What is a Light Client?
Learn what a light client is, how it verifies blockchain data with headers and proofs, why it exists, and where its trust assumptions begin.
Introduction
Light client is the name for a blockchain client that tries to preserve local verification while avoiding the cost of running a full node. That is a more delicate idea than it first appears. If you do not store the chain and do not re-execute every block, what exactly are you still verifying, and what are you forced to trust instead?
That question matters because full verification is expensive. A full node stores large amounts of data, stays online to sync and serve peers, and often replays or checks the full history of state transitions. That is a good trade for infrastructure operators, but not for every phone, browser, embedded device, wallet, rollup component, or application that only needs selective access to the chain. A light client exists to change that trade: use far fewer resources, but keep as much independent verification as the underlying chain design allows.
The important distinction is this: a light client is not just a remote procedure call wrapper around someone else’s node. It still fetches data from providers, but it tries to check that data against cryptographic commitments and consensus evidence that it can validate locally. The exact mechanism differs across chains, because what must be verified depends on how the chain reaches consensus. That is why the same phrase, light client, covers Bitcoin-style SPV, Tendermint verification, Ethereum sync-committee verification, and other designs that look similar at a high level but differ mechanically.
What problem does a light client solve?
A blockchain client has to answer two separate questions. First: what chain history should I accept as canonical? Second: *given that accepted history, is this transaction, account value, validator set, or bridge message really in it? * A full node answers both by keeping enough local data to reconstruct the whole story. A light client tries to answer both with much less data.
The compression point is that blockchains are built out of commitments. A block header commits to other data without containing all of it. A Merkle root commits to a set of transactions or state items without listing them all. A validator signature commits to a vote without replaying every reason behind the vote. Light clients exploit that structure. Instead of downloading everything, they keep the commitments that matter and ask for short proofs tying specific claims back to those commitments.
This creates a new shape of client state. A light client usually stores some small trusted base: recent headers, a validator set or committee, a finalized checkpoint, and enough metadata to know whether a newly received header should be accepted. When it wants a fact like “this transaction was included” or “this key has this value,” it asks a provider for the fact plus a proof. The provider can be untrusted. The proof is what lets the client decide.
That idea sounds almost magical until you notice its boundary: a proof can only prove something relative to a commitment the light client already trusts. So the real challenge is not only proving membership in a Merkle tree. It is securely maintaining the small set of trusted commitments as the chain evolves.
What state does a light client store vs. outsource?
A full node tries to be self-sufficient. It stores blocks, often stores or reconstructs state, validates transactions, and participates in peer-to-peer sync from raw network messages. A light client throws away most of that burden. It usually keeps headers or some compressed representation of consensus progress, plus minimal verification state.
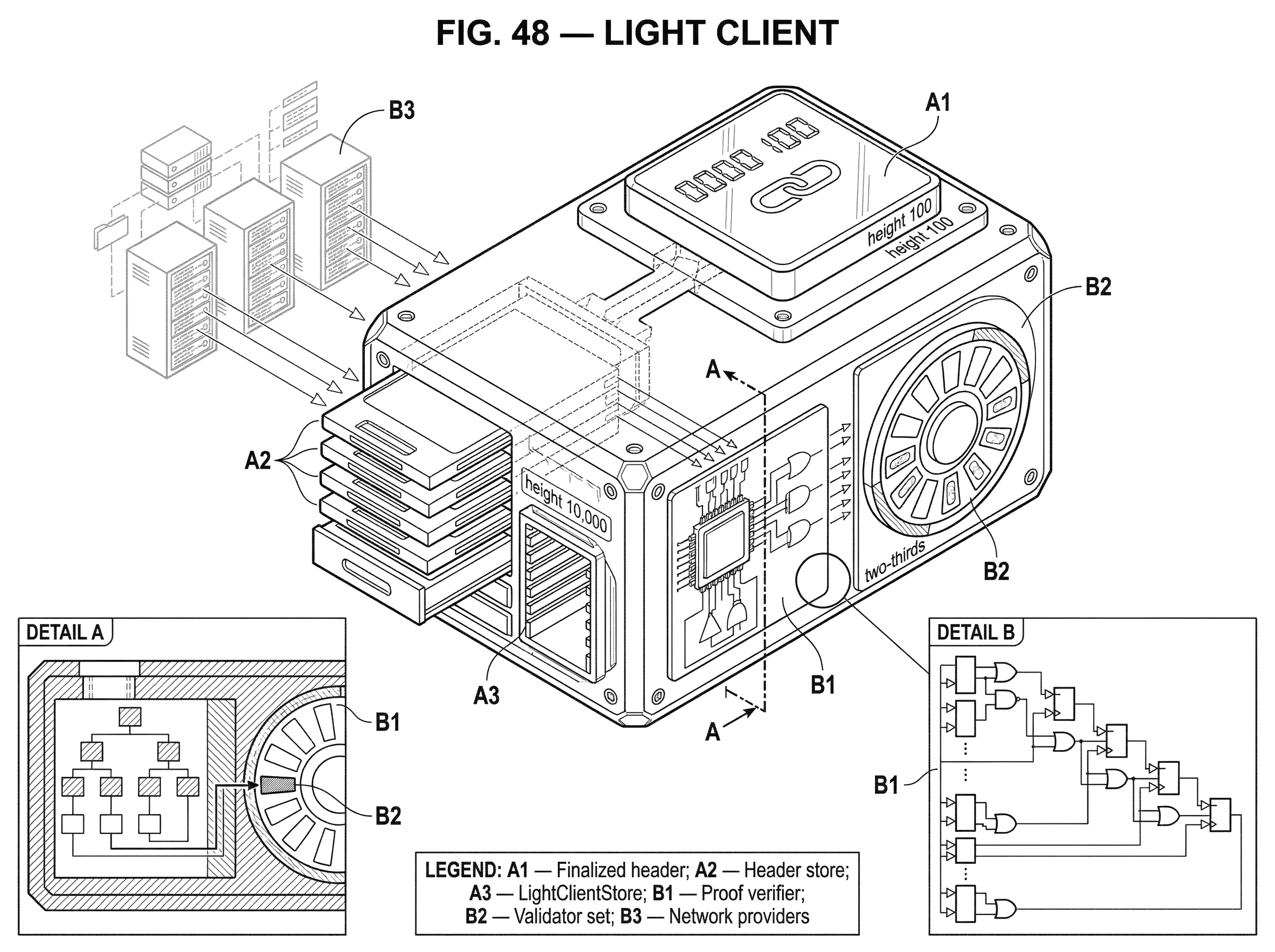
What remains local is the critical part. The client still needs a trust anchor: perhaps a known checkpoint, perhaps a trusted header, perhaps genesis plus a protocol-specific bootstrapping procedure. It also needs enough information to verify future consensus evidence. In Tendermint-based systems, that means tracking verified consensus states and validator-set hashes. In Ethereum’s beacon-chain light client design, that means maintaining a LightClientStore with a finalized header, current and next sync committees, the best valid update seen so far, and optimistic tracking fields. In each case the point is the same: the client’s local state is not the whole chain, but it is enough to test whether new claims are consistent with the chain it already trusts.
What gets outsourced is bulk data and availability. A light client typically does not keep the full blockchain and often does not keep all state locally. Instead it asks full nodes, RPC servers, relayers, or specialized data networks for the specific headers, blocks, account proofs, transaction proofs, or bridge proofs it needs. The savings are substantial because storage, bandwidth, and sync time drop sharply. But now the design has to make sure this outsourcing does not quietly become blind trust.
That is why a light client is best understood as a client that outsources data, not judgment. If it merely asks a server “what is my balance?” and displays the answer, it is acting like a thin hosted client. If it asks “show me the balance and a proof against a commitment I already accept,” and then checks the proof itself, it is acting like a true light client.
How do light clients use commitments and proofs to verify data?
The most universal mechanism in light clients is a two-step pattern.
First, the client accepts a compact commitment to chain state or history. This might be a block header, a finalized checkpoint, a commitment root, or a header signed by a validator committee.
Second, for any specific claim, the client requests a proof connecting that claim to the commitment. Merkle proofs are the classic example. If a block header contains a Merkle root of transactions, a provider can show the transaction and a Merkle branch proving that this transaction hashes up to the root in the trusted header. The client does not need every other transaction in the block. It only needs the path that links the claimed item to the root.
This is why Merkle proofs appear everywhere around light clients. They are the bridge between small commitments and large datasets. In IBC-oriented Cosmos systems, ICS23 exists specifically to provide a standard binary representation of Merkle proofs for existence and non-existence proofs across languages and implementations. That standardization matters because a light client is only useful if different components can agree on what proof object is being checked and what tree semantics it assumes.
But Merkle proofs solve only the second question: whether a claim matches a trusted root. They do not answer the first question: whether the root itself belongs to the right chain. For that, a light client needs to verify consensus.
How does blockchain consensus affect light-client design?
| Consensus type | Verification anchor | Main verification step | Primary challenge | Best for |
|---|---|---|---|---|
| Proof-of-Work (SPV) | Header chain and PoW | Check header PoW and longest chain | Eclipse and header-only blind spots | Simple wallets, SPV clients |
| PoS / BFT (Tendermint) | Validator-set quorum signatures | Verify validator-set continuity and commits | Validator churn and long-range attacks | On-chain clients, relayers, IBC |
| Sync-committee (Ethereum) | Periodic sync-committee attestations | Verify aggregate BLS signature and committee inclusion | Timeouts, optimistic progression tradeoffs | Mobile/browser light clients |
If all blockchains had the same notion of finality, a single generic light-client recipe would work everywhere. They do not. The hard part changes with consensus.
In a proof-of-work setting, the classic idea is header-only verification. A client can download block headers, check proof-of-work on each, and follow the best chain under the protocol’s chain-selection rule. This is the family of ideas commonly associated with simplified payment verification. It reduces resource use dramatically, but it also introduces tradeoffs. A client that only sees headers has less information than a full node, can be more vulnerable to network isolation and privacy leakage, and still may need many headers over time.
In proof-of-stake or Byzantine fault tolerant systems, headers alone are often not enough. The reason is structural. Acceptance of a block depends not just on the block itself but on who was allowed to vote and whether enough of them did. If validator sets evolve over time, then a light client must somehow verify that evolution too. Otherwise an attacker might present a plausible-looking header from an obsolete or fabricated validator set.
This is why research on light clients emphasizes that PoS and BFT designs have a harder synchronization problem than simple header verification suggests. The client must maintain confidence not only in a chain of hashes but in a chain of authority. That requirement leads to different mechanisms on different chains.
How does a Tendermint (Cosmos/IBC) light client safely sync and update?
Tendermint is a good example because its structure makes the problem visible. A committed block is backed by signatures from more than two-thirds of the current validator-set weight. The next block carries evidence of the previous block’s commit, and headers contain cryptographic commitments to state. So a light client can, in principle, verify that a header was properly committed and then use the committed root to verify application-level state proofs.
The subtlety is validator-set change. Suppose a light client trusts a header at height 100. Someone now offers a header at height 10,000. If the validator set had never changed, the client could just verify a commit from the same validators. But validator sets usually do change, and the client at height 100 does not automatically know the set at height 10,000. The Tendermint light-client approach handles this with intermediate verification rather than blind leaps. In IBC’s ICS-007 Tendermint client, the client state tracks parameters like trustLevel, trustingPeriod, unbondingPeriod, latestHeight, and maxClockDrift, while consensus states store things like timestamp, nextValidatorsHash, and commitment root. Verification uses the Tendermint light-client bisection algorithm to bridge from trusted heights to newer heights while checking validator-set continuity and timing constraints.
Mechanically, the client is not saying “I know this new header is good because a server said so.” It is saying “I know an older header and the next validator-set hash that came with it; I can verify enough overlap and signatures in later headers, recursively if needed, until the new height is justified.” The trusting period matters because if a client stays offline too long, the assumptions behind that old trust anchor weaken. The unbonding period matters because stake and validator exits define how long old signatures can still anchor safety against long-range attacks.
This same verified header then becomes the base for application proofs. If an IBC module wants to prove that some packet commitment exists or does not exist, it verifies a Merkle membership or non-membership proof against a commitment root in a previously verified consensus state. The light client is therefore doing two linked jobs: first proving “this header is from the right chain,” then proving “this state claim matches that header.”
How does Ethereum's beacon-chain sync‑committee light client work?
Ethereum’s current consensus-layer light client takes a different route because Ethereum’s consensus looks different. Rather than expecting a light client to track every validator signature, the protocol introduces sync committees as a compact attestation mechanism. A sync committee is a subset of validators assigned for a period, and their aggregated signatures on headers give light clients an efficient way to verify chain progress.
The essential move is to replace “follow the full validator set all the time” with “follow a smaller committee whose authority is itself committed in beacon-chain state.” A light client bootstraps from a trusted block root and a LightClientBootstrap. It verifies, using a Merkle branch against the header’s state_root, that the claimed current sync committee really is the one committed in the trusted state. After that, updates can be checked by verifying the sync-committee aggregate signature over the attested header, using a domain derived from fork data and the genesis validators root.
The client’s persistent state is not a copy of the chain. It is a small store containing the finalized header, current and next sync committees, the best valid update, and optimistic tracking information. Incoming LightClientUpdate objects contain an attested header, potentially a next sync committee and proof, a finalized header and proof, a sync aggregate, and a signature slot. The client verifies Merkle branches where needed, checks the aggregate signature, and applies update-selection rules. The spec uses a supermajority threshold of at least two-thirds participation for decisive updates and defines how to rank competing updates.
There is an important design tradeoff here. The protocol includes a forced-progression mechanism: after an UPDATE_TIMEOUT, an implementation may treat an attested header as finalized to preserve liveness. That is useful when a light client would otherwise stall, but it is explicitly a place where liveness can push against safety if used carelessly. Another caveat in the published spec is that header validation is left as a no-op placeholder, which means real implementations must supply stronger validation logic than the text alone provides.
Still, the overall pattern is clear. The Ethereum light client does not validate everything a full node validates. It validates enough consensus evidence to believe specific headers, and then it can check data against commitments in those headers. This is why Ethereum documentation describes light nodes as fetching necessary data from providers but verifying it locally, rather than keeping full local copies.
What trust assumptions and finality models do light clients rely on?
A smart misunderstanding is to think that a light client either “trusts nothing” or “trusts servers.” Neither is right. It trusts a model.
At minimum, that model includes a bootstrapping assumption. A light client begins from somewhere: a genesis block, a trusted checkpoint, a trusted block root, or some out-of-band source of initial truth. Very few practical designs escape this entirely. Even systems with strong cryptographic compression usually still require some setup or trust anchor.
Then come consensus assumptions. In Tendermint-style systems, safety and liveness hold while less than one-third of validator weight is faulty or malicious. In GRANDPA-style finality gadgets, provable finality depends on partial synchrony and bounded Byzantine participation. In Ethereum’s sync-committee design, the client trusts that committee selection and consensus incentives keep fraudulent committee attestations sufficiently unlikely. In PoW, a header-following light client trusts the economic and network assumptions behind the longest-chain rule.
Then come networking assumptions. A client that connects to a single malicious server can still be censored or misled about what data is available, even if false proofs are hard to forge. Research on light clients repeatedly notes that the lightest designs often shift burden elsewhere: to prover infrastructure, to validator coordination, or to the network path by which proofs are delivered. A client may verify correctness of what it receives while still depending on others for availability and timely updates.
This is why finality matters so much. Some systems offer probabilistic finality, where confidence grows with more work or more time. Others offer provable finality, where a finality proof can convince even an offline client that a block is final. Finality gadgets such as GRANDPA are attractive for light clients because they let a client accept a compact proof of finality without continuously observing the full network. But that convenience rests on the protocol’s synchrony and validator-threshold assumptions.
Where are light clients used in practice (wallets, bridges, rollups)?
| Use case | What must be verified | Typical trust anchor | Common proof types | Why choose a light client |
|---|---|---|---|---|
| End-user wallets | Transaction inclusion and account balance | Known checkpoint or recent header | Merkle inclusion proofs, headers | Low resource usage on phones/browsers |
| Rollups and bridges | Source-chain state or deposit proofs | On-chain verified header or checkpoint | Merkle proofs against verified root | Reduce oracle/trusted-guardian reliance |
| Mobile / embedded apps | Specific state or receipts | Trusted header or bootstrap | Compact receipts and Merkle branches | Operate under severe resource limits |
| On-chain verifiers | Cross-chain commitments | Stored consensus state on-chain | Merkle membership/non-membership proofs | Automated, trust-minimized interoperability |
The most obvious use is wallets and end-user applications. A phone wallet wants to know whether a transaction happened, what an account state is, or whether a recent header is valid, but it does not want to store and process the whole chain. A browser-based app may want similar assurances. Ethereum documentation explicitly points to constrained environments such as phones and metered virtual machines as targets for light-client-friendly design.
Another use is embedded verification inside larger systems. A rollup, bridge, or application contract may embed a light client of another chain so it can verify deposits, message commitments, or state roots without trusting a centralized oracle. This is one of the cleanest ways to reduce trust in interoperability systems: instead of asking “did a committee say the event happened?”, ask “can I verify a proof from the source chain’s own consensus?” The distinction is not academic. Bridge failures often reveal exactly what goes wrong when verification is delegated to a small guardian or validator set without sufficiently robust checking.
Cosmos IBC is the canonical infrastructure example. It relies on on-chain light clients that verify another chain’s headers and then check Merkle proofs against verified commitment roots. That is the reason IBC can be more trust-minimized than a multisig bridge: the receiving chain is not merely taking someone’s word for the source chain state; it is running a light-client verification algorithm.
Other ecosystems express the same need differently. Solana’s “receipt” proposal frames a light client as a participant that does not run a validator but still wants a minimal proof that a transaction was included and that the relevant validator votes reached the desired confirmation depth. The details differ, but the principle is the same: compact proof of inclusion plus compact proof of consensus acceptance.
When do light clients fail? Common failure modes and risks
| Failure mode | Symptom | Why it matters | Short mitigation |
|---|---|---|---|
| Bad bootstrap checkpoint | Client trusts wrong chain | All subsequent proofs validate wrong history | Obtain bootstrap via multiple trusted sources |
| Offline drift / expired trust | Cannot safely sync forward | Trusted anchor outlives trusting period | Refresh checkpoint within trusting window |
| Data availability loss | Proofs unavailable on request | Cannot verify even true claims | Use multiple providers or decentralized data nets |
| Proof-format mismatch | Received proof fails verification | Different tree semantics; false negatives | Use compatible proof spec or adapter (ICS23) |
| Implementation bugs | Valid proofs accepted wrongly | Logic errors and missing checks lead to compromise | Audit validation code and test vectors |
The easiest failure mode is to underestimate bootstrapping. If a client starts from a bad checkpoint, the rest of its verification can be perfectly consistent and still lead to the wrong chain. This is not a bug unique to light clients, but light clients feel it more acutely because they intentionally carry less independent context.
A second failure mode is offline drift. In chains with changing validator sets, a client that disappears for too long may age past its safe trust window. Tendermint-based designs make this explicit through trusting periods and unbonding periods. If the old trusted state is too old, jumping forward becomes unsafe or impossible without a new checkpoint.
A third is data availability. A light client may be able to verify a proof if it gets one, but it cannot force the network to hand it over. This is why Ethereum discussions point to future decentralized data networks such as Portal Network, and why broader roadmap items like statelessness and more efficient commitments matter: not because they change the definition of a light client, but because they improve how proofs are served and verified.
A fourth is proof-format mismatch. Merkle proofs are not generic in the abstract; they depend on exact tree semantics. ICS23 works for certain lexicographically ordered stores and explicitly does not support tries like Ethereum’s Patricia trie without custom logic, because the key is not stored in the leaf in the way ICS23 expects. That detail matters. A proof system is only as portable as the commitment structure it assumes.
A fifth is implementation weakness. Cross-chain exploits often do not break the underlying cryptography; they break the software around verification. The Wormhole exploit, for example, turned on inadequate validation of an injected Solana sysvar account in a signature-verification path. The Ronin bridge compromise showed a different class of failure: when the trust anchor is a small operator-controlled validator quorum, key compromise can defeat the whole scheme. These are not failures of light clients per se, but they explain why trust-minimized verification is attractive and why implementation discipline around it is unforgiving.
How do different light-client designs trade off security, size, and prover cost?
Not every light client sits at the same point on the tradeoff curve. Some are merely lighter versions of full clients that verify headers and rely on RPC for everything else. Some are on-chain verifiers for other chains. Some use succinct proofs, accumulators, or recursive SNARKs to compress verification dramatically further. Research surveys note that these very light designs can inherit strong security properties, but they often move real cost onto provers, require trusted setup assumptions, or introduce operational complexity elsewhere.
That is the broader lesson: a light client does not make verification free. It rearranges where the work happens. A full node does almost everything locally. A classic light client does less locally and asks others for proof-bearing data. A succinct-proof design may make the client extremely small while asking specialized provers or validators to do much more work. The right design depends on what resource is scarce and what assumptions are acceptable.
Conclusion
A light client is a blockchain client that keeps a small trusted view of consensus, fetches specific data from others, and verifies that data locally against cryptographic commitments and consensus evidence. Its central promise is not “no trust,” but less blind trust for much lower resource cost.
If you remember one thing, remember this: a light client works because blockchains are rich in commitments. It throws away most raw data, keeps the commitments that matter, and asks for proofs when it needs details. Everything difficult about light clients comes from the same place; deciding which commitments to trust, and how to keep trusting the right ones as the chain moves forward.
How does a light client affect real-world usage?
Light-client properties change how quickly and safely you can rely on on-chain events, how bridges and wallets prove transfers, and how long you should wait before moving funds. Before you fund, trade, or bridge an asset, check the chain’s finality model, proof formats, and any on-chain light-client support; then use Cube’s trading and withdrawal flows to act on that assessment.
- Fund your Cube account with fiat on‑ramp or a supported crypto transfer.
- Open the asset or network info page and check the chain’s verification details: note its finality model (probabilistic vs provable), whether it exposes an on‑chain light client (e.g., IBC client) or sync‑committee primitives, and the trusting_period or recommended confirmation count.
- If you plan to bridge or withdraw, pick a route that cites on‑chain client verification or provable finality; when only custodial or oracle-based routes exist, require longer confirmation thresholds and confirm proof-format compatibility (ICS23 vs Patricia trie) before moving large amounts.
- Place your trade or withdrawal on Cube: use a limit order to control execution or a market order for immediacy; for sizable transfers, split the operation and wait for the chain‑specific confirmation or trusting_period you recorded before final settlement.
Frequently Asked Questions
A light client keeps a small trusted commitment (for example a header or checkpoint) and, when it needs a specific fact, requests that fact plus a cryptographic proof (typically a Merkle branch) that ties the fact back to the trusted commitment; the client verifies the proof locally instead of downloading or re‑executing the full chain.
Because different consensus designs change what counts as compact, verifiable evidence: PoW clients can often follow headers and proof‑of‑work, while PoS/BFT clients must also verify evolving validator authority (validator sets, committees or finality proofs), so the verification algorithm and state a light client needs depend on the chain’s consensus model.
A light client always needs a trust anchor (genesis, a trusted checkpoint, or an out‑of‑band trusted block root) and the article and specs note this is required in practice; however, most specs do not mandate how that trusted value is distributed, so obtaining it in a secure, user-friendly way remains an unresolved operational question.
Common failure modes are: starting from a bad checkpoint (bad bootstrap), drifting offline past the safe trusting window so validator-set continuity can’t be proven, lacking data availability even when proofs exist, having incompatible proof formats (e.g., trie vs lexicographic Merkle trees), and implementation errors or small trusted operator quorums that break the intended security (illustrated by bridge incidents).
Tendermint-style light clients keep a trusted header and validator-set hashes and advance using an intermediate verification (bisection) algorithm that checks sufficient overlap/signatures and respects parameters like trustLevel, trustingPeriod and unbondingPeriod so the client can safely justify newer headers without blindly accepting them.
Ethereum’s beacon-chain light client uses sync committees (a small subset of validators whose aggregated signatures are committed in chain state) so the client tracks a small LightClientStore (finalized header, current/next sync committees, best update) and verifies incoming LightClientUpdate objects via Merkle branches and sync-committee aggregates; this trades tracking the full validator set for following committees whose authority is itself committed on chain.
No; light clients reduce blind trust but still rely on assumptions: a bootstrapped trusted anchor, consensus assumptions (e.g., <1/3 Byzantine in Tendermint, partial synchrony for finality gadgets, or economic/network assumptions for PoW), and network/availability assumptions for getting proofs - the article describes a light client as trusting a model, not trusting nothing.
Not always - Merkle proofs depend on exact tree semantics and leaf/key formats, so standardized proof formats (ICS23) work for lexicographically ordered stores but do not directly support Ethereum’s Patricia trie without custom handling; proof-format mismatch is a real interoperability caveat.
Very compact/succinct designs (recursive SNARKs, accumulators, or protocols like FlyClient) can make clients extremely small, but research and the article warn these approaches typically move computational or trust costs to provers or require trusted setups and extra operational complexity rather than making verification free.
A light client can verify correctness of a supplied proof but cannot force the network to make that proof available; the article notes this data‑availability problem and points to proposals and networks (e.g., Portal Network, decentralized data layers) as ongoing efforts to improve proof delivery.
Related reading