What is ECDSA?
Learn what ECDSA is, how elliptic-curve signatures work, why the nonce matters, and where real-world implementations succeed or fail.
Introduction
ECDSA is a digital signature algorithm built on elliptic-curve cryptography, and it is one of the core mechanisms that lets modern cryptographic systems prove who authorized something without exposing the secret key that grants that authority. If you sign a software update, authenticate with a hardware token, or authorize a blockchain transaction, there is a good chance some variant of this mechanism is involved.
What makes ECDSA interesting is that it solves two problems at once. It gives short signatures and relatively small public keys compared with older systems such as RSA, which is why it became so widely deployed. But it also does something more subtle: it turns a private number into a public proof of authorization in a way that anyone can verify, while making it computationally hard to forge that proof or recover the secret key.
The catch is that ECDSA is not forgiving. The mathematics is elegant, but the implementation burden is real. In ECDSA, security depends not only on keeping the long-term private key secret, but also on handling a fresh per-signature secret value correctly every single time. That design choice is the source of both ECDSA’s practicality and many of its failures in the real world.
How does ECDSA let someone sign a message without revealing their private key?
A digital signature scheme exists to answer a simple question: how can someone prove that a message came from the holder of a secret key, while letting everyone else verify that proof using only public information? The verifier should learn that the signer had the key, but should not learn the key itself or gain the ability to sign other messages.
ECDSA does this using an elliptic-curve key pair. The private key is a secret integer d chosen from the range 1 to n - 1, where n is the order of a designated base point G on the curve. The public key is the elliptic-curve point Q = d·G. That multiplication is easy to perform in the forward direction, but given Q and G, recovering d is believed to be computationally infeasible for properly chosen curves. That asymmetry is the foundation: public verification remains easy, while key recovery remains hard.
The useful way to think about ECDSA is not as “a formula that outputs two numbers,” even though that is what signatures look like in the end. It is better to think of it as a consistency check. The signer creates a short proof that ties together three facts: the message being signed, a one-time secret chosen for that signature, and the signer’s long-term private key. The verifier then checks whether those relationships could have been produced by someone who knew the private key corresponding to the public key.
That is why ECDSA belongs in the broader family of digital signatures rather than encryption or key exchange. Encryption hides message contents. Key agreement lets two parties derive a shared secret. ECDSA does neither. Its job is authentication and integrity: proving that a message was authorized by the key holder and that the signed message was not changed afterward.
Why use elliptic curves for digital signatures and what advantages do they provide?
Before ECDSA specifically, it helps to understand what elliptic-curve cryptography contributes. An elliptic curve here is not a graphing curiosity; it is a mathematical structure whose points form a group with a defined addition law. Once you pick domain parameters (the finite field, the curve coefficients, a base point G, the order n of that point, and the cofactor h) you can “multiply” a point by an integer through repeated group operations.
This gives a one-way-looking operation: start with G, multiply by a secret scalar d, and obtain a public point Q. The security assumption is that the reverse problem, the elliptic-curve discrete logarithm problem, is hard on well-chosen curves. That hardness lets elliptic-curve systems offer a given security level with much smaller keys than older discrete-log systems over multiplicative groups or RSA-style modulus arithmetic. NIST’s guidance maps the bit length of n to roughly half that many bits of security strength, so an order of about 256 bits corresponds to roughly 128-bit security.
That efficiency is one reason ECDSA spread so widely. It appears in standards, authentication tokens, software signing systems, TLS deployments, and many blockchain protocols. Bitcoin and Ethereum use ECDSA over the secp256k1 curve. Tendermint-style systems also commonly use secp256k1 ECDSA for keypairs and signatures in certain contexts, with compressed public keys and signature normalization rules such as lower-S enforcement for canonical form. The details vary by ecosystem, but the core signature logic is the same.
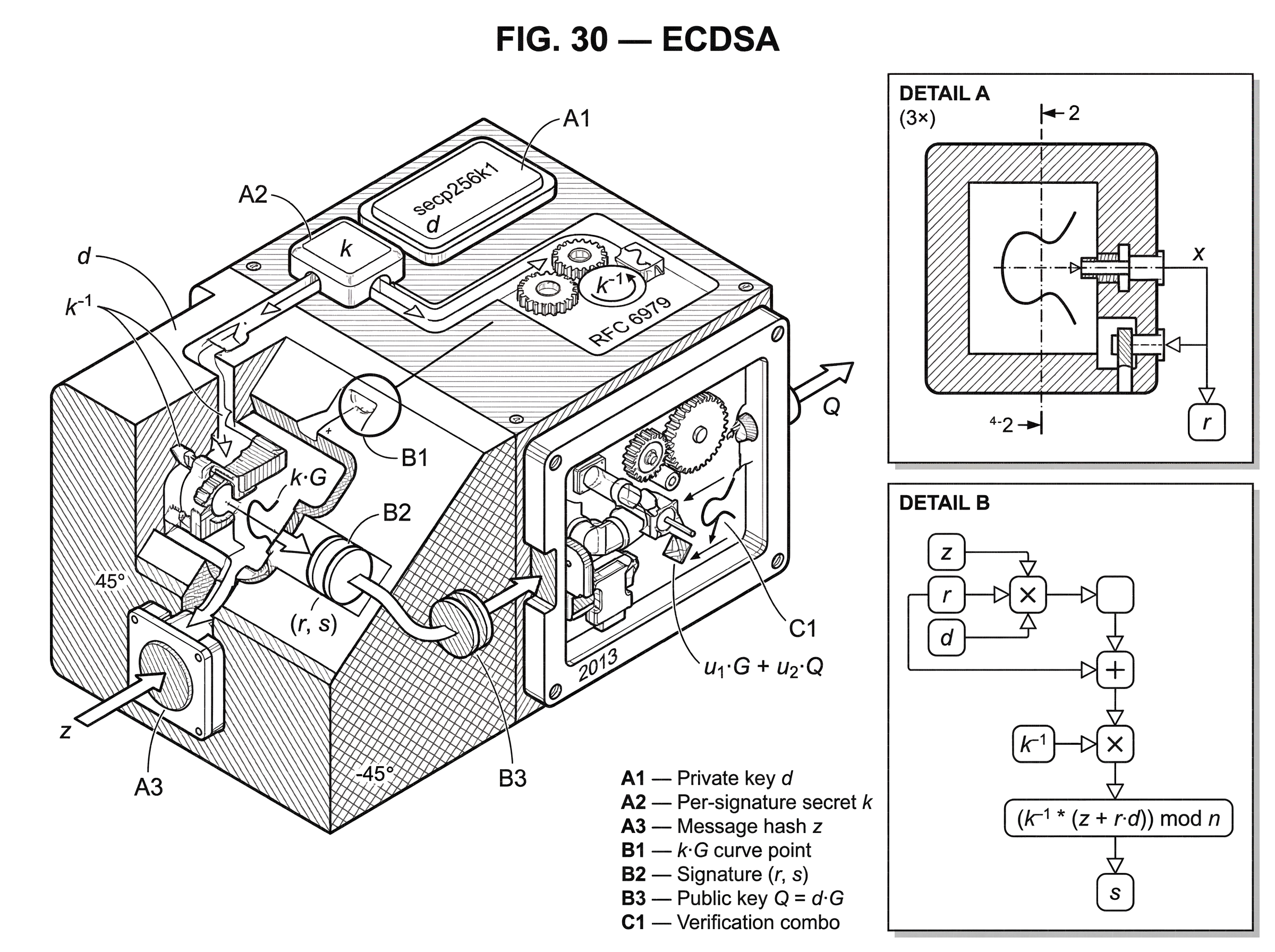
How does ECDSA produce and verify a signature step by step?
The central design choice in ECDSA is that each signature uses not only the private key d, but also a fresh per-message secret number k. This value must be chosen newly for each signature, or derived deterministically in a way that still makes it unique to the message and private key. Standards are explicit about this: a new secret k must be generated before each signature, and both k and its inverse must be protected like the private key itself.
Here is the mechanism in plain language.
Start with a message. The signer first hashes it using an approved hash function or XOF. If the hash output is longer than the bit length of n, the leftmost len(n) bits are used. This matters because ECDSA signs a number derived from the message, not the raw message bytes directly.
Then the signer takes the one-time secret k and computes the elliptic-curve point k·G. The x coordinate of that point, reduced modulo n, becomes the first signature component, r. That step is doing more than producing a number: it commits the signature to the hidden one-time scalar k through the curve’s group structure.
Next the signer mixes together the message hash, the long-term private key d, and the value r, then scales the result by k^-1 mod n, the modular inverse of k. The result is the second signature component, s. In the usual notation, if z is the integer derived from the message hash, then s = k^-1 (z + r·d) mod n.
So the signature is the pair (r, s).
At first glance this can seem arbitrary. Why should these two numbers convince anyone? The key is that the verifier can use the public key Q = d·G to reconstruct the same hidden structure without knowing d or k directly. Verification computes values derived from s^-1, the message hash, and r, then forms a point that is effectively a combination of G and Q. If the signature is valid, that combination lands on the same curve point whose x coordinate produced r during signing. In standard notation, the verifier computes u1 = z·s^-1 mod n and u2 = r·s^-1 mod n, then checks whether the x coordinate of u1·G + u2·Q, reduced modulo n, equals r.
That is the heart of ECDSA. The verifier never solves for the private key. Instead, it checks a geometric-algebraic consistency relation that only someone who knew d and a suitable k should have been able to create.
Example: how ECDSA signs a blockchain transaction (step‑by‑step)
Imagine Alice wants to authorize a blockchain transaction spending funds controlled by her key. Her wallet has a private scalar d and the corresponding public key Q = d·G. The transaction data is serialized, then hashed into a number z.
When Alice signs, her wallet generates a per-signature secret k. Using that secret, it computes the curve point k·G. From that point it extracts a value r, derived from the x coordinate modulo n. Now the wallet combines three ingredients: the message-derived number z, the long-term secret d, and the new value r. It scales that sum by the inverse of k, producing s. The output signature is (r, s).
A node on the network later verifies the transaction. It already knows Alice’s public key Q, either directly or via an address-recovery mechanism specific to the protocol. It hashes the same transaction data to get the same z. Then it uses r, s, z, and Q to build the point u1·G + u2·Q in the verification equation. If the signature is honest, this point lines up with the original hidden point k·G in exactly the way needed for the x coordinate check to reproduce r.
The important thing is not just that both sides did “matching math.” It is that the verifier’s computation replaces knowledge of the private key d with the public point Q = d·G, and replaces direct access to k with the structure left behind in r and s. The signature works because the algebra preserves the relationship between those hidden and public forms.
What happens if the ECDSA nonce k is leaked, biased, or reused?
| Failure mode | What leaks | Attacker data needed | Key recovery ease | Mitigation |
|---|---|---|---|---|
| Nonce reuse | Private key via linear solve | Two signatures with same k | Trivial | Ensure unique k every sign |
| Weak or predictable RNG | k predictability | Signatures and RNG state | Practical | Use CSPRNG or RFC6979 |
| Partial leakage (side‑channel) | Partial k bits | Many signatures with leaks | Possible via HNP techniques | Constant‑time ops and blinding |
| Biased nonces | Statistical k bias | Many signatures | Feasible | Reject biased k; harden RNG |
If there is one fact about ECDSA worth remembering tomorrow, it is this: the per-signature secret k is as sensitive as the private key, and often more fragile in practice.
The reason is visible directly in the signing equation s = k^-1 (z + r·d) mod n. If an attacker learns k for even one signature, then they can rearrange the equation and solve for the private key d. If the same k is reused across two different messages signed under the same key, the attacker can eliminate d between the two equations, recover k, and then recover d. What looks like a temporary helper value is actually carrying the whole security proof on its back.
This is why standards insist on generating a fresh k for every signature and protecting both k and k^-1 from disclosure or modification. It is also why so many real-world ECDSA failures have had the same shape: weak randomness, repeated nonces, biased nonces, or implementation leakage that reveals even partial information about k.
The Android SecureRandom incident is a classic example of the first class of failure. A bug in the PRNG used in Android’s Java cryptography stack made outputs predictable in some cases, and this was exploited against Bitcoin wallet applications in 2013. The cryptographic equations of ECDSA had not failed. The randomness feeding k had failed, and that was enough.
More recent work has shown something even more unsettling: attackers often do not need full nonce disclosure. Side-channel attacks such as LadderLeak demonstrated that leaking less than one bit of nonce information per signature can be enough, when combined with improved hidden-number-problem techniques, to recover ECDSA private keys from vulnerable implementations. EUCLEAK showed another path: a non-constant-time modular inversion in secure-element code enabled electromagnetic side-channel extraction of ECDSA private keys from affected hardware tokens. The lesson is not merely “protect the nonce.” It is that tiny correlations, timing differences, or biased generation can become mathematically amplified into total key recovery.
When should you use deterministic ECDSA (RFC 6979) and what does it change?
| Variant | RNG dependence | Signature repeatability | Side-channel risk | Best for |
|---|---|---|---|---|
| Randomized ECDSA | Fresh RNG per signature | Different each signature | Harder to correlate | Systems with good RNG |
| Deterministic (RFC 6979) | No RNG at signing | Same message → same sig | Higher correlation risk | Constrained RNG systems |
Because randomness failures are so damaging, deterministic ECDSA was introduced as an approved variant. Instead of drawing k from a live randomness source during signing, deterministic ECDSA derives k as a function of the message and private key. RFC 6979 specifies a widely used method based on HMAC_DRBG, seeded with the private key and the hashed message. FIPS 186-5 also approves deterministic ECDSA.
The immediate benefit is practical, not magical. If signing no longer depends on an external random-number generator at that moment, then one major source of catastrophic failure disappears. The same message signed with the same key produces the same signature, and standard ECDSA verifiers need not change at all. Deterministic signing is therefore attractive in constrained environments, testable implementations, and systems where RNG quality during signing is hard to guarantee.
But deterministic ECDSA does not mean randomness no longer matters. The private key itself still must be generated from high-quality entropy. And deterministic signing introduces a different engineering concern: repeated signatures now follow a fixed internal path for the same key and message, which can make side-channel observations easier to correlate unless the implementation is carefully hardened. Both RFC 6979 and FIPS 186-5 caution that deterministic schemes require strong defenses against side-channel and fault attacks, especially in hardware, embedded, and IoT settings.
There is also a subtle detail in RFC 6979 that illustrates how delicate nonce generation is. When the procedure generates candidate values for k, it does not simply reduce them modulo n, because that would induce statistical bias. Instead it rejects out-of-range candidates and retries. That may sound like pedantry, but ECDSA is precisely the kind of algorithm where “small bias” can turn into “recoverable key” under enough observations.
Which domain-parameter and public-key checks prevent ECDSA attacks and interoperability errors?
ECDSA is not just a formula over abstract points. It depends on agreed domain parameters. Over prime fields, these are typically written as T = (p, a, b, G, n, h): the field size p, curve coefficients a and b, base point G, the prime order n of G, and the cofactor h. These parameters define which group everyone is working in. If the parameters differ, the public key and signature equations are no longer talking about the same object.
That is why standards emphasize parameter and public-key validation. Before accepting a mathematically verified signature as meaningful, a verifier may also need assurance about the signatory’s identity, the validity of the domain parameters, the validity of the public key, and the fact that the signer possessed the private key at signing time. SEC 1 is explicit that conformant implementations must perform the cryptographic checks in the scheme specifications because those checks prevent subtle attacks.
This point is easy to underestimate. A public key is not just “some bytes.” In elliptic-curve systems, the bytes encode a point, and that point must actually lie on the intended curve, have the right order properties, and not belong to a malicious small subgroup or invalid curve. Similarly, point encodings must be interpreted correctly: compressed points use a prefix indicating enough information to recover the missing y coordinate, while uncompressed points carry both coordinates directly.
In many blockchain systems, these details show up indirectly. A wallet may store compressed public keys. A library may serialize signatures in ASN.1 DER, while another protocol uses raw R || S. A consensus rule may require lower-S normalization to reduce malleability. These are not changes to the mathematical core of ECDSA, but they are part of making implementations interoperable and safe.
ECDSA vs. Schnorr: why some systems keep ECDSA and others migrate to Schnorr-style signatures
| Property | ECDSA | Schnorr |
|---|---|---|
| Signature structure | Two-value (r, s) pair | Single scalar signature |
| Aggregation / composability | Poor native aggregation | Supports simple aggregation |
| Proofs and security | More intricate proofs | Cleaner, linear proofs |
| Malleability | Signature malleability exists | Non-malleable by design |
| Deployment status | Widely deployed (TLS, blockchain) | Growing adoption (Taproot, libs) |
ECDSA became dominant because it hit an attractive engineering point: shorter keys and signatures than older mainstream alternatives, standardization support, and compatibility with the elliptic-curve infrastructure that many systems were already adopting. In blockchain, that mattered immediately. Every transaction carries signatures or data from which signatures are recovered, so compactness and verification efficiency have visible costs.
At the same time, ECDSA is not the last word in signature design. Compared with Schnorr signatures, for example, ECDSA has a more intricate verification structure and weaker composability properties. Schnorr also has cleaner proofs and supports straightforward aggregation patterns that ECDSA does not. Historically, patent constraints helped delay Schnorr’s deployment, which is one reason ECDSA became so entrenched first. That historical fact explains adoption, but it also clarifies why newer systems sometimes prefer alternatives.
Still, “older” does not mean obsolete. ECDSA remains an approved and heavily deployed signature mechanism. The right conclusion is not that ECDSA is bad, but that it demands disciplined implementation. Good libraries reflect that. The libsecp256k1 project, for example, emphasizes constant-time, constant-memory-access signing and public-key generation, supports RFC 6979-style derandomized ECDSA, and uses implementation techniques intended to reduce leakage while staying fast on the secp256k1 curve.
What security and implementation assumptions does ECDSA rely on?
ECDSA’s security depends on several layers, and confusing them is a common source of misunderstanding.
At the mathematical layer, it depends on the hardness of the elliptic-curve discrete logarithm problem for the chosen curve and parameter sizes. If that assumption fails for a curve, then public keys no longer safely hide private keys.
At the algorithmic layer, it depends on the correct signing and verification equations, proper hash handling, and valid domain parameters. Small deviations can create incompatibility or weaken security.
At the implementation layer, it depends on secrecy of d, k, and related intermediates; correct modular arithmetic; constant-time or otherwise side-channel-resistant handling of secrets; and sound randomness or deterministic derivation where appropriate. This is where many actual failures happen.
At the system layer, it depends on key-management assumptions: who controls the private key, how identities are bound to public keys, and whether the verifier is checking the right key in the right context. A valid ECDSA signature only proves possession of the corresponding private key. It does not, by itself, prove that the key belongs to the person or contract you think it does.
Finally, there is the long-term assumption that classical elliptic-curve hardness remains intact. Current standards note that these algorithms are not expected to resist large-scale quantum computers. That is not a flaw unique to ECDSA, but it does place ECDSA within the broader migration question toward post-quantum or hybrid signature systems.
Conclusion
ECDSA is a way to prove authorization with a private key while keeping that key secret, using the one-way structure of elliptic-curve scalar multiplication. Its signatures are compact, efficient, and widely used across software security, authentication, and blockchains.
The idea that makes ECDSA click is simple: each signature combines a long-term secret key with a one-time secret nonce, and verification checks that the resulting algebra is consistent with the public key. That same design is also ECDSA’s sharp edge. If the nonce is reused, biased, predictable, or leaked through implementation details, the private key can collapse with it.
So the short version is worth remembering: **ECDSA is powerful because elliptic curves make public verification cheap; and fragile because each signature secretly depends on getting k exactly right. **
What should you understand before using ECDSA-based wallets and signing transactions?
Before using ECDSA-based wallets or signing transactions, understand the key risks (nonce quality, curve choice, and implementation-side channels) and confirm compatibility so you do not accidentally expose your private key. On Cube Exchange, complete a few concrete checks, then fund and trade or transfer with the correct asset and network.
- Check which signature curve and encoding your wallet and the target chain use (for example, secp256k1 with compressed keys and lower-S normalization). Inspect wallet settings or the on-chain address metadata in a block explorer.
- Verify your wallet’s signing mode and protections: look for RFC 6979 deterministic signing or vendor statements about RNG quality and constant‑time or secure-element protections in the device or software.
- Perform a small test transfer to your Cube deposit address and confirm the on-chain transaction validates and appears with the expected signature scheme and address format.
- Fund your Cube account with the matching asset on the correct network, open the relevant market, and place a limit order for price control or a market order for immediate execution; review estimated fill and fees before submitting.
Frequently Asked Questions
Because the signing equation s = k^-1 (z + r·d) lets an attacker solve for the long-term private key d if they learn k for even one signature, and reusing the same k across two messages lets an attacker eliminate d and recover k (and then d). Practical failures (weak or repeated nonces, biased nonces, or leakage) have repeatedly led to full key recovery in the wild.
Deterministic ECDSA (RFC 6979) derives k from the private key and the message via an HMAC_DRBG-style process, removing the need for a live RNG at signing time and preventing many randomness-related failures. However, it does not remove the need for good entropy when generating the private key, and deterministic signing can make side‑channel correlations easier unless implementations are hardened.
Yes; research and attacks have shown that leaking far less than the full nonce (even fractional bits or timing/EM side channels) can be amplified by lattice/hidden-number techniques to recover private keys, so partial leakage of k is often sufficient for key recovery.
Verifiers and implementers must check domain parameters and public-key validity (e.g., the point lies on the intended curve, has the right order, and is not in a small/invalid subgroup) in addition to the signature math, because malformed parameters or points can enable subtle attacks or interoperability errors.
Schnorr signatures offer simpler algebraic structure, cleaner proofs, and straightforward signature aggregation/composability that ECDSA lacks, so some newer systems prefer Schnorr for those features even though ECDSA remains widely deployed and approved.
No - deterministic signing only removes the per-signature RNG requirement; the private key must still be generated from high-quality entropy, and deterministic operation requires extra side‑channel defenses in hardware and embedded settings to avoid leakage of internal state.
Common causes include poor or predictable RNGs (e.g., the Android SecureRandom incidents), nonce reuse or low-entropy nonces, biased or malformed candidate nonces, and implementation side channels or non‑constant‑time arithmetic that leak k or k^-1; large-scale scans and published attacks have shown these problems in deployed wallets and libraries.
Generate a fresh, unbiased k per signature (or use RFC 6979 with its unbiased rejection rules), protect k and k^-1 and other intermediates with constant‑time and constant‑memory-access code, validate domain parameters and public keys, and ensure entropy sources and DRBGs meet NIST guidance (SP 800‑90A/90B) - these measures substantially reduce nonce-related and implementation risks.
Related reading