What Is an Audit Trail?
Learn what an audit trail is, why it exists, how it works mechanically, and how logs, integrity, retention, and accountability fit together.
Introduction
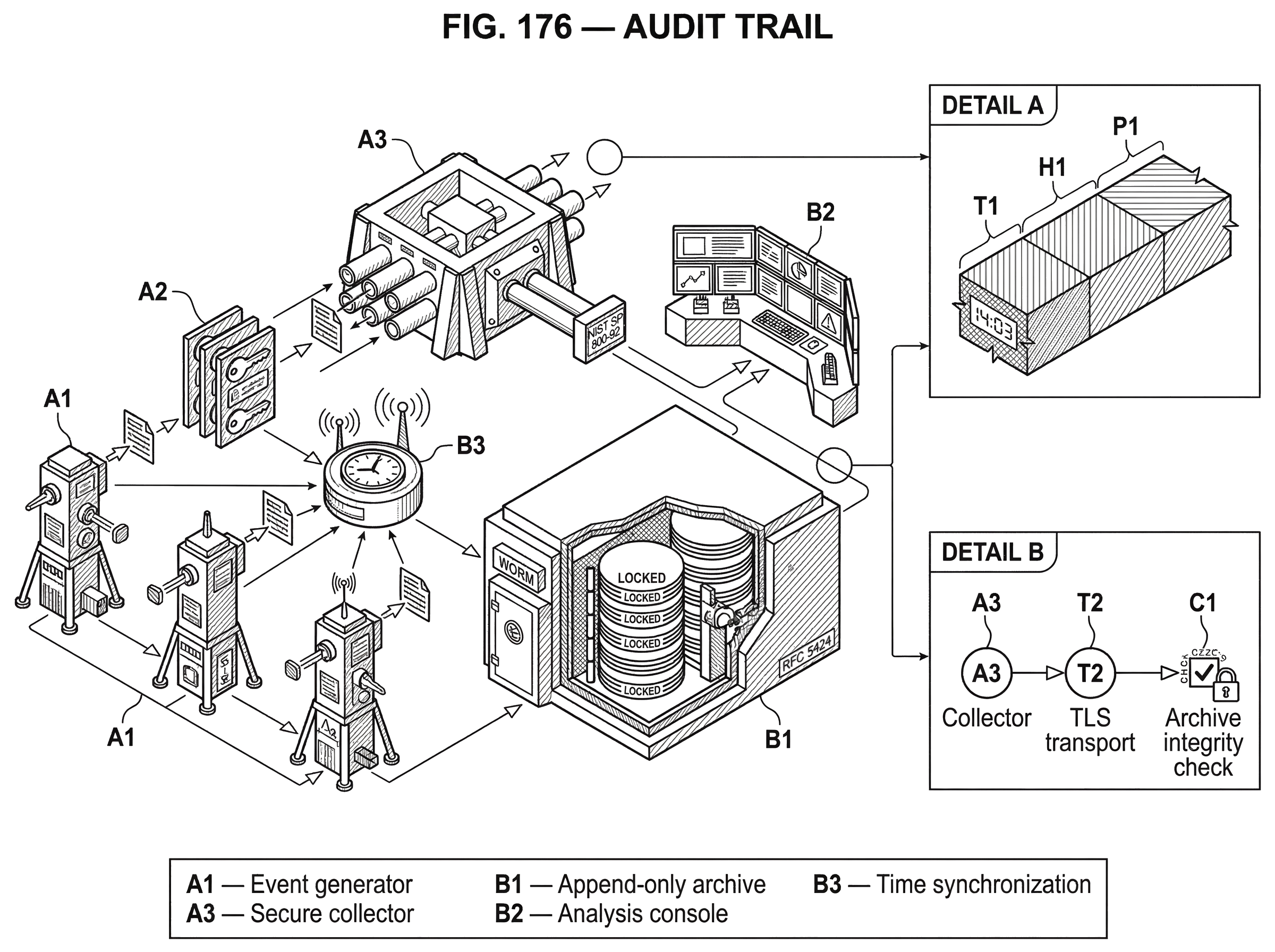
Audit trail is the security concept of keeping a chronological record of actions and events so you can later reconstruct what happened, who did it, and what the outcome was. That sounds simple until you ask the uncomfortable question every incident eventually forces: when something important changes, how do you know whether the record is complete, accurate, and untampered with? The purpose of an audit trail is not merely to collect data. It is to preserve accountability under conditions where systems are distributed, users are privileged, clocks drift, formats differ, and attackers may actively try to erase evidence.
NIST’s glossary captures the core idea in two complementary ways. One definition emphasizes accountability: a record showing who accessed an IT system and what operations they performed during a period. Another emphasizes reconstruction: a chronological record that lets you examine the sequence of activities surrounding a security-relevant operation from inception to result. Those are really the same idea seen from two angles. If you cannot attribute actions to actors, you do not have accountability. If you cannot reconstruct sequence and outcome, you do not have a meaningful trail.
This is why audit trails sit at the center of security controls rather than at the edge as administrative paperwork. Incidents are investigated through them. Fraud is detected through them. Policy violations are demonstrated through them. And when a control changes (a firewall rule, a smart-contract admin role, an allowlist entry, an IAM policy, a validator configuration, a key rotation event) the audit trail is what turns that change from a rumor into a verifiable event in time.
What problem does an audit trail solve?
The underlying problem is memory under conflict. A system is constantly changing: users authenticate, processes start and stop, APIs are called, permissions are granted, transactions are submitted, configurations are modified, and data is read or deleted. Without a durable record, those events vanish into the past. Humans remember selectively, systems expose only current state, and attackers benefit when the path from past to present becomes unclear.
An audit trail solves this by recording not just that an event existed, but enough context to answer the questions that matter later. Typically those questions are: who acted, what action occurred, when it happened, where it originated, whether it succeeded, and what object or resource it affected. PCI DSS Requirement 10 makes this explicit by requiring audit trail entries to include, at minimum, user identification, event type, date and time, success or failure, origination of the event, and the identity or name of the affected data, system component, or resource. That minimum field set is not arbitrary. Each field closes a specific ambiguity that would otherwise make reconstruction fail.
Consider what breaks if one of those pieces is missing. If there is no actor identity, you know an admin action occurred but not which administrator took it. If there is no timestamp, you cannot order the action relative to other events. If there is no target resource, you know something changed but not what changed. If success and failure are not distinguished, repeated failed login attempts blur into successful access. A useful audit trail is therefore not just a pile of messages. It is a record designed to preserve the causal story of security-relevant events.
That same logic applies in blockchain-adjacent systems. A chain itself records transactions and state transitions, but many important actions happen around the chain, not only on it: exchange withdrawal approvals, multisig proposal creation, signer participation, RPC access, key-management operations, validator failover, bridge relayer actions, custody-policy changes, and access-control updates in off-chain infrastructure. The ledger may tell you that a transaction executed. The audit trail tells you why that transaction came to exist, who approved it, from which system, and under what authority.
What makes a record an audit trail rather than just a log
| Record type | Primary purpose | Required fields | Trust level | Typical use |
|---|---|---|---|---|
| Log | operational monitoring | may omit identity or timestamp | low tamper resistance | debugging and metrics |
| Audit trail | accountability and reconstruction | user, action, timestamp, target, result | protected and tamper-evident | forensics, compliance, investigations |
A log is a record of events occurring within systems and networks. NIST SP 800-92 defines logs in exactly that broad way, and defines log management as the process of generating, transmitting, storing, analyzing, and disposing of log data. An audit trail is narrower and more demanding. It is the subset of recorded events organized and protected so that they can support accountability, reconstruction, and examination.
That distinction matters because not every log deserves to be treated as audit evidence. Debug logs help developers diagnose code paths, but they may omit user identity, may not be preserved, and may be casually reformatted. Metrics help operators spot trends, but they aggregate away the individual events needed for attribution. Traces help connect distributed request paths, but they often focus on latency and execution flow rather than administrative intent or security semantics. These telemetry types can enrich an audit trail, but they do not automatically become one.
Here is the mechanism. A record becomes an audit trail when four conditions are met together. It is security-relevant, meaning the event bears on access, changes, decisions, or sensitive operations. It is chronological, so events can be ordered into a sequence. It is attributable, so actions can be linked to a principal or process. And it is trustworthy enough that later readers have some basis for believing it was collected completely and protected from improper alteration.
This last condition is where many organizations fail. They collect abundant logs, but the logs live only on the originating host, can be deleted by local administrators, use inconsistent clocks, and lack any retention discipline. In that setup, the organization has visibility during calm periods but weak evidence during hostile ones. An audit trail must be designed for the moment when the subject of the record has an incentive to change or destroy it.
What structure and fields should an audit event contain?
At a practical level, an audit trail is built from events, and each event needs enough structure to remain interpretable after it leaves the producing system. Some formats do this minimally; others do it richly. RFC 5424, the modern syslog specification, standardizes a message shape with explicit header fields such as priority, timestamp, hostname, application name, process ID, and message ID, plus machine-parseable structured data and optional free-form message text. The importance of this design is not aesthetic. It separates the parts needed for routing, ordering, and parsing from the human-readable message body.
A useful way to think about an event is as a claim with provenance. The claim is that a certain action occurred. The provenance is the metadata that lets you interpret and trust that claim: when the event was produced, by which host or service, on behalf of which user or principal, in which execution context, against which object. Without provenance, an event becomes difficult to correlate and easy to dispute.
Modern telemetry systems make this more explicit. OpenTelemetry defines a common log data model so logs can be represented uniformly, and it allows logs to include TraceId and SpanId for direct correlation with distributed traces. It also carries Resource information, which identifies where the event came from; host, container, pod, application, and similar context. For audit work, this is powerful because many investigations are not about a single isolated event. They are about following one operation across several components: the API gateway that accepted a request, the service that authorized it, the signer that approved it, the queue that relayed it, and the storage layer that committed its result.
The lesson is straightforward: structure is what keeps an audit trail queryable and correlatable after scale arrives. Free-form text can be useful for humans, but free-form text alone is fragile. It requires parsing, parsing fails on edge cases, and inconsistent formatting becomes a tax on every future investigation.
How do you trace a privileged configuration change step by step?
Imagine an institution operating a digital-asset platform. A wallet policy changes at 14:03, and shortly after, a large withdrawal is approved that should have been blocked. The question is not only whether the withdrawal happened. The harder question is whether the policy change caused it, who authorized that change, and whether the records themselves can be trusted.
A good audit trail lets you reconstruct this as a continuous story. First, the identity system records that an administrator authenticated with a specific account and second factor from a particular workstation and source IP. Then the policy service records a request to modify a withdrawal allowlist entry, including the acting user, the object being modified, the previous value, the new value, whether approval workflow requirements were met, and the success result. If a maker-checker model exists, a second event records the reviewer’s approval. The secrets or key-management system may record that a signing policy version was activated. The application layer then records the withdrawal request and the policy evaluation outcome. A trace-linked record may connect that request across the API, risk engine, and signer. Finally, storage or immutable archive infrastructure records receipt and preservation of those events.
Notice what made the reconstruction possible. Not volume. Not verbosity. The decisive factor was that each event carried the fields needed to join it to neighboring events in time, identity, object, and outcome. This is why the best audit trails feel almost boring when read event by event. Their value emerges when many individually plain records line up into a coherent causal sequence.
Now imagine the same scenario with weak logging. The policy service emits only “configuration updated.” The auth service logs successful login events without workstation or IP. The signer logs only that it signed a request, not which policy version authorized it. Timestamps differ by several minutes because systems are not synchronized. In that world, you may strongly suspect abuse, but suspicion is not reconstruction. The audit trail failed because the system recorded activity without preserving the relations between events.
Why are timestamps and event order unreliable, and how do you fix them?
People often hear “chronological record” and assume timestamping is trivial. In reality, time is one of the most failure-prone parts of an audit trail. Systems drift. Time zones vary. Formats differ. Some software records when an event was observed, others when it was generated, and still others when it was indexed. In distributed systems, network delay means arrival order is not always event order.
This is why time synchronization is treated as a control requirement, not just an implementation detail. PCI explicitly requires use of time synchronization technology so critical system clocks are synchronized. RFC 5424 formalizes timestamp representation and even defines a timeQuality structured-data element to express whether time is known, synchronized, and with what stated accuracy. The basic idea is simple: if your event order is unreliable, your explanation of cause and effect becomes unreliable too.
Chronology also depends on transport behavior. Classic syslog over UDP is fast and simple, but NIST notes important limitations: unreliable delivery, no built-in access controls, and no encryption in many legacy implementations. RFC 5424 similarly notes that syslog does not provide end-to-end acknowledgment; messages can be lost, replayed, intercepted, or truncated. So a timestamp alone does not create chronology. Chronology is produced by the combination of synchronized clocks, reliable enough transport, sequence-preserving collection where possible, and awareness of where those assumptions fail.
What are the stages of the audit trail lifecycle and which controls apply at each stage?
| Stage | Main control | Key failure risk | Minimum requirement |
|---|---|---|---|
| Generation | instrument privileged actions | missing critical events | capture actor, action, target, success |
| Transport | secure reliable transport | dropped or replayed messages | TLS or reliable queuing |
| Storage | centralized durable storage | local deletion by admins | append-only or WORM storage |
| Analysis | daily review and alerts | overlooked signals, backlog | timely analysis and triage |
| Disposal | retention policy and privacy | too short or too long | defined retention and access |
NIST’s definition of log management is useful because it frames audit trails as a lifecycle rather than a file. Events are generated, transmitted, stored, analyzed, and eventually disposed of. Security failures can appear at every step.
Generation is where you decide what the system will remember. If you do not instrument privileged actions, authentication events, access to audit logs, and security-control changes, the missing data cannot be recovered later. PCI highlights this by requiring automated audit trails for events such as all individual user access to sensitive data, actions by privileged users, access to audit trails themselves, invalid logical access attempts, and changes to identification and authentication mechanisms. The pattern is clear: log the events whose abuse would matter most.
Transport is where evidence moves from local memory into a broader collection system. This is a dangerous moment because the event is in transit and may be dropped, replayed, or observed. Secure transport choices matter here. RFC 5424 requires implementations to support a TLS-based transport mapping, and recommends its use in deployments. NIST’s guidance similarly pushes organizations away from insecure, unreliable legacy patterns when integrity and confidentiality matter.
Storage is where durability and tamper resistance enter. Keeping the only copy of important events on the same host that produced them is weak by design, especially against privileged attackers. Centralized collection exists partly for operational convenience, but also because it separates evidence from the machine most likely to be compromised. NIST describes multi-tier architectures with log generation at the edge, centralized analysis and storage layers, and monitoring consoles on top. Distributed collectors, caching servers, and even separate logging networks may be used for scale and protection.
Analysis is what turns the trail into action. Routine review identifies incidents, policy violations, operational problems, and fraud, and supports forensic analysis and internal investigations. NIST emphasizes these benefits directly, and PCI requires critical logs to be reviewed at least daily. The purpose of review is not bureaucratic completion. It is to shorten the time between event occurrence and human recognition of a problem.
Disposal matters because audit trails are not kept forever by default, and indefinite retention creates cost, privacy, and security burdens of its own. NIST notes that logs can contain sensitive and personally identifiable information, so privacy and confidentiality protections must apply throughout planning and operation. That means retention is a risk decision, not only a storage decision. Keep too little and investigations fail. Keep too much carelessly and the audit system itself becomes a data-exposure problem.
How do you protect audit records from tampering or deletion?
The central security property of an audit trail is not that it exists, but that it is hard to alter without detection. PCI states this plainly: secure audit trails so they cannot be altered. But this sentence hides a design problem. In real systems, many actors legitimately have some administrative power. So the question becomes: which parts of the trail can be changed, by whom, under what approval, and with what evidence of that change?
The first defense is separation. Forward logs off-host quickly so compromise of the source does not imply compromise of the record. The second is access control. Limit who can read, manage, and delete audit data, and audit those administrative actions too. The third is immutability or append-only storage for high-value records. In cloud environments, this often means object storage with WORM-style retention. Amazon S3 Object Lock is a good concrete example: it prevents object versions from being overwritten or deleted for a retention period or under a legal hold, and in compliance mode even the root user cannot shorten or remove that protection early. That is not an audit trail by itself, but it is a strong building block for preserving one.
This kind of immutability has an important nuance. It protects stored object versions, not the truth of what was originally written. If your collection pipeline is incomplete or maliciously filtered before archival, immutable storage will faithfully preserve an incomplete history. So immutability is necessary for some audit goals, but not sufficient. You also need trustworthy collection and coverage.
The threat model here is not hypothetical. MITRE ATT&CK documents that adversaries clear Windows Event Logs to hide intrusion activity, often using built-in tools such as wevtutil or PowerShell. MITRE CAR further notes that clearing logs is unusual in normal operations and can interfere with event collection and notification, while also pointing defenders to telltale event IDs generated when Windows logs are cleared. These examples are useful because they show the adversary’s logic clearly: if you can damage the audit trail, you reduce the defender’s ability to reconstruct, detect, and prove.
How do you prioritize what to log when audit data volume grows?
It is tempting to think the solution is simply “log everything.” NIST warns against that kind of simplification. The fundamental challenge in log management is balancing limited resources against a continuous and growing supply of heterogeneous log data. There are too many sources, formats differ, timestamps differ, and normalization and advanced processing can be expensive.
So an audit trail is always partly an exercise in prioritization. You are deciding which events are so important that they must be preserved with high fidelity, quick transport, strong protection, and routine review. Security-relevant does not mean every possible state change at maximum detail forever. It means designing for the events whose reconstruction would matter during a real dispute or incident.
This is also where schemas become useful. OpenTelemetry’s common log model and Elastic Common Schema both exist because cross-system logging fails when every team names and structures fields differently. A schema is not the audit trail itself. It is a convention that lowers the cost of correlation, searching, and analysis. The convention is not fundamental; the underlying need for interpretable, consistent event context is fundamental.
Why on‑chain data alone is not a complete audit trail?
| Trail type | What it records | Who provides context | Main limitation | Best for |
|---|---|---|---|---|
| On-chain | final transactions and state | blockchain nodes, explorers | misses off-chain approvals | immutable settlement history |
| Off-chain | approvals, proposals, operator actions | internal systems, SIEM | requires protection from admins | administrative and operational history |
| Combined | both settlement and context | integrated correlating systems | integration and normalization cost | complete investigation evidence |
In blockchain environments, there is a common misunderstanding: that the chain itself is the full audit trail. Public blockchains do provide a durable, ordered record of included transactions and state transitions. That is a remarkable property. But it is only one layer of the evidence story.
Suppose a multisig treasury executes a transfer. The chain can show the transaction, the signers who submitted confirmations on-chain, and the resulting state change. But many questions remain off-chain. Who proposed the transfer inside the organization? Which ticket or business approval justified it? Which signer used which workstation or HSM-backed session? Was an allowlist entry added shortly before execution? Did a monitoring system flag a risk score that was later overridden? Those are audit-trail questions even when the final action settles on-chain.
The same pattern appears with validators, bridges, exchanges, custodians, and wallet infrastructure. The blockchain offers immutable settlement history. The surrounding systems provide the administrative and operational history that explains why settlement occurred. Mature security practice treats these as complementary, not competing, records.
This is also why audit trails are a mechanism for neighboring controls. If an organization uses an allowlist or blocklist, the list itself controls access, but the audit trail records who changed the list and when. Without that trail, the control has enforcement but weak accountability.
Common misconceptions about audit trails and what actually matters
The first misunderstanding is treating audit trails as retrospective only. In reality, they matter during live defense as much as after the fact. Daily review, correlation, and alerting turn the trail into an active detection surface.
The second is assuming that more fields always mean better audit quality. Extra detail can help, but only if it improves attribution, chronology, or reconstruction. Otherwise it raises storage, privacy, and parsing costs without improving evidentiary value.
The third is confusing immutability with truth. An immutable falsehood is still false. Audit quality begins with good instrumentation and trustworthy collection.
The fourth is assuming local admin rights and local logs can coexist safely. They often cannot. If the actor you may need to investigate can erase the record before it is exported, your accountability story is weak by design.
Conclusion
An audit trail is a chronological, attributable, and sufficiently trustworthy record of security-relevant activity that lets you reconstruct what happened from beginning to result. Its purpose is not simply storage. Its purpose is preserving accountability when memory fails, systems are distributed, and some actors may want the record gone.
The key idea to remember is this: an audit trail works when it preserves relationships; between actor and action, action and target, target and outcome, and all of them in time. If those relationships survive collection, transport, storage, and attempted tampering, the trail can support detection, investigation, and control. If they do not, you may still have logs, but you do not really have an audit trail.
How do you secure your crypto setup before trading?
Secure your crypto setup by combining basic operational checks with Cube’s non-custodial MPC protection so you can trade with accountability and recoverability. Start with funding and device enrollment, verify destination and confirmation rules with a small test transfer, then choose the right execution method for the trade.
- Fund your Cube account with fiat via the on‑ramp or with a supported crypto transfer to the provided deposit address.
- Review and confirm your account uses Cube’s non‑custodial MPC key protection, enable multi‑factor authentication (if offered), and record recovery/backup steps or device enrollments recommended during setup.
- When sending to a new address, perform a small test transfer first (for example, a nominal token amount) and verify the required on‑chain confirmation count for that chain before proceeding with larger amounts.
- Open the market for the asset you want to trade. Choose a limit order for price control or a market order for immediate fill, set acceptable slippage and fees, then submit and monitor the fill and on‑chain settlement.
Frequently Asked Questions
An audit trail is a narrower, security-focused subset of logs: it’s the set of recorded events that are security-relevant, can be ordered chronologically, are attributable to a principal or process, and are protected well enough to support later reconstruction and examination. Simply having many or verbose logs does not make an audit trail unless those four conditions are met.
A commonly cited minimum set (echoed in the article via PCI DSS Requirement 10) is: user identification, event type, date and time, success or failure, origination of the event (for example source IP or workstation), and the identity or name of the affected data, system component, or resource. Those fields each remove a specific ambiguity needed for reconstruction.
Reduce tampering risk by forwarding logs off-host quickly (separation), applying strict access controls and auditing those administrative actions, and using immutable or append-only storage for high-value records (for example WORM-style retention such as S3 Object Lock). These controls help but are not foolproof - they must be combined with trustworthy collection and coverage because attackers may subvert generation or transport.
Timestamps are error-prone because clocks drift, different systems record different event times (generated vs observed vs indexed), and network delays can reorder arrivals; therefore time synchronization and expressing time-quality are treated as controls (e.g., synchronized clocks, RFC 5424’s timeQuality element, and PCI requirements for time sync). Chronology requires synchronized clocks plus reliable transport and collection practices so order can be interpreted correctly.
No - immutable storage prevents after-the-fact deletion or overwriting of stored versions but does not guarantee the records are complete or correct; immutability preserves whatever was collected, so you still need trustworthy, complete collection and protected transport to avoid archiving a filtered or falsified history.
No; a blockchain ledger gives an immutable, ordered record of on‑chain transactions, but it often lacks the surrounding administrative and operational context (who proposed or approved a transaction, which off‑chain policy changes preceded it, which signer/session was used). For organizational accountability you still need off‑chain audit records that explain why and how on‑chain actions occurred.
You must prioritize: log the events whose abuse would matter most (privileged actions, authentication, access to audit data, configuration changes), apply consistent schemas to reduce correlation cost (e.g., OpenTelemetry/ECS conventions), and balance retention against privacy and storage costs - logging everything at full fidelity forever is rarely practical.
Yes - if an actor with needed privileges can edit or erase local logs before they are exported, the audit story is weak; defenses include forwarding logs off-host immediately, limiting local administrative capability to affect exports, and auditing administrative actions themselves. MITRE ATT&CK documents real cases where adversaries cleared logs, illustrating that local-only logging is a dangerous single point of failure.
Related reading