What is a Replay Attack?
Learn what a replay attack is, how it works, and how nonces, timestamps, session binding, genesis hashes, and chain IDs stop message reuse.
Introduction
Replay attack is the problem of a system accepting an old, valid message as if it were new. That sounds almost trivial at first: if the message is authentic, why shouldn’t the system accept it? But this is exactly the trap. Security systems often focus on proving that a message came from the right party and was not altered in transit. A replay attack exploits the missing third property: freshness. If the system cannot tell whether a message is being used for the first time or the tenth, authenticity alone is not enough.
NIST defines a replay attack as capturing transmitted authentication or access-control information and retransmitting it to produce an unauthorized effect or gain unauthorized access. In a similar formulation, it is an attack in which an adversary replays previously captured messages between a legitimate claimant and verifier to masquerade as that claimant, or vice versa. The important point is that nothing necessarily needs to be forged. The attacker may succeed while sending bits that were perfectly valid the first time.
That is why replay attacks show up in so many different places. In login protocols, an old authentication message can be reused to impersonate a user. In web sessions, a stolen token can be resubmitted after the original exchange. In blockchains, a signed transaction intended for one chain or one moment can be accepted again on the same chain, on a forked chain, or on a similar network. The surface details change, but the structure is the same: a proof of authorization is treated as reusable when it should have been single-use or context-bound.
Why does message authenticity not guarantee freshness in replay attacks?
The easiest way to understand replay attacks is to separate two questions that systems often blur together. The first is, "Was this message really approved by the right party?" The second is, "Is this approval meant for this use, here and now?" Cryptography often answers the first question very well. A valid signature, message authentication code, or token can strongly show that the sender once authorized the message. But unless the protocol includes some way to limit reuse, that same proof may still be accepted later, in a different session, or even on a different network.
This is the compression point that makes replay attacks click: a replayed message can be both genuine and unauthorized. Genuine, because the original sender really did sign or send it. Unauthorized, because the system is accepting it outside the intended time, sequence, or domain.
An analogy helps here. Think of a concert ticket. The barcode may be genuine, and the scanner can verify that it was issued by the organizer. But if the system does not mark it as used, the same genuine ticket can be scanned again and again. The problem is not counterfeit detection; it is reuse detection. The analogy is useful because replay attacks are about duplicated use of a real credential. It fails where security protocols are more subtle than tickets: a protocol may allow some repeated messages, and “used once” may be defined by sequence number, session, chain, or validity window rather than by a simple yes-or-no record.
Once you see replay this way, many security mechanisms look different. A nonce is not just random decoration. A timestamp is not just metadata. A chain ID is not just a label. They all serve the same deeper purpose: they help the verifier answer, "Is this authorization bound to this specific context, and has it already been consumed?"
How does a replay attack work step by step?
The mechanism is simple enough that it is worth stating plainly. A legitimate user sends a message that the system will accept: maybe a login response, maybe an API request, maybe a signed blockchain transaction. An attacker captures that message. Later, the attacker sends the same message again. If the verifier checks only validity and not freshness, it accepts the replay.
The attacker may capture the message on the network, extract it from logs, copy it from client-side storage, or observe it in some other channel. The exact capture method matters operationally, but not conceptually. Replay attacks are downstream of exposure. Once a valid authorization artifact is available to the attacker, the question becomes whether the system will accept it again.
A small worked example makes this concrete. Imagine a door system where a phone app sends a signed command saying, in effect, “unlock car.” The receiver checks the signature and sees that it matches the owner’s key, so it opens. If an attacker records that radio message and the system does not require a fresh rolling code, nonce, or challenge, the attacker can transmit the same signed command later and unlock the car again. OWASP points to the reported “Rolling PWN” attacks on Honda vehicles as an example of replaying valid codes due to flaws in rolling-code implementation. The significance of the example is not the automotive setting itself. It is that the system treated a previously valid command as still valid when seen again.
The same logic applies to authentication protocols. Suppose a server sends a login challenge, a user responds with some proof derived from a secret, and the server checks the proof. If an attacker can record the response and reuse it later without needing a fresh challenge, the attacker may log in despite knowing no secret at all. NIST’s claimant-verifier wording is aimed exactly at this pattern.
In blockchain systems, the message being replayed is often a signed transaction. A user signs a transaction authorizing a transfer. If the network accepts the same signed payload again, or if another chain interprets the payload under the same rules, the transaction can execute in an unintended place. That is why replay protection is not an optional convenience. It is part of what makes a signature mean this action once, not this action wherever and whenever the bytes still verify.
What conditions enable a replay attack to succeed?
| Prerequisite | Why it matters | Mitigation |
|---|---|---|
| Message exposed | Attacker can capture valid artifact | Reduce exposure, add freshness |
| Authorization reusable outside intent | Proof accepted in wrong context | Bind to nonce, timestamp, or domain |
| Verifier lacks duplicate checks | No way to detect reuse | Store used markers or use challenge-response |
Replay attacks depend on a specific failure mode: the verifier lacks an invariant that distinguishes a fresh authorization from a reused one. Different systems implement that invariant differently, but the logic is the same.
First, the attacker needs a valid message or token. Replay does not usually begin with cryptographic breakage. It begins with observation, leakage, theft, or capture. If the message was never exposed, there is nothing to replay. But message secrecy alone is not enough, because many valid messages are visible by design to intermediaries, clients, or counterparties.
Second, the authorization must remain meaningful outside its original moment. If a protocol embeds a unique challenge chosen by the verifier for each session, an old response will fail because it answers the wrong challenge. If a transaction consumes a nonce that increments on use, a duplicate will fail because the account’s expected nonce has changed. If a signature commits to a specific chain ID or genesis hash, it will fail on another network because the signed domain no longer matches. Replay succeeds where this contextual binding is missing, weak, or inconsistently enforced.
Third, the verifier must not maintain or consult enough state to reject duplicates. This is why replay protection is a design choice with tradeoffs. The strongest defenses often require memory: a counter, a used-token set, a session table, a recent-message window, or chain-specific state. Stateless designs are attractive for performance and simplicity, but they frequently need some substitute for server-side memory, such as self-expiring tokens or challenge-response exchanges. Without that, the verifier has no basis for saying, “I know this is genuine, but I also know it has already been used.”
What defenses stop replay attacks and how do they differ?
| Defense | How it enforces freshness | State required | Main tradeoff | Best for |
|---|---|---|---|---|
| Nonce | Binds signature to unique value | Per-account nonce state | Storage and sync cost | Account sequencing |
| Timestamp / window | Limits validity to a time interval | Clock sync only | Clock drift vulnerabilities | Short-lived tokens |
| Challenge-response | Verifier supplies fresh challenge | Per-session verifier state | Extra round-trip latency | Interactive authentication |
| Session binding | Ties token to specific session | Session or channel state | Session management complexity | TLS/channel-bound tokens |
| Domain separation | Embeds domain into signed payload | No per-message state | Requires unique domain IDs | Cross-chain/fork protection |
There are several common replay defenses, but they are better understood as variations on a single idea: bind authorization to a context that changes.
A nonce is the canonical example. In general security protocols, a nonce is a value intended to be used once. A verifier may send a fresh nonce as a challenge, and the claimant must sign or authenticate that nonce in the response. Because the nonce changes every session, a captured old response no longer matches the new challenge. On account-based blockchains, the term often refers to a transaction sequence number. Substrate’s CheckNonce signed extension explicitly describes its purpose this way: it checks and increments the nonce to give replay protection for transactions. The mechanism is direct. A transaction signed with nonce n is valid only when the account’s next expected nonce is n; once accepted, the expected nonce becomes n+1, and the old transaction cannot be replayed on that chain.
A timestamp or validity window solves the problem differently. Instead of saying “use exactly once,” it says “use only during this interval.” This reduces the replay window rather than eliminating it entirely. That can be good enough when clocks are reasonably synchronized and when retaining long-term per-message state is too expensive. But it introduces assumptions. If clocks drift, if network delays are large, or if an attacker can act within the validity window, replay may still succeed. Time-based freshness is often a practical compromise, not a perfect cure.
A challenge-response protocol is stronger because it lets the verifier choose the freshness value. The claimant proves knowledge of a secret or possession of a key in relation to a challenge that the attacker could not predict in advance. This prevents an attacker from reusing an old proof against a new challenge. Many authentication standards rely on this basic pattern because it separates identity from freshness cleanly.
session binding narrows the allowed context further. A token or message is accepted only within the specific session, channel, or negotiated parameters for which it was created. OWASP places replay attacks alongside authentication and session management for exactly this reason. A bearer token that is not bound to session context is easier to replay than one tied to a particular TLS channel, client state, or short-lived negotiation.
domain separation prevents a proof that is valid in one domain from being valid in another. In blockchain systems, this often means binding signatures to a chain, genesis block, runtime version, or fork identifier. The signed message is still genuine, but it is no longer generic. It says, in effect, “I authorize this action on this network under these rules,” not merely “I authorize this action.” That distinction is what stops cross-chain replay.
Same-chain vs cross-chain replay attacks: what’s the difference?
Blockchain readers often first meet replay attacks during forks, but there are really two related problems. The first is same-chain replay: can the same signed transaction be submitted again on the same network? The second is cross-chain replay: can a transaction valid on one chain also be valid on another?
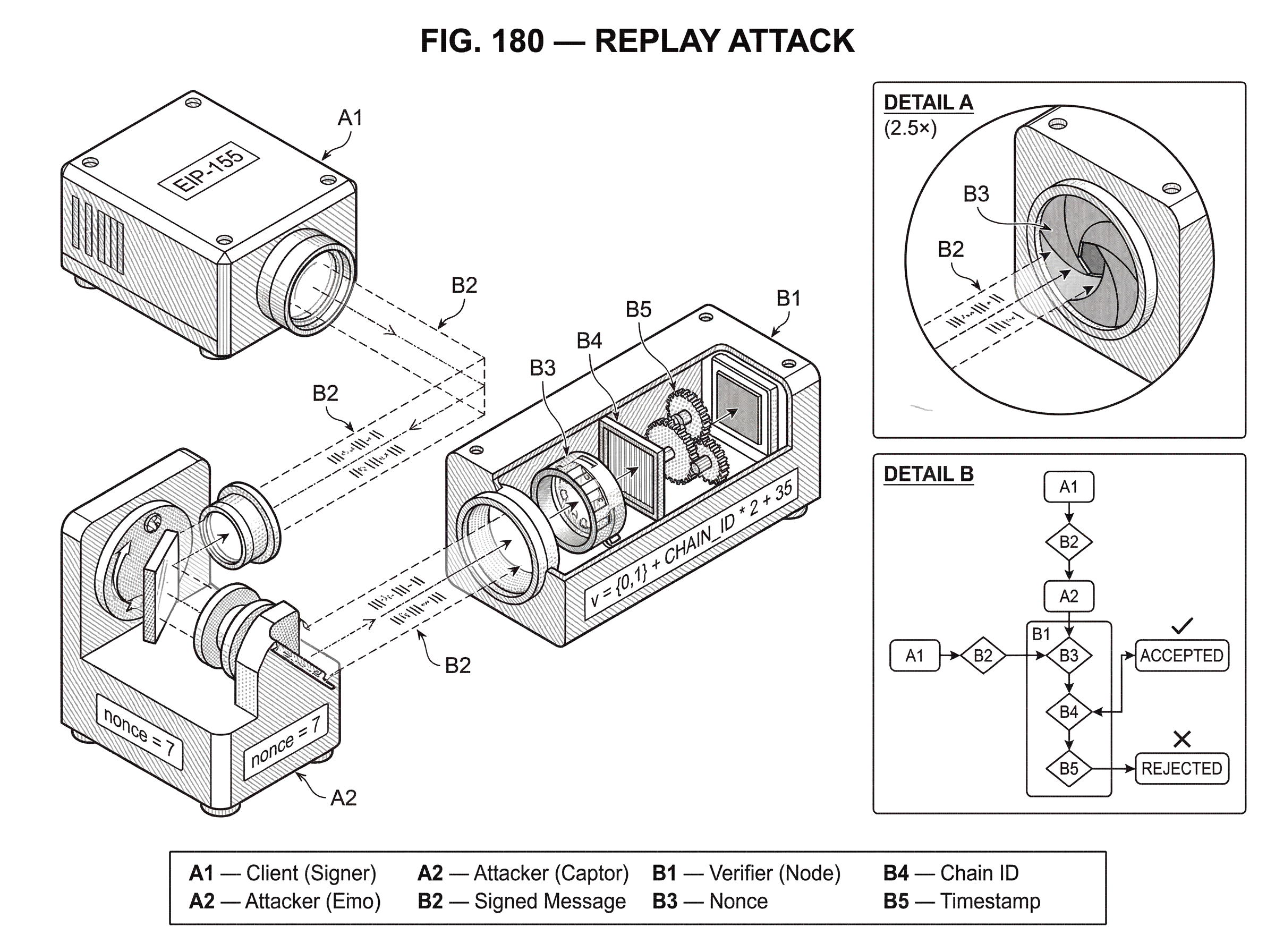
Same-chain replay is usually handled by transaction sequencing. On account-based chains, the account nonce is the main defense. If Alice signs a transfer with nonce 7, validators will accept it only when her next expected nonce is 7. After inclusion, her expected nonce becomes 8, so resubmitting the exact same transaction fails. This is why the outbound relation to the broader concept of nonce matters: nonce-based sequencing is not incidental bookkeeping. It is the primary mechanism that turns a signature into a single-use authorization.
Cross-chain replay is a different problem. Suppose two chains share the same transaction format, signature scheme, and address derivation. A transaction signed for one chain may also verify on the other unless something in the signed payload distinguishes them. This became a practical issue around contentious forks. The Ethereum Foundation’s post after the DAO hard fork explicitly warned users following the non-fork chain to beware of transaction replay attacks. The warning reflects the structure of the risk: if both chains recognize the same signature under the same rules, then an action on one can unintentionally happen on the other.
The key insight is that a signature is only as context-specific as the data it signs. If chain identity is not in the signed message, the cryptography cannot infer it after the fact.
How does Ethereum’s EIP-155 chain ID prevent cross-chain replay?
Ethereum’s most influential replay-protection change is EIP-155. The idea is conceptually simple: include the chain ID in the transaction signing data so that a signature for one chain does not verify as the same authorization on another.
Before this change, the transaction signing hash covered six RLP-encoded elements: nonce, gasprice, startgas, to, value, and data. EIP-155 changes the signing hash so wallets should hash nine elements instead: those six fields plus chainid, 0, and 0. The signature recovery value v is also changed to encode chain identity, with v = {0,1} + CHAIN_ID * 2 + 35, where {0,1} is the parity bit.
Here is the mechanism in ordinary language. A user signs what looks like the same economic action (send value to an address) but the bytes being signed now also say which chain that action belongs to. If another chain has a different CHAIN_ID, the signing hash is different, so the original signature no longer authorizes the transaction there. Nothing about the cryptography became “stronger” in the abstract. The signature became narrower in scope.
That narrowing is why EIP-155 solved the practical fork problem. The proposal explicitly states that it would provide a way to send transactions that work on Ethereum without working on Ethereum Classic, assuming different chain IDs. It is a textbook example of replay defense by domain separation. The transaction remains valid, but only in the domain it was signed for.
There is an important caveat in the specification: old-style signatures using v = 27 or 28 remain valid under the old rules. That preserves backward compatibility, but it also shows a recurring design tradeoff. Compatibility can keep old replay surfaces alive if users, wallets, or nodes continue to support pre-protection formats. Replay protection is often strongest not when the new mechanism exists, but when the ecosystem consistently requires it.
At the smart-contract level, Ethereum later added the CHAINID opcode through EIP-1344 so contracts can read the current chain ID. This matters because replay risks do not stop at transactions. Contracts also verify off-chain signatures, including EIP-712-style typed messages and Layer 2 messages. If a contract cannot access chain identity at runtime, developers may hardcode it or omit it, both of which can become dangerous around forks. EIP-1344’s motivation is explicit: EIP-155 uses chain ID to prevent replay attacks between different chains, and contracts need similar access to chain identity for their own signature handling.
A further subtlety appears in EIP-1965, which proposes checking whether a chain ID was valid at a specific block number. The reason is instructive. If chain identity can change during a contentious split, “what chain am I on now?” may not be enough to interpret an old off-chain signature safely. The deeper lesson is that replay protection sometimes needs not just a domain, but a time-qualified domain.
How does Bitcoin Cash use a fork-specific sighash for replay protection?
Bitcoin-family systems faced the same underlying problem after chain splits: a transaction valid on one fork could be valid on another unless the signature committed to fork-specific context. The Bitcoin Cash replay-protected sighash design addresses this by modifying the transaction digest when the SIGHASH_FORKID flag is set. The sighash type is extended to include a 24-bit fork ID in its most significant bits, so different fork IDs produce different digests.
The mechanism is parallel to EIP-155 even though the transaction model is different. In both cases, the signature commits to chain-specific identity. In Ethereum, that identity is CHAIN_ID embedded in the signed transaction data. In the Bitcoin Cash design, it is a fork ID embedded into the sighash process. The details differ because UTXO transactions and account-model transactions structure authorization differently. The invariant is the same: a valid signature on chain A should not also authorize execution on chain B.
This is a useful place to avoid a common misunderstanding. Replay protection is not unique to one blockchain architecture. What changes across architectures is where the freshness or domain-separation check lives. On account-based chains, nonces and chain IDs are natural places. On UTXO chains, replay-resistant digest rules and fork-specific sighash flags can play the equivalent role.
How do Solana, Substrate, and Cosmos EVM implement replay protection?
| Platform | Freshness mechanism | State location | Typical lifetime | Default behavior |
|---|---|---|---|---|
| Solana | recentblockhash; durable nonce | Client + nonce accounts | Short (blockhash expiry) | Rejects expired blockhashes by default |
| Substrate | CheckNonce, CheckGenesis, CheckEra | On-chain signed extensions | Variable (runtime-defined) | Requires runtime signed extensions |
| Cosmos EVM | EIP-155 chain ID + Bech32 prefixes | Tx signature + chain config | Chain-bound unless changed | Rejects unprotected txs by default |
Replay protection becomes even clearer when you look across systems that solve the same problem with different protocol machinery.
On Solana, ordinary transactions rely on a recent_blockhash, which limits how long a transaction remains valid. The short lifetime itself acts as a replay constraint: a captured transaction cannot be replayed indefinitely because the referenced blockhash ages out. Solana’s durable transaction nonce feature exists precisely because short-lived blockhashes can be inconvenient for delayed signing and submission. A nonce account stores the next nonce value, and when creating a durable-nonce transaction the stored nonce must be passed as the --blockhash argument. This does not abolish replay protection; it replaces one freshness anchor with another managed mechanism. The transaction stays valid long enough to be practical, but still depends on nonce state that advances on use.
Substrate-based chains make the logic unusually explicit in their signed extensions. CheckNonce provides replay protection by checking and incrementing the account nonce. CheckGenesis checks the transaction’s provided genesis hash and is used to provide replay protection between different networks. CheckSpecVersion and CheckTxVersion bind the signature to the runtime and transaction version used during signing, while CheckEra or mortality limits the transaction’s lifetime. This is a very clean illustration of replay defense as layered context binding: sequence, network identity, software version, and validity window all contribute to making a transaction valid only in the intended setting.
Cosmos EVM documents the same point from an EVM-compatibility angle. It notes that replay attacks occur when a signed transaction valid on one network can be replayed on another without the user’s consent, especially because Ethereum-like networks can share address formats, transaction formats, and forks. Its answer is a dual model: Cosmos-native transactions get some inherent separation from chain-specific Bech32 prefixes, while EVM transactions use EIP-155 chain-ID protection and reject unprotected transactions by default. The wording matters because it highlights a real operational fact: replay protection is not just protocol theory. Chains and node operators choose whether legacy, unprotected formats are still accepted.
What are common misunderstandings about replay attacks?
The most common misunderstanding is to think replay attacks are about duplication in the network, as if the problem were merely packet retransmission. Real networks naturally duplicate, reorder, and retry messages. Good protocols are built to survive that. A replay attack is specifically about a duplicated message being accepted as a fresh authorization when it should not be.
A second misunderstanding is to think encryption alone stops replay. It does not. If an encrypted message can be copied and resent verbatim, and the receiver accepts it again, encryption has preserved confidentiality but not freshness. The same is true for signatures. A signature proves approval of the signed content; it does not, by itself, prove that the approval is current, unique, or chain-specific.
A third misunderstanding is to treat replay protection as a single feature rather than a design property. Systems often need several layers. A nonce stops same-account same-chain replay. A chain ID stops cross-chain replay. A validity window limits delayed execution. A session binding stops reuse in another connection. None of these is redundant if the threat model spans multiple contexts.
What can break replay protections when system assumptions change?
Replay protection is especially sensitive to assumptions because freshness is relative to a model of state and context.
If clocks are unreliable, timestamp-based defenses weaken. If the verifier does not store used nonces or cannot reliably increment them, nonce-based defenses weaken. If two chains accidentally share a chain ID, chain-based domain separation weakens. If a system accepts both protected and legacy unprotected formats, the weaker path may remain exploitable. If a hard fork changes chain identity and applications cached the old value carelessly, off-chain signatures may become ambiguous or invalid.
This is why standards and implementations often emphasize not just the presence of replay-protection fields, but where they are included. Substrate’s CheckGenesis documentation explicitly says the genesis hash must be part of the signed payload. That requirement points to a first-principles rule: a verifier cannot safely rely on context that the signer did not actually sign. Likewise, Ethereum’s chain ID fix works because chain identity changes the signing hash itself, not because nodes merely carry chain IDs alongside signatures as advisory metadata.
Another practical edge case is migration and backward compatibility. Cosmos EVM strongly discourages allowing unprotected transactions, even though it documents a way to do so through both a module parameter and node configuration. That dual opt-in is a sensible security posture. It acknowledges that compatibility switches exist, but makes clear that disabling replay protection reopens cross-chain and wrong-network execution risks.
Conclusion
A replay attack is what happens when a system treats proof of authenticity as if it were also proof of freshness. The attacker does not need to forge a message; they only need to reuse one that was valid before.
The lasting idea is simple: a secure authorization must be bound to changing context. That context might be a nonce, a challenge, a timestamp, a session, a genesis hash, a runtime version, or a chain ID. Different systems express it differently, but the purpose is always the same: make “valid once, here” stop being “valid forever, everywhere.”
How do you secure your crypto setup before trading?
Secure your setup by checking wallet hygiene, destination details, and transaction freshness before trading. Cube is non-custodial (MPC) so you keep signing control; use these steps to verify network, address, and replay-protection cues before you trade.
- Fund your Cube account with fiat on-ramp or a supported crypto transfer so you can execute trades or on-chain transfers.
- Verify the target network and chain ID in both your wallet and the destination address before signing any transaction.
- For on-chain transfers, confirm the transaction’s nonce or expiration field (or that the wallet adds EIP-155 chain ID protection) and choose an order/transfer type that matches your timing needs.
- Review destination address, network, fee, nonce/expiry, and expected confirmations; submit and wait for the chain-specific confirmation threshold (or nonce increment) before reusing funds or attempting retries.
Frequently Asked Questions
A nonce ties an authorization to a single expected value (e.g., an account sequence number or a verifier-chosen challenge) so that once the nonce is consumed the same signed message no longer matches; a timestamp instead limits acceptance to a time window, reducing the replay opportunity but not eliminating it and requiring reliable clock assumptions.
Because they only prove the message came from the right party and was unmodified, not that the approval is current or single-use; signatures and encryption preserve authenticity and confidentiality but do not by themselves provide freshness, so an attacker who captures a valid artifact can resend it unless the protocol binds it to changing context.
EIP-155 prevents cross-chain replay by including CHAIN_ID in the transaction signing hash (adding three elements to the hashed data) and encoding the chain identity into the signature recovery value v, so a signature for one chain does not verify as the same authorization on a different chain; however, old-style signatures (v = 27/28) remain valid for backward compatibility and can keep replay surfaces alive until the ecosystem stops supporting them.
Timestamps limit how long a captured message can be reused but assume sufficiently synchronized clocks and accept a non-zero replay window; if clocks drift, network delays are large, or an attacker acts inside the validity interval, replay can still succeed.
The invariant is the same - bind the signature to chain-specific context - but implementations differ: account-model chains typically use nonces and chain IDs embedded in the signed payload, while UTXO-based forks (e.g., Bitcoin Cash) modify the transaction digest/sighash (via a fork ID) so signatures commit to a fork; the location and form of the binding reflect the transaction model.
Three things must hold: the attacker must obtain a valid message or token (capture/leakage), the authorization must still be meaningful outside its original context (no adequate freshness or domain binding), and the verifier must not have or consult state that would reject the duplicate (e.g., incremented nonces or used-token records).
Backward compatibility can leave old, unprotected formats accepted (for example pre-EIP signatures with v = 27/28), so even after a replay-protection mechanism exists, legacy support across wallets, nodes, or contracts can preserve replay surfaces until the ecosystem uniformly stops accepting the weaker format.
Stateless designs usually replace server-side memory with alternative freshness anchors such as self-expiring tokens, verifier-chosen challenges (challenge–response), or short-lived blockhashes; these avoid persistent per-message state but rely on other guarantees (timely expiry, verifier control of the challenge, or managed nonce accounts) and thus trade statefulness for different operational assumptions.
Related reading