What is a Merkle Tree?
Learn what a Merkle tree is, how Merkle roots and proofs work, and why blockchains use them for transaction inclusion, light clients, and state commitments.
Introduction
Merkle tree is the name for a data structure that lets you compress a large collection of data into a single short hash, while still being able to prove that any particular piece of that data is included. In blockchain systems, that is not a convenience; it is one of the basic ways a network stays verifiable without forcing every participant to download and recheck everything. If a block contains thousands of transactions, or a chain maintains a huge evolving state, the core question is always the same: how can many parties agree on exactly what data exists and verify small parts of it efficiently?
The useful tension here is that integrity wants global knowledge, but verification wants local effort. A naïve design says: if you want to know whether transaction T is in block B, download the whole block and inspect it. That works, but it scales poorly. A Merkle tree changes the shape of the problem. Instead of asking verifiers to see all the data, it lets them rely on a short commitment called the Merkle root, plus a short proof path that ties one leaf back to that root.
That is why the idea appears everywhere around blockchains. Bitcoin uses a Merkle root in each block header to commit to all transactions in the block. Certificate Transparency uses a related construction to prove that a certificate was included in a public log and that the log grew append-only. Ethereum uses a more elaborate relative, the Merkle Patricia trie, to commit to world state, transactions, and receipts. Different systems adapt the idea, but the underlying mechanism is the same: hash data upward so a small top-level digest depends on every committed element below.
How does a Merkle tree compress many items into one short digest?
A hash function turns an input of arbitrary size into a fixed-size output. The important property here is not just that hashing is fast; it is that changing the input should unpredictably change the output. If you trust the hash function’s collision resistance and second-preimage resistance, then the hash acts like a compact fingerprint of the input.
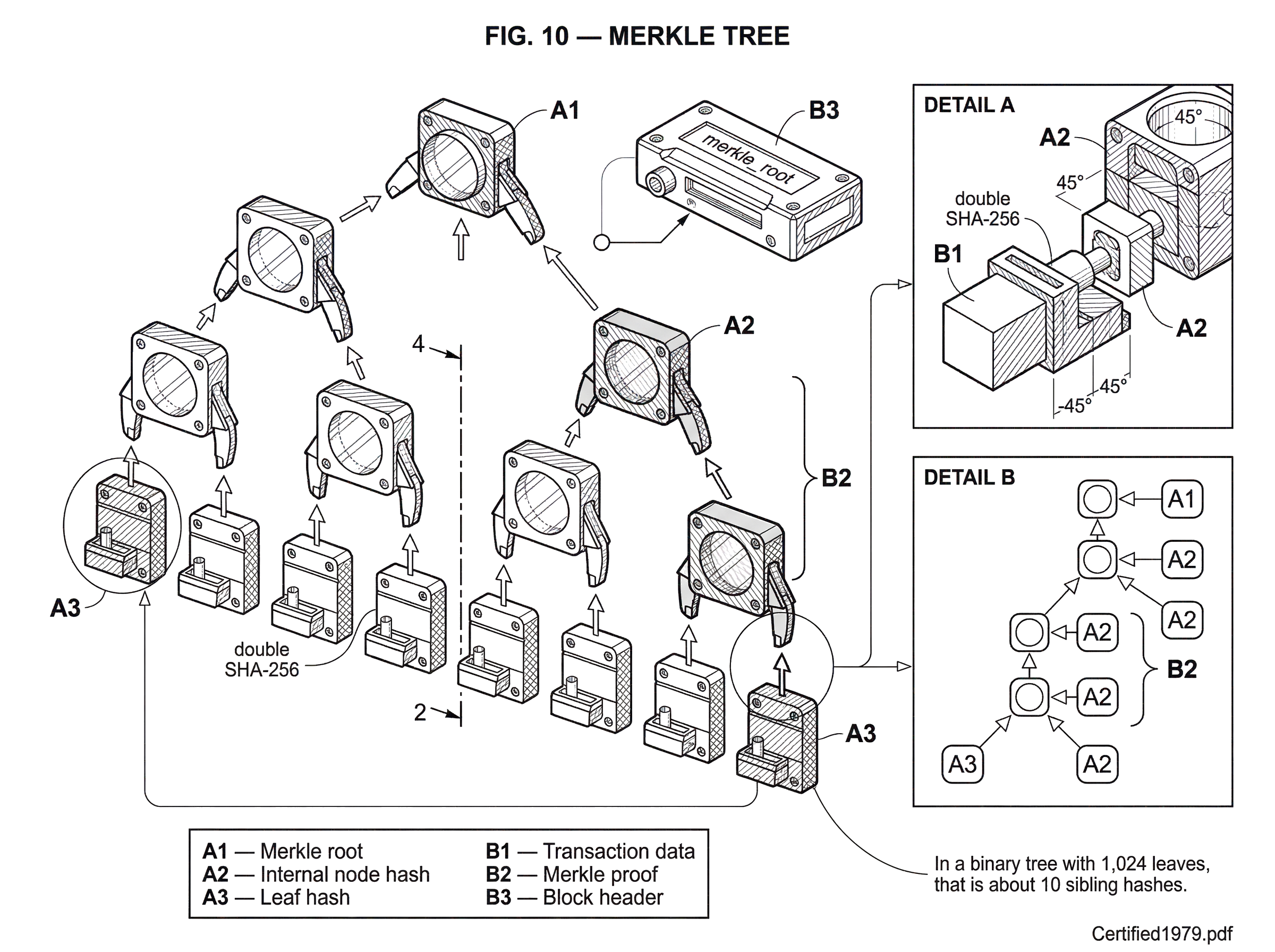
Now imagine you have four transactions: A, B, C, and D. You could hash each one to get four leaf hashes. Then you combine adjacent hashes in pairs and hash again: hash(hash(A) || hash(B)) to make one parent, and hash(hash(C) || hash(D)) to make another. Then you hash those two parent hashes together. The final value is the root.
What matters is the dependency structure. The root does not merely summarize the data in a vague way; it is computed from children, which are computed from children, all the way down to the leaves. If any transaction changes, its leaf hash changes. That changes its parent. That changes the next parent up. Eventually the root changes. So the root is a commitment to the entire ordered collection.
The tree metaphor is useful because it explains both compression and proof size. A tree with n leaves has height roughly log2(n) when it is binary. To prove one leaf is included, you do not need every other leaf. You only need the sibling hash at each level on the way up to the root. That is the compression point: global commitment, local proof.
How does a Merkle inclusion proof let a verifier check a leaf without downloading the whole tree?
Suppose a block header contains a Merkle root, and you want to prove that transaction C is in that block. You do not send all transactions. You send C itself, or its leaf hash depending on context, plus the sibling values needed to reconstruct the route to the root.
In the four-item example, the verifier needs the hash of D, because C and D combine into one parent. The verifier also needs the hash of the parent built from A and B. With those two pieces, the verifier can recompute the parent of C, then the root. If the recomputed root matches the root already trusted from the block header, then C is proven to be included.
This proof is short because the verifier only needs one sibling per level. In a binary tree with 1,024 leaves, that is about 10 sibling hashes. In a tree with a million leaves, it is about 20. The whole block may be large, but the proof grows logarithmically, not linearly.
This is the central reason Merkle trees are so valuable in distributed systems. They let a party verify membership in a large set without having to possess the entire set. In blockchain language, this makes light-client verification possible. A light client can trust a block header chain, receive a Merkle proof for a transaction, and verify inclusion without downloading full blocks.
Does a Merkle root commit to an ordered list or an unordered set, and why does that matter?
A common misunderstanding is to think a Merkle tree commits to an unordered bag of items. In most blockchain uses, it does not. It commits to an ordered list. If you swap two leaves, you generally get a different root.
That matters because many blockchain objects are meaningful only in order. In Bitcoin, the Merkle root commits to the ordered list of transactions in the block. In Certificate Transparency, the tree hash commits to the ordered list of log entries. In Ethereum’s tries, the commitment depends on keys and path structure, not just values.
The mechanism is simple: parent hashes are computed from left child and right child in a specific order. Hash(left || right) is not treated as the same as hash(right || left). So the root binds not only what data is included, but where it sits in the structure.
That is also why proof verification must know the position of the leaf or, equivalently, the left/right orientation of each sibling on the path. A sibling hash alone is not enough; the verifier must know whether to compute hash(current || sibling) or hash(sibling || current) at each step.
How does a light wallet use a Merkle proof to confirm a Bitcoin transaction?
Imagine a wallet using simplified payment verification wants to confirm that it received a payment in a particular Bitcoin block. The wallet already knows the block header chain, so it knows the block header and the merkle_root field inside that header. What it does not have is the whole block body with all transactions.
A full node can answer this wallet by sending the transaction and a Merkle proof. The proof consists of the neighboring hashes needed to rebuild the path from that transaction’s leaf to the block’s root. The wallet hashes the transaction in Bitcoin’s conventional way for tree construction, which is double SHA-256. It then combines that hash with the first sibling in the order specified by the proof. That produces the parent hash one level up. It repeats the process with the next sibling, and then the next, until it reaches a single computed value.
If that final value equals the merkle_root already present in the trusted block header, the wallet has learned something precise: the transaction was part of the transaction list committed to by that block. The wallet has not learned that the transaction is valid in every deeper sense, nor that the chain tip is final forever. It has learned the narrower claim that this transaction is included in that block commitment. That distinction matters, because Merkle proofs establish inclusion, not every other property one might care about.
What is the formal construction of a Merkle tree and how are internal nodes derived?
At a high level, a Merkle tree is built from two ingredients: a set of leaf values and a rule for hashing upward. Ralph Merkle’s original tree-authentication construction defined a recursive function that hashes leaves, then hashes pairs of child values until a root is reached. That root acts as the public commitment to all underlying leaves.
In modern ordinary language, you can define it like this. Start with leaf data values d0, d1, ..., dn-1. Compute a leaf hash for each. Then recursively compute each internal node as the hash of its left child hash concatenated with its right child hash. The root is the single hash produced at the top.
Some systems add domain separation, meaning leaves and internal nodes are hashed in distinguishable ways. Certificate Transparency v2 does this explicitly: a leaf is hashed as `HASH(0x00
leaf_data), while an internal node is hashed as HASH(0x01 | left_hash | right_hash)`. The purpose is subtle but important. Without domain separation, there can be ways to confuse a leaf encoding with an internal-node encoding. With domain separation, the verifier can distinguish what kind of object each hash stands for, improving second-preimage resistance. |
Not every blockchain Merkle construction uses the same conventions. Bitcoin uses double SHA-256 throughout the tree and has its own implementation details. Ethereum’s modified tries use Keccak-256 over encoded nodes, with node types and path encodings that differ from a plain binary hash tree. So Merkle tree names a family of authenticated-hash structures, not one single byte-for-byte format.
How does Bitcoin build its Merkle tree and handle odd numbers of leaves?
| Aspect | Bitcoin rule | Protocol effect |
|---|---|---|
| Hash function | Double SHA-256 | Canonical network interop |
| Leaf definition | Double-SHA256(transaction bytes) | Matches header commitment |
| Odd-count rows | Duplicate last hash | Deterministic tree shape |
| Stored commitment | merkleroot in block header | Light-client trust anchor |
| Delivery mechanism | merkleblock / SPV | Bandwidth-efficient inclusion |
Bitcoin’s block-level Merkle tree is a good canonical starting point because it is conceptually simple. The leaves are the ordered transaction hashes in the block. Internal nodes are built by concatenating two 32-byte child hashes and applying double SHA-256 again. The resulting Merkle root is stored directly in the block header.
There is one implementation detail that often surprises readers: when a row has an odd number of hashes, Bitcoin duplicates the last hash in that row to make a pair. That rule is not mathematically necessary in the abstract; it is a design convention that makes tree construction deterministic for non-power-of-two leaf counts. Different Merkle-based systems handle uneven trees differently, so this is a good example of what is fundamental versus what is conventional. The fundamental part is recursive authenticated aggregation. The duplication rule is a specific protocol choice.
This root in the block header is what allows a light client to ask, “Show me proof that transaction T is in block B,” and receive only a partial tree instead of the whole block. Bitcoin’s merkleblock mechanism was built around exactly this idea for filtered block serving. The economic effect is straightforward: many participants can verify more with less bandwidth.
But this also shows a limit. A Bitcoin transaction Merkle proof only proves inclusion in the transaction set committed by that header. It does not by itself prove, for example, that the transaction spends unspent outputs correctly. Full validation still requires more state and more rules than the tree alone carries.
Can Merkle constructions prove append-only history, and how do consistency proofs work?
| Proof type | Purpose | Prover reveals | Verifier assures | Typical size |
|---|---|---|---|---|
| Inclusion proof | Prove a leaf is included | Leaf value plus sibling hashes | Leaf is in the tree for that root | log2(n) hashes |
| Consistency proof | Prove append-only evolution | Hashes of shared subtrees | Later root extends earlier root | log2(n) hashes |
In blockchains, Merkle trees are often introduced as inclusion-proof machines. That is correct, but incomplete. A related and very powerful idea is that certain Merkle constructions can also prove that a later commitment is an append-only extension of an earlier one.
Certificate Transparency makes this explicit with consistency proofs. If a log once advertised a root for the first m entries, and later advertises a root for the first n entries where n > m, a consistency proof can show that the later tree preserves the earlier prefix unchanged. In other words, the log did not rewrite history; it only appended entries.
This matters because the real security problem is not just “is item x included?” but also “did the committed history evolve honestly?” The Merkle structure makes this efficient because the recursive decomposition of the tree exposes shared subtrees between the old and new versions. A small proof can therefore establish a large structural fact: same prefix, larger tree.
That idea shows up conceptually in blockchain systems too. Whenever a protocol wants to prove not just membership in a state, but lawful evolution from one committed state to another, it is exploiting the fact that authenticated trees preserve structure across versions.
Why do blockchains use Merkle roots and what verification benefits do they provide?
A blockchain is really a machine for producing public commitments over changing data. Blocks commit to transactions. State roots commit to account balances, contract storage, or receipts. Data Availability and fraud-proof systems commit to larger structured datasets. Merkle-style hashing is useful because it lets these commitments stay short even while the underlying data grows large.
There are two consequences that make the structure especially attractive.
The first is efficient verification by constrained nodes. Light clients, bridges, rollup verifiers, and proof systems often cannot afford full data download. Merkle proofs let them verify narrowly targeted claims against a root they already trust from consensus.
The second is composability. Once data is reduced to a root, that root can be embedded elsewhere: in a block header, a signed checkpoint, a bridge message, or another proof system. The root acts like a cryptographic handle for a much larger object. This is why block headers can stay small while still committing to large transaction sets.
The broader lesson is that Merkle trees are not mainly about storage tricks. They are about turning large mutable structures into compact commitments with cheap sub-claims.
Why does Ethereum use a Merkle Patricia trie instead of a plain Merkle tree?
Ethereum shows both the power and the limitations of the plain binary Merkle tree. A blockchain does not only need to commit to a list of transactions; it also needs to commit to a large key-value state that changes after every block. For that job, a simple binary tree over a list is awkward, because state is naturally looked up by key, updated incrementally, and often sparse.
That is why Ethereum uses a modified Merkle Patricia trie rather than a plain transaction-style binary Merkle tree for state. The root still serves the same high-level purpose: it is a cryptographic identity of the state. But the internal structure is adapted to key-based retrieval. Paths are derived from keys, nodes have different types such as branch, extension, and leaf, and encoding rules compress long sparse paths.
The key point is continuity, not difference. Ethereum did not abandon the Merkle idea; it specialized it. The state root, transactions root, and receipts root in block headers are still compact commitments whose security comes from recursive hashing of structured content. Inclusion proofs still work by revealing enough intermediate nodes to recompute the trusted root.
This is also a reminder that the phrase Merkle tree in blockchain discussions often points to a broader family: plain binary trees, Patricia-Merkle tries, sparse Merkle trees, and newer relatives such as Verkle trees. They solve related commitment problems under different performance constraints.
What cryptographic and encoding assumptions must hold for Merkle proofs to be trustworthy?
A Merkle tree is only as trustworthy as the hash function and the construction details around it. If attackers could efficiently find collisions or second preimages, they could try to make different datasets produce the same root or craft misleading proofs. The tree does not create security from nothing; it concentrates the security assumptions of the hash function.
There are also encoding assumptions. The verifier must know exactly how leaves are formed, how internal nodes are formed, how ordering works, and how odd-length cases are handled. If implementations disagree on those details, they compute different roots from the same apparent data. That is why specifications are fussy about byte order, serialization, and prefixes. Bitcoin’s byte-order conventions are a famous source of confusion; some displayed hashes appear in little-endian form, so implementations must handle reversal conventions carefully.
A subtle but important point is that a Merkle proof proves inclusion relative to a specific root. So the real trust question becomes: why do you trust that root? In a blockchain, the answer is usually “because consensus put that root in a block header I trust.” In Certificate Transparency, it may be because the root came from a signed tree head and was cross-checked by monitors. The proof itself does not solve the trust-anchor problem; it assumes one.
What common misunderstandings and implementation mistakes break Merkle-proof security?
The most common misunderstanding is to think Merkle proofs prove more than they do. An inclusion proof does not prove truth in a broad semantic sense. It proves that a piece of data is included in a structure committed to by a particular root. If the committed data itself is fraudulent, incomplete, or shown inconsistently to different users, the Merkle proof can still verify perfectly.
Certificate Transparency makes this limitation explicit: a log can undermine auditing if it presents inconsistent views to different clients. Merkle proofs can show consistency relative to a visible root history, but they cannot by themselves stop all equivocation unless the ecosystem has gossip, monitoring, or other cross-checking mechanisms.
A second misunderstanding is to treat proof verification bugs as rare edge cases. In practice, systems that rely on proofs can fail when contracts or clients mishandle proof structure, replay conditions, or uniqueness checks. The Polygon Plasma bridge vulnerability, for example, was reported as allowing the same proof to be reused many times. That was not a failure of hash trees as a mathematical idea; it was a failure in how a proof-consuming system enforced the broader validity conditions around the proof. This distinction matters because secure use of Merkle commitments is partly cryptographic and partly application logic.
When should systems use sparse Merkle trees, Patricia tries, or Verkle trees instead of plain Merkle trees?
| Structure | Proof size | Best for | Crypto assumptions | Proof complexity |
|---|---|---|---|---|
| Binary Merkle tree | O(log2 n) hashes | Block or transaction lists | Standard hash functions | Fast hash ops |
| Sparse Merkle tree | O(log n) fixed-height | Very large sparse key spaces | Standard hash functions | Similar to Merkle |
| Merkle Patricia trie | O(log n) by key path | Key-value state (Ethereum) | Hashing + path encoding | Path-encoded node proofs |
| Verkle tree | O(logk n); much smaller | Bandwidth-constrained huge states | Vector / polynomial commitments | Heavier crypto multiproofs |
If Merkle trees are so good, why do systems keep inventing sparse Merkle trees, Merkle Patricia tries, and Verkle trees? Because the basic binary tree gives a clean tradeoff, not a perfect one.
A binary Merkle proof has size proportional to tree height, roughly log2(n). That is already excellent, but for extremely large states and bandwidth-constrained settings, even logarithmic proofs can still be too large. Sparse Merkle trees adapt the structure to enormous key spaces with mostly empty leaves. Merkle Patricia tries adapt it to efficient authenticated key-value storage. Verkle trees replace hash-based parent aggregation with vector commitments to get much smaller proofs, at the cost of heavier cryptography and higher computational complexity.
So the design space is about what resource is scarce. If computation is cheap and proof size is the bottleneck, you may move toward Verkle-like commitments. If you want simple, conservative cryptography with well-understood assumptions, plain hash-based Merkle structures remain attractive. The original Merkle idea survives because the root problem has not changed: compact commitment, efficient partial verification.
Conclusion
A Merkle tree is a way to make a large body of data act like a single short commitment, while preserving the ability to prove small pieces of that data efficiently. The root is the compact commitment; the proof path is the local evidence; the hash function is the security foundation.
That is why Merkle trees sit so naturally inside blockchains. They let blocks commit to many transactions, let light clients verify inclusion without full downloads, and let more advanced systems commit to state, logs, and evolving datasets. The details vary from Bitcoin’s transaction tree to Ethereum’s modified trie, but the memorable core is simple: hash upward so one small root can stand in for a large structured whole.
What should you understand before relying on Merkle proofs for transfers or trading?
Merkle proofs establish that a piece of data is included in a specific committed root, but they do not by themselves prove semantic validity or consensus finality. Before you trade, transfer, or rely on a proof, confirm the root’s provenance and the chain’s finality rules; on Cube Exchange follow a clear deposit-and-verify workflow to reduce risk.
- Fund your Cube account with fiat or a supported crypto transfer and make sure you choose the correct network (e.g., BTC vs. Wrapped BTC).
- For incoming on-chain deposits, open a public block explorer, find your deposit tx, and wait the chain’s recommended confirmation count (example: ~6 confirmations for Bitcoin; follow the specific chain guidance for others).
- If a third party supplies a Merkle inclusion proof (light-client style or bridge relay), verify the Merkle root appears in the block header shown by multiple explorers or node sources before acting.
- After confirmations and root verification, open the relevant market or withdraw/transfer flow on Cube, choose an order type (use a limit order for price control or a market order for immediate execution), review fees and destination network, then submit.
Frequently Asked Questions
A Merkle proof contains the target leaf (or its leaf hash) plus the sibling hashes at each level needed to recompute the root; the verifier combines the leaf with each sibling in the specified left/right order up the tree and checks the final computed value equals the trusted Merkle root. Because a binary tree of n leaves has height ≈ log2(n), the proof needs about one sibling per level (e.g., ~10 siblings for 1,024 leaves, ~20 for a million), so proof size grows logarithmically rather than linearly.
A Merkle proof only proves that some data is included in the specific committed structure whose root you trust; it does not by itself prove semantic correctness such as transaction validity, double-spend freedom, or consensus finality. You must still trust the source of the root (for example, the consensus that put a root in a block header) and perform any additional checks required by the application.
Most blockchain Merkle constructions commit to an ordered list because parents are computed as hash(left || right), which is not symmetric; swapping leaves normally changes the root. Therefore proofs must convey the position/orientation (left or right) at each level so the verifier hashes in the correct order.
The security of a Merkle commitment depends on the hash function’s collision and second-preimage resistance and on agreement about exact encoding rules (leaf/internal prefixes, byte order, odd-node handling). Implementation mismatches (endianness, different leaf encodings, or divergent odd-node conventions) or hash weaknesses can make two implementations compute different roots or allow forged-looking proofs, so precise spec agreement is essential.
Ethereum uses a modified Merkle Patricia trie rather than a plain binary Merkle tree so the root commits to a key-addressable key-value state; the trie encodes key-paths into node types (branch, extension, leaf) and inlines small nodes, which makes key lookup and incremental updates efficient while still enabling inclusion proofs via intermediate nodes. This is a specialization of the Merkle idea for sparse, key-indexed state.
Designs like sparse Merkle trees, Merkle‑Patricia tries, and Verkle trees trade off proof size, computational cost, and cryptographic assumptions: sparse trees handle huge sparse key spaces, Patricia tries make authenticated key-value lookups efficient, and Verkle trees (vector commitments) can give much smaller proofs at the cost of heavier, less-standard cryptography and higher prover work. The choice depends on which resource (bandwidth, CPU, or conservative crypto assumptions) is most constrained.
Merkle constructions can also prove append-only consistency: a consistency proof demonstrates that a later root is an append-only extension of an earlier root by exposing shared subtrees so the verifier sees that the earlier prefix was preserved. This is the mechanism Certificate Transparency uses to show logs grew honestly without rewriting history.
Bitcoin’s Merkle tree convention duplicates the last hash in a level when there is an odd number of nodes so pairing is deterministic; this is an implementation choice (not mathematically necessary) that makes tree construction well-defined for non-power-of-two leaf counts and is part of Bitcoin’s practical format.
A Merkle root is only as trustworthy as the root’s origin: the tree proof verifies inclusion relative to that root but does not solve the trust-anchor problem; in blockchains the root is trusted because consensus placed it in a block header, and in logs it is trusted because it was signed/published and cross-checked by monitors or other out‑of‑band mechanisms.
Related reading