What is a Threshold Signature Scheme (TSS)?
Learn what a Threshold Signature Scheme (TSS) is, how threshold signing works, why it exists, and the security tradeoffs behind MPC-style key sharing.
Introduction
Threshold Signature Scheme (TSS) is a way for multiple parties to control a single signing key without any one party ever holding the full private key. That solves a surprisingly deep problem. In ordinary public-key cryptography, a signature is supposed to prove that one secret key authorized a message. But in many real systems, especially wallets, exchanges, validators, and distributed services, trusting one machine or one operator with that full key is exactly what you want to avoid.
The interesting part is that TSS does not change what outsiders verify. A blockchain node, API server, or application still sees a standard signature under a standard public key. The change happens inside the signer. Instead of one device running Sig(sk, m) with private key sk on message m, several parties jointly run a distributed signing protocol using secret shares of sk. If enough of them cooperate, they produce a valid signature. If too few cooperate, they should learn nothing useful about the full key and should not be able to sign.
That combination is why TSS matters. It gives the fault tolerance and compromise resistance people often want from multisig, but without requiring the verifying system to understand a special multisignature script or account format. In Bitcoin, Ethereum, Cosmos-style systems, and other chains, this can be operationally attractive because the resulting signature often looks like any ordinary ECDSA, EdDSA, Schnorr, or BLS signature the chain already accepts.
How does TSS split signing control while preserving ordinary signature verification?
| Model | Visibility | Verifier view | Compromise model | Privacy | Compatibility | Best for |
|---|---|---|---|---|---|---|
| Single-key | single signer | ordinary signature | single point failure | no signer privacy | native support | simple setups |
| Multisig | multiple signatures visible | multiple sigs or script | requires multiple keys | signers usually exposed | needs multisig support | transparent joint control |
| Threshold (TSS) | single standard signature | ordinary signature | threshold coalition required | signer subset typically hidden | compatible with existing systems | custody with compatibility |
The cleanest way to understand TSS is to separate two jobs that are usually fused together. A digital signature scheme has an internal secret, and it has an external verification rule. In the ordinary version, one signer knows the secret and runs the algorithm. In the threshold version, the secret is distributed across n parties, and the signing algorithm is replaced by an interactive protocol. But the external verification rule stays the same.
That is the key compression point: TSS changes who can produce a signature without changing what a valid signature is. A (t, n) threshold setup means n parties hold distinct shares, and any set of at least t + 1 can jointly sign. Any t or fewer should be unable to produce a signature and should not learn the private key from their shares alone. The public key remains a single public key pk, and the verifier still runs the ordinary verification algorithm Vf(pk, m, sig).
This is why threshold signatures are often contrasted with multisig. In a multisig system, the fact that multiple signers participated is usually visible in the transaction format or verification logic. The blockchain or application verifies several signatures or a script condition. In TSS, by contrast, the collaboration happens before the signature appears. The verifier typically sees only one standard signature. That preserves compatibility and often preserves signer privacy as well, because the verifier may not learn which subset of parties actually participated.
The analogy to a vault with multiple locks helps, but only up to a point. It explains the access policy: you need enough participants to open the vault. Where it fails is that TSS is not merely “several keys opening one door.” The parties are not each producing independent signatures that get bundled together. They are jointly computing one signature corresponding to one public key.
What single-point-of-failure problems does a Threshold Signature Scheme solve?
At first glance, secret sharing alone sounds sufficient. Split the private key into pieces, hand the pieces to different people, and reconstruct it whenever you need to sign. But that misses the real threat. If every signing event requires reconstructing the full private key on one machine, even briefly, then the system still has a single catastrophic point of compromise at the moment of signing.
TSS exists to avoid that reconstruction step. The private key is not just stored in pieces; it is used in pieces. That means the main security invariant is not simply “no one stores the whole key.” It is stronger: no full private key is ever assembled in one place during normal operation. If the protocol is well designed and correctly implemented, the signing computation itself preserves that invariant.
That changes the attacker’s job. Instead of compromising one device, one cloud account, one HSM, or one operator, the attacker now has to compromise enough parties to cross the threshold. In a 2-of-3 arrangement, one compromised share should not be enough. In a 3-of-5 arrangement, two should not be enough. The threshold turns key compromise from a single-point event into a coalition problem.
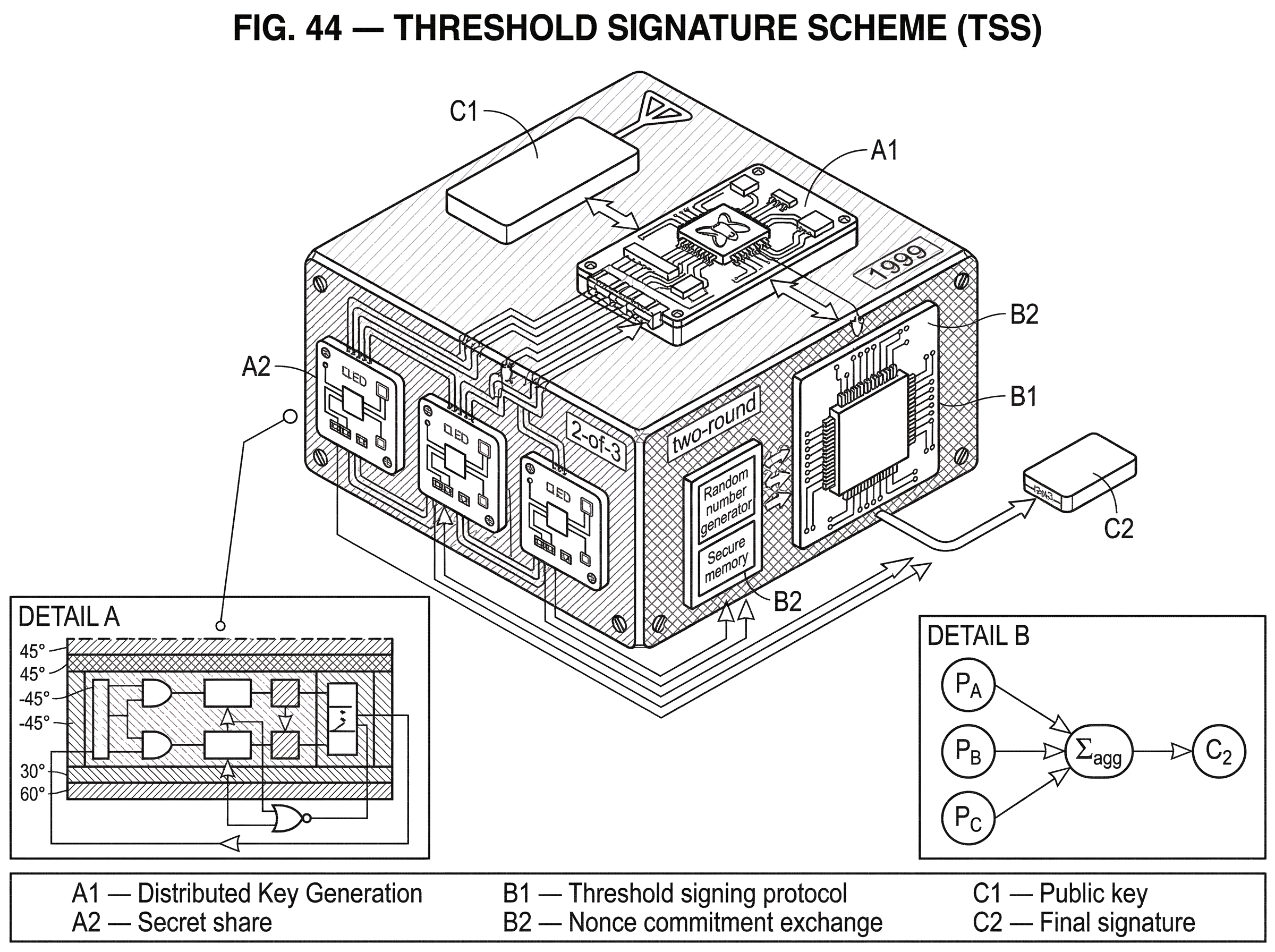
This is why TSS shows up naturally in custody and settlement systems. A useful concrete example is Cube Exchange’s decentralized settlement design, which uses a 2-of-3 threshold signature scheme: the user, Cube Exchange, and an independent Guardian Network each hold one key share; no full private key is ever assembled in one place, and any two shares are required to authorize a settlement. That is exactly the kind of operational structure TSS was built for. The system wants shared control over a single on-chain authority, while avoiding a single machine that can unilaterally move funds.
How does secret sharing enable threshold signing without reconstructing the private key?
Most threshold signature systems begin with a simpler primitive: secret sharing. In Shamir secret sharing, a secret is encoded as the constant term of a random polynomial over a finite field, and each participant gets the value of that polynomial at a different nonzero point. The mathematics ensures that enough points can interpolate the polynomial and recover the secret, while too few points reveal nothing.
This explains the threshold property, but not yet the signing property. Recovering the secret is not enough, because reconstructing it would reintroduce the very vulnerability TSS is meant to avoid. The real challenge is this: how do parties compute the effect of the secret key on a message without first combining their shares into the secret itself?
For some signature families, this is relatively natural. Schnorr-style signatures have an algebraic structure that fits multi-party computation well. Each party can contribute a share of the nonce and a share of the long-term secret, and these combine linearly in a way that is easier to reason about. This is why modern Schnorr threshold systems such as FROST can be relatively round-efficient: the RFC specifies FROST as a two-round Schnorr threshold protocol, and it emphasizes lower network overhead while retaining standard verification under a single group public key.
For other signature families, especially ECDSA, the problem is harder. ECDSA signing involves multiplicative relationships and inversions that do not decompose as cleanly across shares. That is why threshold ECDSA took longer to become practical, and why so much of the recent literature focuses on efficient ways to multiply or transform shared values without leaking information. The survey literature describes secure multiplication of shared secrets (often via multiplicative-to-additive conversion, or MtA) as the main technical obstacle that had to be overcome for efficient threshold ECDSA.
What happens during a 2-of-3 threshold signing session (worked example)?
Imagine three parties jointly controlling a 2-of-3 threshold wallet: Alice, Bob, and Carol. They have already completed setup, so each holds a share of the signing key, and the public key is known to the outside world. Now Alice and Bob want to sign a transaction.
If this were ordinary signing, Alice would load the full secret key and sign. In TSS, neither Alice nor Bob can do that. Instead, they start a protocol. Each side generates fresh secret randomness for this particular message, because digital signatures depend not only on the long-term key but also on per-signature nonce material. They exchange commitments or encrypted intermediate values, depending on the scheme, so that neither side can safely cheat by choosing values after seeing the other side’s contribution.
As the protocol continues, Alice and Bob transform their local shares and fresh randomness into partial results. In a Schnorr-style threshold scheme, those partial results often combine fairly directly into an aggregate nonce and then into per-party signature shares. In an ECDSA-style threshold scheme, the parties usually need heavier subprotocols to compute products of secret-shared values without revealing them, because the final ECDSA formula depends on terms that are not purely linear in the hidden inputs.
At the end, the parties produce pieces that can be combined into one ordinary signature. The outside blockchain node sees a normal signature under the wallet’s public key. It does not learn whether Alice and Bob signed, or Alice and Carol, or all three. What mattered internally was that enough shares participated and that the protocol enforced consistency along the way.
That last point matters more than it first appears. A threshold signing protocol is not just about distributing arithmetic. It is also about preventing a malicious participant from biasing nonces, feeding malformed values, or extracting information from honest parties’ responses. Much of the real complexity of TSS lives there.
Why is distributed key generation (DKG) necessary for secure TSS setup?
A threshold signature system is only as sound as its setup. If some trusted dealer creates the full private key first and then hands out shares, the signing phase may be thresholdized, but the system still had a moment when one entity knew the full key. In some environments that may be acceptable. In many, it defeats the point.
That is why distributed key generation, or DKG, is foundational. In DKG, the parties jointly generate a public key and individual secret shares such that no participant ever learns the full private key. The 1999 work by Gennaro, Jarecki, Krawczyk, and Rabin is a canonical early reference for secure distributed key generation in discrete-log-based systems. The conceptual role of DKG is straightforward: it removes the trusted dealer from the picture and aligns the setup phase with the same decentralization goal as the signing phase.
This is also where verifiable secret sharing enters. During DKG, parties need ways to prove that the shares and commitments they distribute are consistent, so a malicious participant cannot poison the setup with malformed data that later breaks signing or leaks information. If the setup is wrong, the system may produce invalid signatures, fail unpredictably, or worse, create shares whose combination gives an attacker leverage over the honest parties.
The practical lesson is simple: threshold signing is not only a signing protocol; it is a lifecycle. Key generation, resharing, participant changes, nonce handling, and transport security are all part of the security boundary.
Why is threshold ECDSA more complex than threshold Schnorr?
| Signature family | Algebraic fit | Main obstacle | Typical tools | Practicality |
|---|---|---|---|---|
| Schnorr | linear in exponent | nonce bias attacks | FROST; commitments | round-efficient and cleaner |
| ECDSA | multiplicative and inverses | secure multiplication (MtA) | Paillier; MtA; ZK range proofs | complex; heavier proofs and tools |
| BLS | pairing-friendly aggregation | adaptive-security proofs | DKG; pairing groups | compact signatures; different assumptions |
The reason Schnorr threshold signing is often cleaner comes from the algebra. Schnorr signatures are linear enough that secret shares can often stay in the exponent and combine naturally. This does not make Schnorr threshold protocols trivial, but it makes the path more direct.
ECDSA, by contrast, mixes hidden values through multiplication and inversion in ways that are awkward under secret sharing. If parties hold additive shares of secrets, multiplying those shares is not a local operation. You need an additional protocol that turns local secret pieces into shares of a product, without revealing the multiplicands themselves. This is where MtA protocols and additively homomorphic encryption, often Paillier, become important in threshold ECDSA constructions.
The 2019 ePrint by Canetti, Gennaro, Goldfeder, Makriyannis, and Peled is important here because it presents a practical dealerless threshold ECDSA design for general t-of-n settings and emphasizes efficiency improvements over prior work. Mechanically, the paper uses pairwise share-conversion techniques inspired by MPC systems such as SPDZ, so parties can obtain additive sharings of values like products and inverses needed inside ECDSA without reconstructing secrets. This was a major step toward making threshold ECDSA practical for blockchain-compatible wallets.
But the deeper lesson is not just “ECDSA is harder.” It is that the exact signature algorithm matters enormously. A threshold signature scheme is not a single protocol that works identically everywhere. It is a family of constructions that adapt to the algebra of the underlying signature scheme. When people say “TSS” in production systems, they often specifically mean threshold ECDSA because they need compatibility with systems that already verify ECDSA signatures, such as Bitcoin or many EVM-style workflows. In other settings, threshold Schnorr or threshold BLS may be a better fit.
What operational trade-offs do rounds, presignatures, and aborts introduce in TSS?
| Signing mode | Online latency | Stored-state risk | Abort sensitivity | Typical use |
|---|---|---|---|---|
| Local single-key signing | minimal | none | none | single-owner wallets |
| Threshold with presigning | very low online latency | presignatures are sensitive | preprocessing aborts possible | low-latency MPC wallets |
| Round-optimized threshold (e.g., FROST) | moderate (few rounds) | low if no presignatures | DoS by misbehaving parties | decentralized signing with fewer rounds |
Threshold signing is rarely just “more secure signing.” It usually trades simplicity for distributed trust. Those tradeoffs show up most clearly in interactivity.
An ordinary signature call is local: feed in a message, get back a signature. A threshold signing session is typically interactive. Parties must exchange commitments, proofs, ciphertexts, shares, or confirmations across one or more rounds. That means latency, coordination, and a larger attack surface around networking and liveness. If one participant goes offline at the wrong moment, signing may stall. If one participant sends malformed data, the protocol may abort.
This is why round optimization matters. FROST aims to reduce Schnorr threshold signing to two rounds. For threshold ECDSA, later work pushes expensive work into an offline preprocessing phase so that the online phase, once the message is known, becomes faster. The 2020 work on one-round threshold ECDSA with identifiable abort is a good example: it moves much of the work into message-independent preprocessing and leaves a single online communication round when the actual message arrives.
That is useful operationally, but it introduces another subtlety: presignatures or preprocessed state become sensitive assets. Survey work on ECDSA threshold signing emphasizes that these offline artifacts must be stored carefully and wiped after use, because if they are reused or leaked, they may enable signing without the long-term private key. In other words, preprocessing reduces online latency by turning some future signing power into stored cryptographic state. That state deserves the same seriousness as key material.
Another distinction that matters is the difference between security and robustness. A protocol may be unforgeable (meaning attackers cannot produce signatures without enough shares) yet still be easy to disrupt. FROST, for example, explicitly does not provide robustness in the sense of guaranteeing that signing completes even if a participant misbehaves. A malicious participant can cause denial of service by sending malformed shares or by failing to finish the protocol. Some protocols add identifiable abort, meaning honest parties can at least agree on who caused the failure. That does not prevent the abort, but it can support remediation, replacement, or economic penalties.
What implementation pitfalls can break TSS security?
There is a temptation to think that once a threshold protocol has a paper and a proof, the main problem is solved. The recent history of TSS is a strong warning against that view.
A large fraction of real risk lies in implementation details that sit below the level of the headline theorem. Paillier parameter sizing and range proofs matter in threshold ECDSA. The 2019 threshold ECDSA paper itself discusses a flaw in an earlier version: if encrypted values were not properly range-checked and Paillier moduli were too small, information leakage could enable key recovery. That is not a cosmetic issue. It means a seemingly technical omission can completely defeat the threshold guarantee.
The same pattern appears in deployed libraries. The Trail of Bits disclosure on Shamir and Feldman VSS bugs showed that simple-looking mistakes in share identifiers can leak the secret or crash nodes. If a share is effectively evaluated at zero modulo the group order, the share can equal the secret itself. That is a vivid example of why threshold cryptography is unforgiving: the underlying math may be elegant, but the invariants are brittle if the code does not enforce them exactly.
The TSSHOCK disclosures make the point even more sharply. Verichains reported key-extraction attacks against threshold ECDSA implementations that exploited ambiguous encoding and unsound optimizations. Their write-up argues that in some cases a single malicious participant could recover the full private key after only one or two signatures, without forcing an abort and without obvious traces. Whether every detail of every affected implementation generalizes is less important than the core lesson: threshold security is a systems property, not just a protocol property.
Even mature libraries say as much implicitly. The widely used Go library tss-lib implements threshold ECDSA and EdDSA with key generation, signing, and resharing, but it leaves transport to the application. That is a sensible engineering boundary, yet it means integrators must design secure broadcast and point-to-point channels, encryption, session identifiers, and timeout handling themselves. If those layers are weak, the threshold protocol above them may not save the system.
Which signature algorithms are best suited for threshold signing (ECDSA, Schnorr, BLS)?
Once the basic idea is clear, it helps to see that TSS is not tied to a single blockchain or a single signature algorithm.
For ECDSA, threshold schemes are especially important because many existing blockchains and wallet standards already expect ECDSA signatures. The payoff is compatibility: a threshold signer can control a normal-looking externally owned account or UTXO-spending key without changing the chain’s verification rules. That is a major reason threshold ECDSA became so central in custody and MPC wallet systems.
For Schnorr and EdDSA-style systems, threshold signing is often more natural algebraically. FROST shows what that looks like in standard form: a threshold protocol over a prime-order group, with ciphersuites including ristretto255, Ed25519, P-256, and secp256k1. That breadth matters because it shows the idea is not attached to one ecosystem. The same threshold principle can be instantiated anywhere the underlying group and signature structure allow it.
For BLS, the appeal is different again. BLS signatures are compact and support useful aggregation properties. Early work proposed threshold and proactive threshold variants built on the BLS or GDH signature structure. More recent work studies adaptive security for threshold BLS, which is especially relevant because unique signatures can be valuable in distributed randomness and asynchronous consensus settings. But the proof landscape is different and sometimes relies on stronger assumptions, so “better” depends on what property you care about: compatibility, proof assumptions, compactness, rounds, or aggregation.
What security and operational problems remain after adopting TSS?
It is worth being precise about the limits.
TSS does not make key management disappear. It redistributes it. You still need secure endpoints, authenticated communication, participant coordination, recovery procedures, software updates, and policies for what happens when one participant is compromised or unavailable. In fact, because the system is interactive, TSS often increases operational complexity even as it reduces single-key risk.
TSS also does not automatically provide robustness, fairness, or anonymity among participants. Some protocols reveal which parties took part to the coordinator. Some can identify cheaters on abort; others cannot. Some tolerate only static corruptions in their proofs, meaning the security argument assumes the adversary chooses whom to corrupt ahead of time. Others aim for adaptive security, where corruptions can happen during execution, but these often need stronger assumptions or more elaborate setup.
And TSS does not exempt you from the underlying signature scheme’s assumptions. FROST is not post-quantum because Schnorr over elliptic curves is not post-quantum. Threshold ECDSA inherits the complexity and assumptions of ECDSA plus whatever additional assumptions its MPC subprotocols require, such as Paillier-related hardness assumptions and the soundness of associated zero-knowledge proofs.
Conclusion
A Threshold Signature Scheme lets a group act like one signer without ever concentrating the full private key in one place. That is the simple statement. The deeper truth is that TSS moves security from a single secret into a controlled collaboration: enough shares can authorize, too few cannot, and outsiders still verify an ordinary signature.
The enduring idea to remember is this: TSS changes the location of trust, not the meaning of a signature. That is why it is powerful. It lets existing signature ecosystems keep their public interfaces while replacing single-point key custody with distributed control. But that power comes with discipline; in setup, protocol choice, networking, nonce handling, preprocessing, and implementation. When those pieces hold together, TSS turns “one key, one failure” into something much harder to break.
What should you understand before using a Threshold Signature Scheme (TSS)?
Before relying on a Threshold Signature Scheme for custody or settlement, confirm the protocol and operational safeguards you depend on and how Cube Exchange participates in the flow. Cube’s settlement workflow interoperates with standard on-chain signatures while you retain control over funding, transfers, and confirmations within the Cube transfer flow.
- Confirm threshold parameters and setup provenance: verify the exact t-of-n (e.g., 2-of-3), who holds shares (user, Cube, Guardian), and that setup used distributed key generation (DKG) with verifiable shares or published DKG proofs.
- Verify the signature family and preprocessing policy: check whether the system uses ECDSA, Schnorr, or BLS and whether it relies on presignatures; if presignatures are used, confirm they are single-use and how they are stored/wiped.
- Check audits and implementation details: review third-party security audits, release notes, and test vectors for range checks, correct share identifiers, and protections against nonce-bias or MtA failures.
- Exercise the flow with a small transfer on Cube: fund your Cube account with a small amount, open the withdrawal/settlement flow to the desired address, choose the correct network and fee option, and wait for the chain-specific confirmation threshold before moving larger sums.
Frequently Asked Questions
Unlike multisig, which exposes that multiple parties signed (often via multiple signatures or a script), a threshold signature produces a single ordinary signature under one public key so verifiers see no special multisig structure and typically cannot tell which subset of parties participated.
If a trusted dealer ever creates the full private key and hands out shares, that single moment defeats the decentralization goal; distributed key generation (DKG) lets parties jointly create the public key and secret shares so no participant ever learns the whole private key during setup.
Schnorr signatures compose linearly so shares and nonces combine neatly across parties, whereas ECDSA involves multiplicative terms and inverses that do not decompose under simple additive sharing; making threshold ECDSA practical therefore requires extra subprotocols (e.g., MtA, Paillier-based steps or share-conversion) to compute products and inverses without revealing secrets.
Preprocessing (presignatures) moves expensive, message-independent work offline to make the online signing round faster, but those offline artifacts are sensitive: if they are leaked, reused, or not properly wiped they can enable signing without the long‑term private key, so they must be stored and managed with key‑level care.
TSS shifts the single-point-of-failure model: an attacker must compromise enough shares to meet the threshold rather than a single device, but that guarantee only holds if the protocol never reconstructs the full key and the setup (e.g., DKG) and implementation are correct.
Not automatically; many protocols provide security with abort (an attacker can disrupt signing) and some offer identifiable abort so honest parties can name the misbehaving participant, but few basic schemes guarantee liveness/robustness (i.e., completion despite misbehavior) without extra mechanisms or wrappers.
No - real-world threshold implementations have been broken by subtle implementation mistakes and missing checks; public audits and disclosures (Trail of Bits, TSSHOCK) show issues like ambiguous encoding, missing range checks, or incorrect share-ID handling that can leak secrets or enable key extraction.
Yes - from the verifier’s perspective the output is generally an ordinary signature under a single public key, so blockchains and other systems accept it without changes and typically cannot distinguish TSS-produced signatures from single-signer signatures.
No - TSS reduces single-key custody but does not remove operational requirements: you still need secure endpoints, authenticated and reliable transport, policies for resharing and recovery, and careful nonce and presignature handling; popular libraries (e.g., tss-lib) intentionally leave transport and lifecycle details to integrators.
Related reading