A bridge is usually an application built on this pipeline. Message passing is the more general primitive.
Why is a token bridge actually a message‑passing system?
Consider a user who wants to move value from one chain to another. At first glance, it looks like the bridge is “moving tokens.” But blockchains cannot literally teleport native assets across consensus boundaries. What the system can do is coordinate two separate state changes using a message.
Suppose the user deposits 100 tokens into a bridge contract on chain A. That deposit is an event inside chain A’s state. Nothing has happened yet on chain B. For chain B to reflect the move, it needs a message whose meaning is roughly: “a valid deposit of 100 units for this recipient has occurred on chain A and has not already been consumed.” The bridge then delivers this claim, along with whatever evidence its trust model requires, to chain B. If chain B accepts the proof, it may mint a wrapped asset, unlock inventory, or credit some canonical representation.
Now the key insight: the thing that crosses chains is not the token itself. It is the authorization to perform a corresponding state change elsewhere. That is message passing.
This perspective also clarifies why bridge failures are often message-verification failures. If the destination chain accepts a false message, it can mint or release assets without a corresponding lock or burn on the origin side. That is exactly why verification logic is existentially important. In the Wormhole exploit analyzed by CertiK, the attacker bypassed signature verification on Solana by exploiting sysvar validation, posted a malicious message, and then used that message to mint wrapped ETH. The loss did not come from some mystical “cross-chain bug.” It came from the destination side treating an invalid message as valid. Here is the mechanism in plain terms: bad verification produced a false claim, and the false claim authorized real value creation.
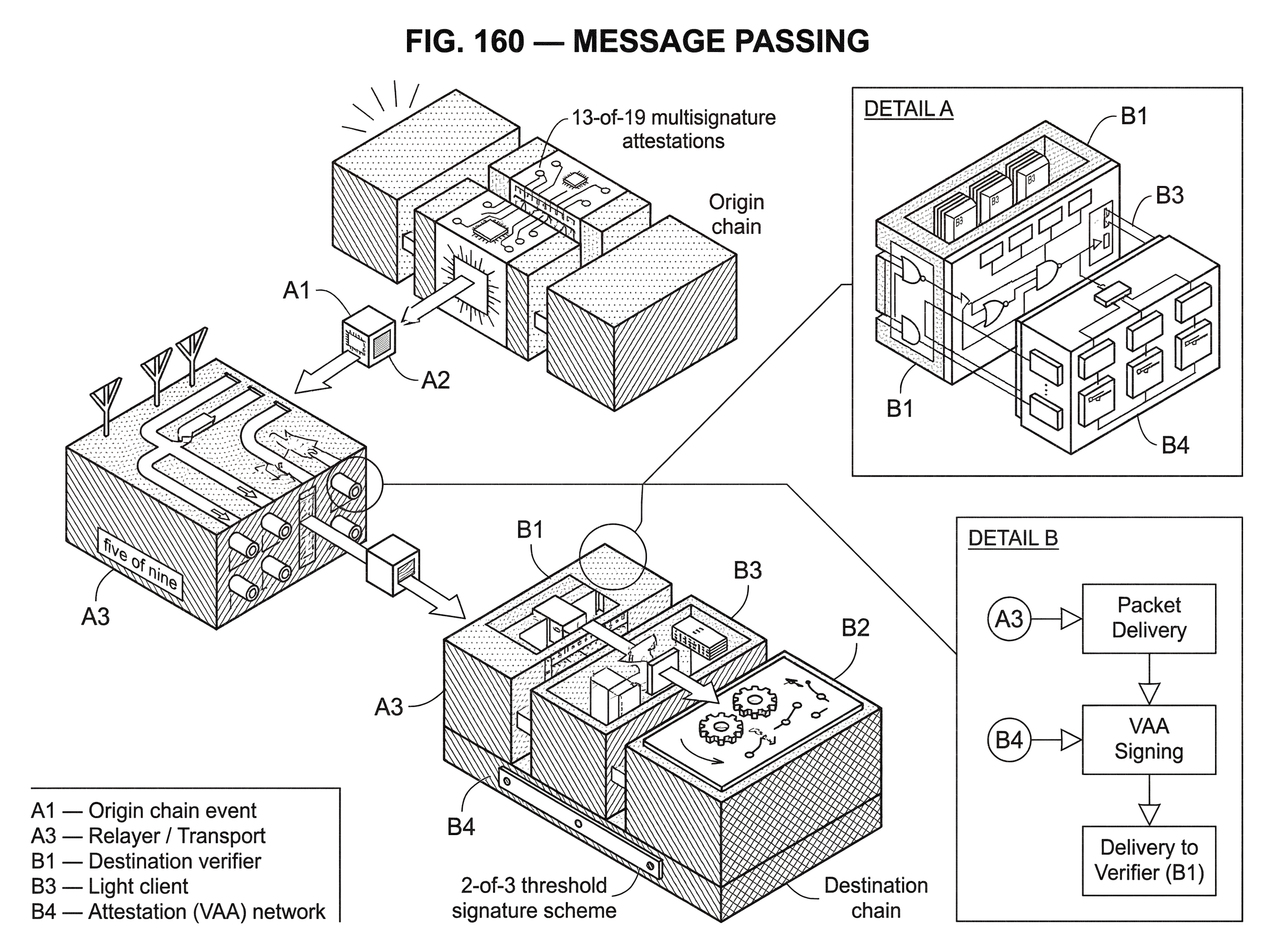
The same logic explains why operational trust surfaces matter. The Ronin breach was not fundamentally about packet formats or API design. Attackers gained enough validator keys (five of nine) to forge fake withdrawals. Once the system’s quorum rule was satisfied, fraudulent bridge messages looked authentic to the contracts. Again, the lesson is mechanical: if your verification layer depends on a signer set, then compromise of that signer set means compromise of the message-passing system.
What gives cross‑chain message passing its security?
| Model | How verified | Portability | Main trust surface | Best for |
|---|---|---|---|---|
| Light client | Merkle proofs + headers | Chain-specific, heavier | Source chain finality assumptions | Minimize intermediaries |
| Intermediary attestation | Quorum signatures / multisig | High across heterogeneous chains | Guardian / signer keys | Fast, broad compatibility |
| Network-mediated (DON/CCIP) | Decentralized node consensus | Designed for many chains | Node operators & governance | Programmable transfers |
| Format-first (XCM) | Transport supplies proofs | Format-agnostic; transport varies | Chosen transport protocol | Complex instruction sets |
Every message-passing design has to answer a hard question: what exactly convinces the destination chain that the message is real? There are a few broad answers, and they lead to very different systems.
A light-client model tries to make the destination verify the origin chain more directly. This is the intuition behind IBC. Each side of an IBC connection uses the other chain’s light client to verify incoming messages. The IBC stack separates this into layers. The transport, authentication, and ordering layer handles connections, clients, channels, and packet semantics; the application layer defines what those packets mean for things like fungible token transfer or interchain accounts. The attraction of this design is that trust is pushed closer to the underlying chains themselves. If the light client is correct and the source chain’s finality assumptions hold, the destination need not trust a separate signing committee to tell it what happened.
An intermediary-attestation model asks the destination to trust a separate network or committee to observe events and attest to them. Wormhole is a clear example. Its Guardian network monitors chains and produces VAAs, with standard 13-of-19 multisignature attestations. The destination chain verifies the VAA rather than directly verifying the source chain’s consensus. This can be more portable across heterogeneous chains, because many chains can verify signatures more easily than they can host robust light clients for every other chain. But the trust center shifts: security now depends materially on the honesty, key security, software correctness, and governance of the attestation network.
A network-mediated model uses an external decentralized infrastructure layer to validate and route messages. Chainlink CCIP presents arbitrary messaging and programmable token transfer as first-class capabilities and frames security in terms of decentralized oracle networks, rate limiting, timelocked upgrades, and vetted operators. Hyperlane similarly exposes general message passing, but with more explicit modularity around verification through custom hooks and interchain security modules. The practical question in these systems is not whether there is message passing (there is) but which security assumptions the application is choosing when it opts into a given verification path.
A format-first model separates the meaning of a message from its transport. Polkadot’s XCM is a messaging format and language for communication between consensus systems. It defines what messages look like and what instructions they contain, but not how they are delivered; transports such as XCMP, HRMP, or VMP handle that. This separation matters because it makes clear that message passing has at least two independent design problems: semantics and delivery. You can standardize one without fixing the other.
The most important consequence is that there is no free lunch. If a protocol is highly general across many chains, it often relies on a verification mechanism that is easier to deploy everywhere, such as multisignature attestations. If a protocol minimizes trust in intermediaries, it may require more demanding light-client machinery and tighter assumptions about finality and proof verification. The design space is about where you place complexity and which failures you are willing to risk.
Why 'message sent' ≠ 'message done': ordering and finality in cross‑chain systems
A cross-chain message is not meaningful just because someone emitted it. It becomes meaningful only when the destination can decide that the origin-side event is final enough and that executing it will not violate ordering or replay rules.
This is why transport layers talk so much about authentication and ordering. IBC’s core specifications cover client semantics, connection semantics, and channel and packet semantics precisely because cross-chain communication is not just “submit bytes over there.” The system has to know which channel a packet belongs to, whether it has already been received, whether packets must be processed in order, and what acknowledgment or timeout behavior applies. Without these rules, the receiver may execute a stale packet, process the same packet twice, or observe packets in an order the application cannot tolerate.
XCM makes a related point from another angle. It emphasizes asynchronous behavior and a “fire and forget” default. That means a sender should not imagine cross-chain communication as a synchronous function call that returns immediately with certainty about remote effects. The destination may process later, fail to process, or produce a separate response flow. Once that clicks, many design choices become easier to understand. A cross-chain application must often track pending state, acknowledgments, retries, and compensation logic because the communication path is fundamentally asynchronous.
Finality complicates this further. A message derived from a source-chain event is only as reliable as the assumption that the event will remain part of canonical history. If the origin chain can reorganize deeply, or if a bridge acts on insufficient confirmation, then the destination may execute based on a fact that later disappears from the source. The research literature on interoperability treats this as part of a broader integrity problem: valid cross-chain transactions depend on the validity and finality of the underlying local events.
So when a protocol advertises “verified cross-chain messages,” the right follow-up question is: verified against what notion of finality, by which verifier, and with what replay and ordering protections?
What can developers build with cross‑chain message passing?
Once you view message passing as “verified authorization for remote state change,” many applications become variations on a single pattern.
Token transfer is the most familiar case. IBC standardizes fungible token transfer in ICS-020. Chainlink CCIP exposes token transfer and programmable token transfer, where tokens and instructions travel together. Hyperlane Warp Routes bridge tokens between chains. The common mechanism is that a remote chain receives enough evidence to alter balances or mint representations under predefined rules.
But the more revealing examples are not purely about assets. Interchain accounts let one chain cause authenticated calls on another. IBC includes an Interchain Accounts standard, and Hyperlane documents a similar concept. In these systems, the payload is not “credit this amount” but “execute this remote action as an account whose authority originates elsewhere.” That is much closer to general computation across chains.
Generalized messaging takes the next step. Wormhole’s messaging product is explicitly about sending verified cross-chain messages. CCIP’s arbitrary messaging allows developers to encode any data they wish and deliver it to a receiving contract on another chain. Hyperlane describes general message passing as sending arbitrary data and function calls across chains. Once arbitrary bytes can be sent and meaningfully interpreted, developers can coordinate governance, trigger liquidations, sync application state, route orders, or compose workflows spanning multiple execution environments.
This is also where the line between interoperability and orchestration starts to blur. A token transfer may just be a special case of a richer cross-chain program: “send value there, then use it as collateral, then update a position here.” Chainlink’s programmable token transfer makes that explicit by allowing tokens and instructions in one transaction.
Real systems outside bridges rely on the same underlying idea. In decentralized settlement, threshold signing can act as the authorization mechanism for cross-domain or multi-party state changes. Cube Exchange, for example, uses a 2-of-3 threshold signature scheme for decentralized settlement: the user, Cube Exchange, and an independent Guardian Network each hold one key share; no full private key is ever assembled in one place, and any two shares are required to authorize a settlement. That is not identical to cross-chain packet transport, but it illustrates the same structural point: remote execution becomes safe only when authorization can be proven under a verification rule that no single actor can satisfy alone.
What commonly fails in cross‑chain message‑passing systems?
| Failure | Root cause | Typical impact | Short mitigation |
|---|---|---|---|
| Bad verification logic | incorrect or missing checks | false messages executed | strict proof validation |
| Weak operator security | compromised signer keys | unauthorized minting/releases | harden key operations |
| Async handling errors | assume synchronous delivery | double processing or inconsistency | idempotency and timeouts |
| Source-chain assumptions | underestimate reorgs/finality | stale or reversed claims | require confirmations or light-client |
Most failures in message passing come from one of four places: bad verification logic, weak signer or operator security, incorrect handling of asynchronous state, or misplaced assumptions about the source chain.
Bad verification logic is the most direct failure. If the destination contract verifies the wrong fields, trusts malformed proofs, mishandles signature checks, or delegates a critical check to unsafe code, false messages become executable. The Wormhole exploit is a vivid example because the bug sat directly in the path from attestation verification to asset minting.
Weak operator security matters whenever the protocol relies on an intermediary network. The Ronin breach showed that decentralized-looking designs can collapse if too many keys are operationally concentrated or if old permissions linger as backdoors. The broader interoperability security literature similarly finds large losses concentrated in systems secured by intermediary permissioned networks with weak cryptographic key operations. That does not mean all attestation-based systems are doomed. It means their security lives or dies by operational rigor as much as by protocol design.
Incorrect asynchronous handling is subtler but common. Developers may assume delivery is instantaneous, that remote execution always succeeds, or that retries are harmless. In reality, cross-chain applications need idempotency, replay protection, timeout handling, and careful distinction between “message accepted for delivery” and “business action completed.” If those states are conflated, a relayed packet may be processed twice or a failed remote action may leave the local side in an inconsistent state.
Misplaced assumptions about the source chain are the deepest issue. A destination chain can only verify what its model allows it to verify. If the source chain’s finality is probabilistic, if the light client is out of date, if the bridge underestimates reorg risk, or if the chain itself is vulnerable to consensus failure, then message passing inherits those weaknesses. No interoperability layer can be stronger than the assumptions it imports.
This is why the best way to think about message passing is not “a bridge feature” but a security boundary. It is the boundary where one state machine decides how much of another state machine’s reality it is willing to accept.
Why do cross‑chain protocols use layered designs for message passing?
A notable pattern across ecosystems is separation of concerns.
IBC distinguishes the transport/authentication/ordering layer from application semantics. XCM distinguishes message format from delivery transport. Messaging systems often separate verification from execution, and execution from relaying. This is not just software neatness. It reflects the structure of the problem.
The chain receiving a message must answer three distinct questions. Did the message really originate from the claimed source? Was it delivered in a way consistent with the protocol’s ordering and replay rules? And if both are true, what should the application do with it? Mixing these concerns makes systems brittle because a bug in application logic can contaminate transport guarantees, or a transport assumption can silently become part of the application’s trust model.
Layering also makes interoperability more reusable. Once a protocol can securely move generic packets or verified payloads, multiple applications can share that substrate: token transfers, NFTs, governance messages, interchain accounts, oracle updates, and more. This is why many standards and products emphasize arbitrary byte payloads. Generality at the message layer lets ecosystems innovate at the application layer.
Conclusion
Message passing is the basic trick that makes blockchain interoperability possible: one chain commits an event, another chain receives a claim about that event, and the destination acts only if its verification rules say the claim is good enough.
Everything else is a specialization of that pattern.
- bridges
- interchain accounts
- omnichain apps
- programmable token transfers
If you remember one thing, remember this: cross-chain systems do not really move state between chains; they coordinate separate state transitions by transporting and verifying messages. Once you see that, the design space becomes clearer, and so do the risks. The whole game is deciding who verifies the message, what assumptions that verification imports, and what the destination is willing to do once it believes it.
How do you move crypto safely between accounts or networks?
To move crypto safely between accounts or networks, verify the exact asset, network, destination details, fees, and confirmation requirements before you send. Use Cube Exchange to fund your on-chain wallet and submit the transfer; if you route through an external bridge, treat the bridge as a separate service and confirm its network mapping and finality rules before depositing.
- Fund your Cube account with the exact token and network you plan to move (for example, USDC on Ethereum Mainnet).
- Confirm the destination chain and token standard (e.g., ERC‑20 vs a bridged representation) and copy the destination address and any memo/tag exactly.
- Send a small test transfer first (a tiny on‑chain amount or 0.1–1% of the planned value) and confirm it arrives on the destination chain.
- Check origin-chain gas fees and the destination-side confirmation/finality expectations (for example, wait ~12 confirmations on Ethereum L1 or the bridge’s recommended finality threshold) before sending the full amount.
- Initiate the full transfer from Cube (or deposit to the bridge's specified address), monitor the on‑chain transaction and any attestation steps, and confirm the destination balance before considering the process complete.
Frequently Asked Questions
Light-client models (exemplified by IBC) have the destination verify the origin chain’s consensus proofs directly, pushing trust toward the source chain and its finality assumptions; intermediary‑attestation models (exemplified by Wormhole) ask the destination to verify signatures from a separate guardian or committee that observed the event. The trade-off is portability versus trust: light clients minimize intermediary trust but require chains to support client verification, while attestation networks are easier to deploy across heterogeneous chains but introduce operator/committee trust and operational risk.
Relayers are off‑chain processes or operators that scan the origin chain, package proofs or VAAs, and submit them to the destination chain; they are the “physical” delivery layer for most systems. How they are economically incentivized is not standardized - IBC documentation and community work have left relayer incentives and governance unsettled - so relayer operation and incentives vary by protocol and remain an open operational question.
Finality and reorganization risk determine how credible an origin‑chain event is; a message derived from a non‑final or reorganizable state can later disappear, causing the destination to act on a fact that no longer holds. Protocols therefore require clients or attestations to prove enough finality and include timeouts, confirmation thresholds, or light‑client assumptions to reduce reorg risk.
Most bridge compromises are caused by one of four failures: incorrect verification logic on the destination, weak signer/operator security in intermediary networks, incorrect handling of asynchronous delivery and retries, or wrong assumptions about the source chain’s guarantees. The Wormhole and Ronin incidents illustrate verification bugs and signer compromise as concrete failure modes.
No - cross‑chain message passing is fundamentally asynchronous and more like presenting a notarized claim than a synchronous API call. Protocols (and XCM explicitly) treat messages as "fire and forget" by default, meaning senders must manage pending state, acknowledgments, retries, and compensation because remote execution may be delayed or fail.
Ordering and replay protections are implemented at the transport/authentication layer: connections, channels, packet sequence numbers, acknowledgments, and timeouts tell the destination whether a packet belongs to a given channel, whether it was already processed, and whether packets must be ordered. Standards like IBC codify channel semantics and acknowledgments to avoid stale, duplicated, or out‑of‑order execution.
When a user moves tokens across chains, the system is not teleporting native assets but transporting an authorization to perform a corresponding state change (e.g., mint a wrapped token or unlock inventory) on the destination chain. The origin chain’s lock/burn is the committed event and the message carries proof that lets the destination enact the paired state change.
Generality often trades off with trust minimization: highly portable, general messaging tends to rely on signature‑based attestations or oracle networks that are easier to run everywhere but introduce intermediary trust, while designs that minimize intermediaries (light clients) require stronger client support and stricter finality assumptions from the chains. There is no free lunch - protocols place complexity in different layers depending on which failures they accept.
Guardian/attestation networks produce signed VAAs (Wormhole uses a standard multisig quorum model) that destinations verify instead of running a foreign light client; this makes cross‑chain messaging easier across heterogeneous chains but concentrates risk in guardian key security and quorum procedures. The documentation warns that multisig verification costs scale with signer count and that guardian selection/operational practices are important but not fully specified publicly.
Developers should assume asynchronous delivery and design idempotent handlers, replay protection, explicit timeouts, retry and compensation flows, and clear state for “pending” vs “completed” cross‑chain actions; conflating delivery acceptance with business completion is a common source of bugs. The article emphasizes idempotency, replay protection, and careful handling of acknowledgments to avoid inconsistent local state when remote execution fails or is delayed.
Related reading