What Is Proof of Stake?
Learn what Proof of Stake is, how it secures blockchains with staked collateral, how validators and finality work, and where the model depends on assumptions.
Introduction
Proof of Stake is a way for a blockchain to decide who gets to add new blocks and what history the network should accept, without relying on continuous energy expenditure. The central idea is simple but easy to underestimate: instead of making consensus expensive by burning electricity, the protocol makes misbehavior expensive by putting valuable assets at risk.
That change sounds cosmetic until you follow the mechanism through. In a proof-of-work system, the network leans on an external cost: miners must spend real-world resources to compete. In a proof-of-stake system, the network internalizes that cost: participants lock capital inside the protocol, and the protocol uses rewards, penalties, and sometimes outright destruction of stake to shape behavior. If this works, the chain gets security with much lower energy use and often with faster or stronger finality. If it fails, the protocol can drift into subtle attacks, social dependence, or validator concentration.
So the real question is not merely what is proof of stake? It is: **how can locked coins substitute for burned electricity as a basis for consensus? ** Once that clicks, most of the surrounding design choices (validator duties, slashing, finality rules, checkpointing, and even bootstrapping assumptions) make sense.
What core problems does blockchain consensus solve?
A public blockchain has to solve two problems at once. It must prevent Sybil attacks, where one real-world actor pretends to be many participants, and it must help widely distributed nodes converge on a single transaction history even when messages arrive late, machines fail, or some participants cheat.
In ordinary distributed systems, you often solve the first problem by deciding who is allowed in. A public blockchain does not get that luxury. Anyone can show up. So the protocol needs some scarce resource that cannot be faked cheaply. Proof of work uses computation and energy for this purpose. Proof of stake uses ownership of the chain’s native asset, locked as collateral.
This is the key invariant: in proof of stake, influence over consensus is tied to capital that is exposed to protocol-defined loss. Not just capital held in a wallet, but capital that has been committed in a form the protocol can track and penalize. That is why staking is not an incidental feature layered on top of consensus. It is the economic backbone of consensus itself.
How does Proof of Stake use locked collateral to secure a blockchain?
Here is the simplest useful model. Imagine a blockchain where participants called validators lock tokens into the protocol. The protocol then uses those validators to propose blocks, vote on blocks, or do both. If validators follow the rules, they earn rewards. If they go offline, they may lose some rewards or suffer mild penalties. If they sign conflicting messages or otherwise violate core safety rules, they can be slashed, meaning part of their stake is destroyed and they are forced out.
This mechanism works because consensus is not really about choosing a winner once. It is about making the honest path the best long-run strategy for a large set of independent actors. A validator with stake has something to lose. If the protocol can reliably detect certain forms of cheating, it can attach a predictable economic cost to them. That converts some Byzantine behavior from “technically possible” into “economically irrational.”
This is where many first explanations go too fast. The important point is not simply that validators have “skin in the game.” The stronger point is that the protocol itself can seize that skin when specific violations are provable. Without that enforcement step, early proof-of-stake designs ran into the classic nothing-at-stake problem: if signing on multiple competing forks is almost free, why not support all of them and collect rewards whichever fork wins? Modern proof-of-stake systems exist largely because they found ways to punish that behavior.
What actions do validators perform in a Proof of Stake network?
In most proof-of-stake systems, validators are not just passive depositors. They perform ongoing consensus work. The exact duties vary by protocol, but the structure is usually some combination of proposing candidate blocks and voting on which blocks should count.
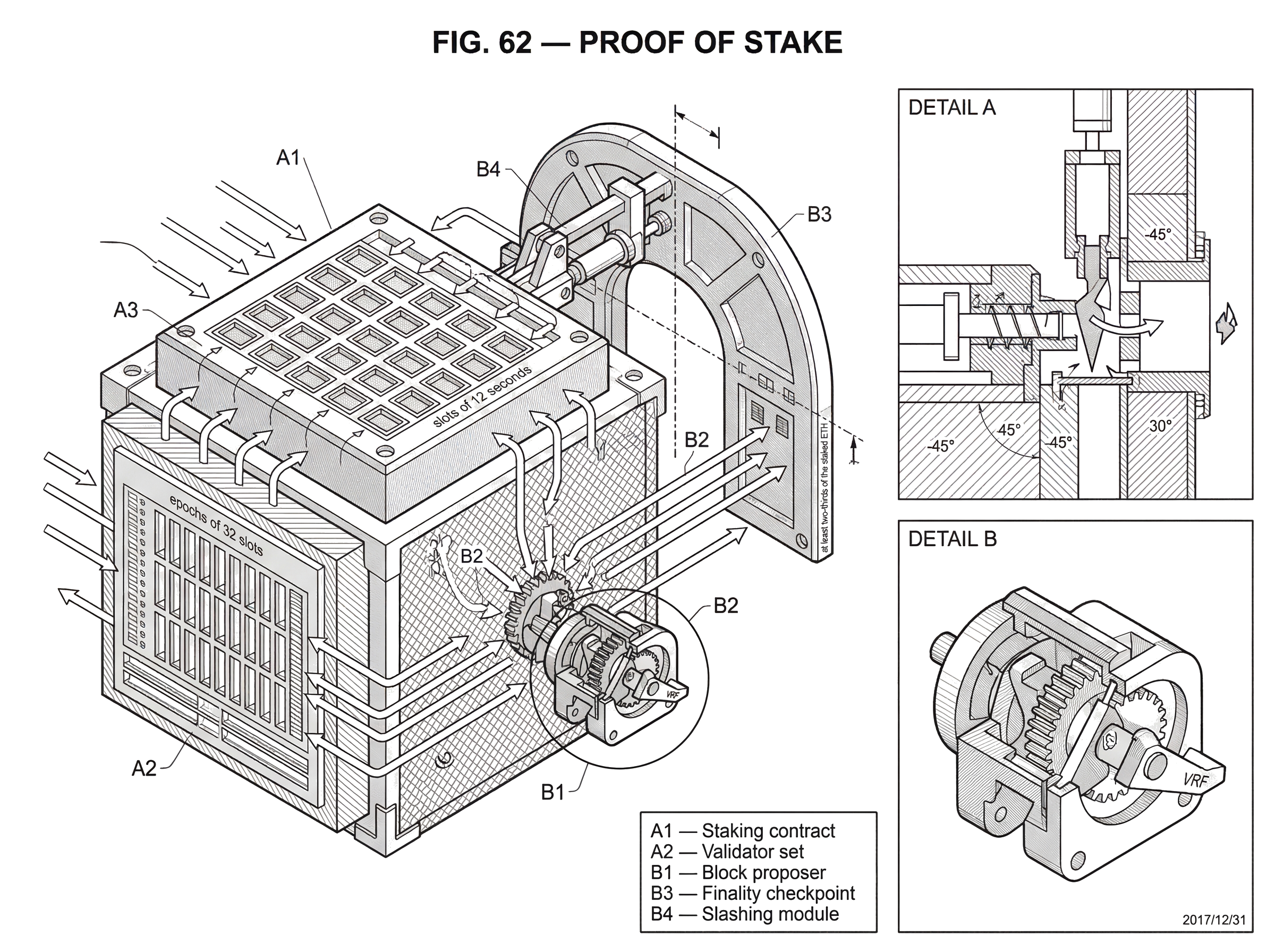
Ethereum provides a concrete example. A validator joins by staking ETH into a contract, then runs software that participates in consensus. Time is divided into fixed periods: slots of 12 seconds and epochs of 32 slots. In each slot, one validator is selected to propose a block, while other validators are assigned to attest to what they believe the canonical chain is. Those attestations are not informal opinions. They are signed consensus messages used for both chain selection and finality.
A simple narrative helps. Suppose a slot begins and one validator is chosen as proposer. That validator assembles a block and broadcasts it. Other validators assigned to that slot examine the block and the recent chain state. If the block is valid and extends the chain they believe the protocol favors, they sign Attestation for it. Those signatures do several jobs at once: they help the network decide which head of the chain to follow right now, they feed into rewards and penalties, and later they contribute to finality checkpoints. The protocol is therefore constantly converting validator behavior into measurable, billable evidence.
Other chains package the same idea differently. Tendermint-style systems use rounds of Byzantine Fault Tolerant voting among validators. Polkadot uses a nominated proof-of-stake model where nominators back validators and an election chooses the active set. Algorand uses cryptographic self-selection with verifiable random functions to privately determine who participates in a committee. The surface mechanics differ, but the underlying structure is the same: stake determines who has authority to help decide the next state, and that authority is constrained by rules that can punish certain deviations.
Why do Proof of Stake systems need unpredictable validator selection?
A proof-of-stake chain cannot let validators choose their own turns. It needs some way to assign proposal or voting responsibilities that is hard to game. That usually means pseudo-random selection, often weighted by stake.
Why stake-weighted? Because if a participant has committed 5% of all active stake, the protocol usually wants that participant to get about 5% of the opportunities to influence consensus. That keeps authority proportional to collateral at risk. But making that selection fair is harder than it sounds. If validators can predict or influence future selections too easily, they may exploit the schedule. This is the family of problems often called stake grinding: manipulating randomness so that future block opportunities tilt in your favor.
Different protocols handle this differently. Ethereum uses a combination of protocol randomness and stake-weighted sampling for proposer and committee selection. Algorand uses VRFs so users can privately check whether they were selected and prove that selection when they send messages. Tezos historically used cycle-based seed generation with validator commitments and reveals. The exact cryptographic machinery varies, but the reason it exists is always the same: consensus power must be assigned in a way that is both proportional to stake and resistant to manipulation.
When is a PoS block considered final and irreversible?
| Finality type | Reversion requires | Punishable on‑chain? | Typical time | Trade‑off |
|---|---|---|---|---|
| Probabilistic (PoW) | More cumulative mining work | No | Many confirmations (minutes+) | Energy-backed, slower guarantees |
| Economic finality (Casper‑style) | Burning large bonded stake | Yes (slashing evidence) | Epochs to finalize | Faster finality, requires slashability |
| BFT finality (Tendermint) | Breaking a 2/3 quorum | Yes (voting fault proofs) | Seconds to sub‑seconds | Immediate finality, quorum assumption |
Many people first meet proof of stake through the word finality, and that is not accidental. Proof-of-work systems often rely on probabilistic settlement: a block becomes less likely to be reversed as more work piles on top of it. Many proof-of-stake systems try to offer something stronger: explicit moments when reverting history would require a large amount of stake to violate rules and be destroyed.
This is often called economic finality. The idea is not that reversal becomes physically impossible. It is that reversal would require identifiable validators to burn very large sums of money. That gives users a different kind of assurance. Instead of asking, “How much cumulative work stands behind this block?” they can ask, “What amount of bonded capital would have to be sacrificed to reverse this?”
Ethereum again gives a useful example. Its finality mechanism, Casper FFG, organizes time into checkpoints. If votes representing at least two-thirds of the staked ETH support a checkpoint pair in the required way, the newer checkpoint becomes justified, and then an earlier checkpoint can become finalized. Once finalized, changing that history is not just a matter of producing an alternative chain. It would require slashable violations by a sufficiently large stake.
This is one of the deepest differences between proof of work and proof of stake. In proof of work, a chain reorganization depends on future expenditure of external resources. In proof of stake, a finalized reorganization depends on rule-breaking by already identified stakers whose deposits can be burned. The protection is therefore not merely computational; it is explicitly economic and, in some systems, near-immediate once the threshold is reached.
How do rewards and slashing shape validator incentives in PoS?
A proof-of-stake protocol cannot rely only on rare catastrophic punishments. It also needs everyday incentives that keep validators online, responsive, and aligned with the chain’s timing.
That is why most systems use a layered incentive structure. Honest participation earns regular rewards. Missing duties may reduce rewards or impose mild penalties. Severe safety violations trigger slashing. The gentle incentives handle routine operational behavior; the severe penalties defend the protocol’s core safety properties.
Ethereum’s reward design illustrates this layering. Validators earn base rewards tied to their effective balance and the total active stake. Attestations are broken into components such as source, target, and head votes, each affecting rewards or penalties. Missing some duties simply means not earning the associated reward; missing others can create explicit penalties. Slashing is reserved for serious offenses like double-voting or signing conflicting chain histories. There is also a correlation effect: when many validators are slashed together, the penalty increases, which makes coordinated attacks much more expensive than isolated mistakes.
That last feature matters. If the cost of misbehavior scaled only linearly and mildly, a large coordinated attacker might treat slashing as just another operating expense. By increasing penalties when many validators fail together, the protocol tries to make mass collusion economically explosive.
What security challenges did PoS designs have to solve (nothing‑at‑stake, long‑range, liveness)?
| Problem | Why it matters | Common mitigation | Primary trade‑off |
|---|---|---|---|
| Nothing‑at‑stake | Signing every fork prevents convergence | Slashing equivocation on‑chain | Requires provable evidence |
| Long‑range attacks | Former keys can forge old history | Weak subjectivity / recent checkpoints | Needs out‑of‑band trust |
| Stake grinding | Biasing future leader selection | Unbiasable randomness / VRFs | Complex randomness design |
| Mass validator outage | Finality can stall at scale | Inactivity leak / emergency recovery | Dilutes absent stake; blunt tool |
Proof of stake is conceptually elegant, but it is not automatically secure. Several of its most important ideas were invented to fix problems that show up precisely because stake is a cheaper resource to wield than electricity.
The first is the nothing-at-stake problem. In a naive longest-chain proof-of-stake design, creating blocks or votes on multiple forks may cost almost nothing, so validators have an incentive to support every plausible branch. That makes convergence harder. Slashing is the direct answer: if validators can be punished for signing conflicting messages, then building on every fork is no longer free.
The second is the long-range attack problem. In proof of stake, former validators may no longer have current stake at risk, but they may still possess old signing keys. In some models, they could cooperate to sign an alternative history far in the past. Because generating signatures is cheap, a new node that has been offline for a very long time might have trouble distinguishing the real history from a fabricated one if it relies only on genesis-to-present validation.
This leads to one of proof of stake’s most important assumptions: weak subjectivity. A node cannot safely come online after an arbitrarily long absence and trust only raw protocol rules from genesis. It also needs a reasonably recent trusted checkpoint or some recent view of the chain obtained out of band. That sounds uncomfortable at first, especially to readers trained on Bitcoin’s “validate from genesis” ideal. But it is better understood as a trade: proof of stake reduces ongoing physical cost and often improves finality, while accepting that very long-offline nodes need some recent anchor.
The third is liveness under mass outages. What happens if many validators disappear at once due to a client bug, an internet partition, or operator failure? Some proof-of-stake systems include emergency mechanisms to recover. Ethereum has an inactivity leak: if finality stalls for enough epochs, nonparticipating validators gradually lose stake so that the remaining active validators can eventually regain the supermajority needed to finalize again. This is a blunt tool, but it expresses a clear priority: the system is willing to dilute absent stake over time to restore liveness.
How do PoS protocol designs differ (chain‑based vs BFT vs committee models)?
It is better to think of proof of stake as a design space than as a single algorithm. The shared element is stake as the Sybil-resistance and incentive primitive. Beyond that, systems diverge.
Some are chain-based. In these designs, validators are assigned block-production rights over time, and the network follows a chain-selection rule somewhat analogous to Nakamoto consensus, though usually with more explicit voting or checkpointing layered in. Early designs and several research protocols fit here.
Others are BFT-style. In these, validators engage in rounds of voting to explicitly decide blocks or checkpoints, usually with a supermajority threshold such as two-thirds. Tendermint-style systems are the cleanest example, and Ethereum’s current design is in part a hybrid: a chain-selection rule for the live head plus a BFT-like finality gadget.
Still others push committee selection and agreement in different directions. Algorand relies heavily on VRF-selected committees. Ouroboros emphasizes provable security and slot leadership. Polkadot’s NPoS separates the broader staking population from the active validator set through nomination and election. Avalanche-family protocols are different again: they pair consensus with an external Sybil-resistance mechanism, and proof of stake is a natural fit for that role.
This variation is not a sign that the field is confused. It reflects a real engineering fact: stake tells you who is allowed to influence consensus, but it does not uniquely determine how agreement should be reached.
What practical benefits does Proof of Stake offer over Proof of Work?
The most visible advantage is energy efficiency. Since validators do not compete by doing useless work continuously, a proof-of-stake network can secure itself without the same scale of electricity consumption associated with proof of work.
But that is not the only benefit. Because there is no need for specialized mining hardware, participation can have lower hardware barriers, even though operational complexity may still be high. Ethereum, for example, reduced energy use by moving to proof of stake, but validating there is still operationally nontrivial because validators run multiple pieces of software and must manage uptime, updates, and key safety.
Proof of stake can also reduce the amount of token issuance needed to pay for security. In proof of work, miners must usually be compensated for ongoing external costs like electricity and hardware depreciation. In proof of stake, validators are primarily being compensated for opportunity cost, operational work, and the risk of penalties. That can make the security budget look different, though not necessarily trivial.
Finally, proof of stake can integrate more naturally with explicit finality and with scaling designs that benefit from committee selection, validator rotation, and structured voting. This was one of the reasons Ethereum cited in switching from proof of work to proof of stake.
What assumptions and failure modes does Proof of Stake rely on?
Proof of stake does not make decentralization automatic. In fact, it introduces its own concentration pressures. Large staking providers, exchanges, custodians, and liquid staking protocols can accumulate significant influence because many users prefer convenience, liquidity, or professional operations over direct validation. Ethereum measurement studies have found that liquid staking services have a large effect on staking-power concentration, even if overall decentralization compares roughly to Ethereum’s prior proof-of-work era.
Operational complexity is another underestimated issue. A proof-of-stake protocol may be energy-light and still be operationally fragile. Client bugs, validator software heterogeneity, upgrade coordination, network partitions, and service-operator failures can all affect participation and liveness. Ethereum has seen participation dips around upgrades and client incidents. Solana has experienced liveness failures where validator coordination was needed to restart the network after severe disruption. These events do not mean proof of stake is broken in principle, but they do show that real security depends on software and operations, not only on elegant incentive models.
There is also a deeper theoretical limit for some longest-chain proof-of-stake designs. Research has shown structural incentive problems around predictability, recency, and undetectable deviations in certain classes of protocols. The practical lesson is not that all proof of stake fails, but that protocol details matter enormously. You do not get security merely by replacing “hashpower” with “stake.” You need a design that addresses equivocation, randomness bias, long-range history, and coordination under failure.
Proof of Stake vs Proof of Work: how do their security models differ?
| Consensus model | Resource used | How commitment shown | Attack cost paid in | Typical benefit |
|---|---|---|---|---|
| Proof of Work | Computation / electricity | Ongoing hashpower spent | Continuous energy and hardware | Well-tested bootstrapping |
| Proof of Stake | Native token stake | Locked deposits / bonded stake | Burnable bonded capital (slashing) | Lower energy, faster finality |
The cleanest comparison is this: proof of work rents security from the physical world; proof of stake escrows security inside the protocol.
In proof of work, miners prove commitment by spending energy that cannot be recovered. Attacking the chain requires controlling enough hardware and electricity to outcompete honest miners. In proof of stake, validators prove commitment by locking capital that can be penalized. Attacking the chain requires controlling enough stake to dominate voting or finality, and in many cases it also requires exposing that stake to slashing.
Neither model is free of trust assumptions or concentration risk. Proof of work depends on hardware supply chains, electricity access, and mining economics. Proof of stake depends on stake distribution, slashing enforcement, recent-checkpoint trust for long-offline nodes, and healthy validator/client diversity. The important difference is not that one has assumptions and the other does not. It is that they place their assumptions in different places.
Conclusion
Proof of Stake is a consensus approach in which blockchain security comes from capital locked under protocol control rather than energy burned in open competition. Validators are given authority in proportion to stake, rewarded for honest participation, and penalized (sometimes severely) for actions that threaten safety.
What makes the idea work is not staking by itself, but the combination of stake, verifiable validator duties, slashing, and finality rules. That combination lets a blockchain turn coins into collateral and collateral into security. The trade is powerful but not magical: proof of stake gains efficiency and often stronger finality, while depending more on protocol design, operational discipline, and recent-state trust assumptions.
If you remember one thing tomorrow, make it this: proof of stake works by making consensus a problem of collateral management rather than energy expenditure.
What should you understand before using Proof of Stake infrastructure?
Understand the PoS risks that matter for trading or moving funds: finality rules, slashing exposure, validator concentration, and whether an asset is a liquid‑staked derivative with redemption delays. On Cube Exchange you can run these checks, fund your account, and act while respecting chain finality and liquidity constraints.
Frequently Asked Questions
Slashing makes signing conflicting messages provable and punishable: if a validator signs messages that violate safety rules (e.g., double-voting), the protocol can destroy part of their bonded stake and eject them, turning the formerly cheap strategy of supporting many forks into an economically costly one. This is the primary on‑chain defense against the nothing‑at‑stake problem, though precise slashing formulas and escalation behavior vary by protocol.
Weak subjectivity means a node that has been offline for a long time cannot safely reconstruct canonical history from genesis alone and needs a recent trusted checkpoint or external hint; this mitigates long‑range attacks where former validators with old keys could produce an alternative past. It is an explicit tradeoff of many PoS designs: lower ongoing energy cost in exchange for occasional out‑of‑band trust for very long‑offline nodes.
Protocols use unpredictable, stake‑weighted selection so proposers and voting committees are hard to precompute or bias; implementations range from Ethereum’s protocol randomness and stake‑weighted sampling to Algorand’s VRF‑based private selection. The goal is to prevent stake‑grinding or other manipulations that would let validators bias future opportunities in their favor.
Yes - many PoS designs provide stronger, explicit economic finality: once a checkpoint is finalized by a supermajority of staked votes, reverting it would require identifiable validators to violate slashing rules and forfeit large amounts of stake, so finality is framed as an economic barrier rather than cumulative external work. This makes some PoS finality guarantees tighter and faster than probabilistic PoW confirmations.
PoS introduces distinct centralization pressures: large staking providers, exchanges, custodians, and liquid‑staking protocols can concentrate voting power because users trade convenience and liquidity for custody, and empirical studies of Ethereum show liquid staking substantially affects stake concentration. Protocol design and governance choices influence how acute this risk becomes.
Many PoS systems include emergency or gradual recovery mechanisms for mass outages; for example, Ethereum’s inactivity leak slowly penalizes nonparticipating validators so active validators can eventually reach the supermajority needed to finalize again. These measures prioritize restoring liveness but can dilute absent validators’ stake and are deliberately blunt.
Validators generally do not need specialized mining rigs, so entry barriers for hardware are lower than PoW, but running a validator is operationally demanding: clients, key management, uptime, upgrades, and in Ethereum’s case running separate execution, consensus and validator components all create real operational complexity and risk. Lower hardware cost does not imply trivial operational requirements.
Related reading