What Is Consensus Safety?
Learn what consensus safety means in blockchains: how protocols prevent conflicting finality, why safety differs from liveness, and what assumptions it needs.
Introduction
Consensus safety is the part of a consensus protocol that prevents a distributed system from accepting contradictory outcomes. In a blockchain, that usually means the system should not let two conflicting blocks, transactions, or state transitions both become accepted as final. Without safety, a ledger can keep running and still fail at its basic job: providing a single shared history that everyone can rely on.
The reason this topic matters is that distributed systems are built from parts that can disagree for perfectly ordinary reasons. Messages arrive late. Nodes crash. Some machines lie. Networks partition. Clocks drift. Under those conditions, getting every participant to see exactly the same events in exactly the same order is not automatic. It is a protocol achievement, and safety is the part of that achievement that says: even in the middle of confusion, the system must not cross certain lines.
That line is easiest to see through the failure it prevents. Imagine Alice pays the same coin to Bob on one branch and to Carol on another. If the system allows both branches to become final, there is no longer a single ledger; there are two incompatible truths. The same issue appears in smart-contract systems. If one subset of nodes treats a liquidation as final and another finalizes a conflicting state, the problem is not merely delayed progress. It is a broken state machine. Safety is what rules out that kind of contradiction.
The subtlety is that safety is not the same thing as speed, throughput, or even forward progress. A protocol can be perfectly safe and make no progress for a while. In fact, many consensus designs are built exactly that way: when the network becomes too uncertain, they would rather stop finalizing than risk finalizing two incompatible histories. That tradeoff is not an implementation detail. It is a consequence of deep limits on distributed agreement.
What does consensus safety mean and why is it phrased as “nothing bad is ever decided”?
| Property | Guarantee | When it must hold | Tolerance for halt | Typical metric |
|---|---|---|---|---|
| Safety | No conflicting decisions | Always | May pause progress | Finality / invariant |
| Liveness | Some decision eventually | Under timing assumptions | Cannot tolerate permanent halt | Throughput / latency |
The shortest useful definition is this: safety means correct participants do not decide conflicting values. In blockchain terms, that often becomes: honest nodes do not finalize two different blocks at the same height, or two incompatible checkpoint histories, or two states that cannot both arise from one valid sequence of transactions.
There is an important asymmetry hidden in that definition. Safety is about preventing a bad event from ever happening. Liveness, by contrast, is about ensuring a good event eventually happens. Those are different kinds of guarantees. If a protocol temporarily stops, safety can still hold. But if a protocol finalizes a contradiction even once, safety has already failed, and no amount of later recovery can undo the fact that the protocol allowed mutually incompatible decisions.
This is why safety is often treated as the harder boundary. Engineers can sometimes tolerate delayed confirmations, stalled finality, or a temporary halt. They cannot tolerate a system that tells two users incompatible things are both irrevocably true. A safe protocol may become conservative under stress. An unsafe one becomes unreliable at the exact moment reliability matters most.
A useful way to think about it is as an invariant. An invariant is a property that must remain true throughout execution, not merely at the end. For consensus, the central invariant is that the set of decided or finalized outcomes must remain mutually compatible. Different protocols express compatibility differently. In a linear log replication system such as PBFT, it means all non-faulty replicas agree on one total order of requests. In a BFT-finality system such as Tendermint or GRANDPA, it means no two conflicting blocks can both satisfy the protocol’s commit or finalization rule. In Ethereum-style finality gadgets, it means the finalized checkpoint set cannot contain conflicting branches.
That is the compression point for the whole topic: consensus safety is fundamentally about preserving one coherent history under uncertainty. Once that clicks, many technical rules that seem arbitrary start to make sense. Quorum sizes, vote-locking, slashing rules, prepared certificates, checkpoint proofs, and view changes are all mechanisms for protecting that invariant.
Why is achieving consensus safety hard in distributed systems?
The difficulty comes from the fact that each participant sees only a local picture. No node directly observes “the global state of the network.” It only sees the messages that have reached it so far. If messages can be delayed arbitrarily, then from a node’s perspective there is an ambiguity it cannot resolve: is another node slow, disconnected, crashed, or malicious? Those cases can look identical for a while.
This matters because deciding too early can create conflicting decisions. Suppose two groups of nodes are temporarily cut off from each other. Each group sees silence from the other side. If both are allowed to move ahead and finalize based only on what they can currently observe, they may commit incompatible values. Safety therefore demands some rule that makes this impossible. Usually that rule takes the form of quorum intersection: any two quorums large enough to decide must overlap in enough honest participants that conflicting decisions cannot both be certified.
But there is a deeper constraint. The classic FLP impossibility result shows that in a fully asynchronous system, deterministic consensus cannot guarantee termination even with just one faulty process. The practical lesson is not “consensus is impossible.” It is narrower and more important: if you refuse to assume any eventual timing regularity at all, then a deterministic protocol cannot guarantee both agreement and eventual decision in all executions. That is why modern protocols separate the guarantees. Safety must hold regardless of timing chaos; progress is usually guaranteed only once the network becomes well-behaved enough.
This is exactly the role of partial synchrony, the model that underlies much modern consensus design. In partial synchrony, there is eventually some bound on message delay, but participants may not know that bound in advance, or it may only start holding after an unknown global stabilization time. Dwork, Lynch, and Stockmeyer showed that safety and termination can be separated cleanly in such models: the protocol can require safety under any asynchrony, while requiring termination only when timing bounds eventually hold. That separation is the backbone of practical BFT consensus.
Why do consensus protocols often prioritize safety over liveness?
Because of these limits, well-designed consensus protocols usually privilege safety over liveness. When the network is healthy, they aim for both. When the network becomes ambiguous, they are designed to keep the invariant and sacrifice progress if necessary.
This is why operators sometimes say a chain has “stalled” or “stopped finalizing” during an incident. That can be bad, but it is not the same as a safety failure. In fact, a stall is often evidence that the protocol’s guardrails are working: the system detected conditions under which safe agreement could not be established, so it refused to finalize further blocks. The opposite behavior (continuing to finalize through uncertainty with no strong protection against conflicting finalization) would be much more dangerous.
PBFT states this distinction explicitly. Its safety does not rely on synchrony, but its liveness does. Under prolonged unbounded delays, the protocol may stop making progress, yet it still preserves agreement among non-faulty replicas as long as the fault threshold is respected. Tendermint makes a similar tradeoff: with less than one-third Byzantine voting power, if a correct validator decides on block B, then no correct validator can decide on a different block, while liveness depends on partial synchrony and timing assumptions. Gasper, Ethereum’s proof-of-stake design combining Casper FFG with LMD GHOST, similarly separates safety from stronger liveness claims and frames safety as the absence of conflicting finalized blocks.
This is not merely a common design style. It reflects the structure of the problem. Progress is an eventual property. Safety is an always property. When a protocol cannot have both under all circumstances, it is almost always better to preserve the always-property.
How do consensus protocols enforce safety (quorums, locks, and evidence)?
Although consensus families look different on the surface, many of them protect safety using the same underlying mechanism: they ensure that any certificate strong enough to finalize one value must overlap with any certificate strong enough to finalize a conflicting value in at least one honest participant, and that honest participant is constrained not to support both.
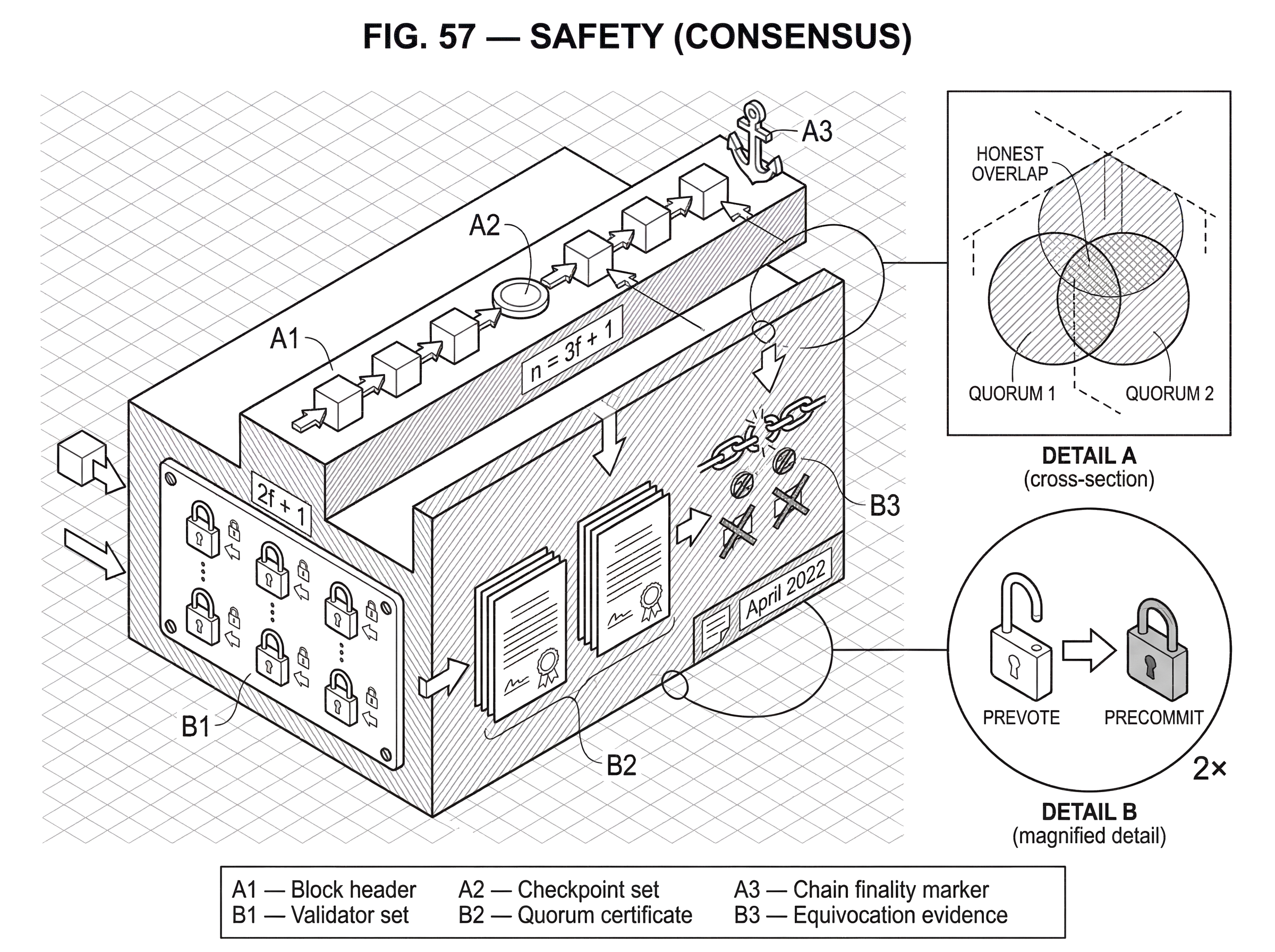
The arithmetic is the heart of it. In Byzantine-fault-tolerant systems tolerating up to f faulty participants, a common threshold is n = 3f + 1 total participants and a decision quorum of 2f + 1. Why these numbers? Because any two sets of size 2f + 1 drawn from 3f + 1 participants must intersect in at least f + 1 participants. Since at most f can be Byzantine, the overlap contains at least one honest participant. If honest participants follow a rule that prevents them from endorsing conflicting values, then two conflicting decision quorums cannot both exist.
That is the mechanism. The rest of the protocol is about making the honest-overlap rule real in an adversarial network.
In PBFT, the protocol uses the three familiar phases (pre-prepare, prepare, and commit) to make replicas converge on one sequence number and one request ordering. A replica becomes prepared for a request when it has logged a matching pre-prepare and enough matching prepares; it becomes committed-local when it has enough matching commits to execute safely. Those intermediate states are not bureaucratic overhead. They are the memory of the protocol. During a leader change, they prevent a new leader from proposing an order that conflicts with one already sufficiently supported. The protocol preserves safety by carrying forward evidence of what could already be committed.
Tendermint expresses the same idea through prevotes, precommits, and locking. A validator that has observed enough support for a block becomes locked on it and does not freely move to a conflicting block in later rounds unless specific conditions are met. The lock is what gives the quorum intersection arithmetic teeth. If a block received a supermajority strong enough to lead honest validators into a lock, then a conflicting block cannot later collect another valid supermajority unless enough validators equivocate; and if that happens at scale, the system treats it as accountable Byzantine behavior.
Ethereum’s finality gadget uses a checkpoint structure instead of one-shot block commits, but the logic is similar. Finalization depends on supermajority links among checkpoints. The slashing conditions are designed so that validators cannot cast pairs of attestations that would allow conflicting checkpoint histories to both become finalized. The protocol’s accountable safety theorem says that if conflicting finalization occurs, there must be slashable evidence against at least one-third of stake. Safety is therefore not just “hopefully true.” It is tied to a concrete contradiction in validator behavior.
GRANDPA pushes the same pattern into a finality gadget framework. Blocks may be produced optimistically by another mechanism, but finality comes from votes that identify a block and its ancestry. If conflicting blocks are finalized, the protocol can construct evidence identifying Byzantine voters responsible for the contradiction. Again, the basic structure is quorum overlap plus honest voting restrictions plus evidence when those restrictions are violated.
Why does a two‑thirds (2f+1) quorum matter for safety in BFT systems?
| Parameter | Formula | Intuition | Consequence |
|---|---|---|---|
| n | n = 3f + 1 | Total validators bound | Sets adversary threshold |
| Quorum | 2f + 1 | Supermajority decision set | Requires honest overlap |
| Overlap | ≥ f + 1 | At least one honest | Prevents conflicting quorums |
| Max faulty | f | Allowed adversarial nodes | Safety holds if ≤ f |
Consider a network with n = 4 validators and fault tolerance f = 1. The protocol requires 2f + 1 = 3 votes to finalize a block. Now imagine block X gets finalized. That means three validators voted for X. Since only one validator can be Byzantine, at least two of those three are honest.
Now ask whether a conflicting block Y at the same height could also be finalized. It would also need three votes. But among four validators, any two groups of three overlap in at least two validators. Since at most one validator is Byzantine, at least one overlapping validator is honest. If honest validators never cast conflicting finality votes for both X and Y, then Y cannot gather a valid quorum after X has already done so.
That is the reason threshold systems often center on two-thirds. It is not aesthetic. It is the smallest supermajority that still forces enough overlap under a one-third Byzantine bound.
Now notice what changes if the assumptions change. If half the validators can be Byzantine, the overlap argument no longer protects you in the same way, because the overlapping participants might all be adversarial. Or if honest validators are allowed to vote inconsistently after seeing delayed messages, the intersection still exists but the protocol rule is too weak to use it. Safety therefore depends on both quorum math and validator behavior rules. Neither is sufficient alone.
How does safety differ in Nakamoto‑style (longest‑chain) consensus?
| Design | Finality type | Safety guarantee | Typical evidence | When finality holds |
|---|---|---|---|---|
| BFT systems | Deterministic / instant | Conflicting finality impossible | Supermajority certificates | Immediately after commit rule |
| Nakamoto style | Probabilistic / eventual | Reversal probability falls over time | Chain depth confirmations | After many confirming blocks |
Not all blockchains use deterministic BFT-style finality. In Nakamoto-style consensus, including Bitcoin and some proof-of-stake descendants, safety is typically probabilistic rather than absolute at a particular moment. The system does not usually produce a crisp event saying “this block is now impossible to reverse under the protocol rules.” Instead, the chance of reversal falls as more blocks accumulate on top of it.
That means the meaning of safety changes slightly. It is still about avoiding contradictory accepted histories, but the guarantee is no longer usually phrased as “no correct node can ever finalize a conflicting block after this point.” It is phrased in terms of very low reorganization probability under assumptions about honest majority resources, network conditions, and adversarial power.
This is why the connection between safety and finality depends on the architecture. In BFT-style systems, finality is often deterministic and direct: once the commit rule is met, conflicting finalization should be impossible unless the fault threshold was exceeded or the assumptions were violated. In longest-chain systems, finality is economic and probabilistic: safety improves with confirmations, but no single confirmation depth is a theorem-free magic number divorced from assumptions.
The common thread is still coherent history. The difference is whether the protocol enforces it with explicit finalization certificates or with probabilistic chain selection dynamics.
What assumptions does consensus safety rely on (network, fault, and cryptographic models)?
A consensus protocol does not promise safety in a vacuum. Its guarantee is always conditional on a fault model and a network model.
The fault model says what bad actors are allowed to do. A fail-stop fault means a node can simply stop. An omission fault means it may fail to send or receive some messages. A Byzantine fault means it can behave arbitrarily: send contradictory messages, lie about state, or coordinate strategically. Safety thresholds depend sharply on which model you assume. Under partial synchrony, Dwork, Lynch, and Stockmeyer showed exact resiliency thresholds such as n >= 2t + 1 for fail-stop or omission faults and n >= 3t + 1 for Byzantine faults. Those numbers are not implementation folklore; they are structural limits.
The network model says what message delays may occur. If you assume full synchrony, you can often get stronger timing guarantees. If you assume complete asynchrony, FLP tells you deterministic progress guarantees hit a wall. If you assume partial synchrony, you can often design protocols where safety is unconditional and liveness resumes after stabilization. Much of practical blockchain consensus lives in this middle ground.
There is often also a cryptographic model. PBFT relies on message authentication and a computationally bounded adversary. Gasper and Tendermint rely on signatures and slashing evidence. Ouroboros Praos adds assumptions about honest-majority stake, semi-synchronous communication, and cryptographic primitives such as forward-secure signatures and VRFs. If those assumptions are broken, the protocol may still run, but the formal safety theorem may no longer apply.
This is why saying “the chain is safe” without naming the model is imprecise. Safe against what? Under what network conditions? Up to what fraction of Byzantine stake or validators? With what key-security assumptions? Consensus safety is always safety under stated conditions.
What does a real consensus safety failure look like in practice?
A real safety failure is not just turbulence. It is the protocol allowing incompatible histories to be accepted as final, or forcing different correct participants into irreconcilable states.
Sometimes the danger appears first as a liveness incident. Solana’s April 2022 outage is a useful example of the distinction. A huge transaction flood caused validators to run out of memory and crash; insufficient votes landed to finalize earlier blocks, abandoned forks could not be cleaned up, and consensus stalled. That was operationally severe, but the notable point for this topic is the shape of the failure: the system failed to keep making progress. It did not become safe by continuing incorrectly; it became unavailable because it could not safely finalize. That is a liveness breakdown with safety implications, not a textbook conflicting-finality event.
By contrast, some systems build explicit accountability around genuine safety failures. Tendermint notes that if two blocks at the same height each carry two-thirds commit signatures, then at least one-third of validators must have signed duplicitously. Gasper similarly ties conflicting finalization to slashable stake. GRANDPA provides a challenge procedure to identify Byzantine voters if conflicting blocks are finalized. In these systems, a safety failure is not merely “some nodes were confused.” It creates cryptographic evidence that the protocol’s non-equivocation rules were violated at scale.
There is also a broader layer above protocol mechanics: social consensus. Ethereum’s DAO hard fork is the canonical illustration. The protocol history was altered through a social decision implemented as a hard fork. This was not a consensus-safety failure in the narrow theorem sense; it was a governance override of what the chain history would be. The lesson is that protocol safety and social finality are related but not identical. A chain can have strong protocol-level safety and still be subject, in extraordinary circumstances, to human coordination that changes which history the community treats as canonical.
Common misunderstandings about consensus safety
A common misunderstanding is to equate safety with “the network stays up.” That is liveness or availability, not safety. A halted but non-contradictory system may be safe. A fast-moving system that finalizes conflicting states is unsafe.
Another misunderstanding is to think safety means “no forks ever happen.” Many systems can temporarily fork at the proposal or observation layer while still preserving safety at the finality layer. What safety rules out is conflicting decisions, not every transient disagreement about the head of the chain.
A third misunderstanding is that cryptography alone gives safety. Signatures help identify senders and prove equivocation, but they do not replace the need for quorum intersection or synchrony assumptions. Dwork, Lynch, and Stockmeyer even note that in partially synchronous communication models, authentication does not improve Byzantine resiliency thresholds. Cryptography is a tool inside the protocol, not a substitute for the protocol’s structure.
Conclusion
Consensus safety is the guarantee that a distributed system will not decide contradictory outcomes. In blockchains, that is what prevents two conflicting histories from both becoming final. The mechanism behind it is usually some combination of quorum intersection, rules that constrain honest voting, and evidence that exposes large-scale equivocation when those rules are violated.
The most important thing to remember is simple: when conditions are uncertain, a safe consensus protocol would rather delay finality than fake agreement. That is why safety sits at the foundation of blockchain finality, double-spend resistance, and shared state correctness. If tomorrow you forget the details, keep this: safety is the property that preserves one coherent history even when the network cannot yet agree on everything else.
What should I understand about consensus safety before depositing, trading, or transferring?
Before you deposit, trade, or transfer an asset, understand the chain’s finality model and how that affects reversals so you can adjust confirmations, withdrawal timing, and order execution accordingly. On Cube Exchange you can fund your account and execute trades or withdrawals while observing the chain-specific finality guidance described below to reduce the risk of reversals or unexpected stalls.
- Fund your Cube account with fiat or a supported crypto transfer to the exact chain and token you plan to use (choose the network carefully when multiple networks host the same token).
- Check the chain’s finality model: if it’s BFT-style, record the finality condition (e.g., two‑thirds commit or finalized checkpoint); if it’s Nakamoto-style, note a safe confirmation depth (e.g., 6+ confirmations for BTC‑like chains) and any recent reorg history.
- Open the relevant market or withdrawal flow on Cube. For trading, prefer limit orders when you need price control; for immediate execution use a market order and account for possible short-lived reorganizations on probabilistic chains.
- For withdrawals or large transfers, wait for the chain-specific finality threshold (BFT finalization or the chosen confirmation depth) before moving funds off Cube or using them as collateral.
- After submitting a withdrawal or trade, monitor on‑chain confirmations and Cube’s transaction status until the finality threshold you recorded is met, then proceed with downstream actions (margin, transfer, or external deposit).
Frequently Asked Questions
Safety is the guarantee that correct participants never decide conflicting values (so two incompatible histories cannot both be finalized); liveness is the guarantee that some desired decision eventually happens. They are different kinds of guarantees: safety must hold always, while liveness is an eventual property and can be sacrificed temporarily to preserve safety.
Because a single contradictory finalization permanently breaks the shared history, protocols are designed to preserve safety even at the cost of halting progress; a temporary stall is preferable to finalizing incompatible states. The article explains this trade-off as a structural consequence of consensus limits rather than an implementation detail.
With up to f Byzantine faults the common threshold is n = 3f + 1 total participants and a decision quorum of 2f + 1 because any two quorums of size 2f + 1 must overlap in at least f + 1 participants, ensuring at least one honest node is in the intersection that prevents two conflicting quorums. That quorum‑intersection arithmetic combined with rules that constrain honest voting is the mechanical basis for safety.
Deterministic consensus cannot guarantee termination in a fully asynchronous model (the FLP result), so practical protocols use partial synchrony: safety is preserved under arbitrary delays, while liveness is guaranteed only after timing stabilizes. This separation (safety unconditional, liveness conditional on eventual bounds) underlies many BFT designs.
BFT-style protocols (e.g., PBFT, Tendermint, GRANDPA) aim for deterministic finality: once the finality rule is met a conflicting finalization should be impossible unless the fault threshold or assumptions are violated. Nakamoto-style (longest-chain) systems provide probabilistic safety, where reversal probability falls with more confirmations rather than producing an absolute, single-step finality event.
A real safety failure is when the protocol allows incompatible histories to be accepted as final or produces cryptographic evidence of large-scale equivocation; the article contrasts liveness incidents (like a halt or stall) with true safety breaches and cites examples such as Solana’s April 2022 stall (operational liveness failure) and community hard forks like the DAO recovery (a social override of history rather than a narrow protocol theorem failure).
No - signatures and other cryptographic tools are necessary but not sufficient: cryptography helps authenticate messages and produce evidence of equivocation, but you still need quorum intersection rules and timing/network assumptions; cryptography does not by itself replace those structural requirements. The article emphasises that safety guarantees are statements about protocol plus model assumptions, not about code or signatures alone.
Related reading