What Is Oracle Manipulation?
Learn what oracle manipulation is, how flash-loan-funded price attacks work, and why aggregation, TWAPs, and delayed feeds reduce risk.
Introduction
oracle manipulation is the attack of making a smart contract believe a false external fact (most often a false price) and then profiting from the contract’s perfectly consistent response to that bad input. That is the uncomfortable part: the contract may execute exactly as written, yet still fail economically because the data it trusted was temporarily wrong.
This matters because blockchains do not natively know market prices, interest rates, weather events, sports results, or any other off-chain fact. They need oracles and data feeds to bridge that gap. The moment a protocol depends on an oracle, it inherits a new question: what would it take to make this data wrong at the exact moment the protocol reads it? Oracle manipulation is the answer to that question in adversarial form.
The core idea is simple. A smart contract is not harmed by “volatility” in the abstract. It is harmed when the value it reads is not a trustworthy representation of the thing it is supposed to measure. If a lending market uses a price feed to decide how much a borrower can withdraw, then a manipulated price is not just a bad statistic. It becomes a mechanism for creating bad loans, wrongful liquidations, or drained reserves.
The easiest way to understand oracle manipulation is to separate market reality from oracle reality. Market reality is the broad, underlying price that emerges across venues and over time. Oracle reality is whatever number the contract sees at the moment it executes. Good oracle design tries to keep those two realities close. Oracle manipulation works by forcing them apart long enough to exploit the gap.
Why are blockchain oracles vulnerable to manipulation?
Smart contracts are deterministic machines. They cannot look out at the world and decide whether a number “feels right.” They only see the bytes passed into them or stored on-chain. So when a lending protocol asks, in effect, “how much is this collateral worth?”, it must rely on some oracle mechanism that compresses a messy external market into a single on-chain value.
That compression is where the risk appears. Real markets are distributed across exchanges, order books, liquidity pools, market makers, and data vendors. Prices differ across venues, sometimes briefly and sometimes materially. Some trades are tiny and noisy; some are deep and informative. Some venues can be moved cheaply because they have thin liquidity. If an oracle naively reads from one fragile source, then the protocol has confused availability of a number with truth of a number.
This is why a spot price from a single decentralized exchange is often dangerous as a sole oracle. A DEX pool always has a price implied by its reserves, but that does not mean the price is hard to manipulate. In an automated market maker, the displayed price is just a consequence of current reserves. If someone pushes enough size through the pool, the reserves change, and so does the implied price. If a protocol reads that price in the middle of the disturbance, it may be reading an intentionally manufactured state rather than a fair market value.
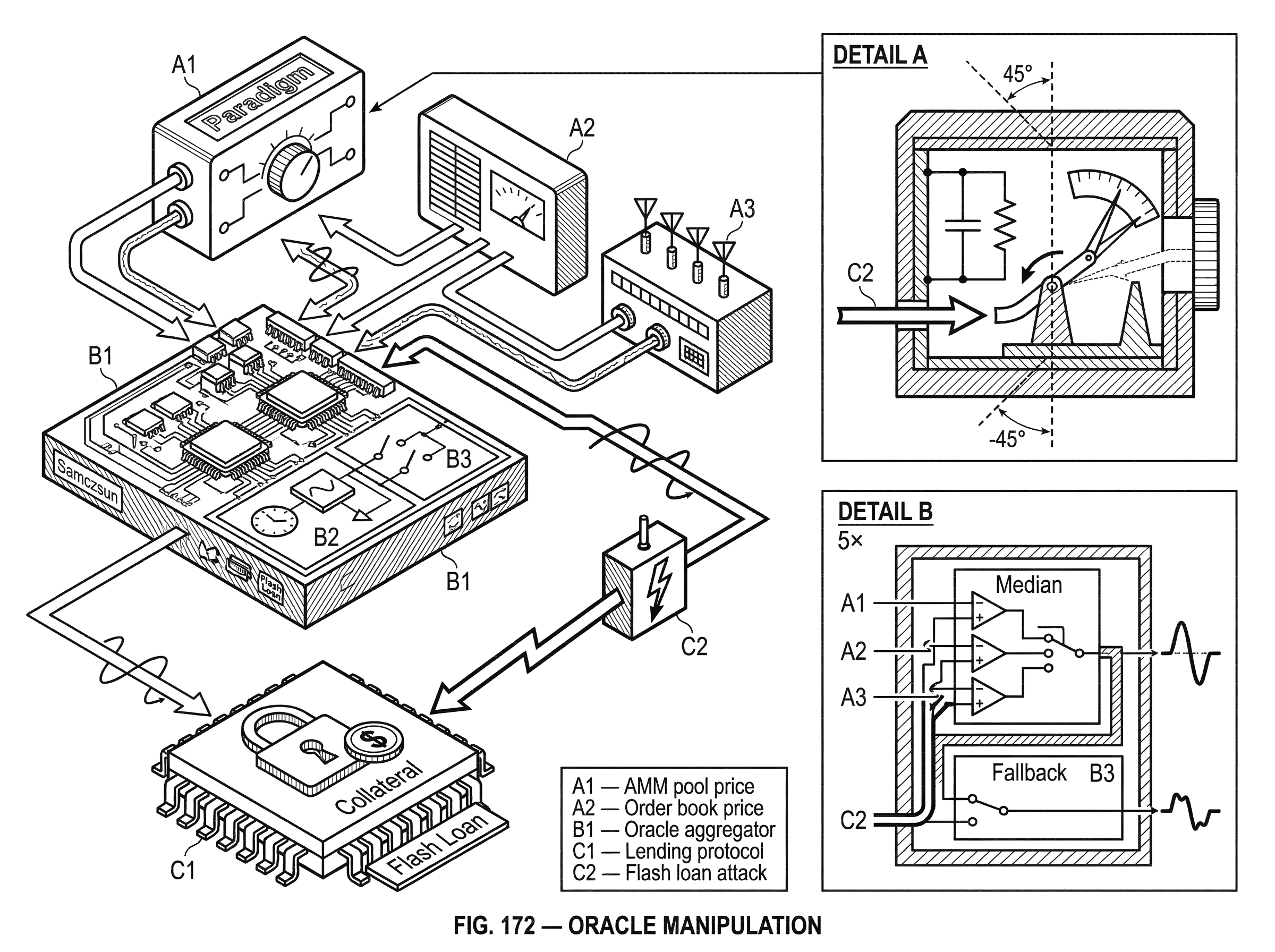
Paradigm’s practical warning captures the issue well: reading price information during the middle of a transaction can be unsafe, because an attacker can move the on-chain state, trigger the oracle read, and then continue executing before arbitrage restores the pool. Samczsun’s forensic writeups on DDEX and bZx showed exactly this pattern in the wild: the protocol did not need to be broken in the ordinary software sense. It only needed to trust a price that could be bent at the instant of use.
How do oracle manipulation attacks work?
| Step | Attacker action | Effect on contract | Amplifier | Attacker cost |
|---|---|---|---|---|
| Find target | Locate oracle-dependent call | Identifies exploitable entrypoint | none | low |
| Distort source | Move a thin venue price | Changes oracle reality | flash loan | low–moderate |
| Trigger read | Execute transaction reading oracle | Contract accepts false value | atomic tx | minimal |
| Extract value | Borrow/withdraw or redeem | Realize profit before correction | atomic tx | profit > cost |
Most oracle manipulation attacks have the same shape. First, the attacker identifies a protocol action whose payoff depends on an oracle value: borrowing, liquidating, minting, redeeming, settling, or rebalancing. Then the attacker identifies the weakest path by which that oracle value is formed. Finally, the attacker distorts that path just long enough to make the protocol execute on a false premise.
The critical invariant is this: the attacker does not need to change the true market price everywhere. They only need to change the value the victim contract accepts as authoritative. That is why oracle manipulation is often much cheaper than it first appears. Moving the entire market is expensive. Moving one thin pool, one fallback path, one reporter set, or one update window may be feasible.
A worked example makes this concrete. Imagine a lending protocol that accepts token B as collateral and values it using the spot price from a single AMM pool against token A. The protocol’s logic is straightforward: deposit B, read the oracle price, compute collateral value, and allow borrowing of A up to some fraction of that value.
An attacker begins by acquiring temporary capital. In modern DeFi this often comes from a flash loan, which is an uncollateralized loan that must be repaid within the same transaction or the entire transaction reverts. As Chainlink’s explainer emphasizes, flash loans do not create the vulnerability. They provide the scale needed to exploit one that already exists.
Now the attacker uses that borrowed capital to buy or sell aggressively in the AMM pool, shifting its reserves and therefore its spot price. In an ordinary market context, this would be a temporary distortion that arbitrageurs quickly trade away. But the attacker does not wait. In the same transaction, while the pool is still distorted, the attacker deposits token B into the lending protocol. The protocol queries the oracle, sees the manipulated spot price, concludes that B is worth far more than it really is, and allows the attacker to borrow too much A.
The attacker then withdraws the borrowed A, unwinds whatever trades are needed, repays the flash loan, and keeps the difference as profit. Everything happened atomically. No one had to leave capital exposed across blocks. No arbitrageur got the chance to correct the price before the protocol consumed it. The result is a loan that was undercollateralized in market reality but appeared healthy in oracle reality.
That same structure can be inverted. If a protocol is vulnerable to liquidations, an attacker may temporarily push a collateral price down rather than up, making healthy positions appear unsafe. If a vault share price or LP token valuation depends on a manipulable pool, an attacker may distort the valuation to mint too many shares cheap and redeem them later at fair value. Harvest Finance’s reported exploit followed that broad pattern: push a pool valuation away from fair value, enter at the bad valuation, then restore and exit.
Do flash loans cause oracle manipulation or just make attacks easier?
Flash loans deserve attention because they changed the economics of oracle attacks. Before flash loans, a manipulator needed large owned capital or substantial coordination. With flash loans, anyone who can assemble a profitable transaction can temporarily command very large balances.
But it is important to be exact here. A flash loan is not itself oracle manipulation. It is a financing tool. Chainlink’s security-oriented explanation makes this distinction clearly: flash loans expose existing protocol vulnerabilities rather than creating new ones from nothing. If a protocol reads a robust, manipulation-resistant oracle, a flash loan does not magically defeat it. If a protocol reads a fragile oracle, the flash loan makes exploitation much easier.
This distinction matters for defense. If engineers say “the problem is flash loans,” they are likely to implement the wrong fix. Blocking contracts, adding anti-bot rules, or limiting composability may inconvenience attackers, but the real question remains: is the oracle value economically hard to distort at the point of use? If the answer is no, the vulnerability persists.
Which common design mistakes enable oracle manipulation?
The most common design mistake is treating a local price as if it were a reference price. A local price is what one venue currently implies. A reference price is an attempt to estimate broader fair value. Single-pool spot prices are local. Market-wide aggregated feeds are closer to reference prices.
This difference sounds semantic, but it is mechanical. A local price can move because one pool’s reserves change, one order book thins out, or one reserve route is gamed. Samczsun’s DDEX example is revealing because the attack did not merely hit the obvious primary source. It manipulated the conditions under which the oracle fell back from one source to another, then attacked the fallback. That is a recurring lesson: once oracle logic becomes conditional, an attacker looks for the cheapest branch, not the most prominent one.
Another common mistake is ignoring timing. A price that would be harmless if sampled over an hour may be dangerous if read synchronously during a user transaction. Paradigm’s framing is useful here: a DEX spot price during a transaction is like reading a scale before it has settled. The issue is not that AMMs are always wrong. The issue is that they can be momentarily wrong in a way an attacker controls.
A third mistake is assuming decentralization by itself solves the problem. An on-chain oracle can be fully decentralized in the narrow sense that anyone may update it, yet still be easy to manipulate because all it does is mirror a manipulable on-chain venue. Conversely, an oracle can rely on off-chain reporters and still be much harder to manipulate if those reporters aggregate across many venues and publish values asynchronously. The question is not “on-chain or off-chain?” in the abstract. The question is what source diversity, aggregation rule, update timing, and trust assumptions determine the final number.
How does aggregating price sources reduce manipulation risk?
| Method | Manipulation cost | Latency | Best for | Main limitation |
|---|---|---|---|---|
| Median reporters | High if independent | Low | Reference pricing | Reporter collusion |
| Volume-weighted avg | Higher across venues | Low | Liquid-market price | Shared source bias |
| TWAP | Increases multi-block cost | High | On-chain AMM consumers | Slow to reflect moves |
| Off-chain async | Very high across sources | Variable | Flash-loan resilience | Staleness risk |
The first broad defense is distribution: do not rely on one source, one reporter, or one venue if the protocol cannot afford that source being wrong. The Chainlink whitepaper states the principle plainly: query multiple sources and aggregate their responses so that no single faulty or malicious source can control the output.
This works because manipulation becomes a coordination problem rather than a point attack. If an oracle reads from one exchange, the attacker asks, “what does it cost to move that exchange?” If the oracle aggregates over many venues, the attacker must ask, “what does it cost to move enough of the data that the aggregation output changes materially?” Those are very different questions.
Aggregation is not magic. It is a modeling choice. A median, mean, trimmed mean, volume-weighted average, or stake-weighted median each encodes a view about which deviations should matter and which should be treated as noise or outliers. Maker’s median oracle is a clean example of one family of design: maintain a governance-chosen set of authorized writers and take the median of reported prices once a quorum is met. The security intuition is direct: to move the output much, an attacker must corrupt enough writers to move the middle of the ordered set, not merely one reporter.
That said, aggregation introduces its own assumptions. Are the sources truly independent, or are multiple reporters scraping the same exchange? Are reporters freeloading by copying each other instead of independently sourcing data, as the Chainlink whitepaper warns? Is the quorum chosen to balance liveness and manipulation resistance? Oracle manipulation does not disappear under aggregation; it changes from “move one pool” to “bias enough inputs or enough influence over the aggregator.”
When should you use TWAPs to protect against oracle attacks?
The second broad defense is temporal smoothing: do not let one instant dominate the oracle output if the protocol can tolerate some lag. This is the idea behind a time-weighted average price, or TWAP. Instead of asking “what is the price right now at this exact manipulated moment?”, a TWAP asks, in effect, “what has the price been over a window of time?”
This raises attack cost because the attacker must sustain the distortion across multiple blocks or multiple samples rather than for one atomic moment. Uniswap’s oracle designs popularized this approach for on-chain consumers. Paradigm’s discussion captures the tradeoff well: for large, liquid pools over long windows, TWAPs are much more resistant to manipulation, but they react slowly and only work where there is already meaningful on-chain liquidity.
The limitation is important. Time averaging protects against brief distortions; it does not make an illiquid market liquid. If the underlying venue is thin, the averaged price can still be poor. And if market conditions change quickly, a long TWAP may be safer against manipulation but worse at tracking genuine price moves.
Uniswap’s own analysis after Ethereum’s move to proof of stake adds another nuance. TWAP security partly depended on attackers not being able to predict and control consecutive blocks. Under proof of stake, validators may have more foresight over block production, making some multi-block manipulation paths more plausible in theory. Yet the same analysis argues that for major pools, economically meaningful attacks remain prohibitively expensive today, especially when wide-range liquidity is present. The lesson is not “TWAPs are broken.” It is that oracle security is conditional on market structure and chain-level assumptions, not just contract code.
Why asynchronous off-chain aggregation changes the attack surface
A third defense changes not just the formula, but the whole timing model. If prices are aggregated off-chain from many venues and then posted on-chain asynchronously, the attacker can no longer rely on distorting one venue within the same transaction that the victim contract reads.
Chainlink’s explanation of flash-loan oracle attacks makes this point directly. Flash loans exist only inside one transaction. If the oracle value is produced off-chain from broad market data and published asynchronously, then a single in-transaction AMM distortion does not directly rewrite the oracle output. The attacker would need to influence the broader market sources or compromise enough of the reporting pipeline, which is a very different and usually much harder problem.
This is why decentralized oracle networks often emphasize broad market coverage, multiple independent aggregators, outlier filtering, and asynchronous publication. The security gain does not come from some mystical property of “off-chain.” It comes from changing what must be attacked. Instead of reading a manipulable local state synchronously, the protocol reads a value produced by a separate process whose inputs span more venues and more time.
Other oracle architectures pursue similar ends with different assumptions. Pyth, for example, aggregates data from multiple publishers and attaches a confidence interval, with prices generated on its own network and then pulled onto consumer chains. That design shifts some responsibility onto integrators, who must ensure prices are refreshed appropriately and not used stale. But the common theme remains: robust oracle design tries to make the consumed value reflect more than a single fragile on-chain snapshot.
What does delaying price adoption (OSM) protect against?
| Control | Security gain | Delay introduced | Operational cost | When to use |
|---|---|---|---|---|
| OSM delay | Time to react to anomalies | Hours to days configurable | Monitoring + governance | High-risk collateral |
| Sanity bounds | Blocks large spikes | Near-zero | Parameter tuning | Stablecoins, peg checks |
| Stale-price checks | Avoids very old prices | Depends on threshold | Consumer refresh burden | Fast-moving markets |
| Emergency pause | Stop damage in-flight | Immediate to users | Governance coordination | Severe incidents |
Sometimes the best defense is not to make the first number perfect, but to create time to react before it matters. Maker’s Oracle Security Module, or OSM, does this by delaying when a newly reported price becomes active inside the protocol.
The mechanism is conceptually simple. The oracle receives a new value, stores it as the next value, and only later promotes it to the current value used by the system. That delay gives governance, operators, and market participants a chance to notice an anomalous move and intervene before the protocol liquidates positions or accepts bad collateral valuations.
This is a real security tradeoff, not a free lunch. Delay reduces responsiveness. In fast markets, a stale but safe price can itself create risk. Maker’s documentation is unusually candid about operational and implementation details here, including the role of external poke() callers and edge cases in how the delay is enforced. That candor illustrates a broader truth: oracle security is partly cryptographic and economic, but also deeply operational.
What failure modes can persist after common oracle defenses?
The easiest misconception is to think oracle manipulation is solved once a protocol uses “a decentralized oracle.” In reality, each defense substitutes one set of assumptions for another.
If a protocol uses a reporter median, it must reason about reporter independence, key management, incentives, and governance over the reporter set. Maker’s median documentation makes these operational dependencies explicit: whitelisted writers, quorum rules, relayers, and governance all matter. If enough authorized reporters collude or fail, the median can still return bad or invalid results.
If a protocol uses asynchronous off-chain feeds, it must reason about source selection, update frequency, staleness thresholds, and what happens under congestion. If a protocol uses a TWAP, it must reason about window length, underlying liquidity, and multi-block manipulation assumptions. If it uses a pull oracle, it must reason about whether consumers update often enough before using the price.
In other words, oracle manipulation is not one bug class with one universal patch. It is the family of failures that occur when a protocol’s economic trust in data exceeds the real cost of corrupting that data.
What layered oracle design is considered “good enough” in practice?
A robust oracle design usually combines several levers rather than relying on one. It broadens source coverage so one venue does not dominate. It uses an aggregation rule that resists outliers. It smooths across time where latency permits. It rejects obviously implausible moves with sanity bounds or circuit breakers. It may delay adoption of new prices for especially sensitive functions. And it plans explicit emergency responses for the case where the oracle path still fails.
This layered approach appears across systems. Maker combines medianization with delayed adoption through the OSM and, at the extreme, governance-triggered emergency shutdown mechanisms. Chainlink emphasizes multi-source off-chain aggregation and asynchronous publication. Uniswap-style TWAP consumers rely on time-weighted observations instead of raw spot. Open Oracle-style systems separate off-chain signed reporting from on-chain aggregation views. Different stacks make different tradeoffs, but the pattern is the same: make manipulation expensive, detectable, slow, and operationally containable.
Conclusion
Oracle manipulation happens when a protocol trusts a data path that is cheaper to distort than the protocol assumes. The attacker’s job is not to rewrite reality. It is to rewrite the contract’s view of reality for just long enough to extract value.
That is why the central question in oracle design is not simply where a number comes from, but how hard it is to make that number wrong at the moment it matters. If you remember one thing, remember this: a smart contract is only as sound as the data it is willing to treat as truth.
What should you understand before using oracle‑backed DeFi services?
Before trading, depositing, or using oracle‑dependent features, confirm how the protocol forms the prices it consumes and whether that path can be distorted in a single transaction. On Cube Exchange, fund your account and execute trades or transfers while applying these checks so you can limit exposure to a manipulated oracle read.
- Check the protocol’s oracle type in its documentation: is it a single DEX spot, a TWAP (note the window length), or an off‑chain aggregator (Chainlink, Pyth)? Note fallback rules and publication cadence.
- Fund your Cube account via fiat on‑ramp or a supported crypto transfer so you can act quickly if a price anomaly appears.
- When trading thin pairs on Cube, use limit orders and set strict slippage tolerances; when supplying collateral, target a higher collateralization than the protocol minimum.
- Before depositing or borrowing against an oracle price, confirm the feed’s staleness threshold or any delay/OSM window and wait for the feed to reach a stable, post‑delay value.
Frequently Asked Questions
Flash loans are an amplifier: they let an attacker temporarily command large capital inside one transaction, which lowers the economic barriers to exploiting an existing oracle weakness - but they do not create a new vulnerability by themselves. If a protocol already reads a manipulation‑resistant oracle, a flash loan cannot magically defeat it; conversely, if the oracle is fragile, a flash loan makes exploitation much cheaper.
Because a single DEX spot price reflects one local state (pool reserves) rather than market-wide fair value, it can be moved cheaply by a large in‑transaction trade and therefore be unsafe as the sole price source for sensitive protocol actions.
Aggregating multiple sources (median, trimmed mean, volume‑weighted averages, etc.) raises the attacker’s cost by turning a point attack into a coordination problem, but aggregation only helps to the extent sources are independent and correctly weighted - if many reporters mirror the same venue or collude, the aggregate can still be biased.
Time‑weighted averaging (TWAP) raises attack cost because an attacker must sustain distortion across multiple blocks or samples, but it slows responsiveness and can still be unreliable if underlying venues are illiquid or if block‑producer advantages (e.g., PoS proposer look‑ahead) make multi‑block manipulation more plausible.
Asynchronous off‑chain aggregation (publishers aggregate many venues off‑chain and post results on‑chain later) prevents single‑transaction AMM distortions from directly rewriting the oracle output; an attacker would instead need to bias the broader market, compromise multiple reporters, or attack the reporting pipeline.
Maker’s Oracle Security Module delays when a reported price becomes active so governance and operators can react to anomalous updates, but that safety comes at the cost of responsiveness, requires reliable relayers/keepers to call poke(), and reintroduces operational and governance dependencies.
No single architectural choice universally solves oracle manipulation: each defense (aggregation, TWAPs, off‑chain aggregation, delays) substitutes one set of assumptions for another, so a protocol must pick designs and parameters that make corrupting the consumed value harder than the economic value of attacking the protocol.
Attackers search for the cheapest path to change the number the contract actually reads - this can be a thin DEX pool, a fallback branch, a small set of reporters, or an update window - so conditional oracle logic, fallback rules, or complex routing often create the weakest, most exploitable branch.
Related reading