Category archive
Foundations
The building blocks of crypto: wallets, private keys, consensus mechanisms, and the core concepts underpinning blockchain technology.
Articles
Current page
Page 13 of 20
Mar 21, 2026
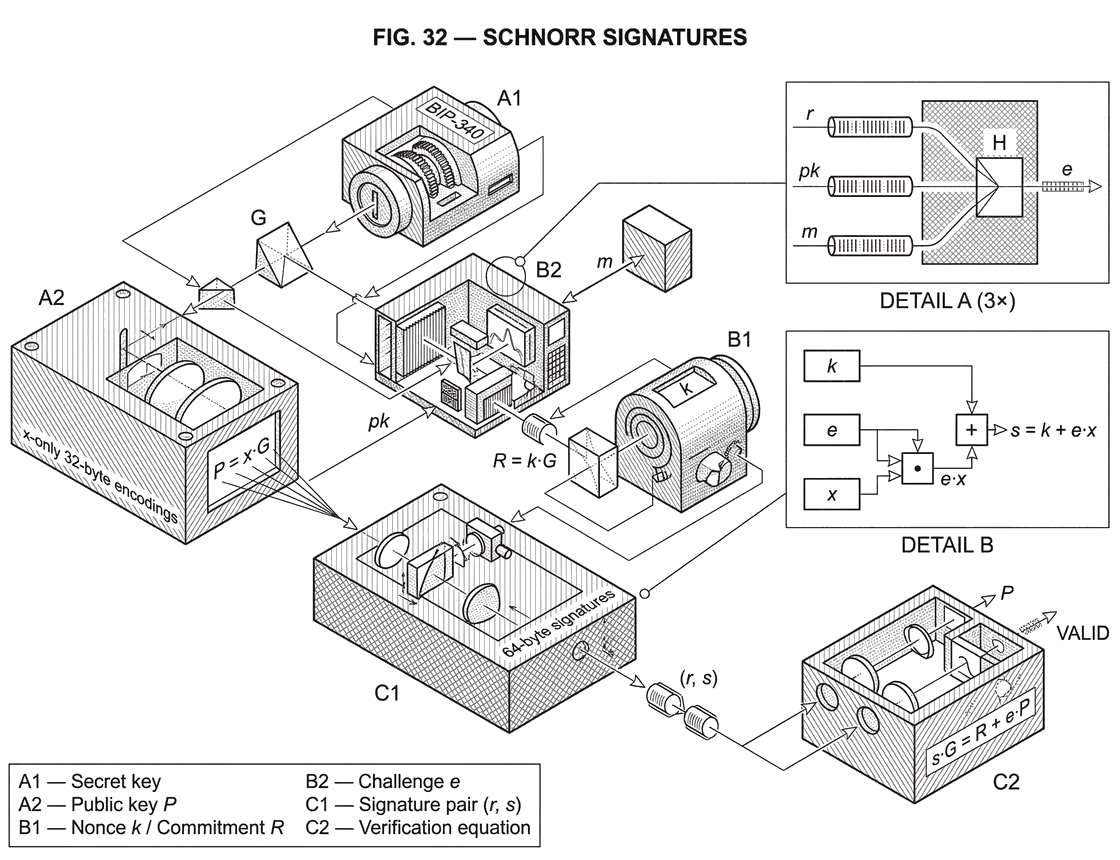
What is a STARK?
24 min read
Mar 21, 2026
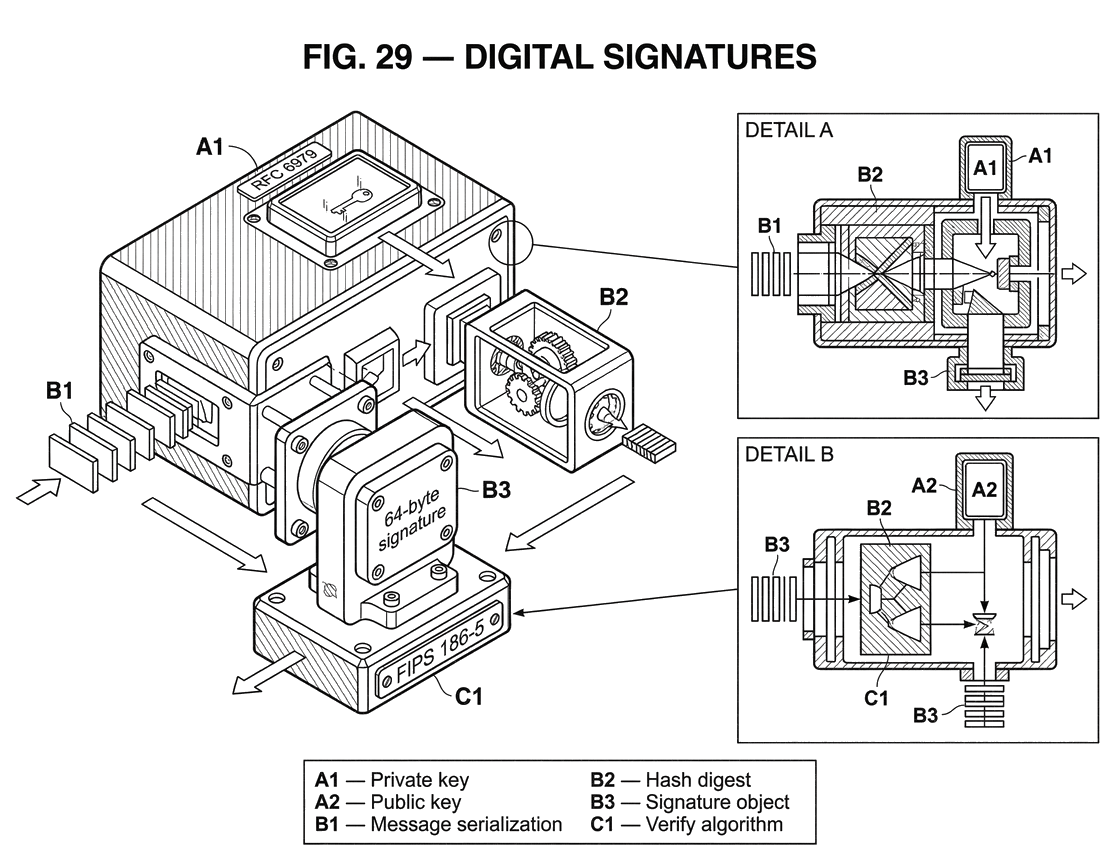
What is Ed25519?
24 min read
Mar 21, 2026
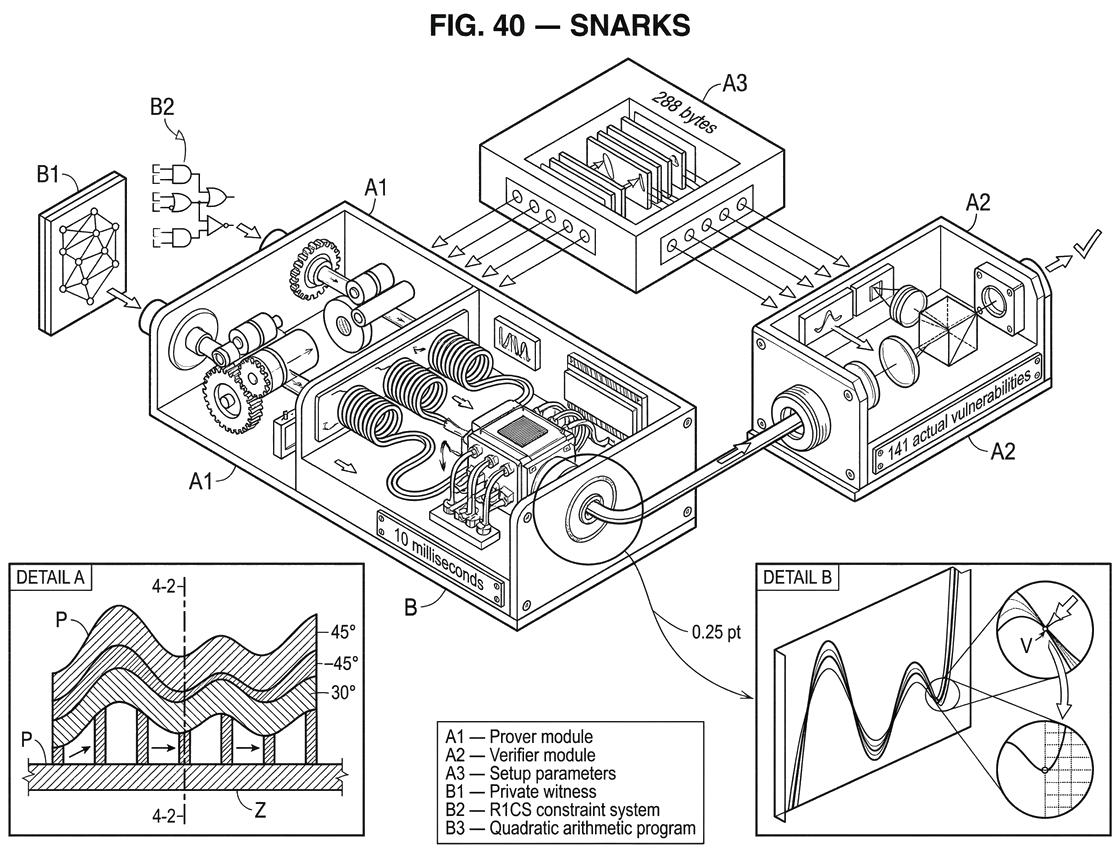
What Are SNARKs?
27 min read
Mar 21, 2026
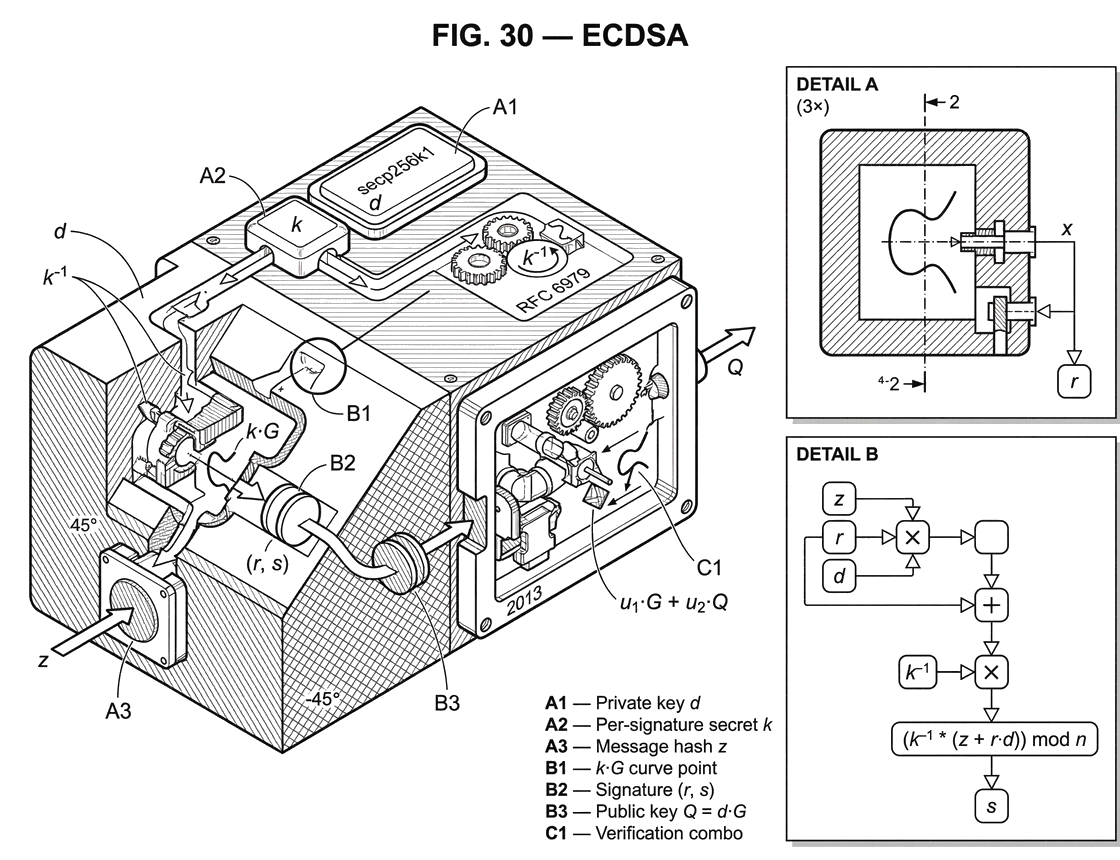
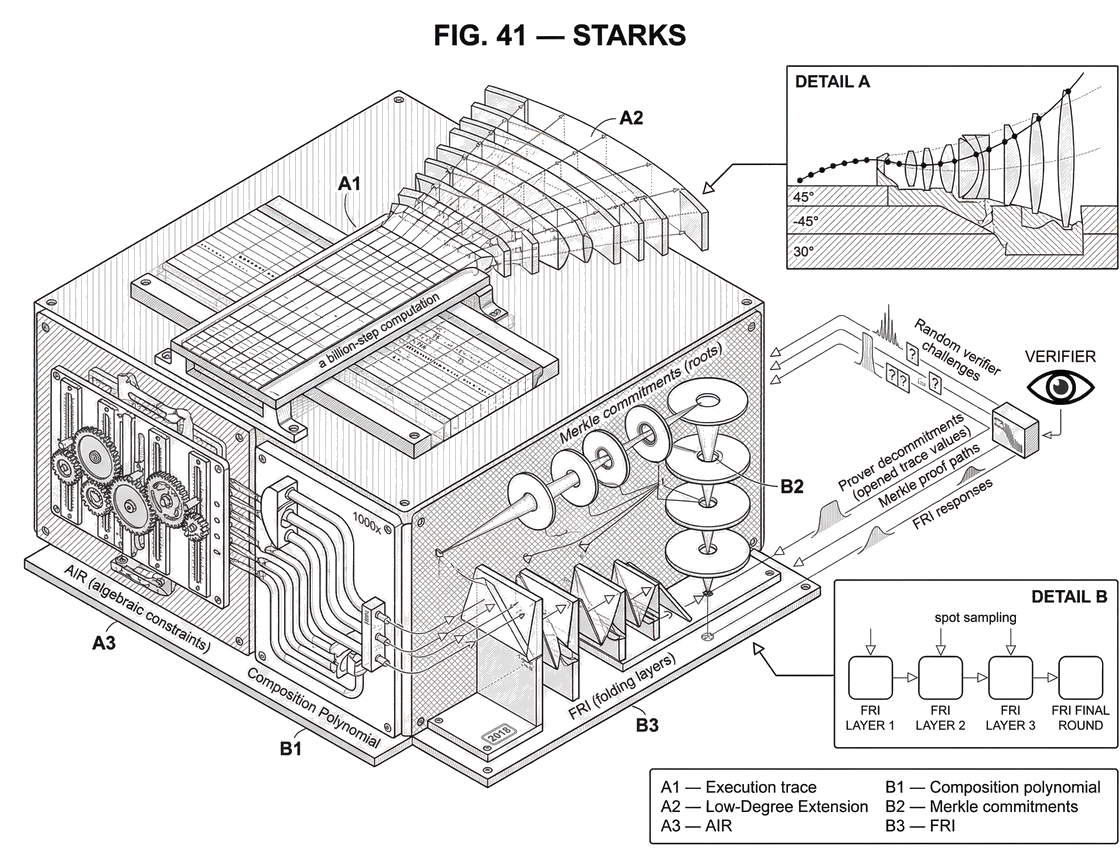
What is ECDSA?
22 min read
Mar 21, 2026
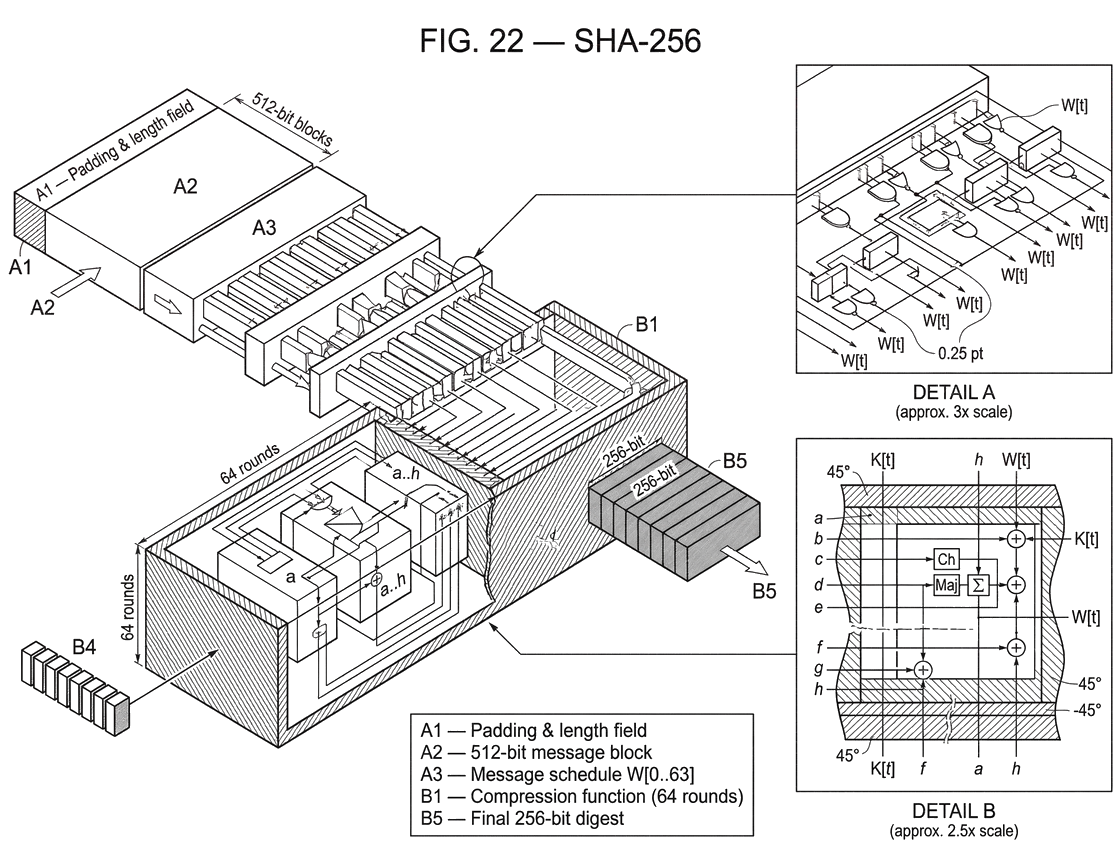
What is SHA-256?
24 min read
Mar 21, 2026
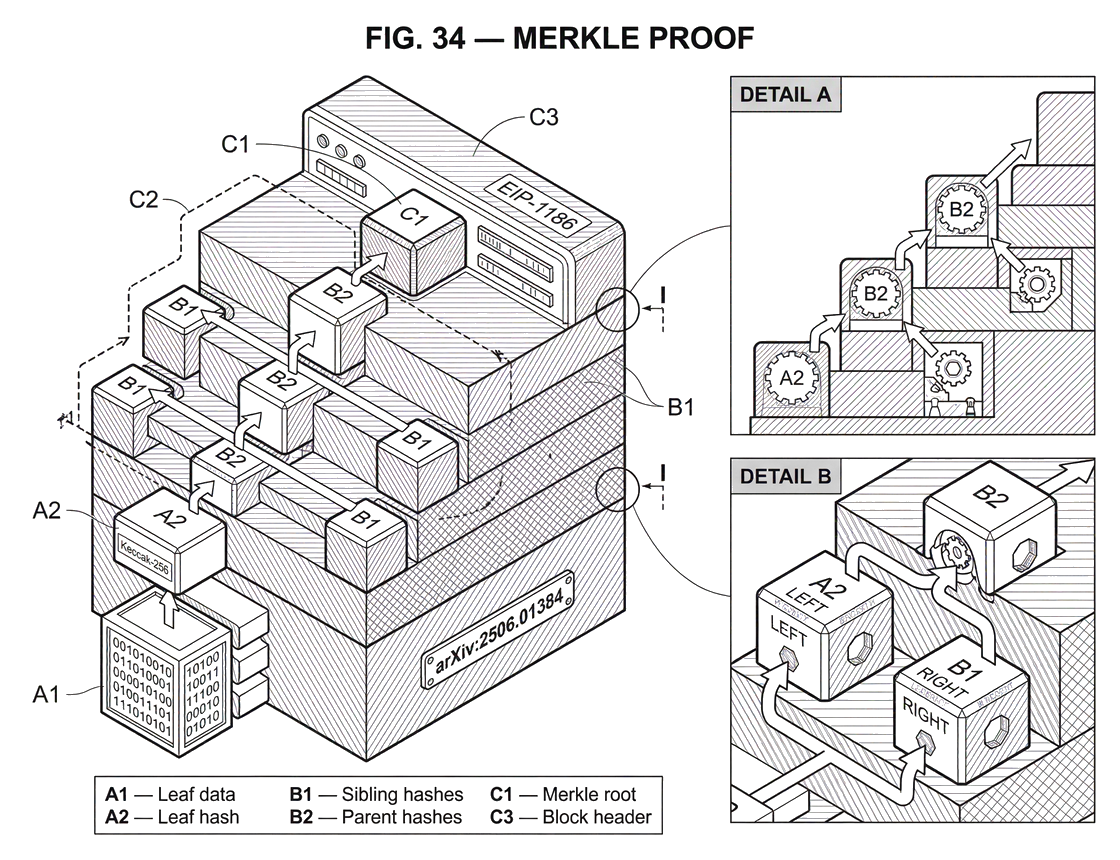
What is a Merkle Proof?
22 min read