Sub-hub archive
Foundations: Security
Articles
Current page
Page 1 of 2
Mar 21, 2026
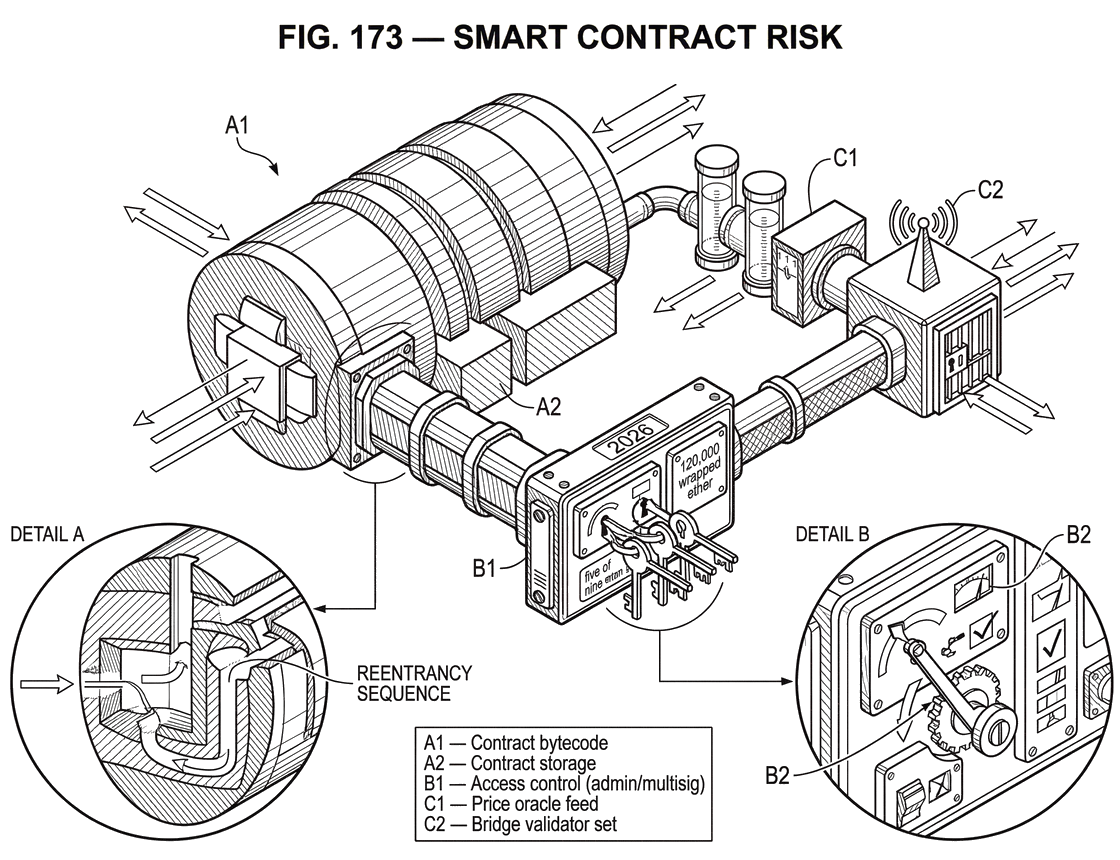
What is Smart Contract Risk?
26 min read
Mar 21, 2026
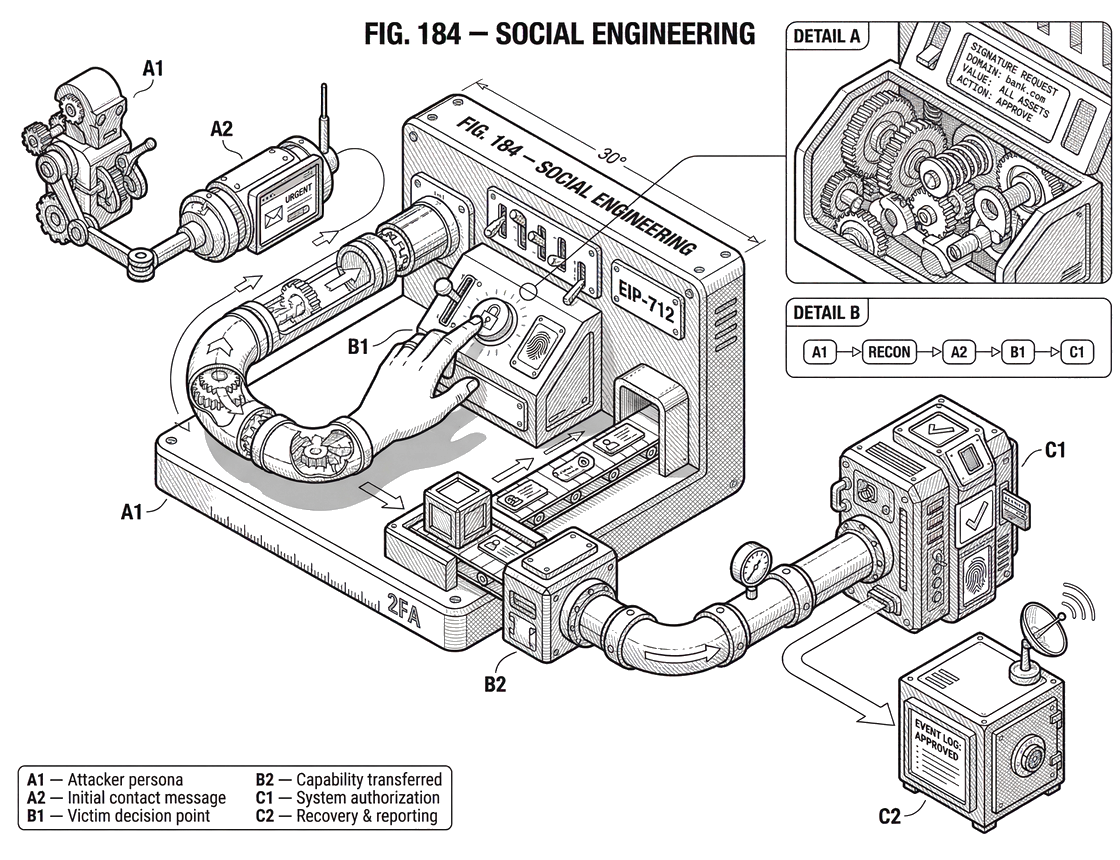
What Is Social Engineering?
25 min read
Mar 21, 2026
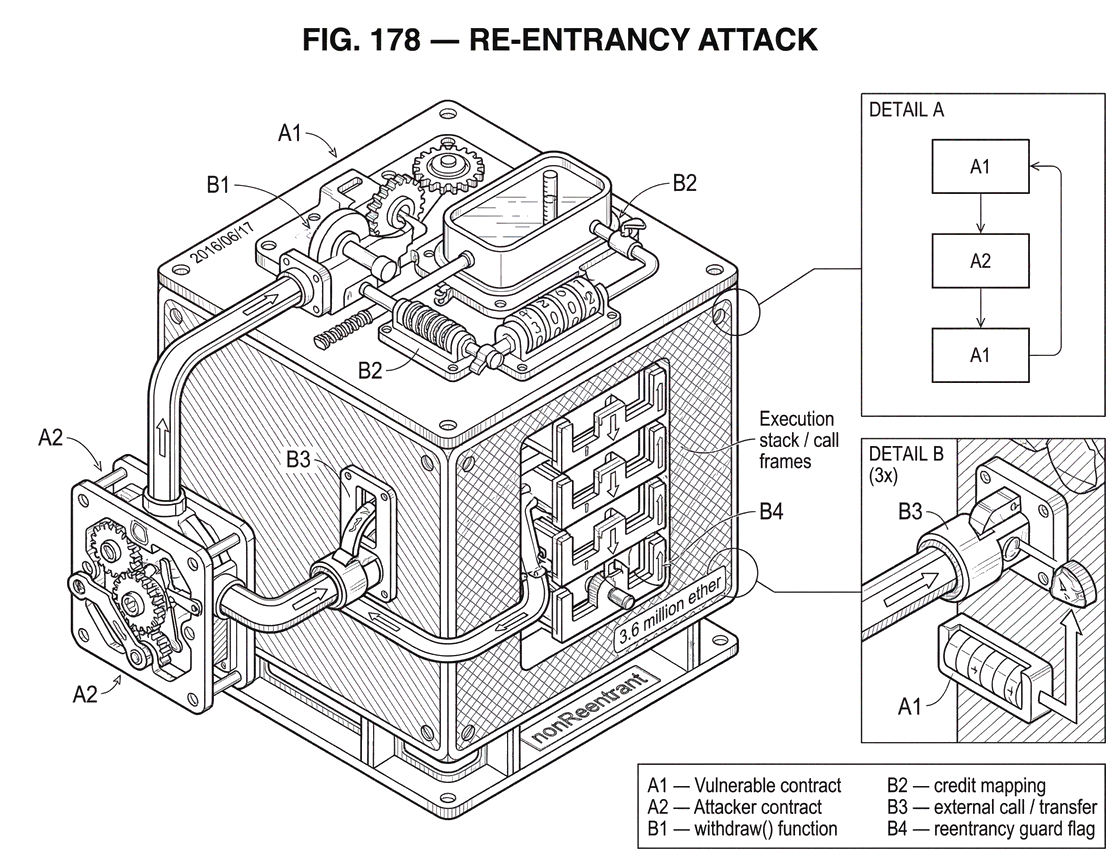
What is a Re-Entrancy Attack?
25 min read
Mar 21, 2026
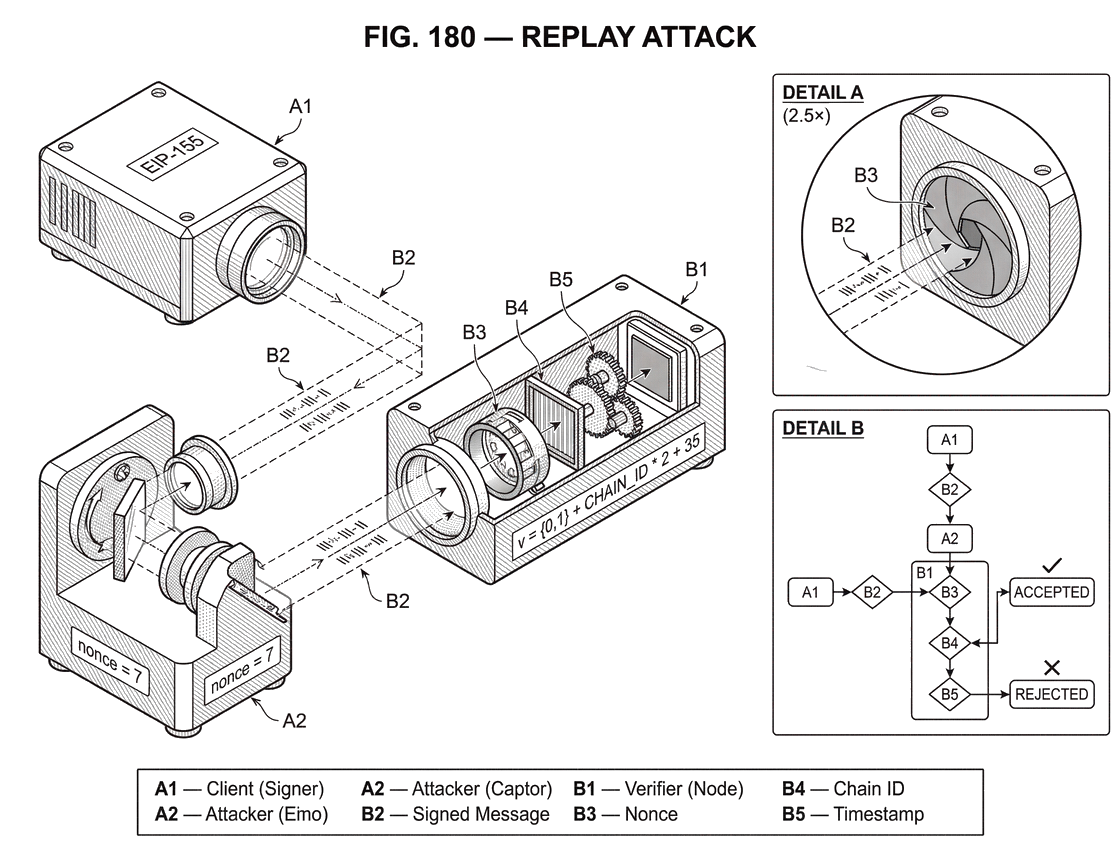
What is a Replay Attack?
26 min read
Mar 21, 2026
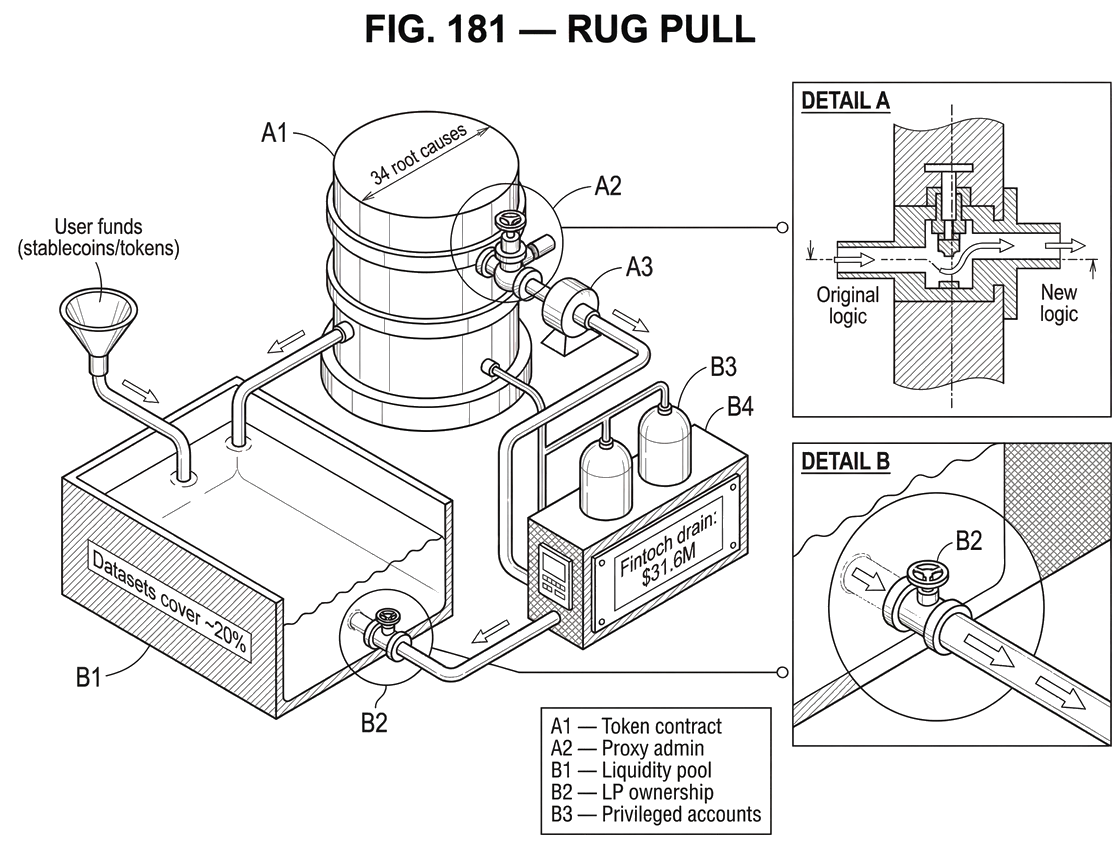
What Is a Rug Pull?
23 min read
Mar 21, 2026
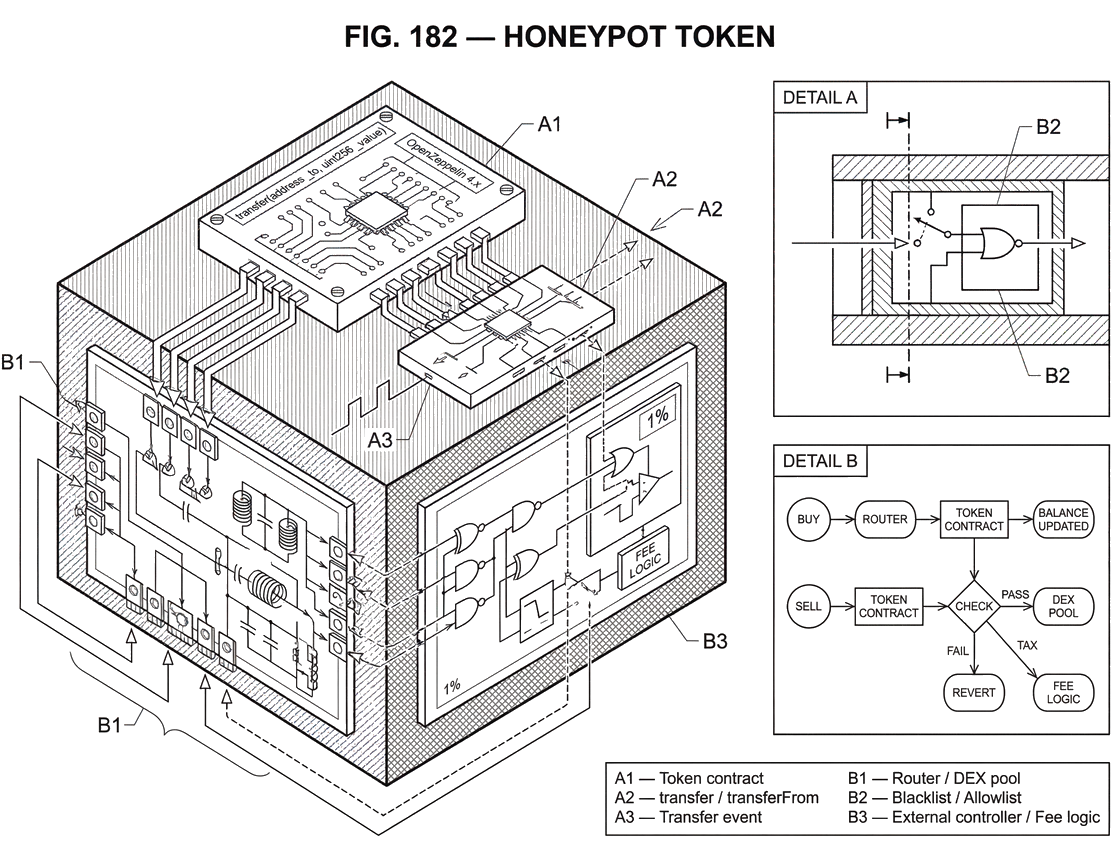
What is a Honeypot Token?
23 min read
Mar 21, 2026
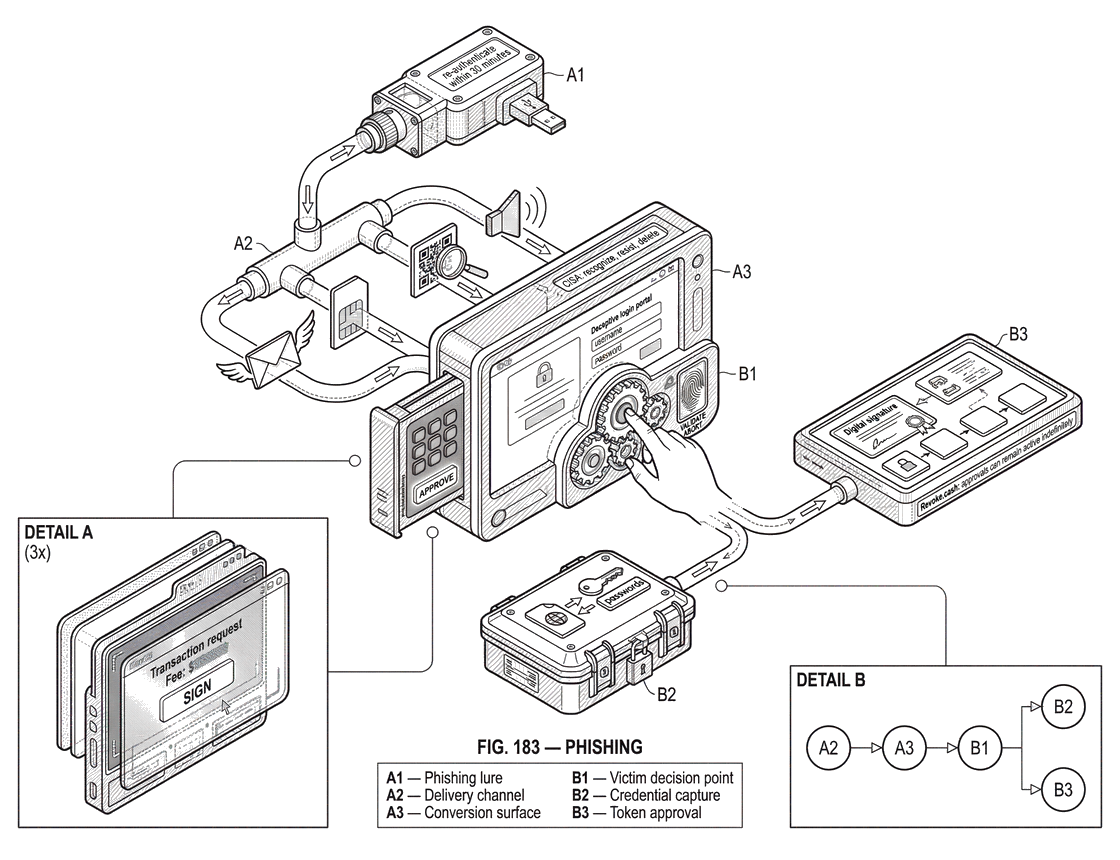
What Is Phishing?
25 min read
Mar 21, 2026
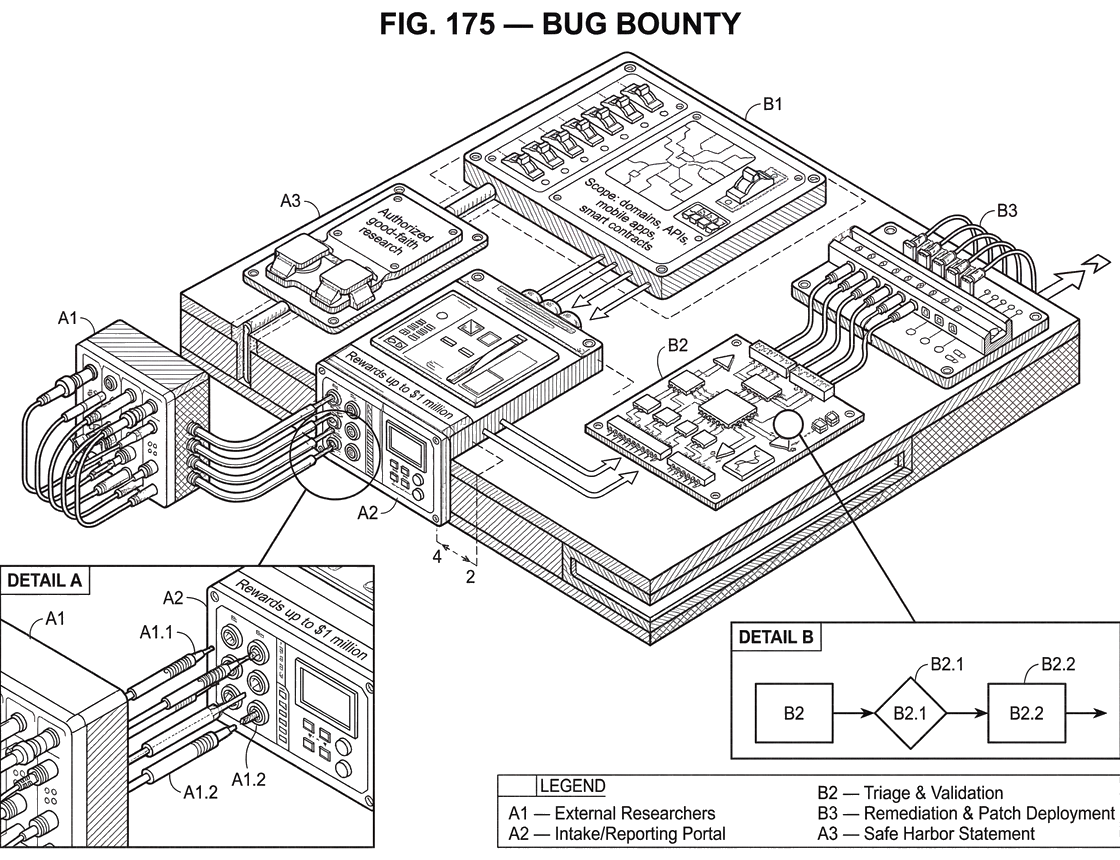
What is Bug Bounty?
24 min read
Mar 21, 2026
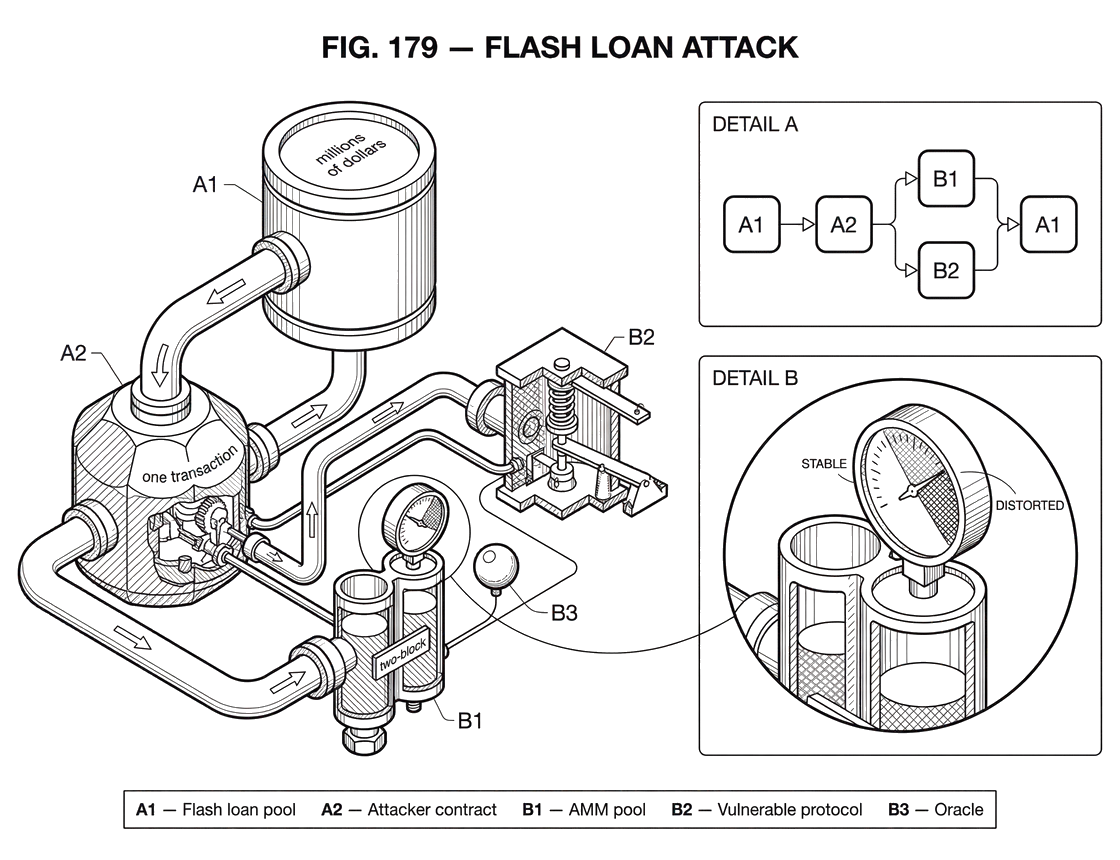
What is a Flash Loan Attack?
23 min read