What is Proof of Work?
Learn what Proof of Work is, how PoW mining secures blockchains, why it resists Sybil attacks, and the tradeoffs in energy, incentives, and security.
Introduction
Proof of Work is a way for an open network to decide who gets to add the next block by making that privilege costly to win and cheap to verify. That design matters because a permissionless system has a hard problem at its center: if anyone in the world can join, anyone can also create thousands or millions of fake identities. A consensus system that counted participants directly would be trivial to manipulate. Proof of Work solves that by counting expended resources instead of names.
At first glance, this can seem perverse. Why would a serious system deliberately require wasted computation? The key is that the computation is not there because the result is intrinsically useful. It is there because cost itself is the security primitive. If producing influence in the system requires real-world expenditure (hardware, electricity, and time) then taking over the system becomes expensive in a way that creating fake accounts is not.
This idea predates Bitcoin. In the early 1990s, Cynthia Dwork and Moni Naor proposed requiring senders to compute a moderately hard function before sending email, as a way to deter junk mail. Their framing is still the clearest starting point: a good work function should be feasible to compute, hard to amortize across many attempts, and easy to verify. Modern blockchain Proof of Work takes that same asymmetry and uses it for leader selection in consensus rather than spam control.
How does Proof of Work stop Sybil attacks by making participation costly?
In a permissionless network, the main danger is not merely dishonesty. It is cheap multiplicity. If influence can be gained by appearing as many participants, then the system cannot distinguish a thousand real participants from one attacker with a thousand keys. This is the classic Sybil problem.
Proof of Work changes the basis of influence. Instead of asking, “How many identities support this block?” the network asks, “Who can present evidence that they spent scarce computational effort under the current rules?” That shift is the whole mechanism. Identities remain cheap, but winning becomes expensive. A miner can create as many addresses as it likes; none of them help unless the miner also controls more hashing power.
The best way to think about PoW is as a lottery whose tickets must be manufactured in real time at real cost. Each mining attempt is a fresh ticket. Most tickets lose. Very rarely, one satisfies the network’s difficulty condition and becomes a valid proof. Because there is no known shortcut, the practical strategy is brute force: keep trying slightly different inputs until one works. The network can then check the winning ticket almost instantly.
That asymmetry is essential. If finding a proof were easy, anyone could flood the network with valid blocks. If checking a proof were expensive, every node would struggle to validate what miners produce. PoW works only because search is costly but verification is cheap.
How do miners generate valid Proof of Work hashes?
In many PoW systems, the puzzle is built from a cryptographic hash function. A hash function takes input data and produces a fixed-size output called a digest. Small input changes produce unpredictable output changes. That unpredictability is what makes repeated guessing meaningful.
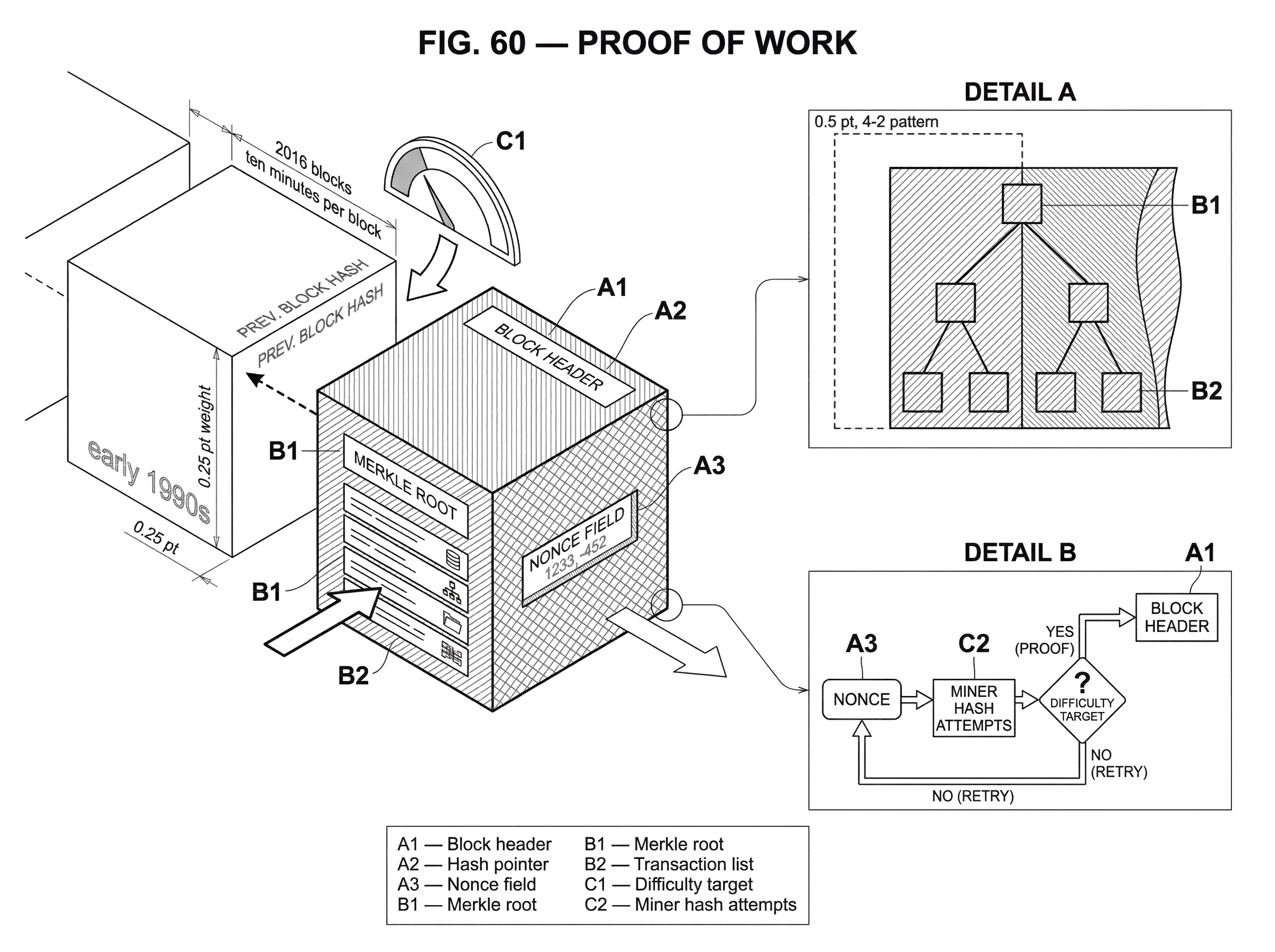
A miner starts with a candidate block. The block contains transactions and some metadata. The miner then varies a field such as a nonce (a number used to generate new hash attempts) and hashes the block header again and again. Each different nonce gives a different digest. The miner is looking for a digest that falls below a network target.
That target is what defines difficulty. If the target is high, many digests qualify and blocks are easy to find. If the target is low, only a tiny fraction qualify and miners must perform many more hash attempts on average. The proof, then, is not a mathematical theorem in the usual sense. It is evidence that the miner found a rare input by spending enough trial-and-error effort.
A simple narrative makes this concrete. Imagine a network where a valid block hash must begin with a long run of zero bits. A miner assembles a block and hashes it. The result fails. The miner changes the nonce and hashes again. That fails too. It keeps doing this millions or billions of times. Eventually one attempt lands in the tiny region of hash outputs that satisfy the rule. The miner broadcasts the block. Other nodes do not need to repeat the search; they hash the header once, see that the digest meets the target, and accept that the miner really did the work.
That is the mechanical heart of PoW. The network is not rewarding cleverness. It is rewarding the first successful search through a large, random-looking space.
How does Proof of Work secure blockchain consensus instead of just pricing access?
Dwork and Naor used work to price access to a service: sending mail. Blockchains use work to order history. The jump from one to the other is less mysterious than it first appears.
A blockchain needs some way to decide which candidate block becomes the next accepted block when many parties may propose competing versions. In a permissionless setting, there is no trusted coordinator to assign turns. Proof of Work creates a decentralized race. Anyone may try, but the chance of winning is proportional to the amount of computational effort they can sustain.
Once blocks are chained together, this creates an important cumulative property. Each block contains proof that work was spent, and later blocks build on earlier ones. Rewriting history now means more than editing a database entry. It means recreating the work behind the altered block and catching up with the work added after it. The deeper a block sits under later blocks, the more accumulated work defends it.
This is why PoW systems usually follow the chain with the most total work, often simplified in explanations as the “longest chain.” Length alone is not the point. The point is that the preferred history is the one that was most expensive to produce under the protocol’s rules. Consensus emerges because honest nodes converge on the heaviest valid chain they know about.
That also explains why PoW finality is probabilistic rather than absolute. Two miners can sometimes find valid blocks at nearly the same time, creating a temporary fork. Some nodes see one first; others see the other. Eventually one branch gets extended by more work and the network converges on it. The orphaned branch’s block was valid, but it ended up on the losing side of the race. A transaction becomes safer as more work accumulates on top of it, not because some single event made it irrevocable.
What is difficulty adjustment and how does it keep block times stable?
A PoW network needs blocks to arrive at a roughly predictable rate. If blocks arrived too quickly, forks would become frequent and the network would struggle to synchronize. If they arrived too slowly, transaction confirmation would become sluggish and security assumptions tied to block cadence would drift.
But total mining power is not constant. New miners join. Old miners leave. Hardware improves. Electricity prices change. A fixed puzzle would therefore produce unstable block times. The network needs a feedback mechanism.
That mechanism is difficulty adjustment. The protocol observes how quickly recent blocks were found and updates the target accordingly. If blocks arrived faster than intended, the protocol lowers the target so valid hashes become rarer. If blocks arrived too slowly, it raises the target so valid hashes become easier to find. Bitcoin famously adjusts every 2016 blocks to aim for an average of about ten minutes per block.
The important idea is that the network does not target a fixed amount of total energy usage. It targets a fixed rate of block production. Competition among miners then drives total resource expenditure toward the level justified by expected rewards. In other words, the protocol controls how often someone wins, but the market largely determines how much aggregate spending happens to chase each win.
Why do miners follow incentives and how do rewards shape mining behavior?
Proof of Work is not only a cryptographic mechanism. It is also an incentive system. Miners spend resources because the protocol offers rewards, typically a combination of newly issued coins and transaction fees. The work secures the chain because miners are willing to buy a chance at those rewards.
This has a subtle consequence. The system’s security is not simply “there is a hard puzzle.” It is “honest extension of the chain is the most attractive way for a large enough share of resources to pursue rewards.” If that incentive picture changes, security changes with it.
A useful way to see this is to imagine two miners deciding what to do after finding a block. The intended behavior is to publish it immediately so others can build on it. But game theory can complicate that. Eyal and Sirer showed that in Bitcoin-like systems, a colluding minority can sometimes increase its revenue by withholding blocks and strategically releasing them later, a strategy called selfish mining. The attack works by causing honest miners to waste effort on branches that will lose, thereby increasing the attacker’s share of main-chain blocks.
This result matters because it breaks a common oversimplification: PoW security is not guaranteed merely because no one has over 50% of the hashpower. Majority control is still a critical threshold for many attacks, especially straightforward chain rewrites, but incentive failures can appear well below 50% depending on network conditions and propagation advantages. So the real assumptions behind PoW are richer than “honest majority.” They include network connectivity, information propagation, and miner coordination dynamics.
Mining pools grow out of this economic reality. Block discovery is a lottery, so solo mining income is highly variable. Pools let miners combine effort and share rewards more smoothly. That reduces variance, which is attractive, but it also concentrates decision-making. A network can be open in principle while still becoming operationally concentrated in a small number of pools.
Why must PoW puzzles prevent preprocessing and amortization?
| Algorithm | Primary resource | Amortization risk | ASIC resistance | Typical example |
|---|---|---|---|---|
| SHA-256 | Computation cycles | Low | Low (ASICs common) | Bitcoin |
| scrypt | Memory bandwidth | Medium | Medium (memory-hard) | Litecoin |
| Ethash | Memory + I/O (DAG) | Low–medium | Intended high; ASICs later | Ethereum (historical) |
A PoW puzzle is only useful if each attempt really costs something. This sounds obvious, but it has a precise meaning. If an attacker can preprocess information once and then solve many future puzzles cheaply, the pricing mechanism collapses. Dwork and Naor emphasized exactly this point when rejecting candidate functions that allowed amortization after preprocessing.
The same principle applies in blockchain PoW. The protocol wants each block race to require fresh expenditure tied to the current block context. A miner should not be able to do one big computation today and coast through thousands of future rounds almost for free. Hash-based PoW is attractive partly because changing the block header changes the search space in a way that preserves the need for repeated fresh trials.
This is also where different PoW algorithms start to matter. Bitcoin uses SHA-256-based mining. Litecoin adopted scrypt, drawing on a design intended to be memory-hard. Ethereum historically used Ethash, which relied on repeated access to a large dataset called a DAG and was designed to make mining more memory-intensive. The shared goal in these variants is not to change the basic logic of PoW, but to change the resource profile of the work; for example, to reduce the relative advantage of specialized hardware.
Here the analogy to “making the puzzle fair” is helpful, but only up to a point. Memory-hard designs can raise the cost of custom hardware or change what kinds of hardware are competitive. They do not abolish competition or guarantee lasting ASIC resistance. Ethereum’s Ethash, for example, was designed to be memory-hard and was thought to discourage ASIC dominance, yet Ethash ASICs were eventually built. The deeper lesson is that PoW can choose which costs matter most, but it cannot eliminate the economic pressure to optimize those costs.
Why does Proof of Work consume large amounts of energy?
| Aspect | Proof of Work | Proof of Stake |
|---|---|---|
| Energy consumption | High electricity use | Minimal electricity use |
| Sybil defense | Costly resource-based influence | Stake-weighted influence |
| Finality model | Probabilistic finality | Often faster or economic finality |
| Centralization pressure | Hardware and power concentration | Wealth/stake concentration |
One of the most common misunderstandings about Proof of Work is to treat its energy use as an unfortunate implementation bug. In reality, energy expenditure is closely tied to how PoW creates scarcity in an otherwise abundant digital environment.
A digital network can verify signatures, copy messages, and create new identities at near-zero marginal cost. PoW inserts a process that is deliberately not near-zero cost. That is how it makes influence expensive. If the work could be produced without meaningful resource expenditure, then the anti-Sybil property would weaken or disappear.
This does not mean every joule spent by every miner is equally necessary in some engineering sense. It means the class of mechanism depends on costly competition. In equilibrium, miners collectively spend resources because block rewards justify it. As a result, large PoW systems consume substantial electricity and encourage investment in specialized hardware. NIST’s overview highlights this clearly: PoW security comes with significant resource consumption, hardware competition, and a tendency for mining to cluster where electricity is cheap.
That tradeoff became especially vivid when Ethereum moved from Proof of Work to Proof of Stake in The Merge. Ethereum’s official documentation describes the transition as a replacement of mining-based security with validator-based security and reports a dramatic reduction in energy consumption. Whether one prefers PoW or PoS depends on what kinds of assumptions and failure modes one considers more acceptable, but the comparison makes one thing unmistakable: PoW’s energy cost is central to what it is.
What are the main risks and attacks against Proof of Work?
| Failure mode | Primary effect | Attacker requirement | Common mitigations |
|---|---|---|---|
| 51% attack | Chain reorgs, double-spend | Majority effective hashpower | Raise confirmations, raise attack cost |
| Selfish mining | Revenue diversion, more forks | Moderate pool + propagation edge | Relay rules, protocol tie-breaks |
| Rented hashpower attack | Temporary majority takeover | Cheap hired hashpower | Exchange monitoring, longer waits |
| Latency/propagation | Uneven block advantage | Network connectivity edge | Improved relays, propagate all blocks |
The cleanest failure mode is the 51% attack. If an attacker controls a majority of the effective hashpower, it can usually outpace the rest of the network in extending its preferred chain. That does not let it arbitrarily rewrite every rule (it cannot, for example, create coins in violation of consensus rules if nodes validate correctly) but it can reorganize recent history, censor transactions, and double-spend by replacing blocks.
Smaller PoW chains are especially vulnerable because hashpower can sometimes be rented or redirected. Ethereum Classic suffered high-profile attacks of this kind in 2020, where rented majority hashpower was used to rewrite the chain and double-spend against exchanges. The lesson is simple but important: PoW security is not an abstract theorem detached from market structure. It depends on how expensive it is, in practice, to marshal enough mining power against a given chain.
Even without majority attacks, centralization pressures matter. Specialized hardware, access to cheap electricity, economies of scale, and pool coordination can all narrow the set of actors who matter most. Empirical studies of Bitcoin and Ethereum’s PoW-era decentralization found a mixed picture rather than a simple victory for either system. PoW can enable open participation, but openness at the protocol layer does not automatically produce evenly distributed power in operation.
There is also the issue of latency and forks. If blocks propagate slowly relative to how quickly they are found, miners with better network connectivity gain an advantage. They hear about new blocks earlier, waste less work on stale branches, and may enjoy strategic options not available to others. This is one reason why networking infrastructure, relay systems, and block propagation policies are not side details in PoW systems. They are part of the security envelope.
What property does Proof of Work actually purchase for a blockchain?
It helps to strip away the surface details and ask what service PoW fundamentally provides. It does not prove useful computation. It does not prove honesty. It does not guarantee egalitarian participation.
What it buys is a way to make block production costly, publicly checkable, and difficult to fake in a network with no admission control. That creates a measurable notion of chain weight: history backed by more cumulative work is harder to replace. From there, the protocol gets a rule for converging on one ledger and a cost model for attacking it.
This is why the old anti-spam framing still matters. Dwork and Naor saw work as a pricing mechanism: cheap for occasional legitimate use, expensive at abusive scale, and easy for recipients to verify. Blockchain PoW applies the same principle to consensus. The system does not ask participants to be trustworthy. It asks them to present evidence of burned resources, then treats that evidence as the basis for influence.
That move is both elegant and costly. Elegant, because it gives a permissionless network a common measure that does not depend on identity or trust. Costly, because the measure is grounded in real-world expenditure, with all the environmental, industrial, and centralization consequences that follow.
Conclusion
Proof of Work is a consensus mechanism that converts real-world cost into digital influence. Miners repeatedly search for a rare valid hash, the network verifies the result cheaply, and the chain with the most cumulative work becomes the accepted history. That is why PoW can resist Sybil attacks in open networks, and it is also why it consumes substantial resources and creates strong economic pressures toward specialization and concentration.
The idea to remember tomorrow is simple: PoW works because it makes rewriting history expensive, not because it makes miners trustworthy.
What should I understand about Proof of Work before trading or depositing?
Proof of Work ties security to cumulative mining work, so you should assess chain strength and reorg risk before trading, depositing, or withdrawing PoW assets. On Cube Exchange, fund your account, check the chain’s recent work and hashrate trends, then use the normal trade or transfer flow with an appropriate confirmation depth.
- Deposit funds into your Cube account via the fiat on-ramp or a direct token transfer so you can trade or withdraw on-chain.
- Open a public chain explorer and check the chain’s total work/hashrate trend, recent difficulty adjustments, and any recent reorgs or reported 51% incidents.
- Choose a confirmation depth to accept as final; wait at least 6 confirmations for Bitcoin-style chains and use substantially more for smaller PoW networks or chains with declining hashrate.
- Execute your trade or submit the on-chain withdrawal on Cube, then monitor block confirmations until you reach your chosen depth and only then treat the transfer as final.
Frequently Asked Questions
PoW makes influence costly because cost itself is the security primitive: by requiring real-world expenditure (hardware, electricity, time) to win block races, the protocol replaces counting identities with counting expended resources, which is hard to fake and easy to verify.
Instead of trusting identities, PoW asks who can present verifiable evidence of having spent scarce computation on the current puzzle; that ties influence to controllable hashpower rather than cheap, duplicable identities and thus mitigates Sybil attacks.
Difficulty adjustment observes how fast recent blocks were found and updates the target so blocks arrive at a roughly predictable rate (e.g., Bitcoin retargets every 2016 blocks for ~10 minute blocks); this controls block cadence while competition determines total spending to chase rewards.
Selfish mining is a strategy where a colluding miner withholds found blocks to cause honest miners to waste work and thereby increase the colluders’ revenue; analysis shows it can be profitable below a 50% hashpower threshold depending on network propagation (γ), so incentive failures can arise well before majority control.
If a pricing/work function admits cheap preprocessing or amortization, attackers could solve many future puzzles at much lower marginal cost and the anti‑Sybil pricing collapses; both Dwork–Naor and the article flag resisting amortization as a precise design requirement for PoW puzzles.
PoW provides probabilistic finality: concurrent valid blocks and temporary forks can occur, so a transaction’s safety increases as more cumulative work (later blocks) builds on it rather than by any single irreversible event.
Mining pools exist because block rewards are a lottery and pooling smooths income variance, but pools concentrate decision-making and can centralize operational control, which changes the system’s threat model despite protocol‑level openness.
A 51% attack occurs when an attacker controls a majority of effective hashpower and can thus outpace honest miners to rewrite recent history, censor transactions, or double‑spend; real-world incidents (e.g., rented-hashpower attacks on smaller chains) illustrate how practical economics can enable such attacks on weaker networks.
Memory‑hard and CPU‑focused PoW designs (scrypt, Ethash, RandomX) aim to shift which physical resource matters, but history shows ASICs can still be developed for ostensibly resistant algorithms, so lasting ASIC resistance is not guaranteed - PoW can change the resource profile but not eliminate competitive optimization.
Related reading