What is a Digital Signature?
Learn what digital signatures are, how private/public keys enable signing and verification, what security they provide, and where their limits matter.
Introduction
Digital signatures are the cryptographic mechanism that lets a piece of digital data carry proof of authorization. That sounds simple, but it solves a deep problem: digital information is easy to copy perfectly, easy to alter invisibly, and has no natural equivalent of ink, handwriting, or a wax seal. If Alice sends Bob a message saying “transfer these funds” or “install this software,” Bob needs a way to tell whether Alice really approved that exact message.
A digital signature exists to answer that question. In the standard security definition, it is the result of a cryptographic transformation of data that, when properly implemented, provides a way to verify origin authentication, data integrity, and signer non-repudiation. In plainer language, it is evidence that a specific private key approved specific data, and that the data has not changed since the signature was made.
The important word there is specific. A digital signature is not a general aura of trust attached to a person, file, or account. It is tied to a particular message. If the message changes, even slightly, the signature should no longer verify. That tight binding between approval and exact contents is what makes signatures so useful in cryptography and so central to blockchains.
Why do we need digital signatures?
Suppose you receive a digital instruction: “send 5 tokens to this address.” Without a signature, anyone who can inject or alter messages might forge that instruction. Even if the message came from the right network connection, that still would not prove the sender actually authorized it. Networks can be spoofed, machines can be compromised, and files can be copied.
A signature solves this by separating two roles that physical signatures blur together. There is a secret signing capability, held only by the signer, and a public verification capability, available to everyone who needs to check signatures. The signer uses a private key to produce a signature. Anyone with the corresponding public key can test whether that signature is valid for that message.
This asymmetry is the key idea. If verification required the same secret used to sign, you could not let others check your signature without also giving them the power to forge one. Public-key cryptography breaks that symmetry: verify broadly, sign narrowly.
That is why signatures are everywhere in modern systems. A blockchain validator checks whether a transaction was authorized by the owner of an account. An operating system checks whether a software update came from the claimed publisher. A secure protocol checks whether a handshake transcript was approved by the private key tied to a certificate. In all of these, the signature is not hiding the message. It is proving something about the message.
How do private and public keys create and verify a digital signature?
At the most abstract level, a digital signature scheme has three algorithms. KeyGen creates a key pair: a private key and a matching public key. Sign takes a private key and a message and outputs a signature. Verify takes a public key, a message, and a signature, and returns either valid or invalid.
If the scheme is working properly, two things should be true. First, valid signatures created by the owner of the private key should verify successfully under the matching public key. Second, without the private key, it should be computationally infeasible to create a new valid signature on a message you were not authorized to sign.
That second property is the real security claim. Cryptography rarely says “impossible”; it says “so hard that no practical attacker can do it with feasible resources.” The exact meaning depends on the algorithm, key size, and assumptions behind it. NIST’s current Digital Signature Standard approves RSA, ECDSA, and EdDSA for federal use, with the older DSA retained only for verifying legacy signatures generated earlier.
The familiar public/private key language can make signatures sound more magical than they are. Here is the mechanism in ordinary terms: the private key gives you a way to produce a mathematical object that fits the message and public key together in a pattern only someone with the private key should be able to create. Verification checks that pattern. Different algorithms realize that pattern differently, but the logic stays the same.
Why do systems hash a message before signing it?
In practice, digital signatures are usually hash-then-sign. NIST explicitly describes a common signature operation as applying a hash function first and then a digital signature function. This is not a detail bolted on for efficiency alone; it is part of how modern signature systems are designed.
A cryptographic hash function takes an arbitrarily long message and compresses it into a fixed-size digest. If the hash function is secure, it should be hard to find two different messages with the same digest, and hard to reverse the digest back into the original message. When signing, the system usually hashes the message and signs the digest rather than the raw message bytes.
Why do this? The first reason is efficiency. Signature algorithms operate most naturally on fixed-size inputs, while messages can be tiny or enormous. Hashing reduces the input to a manageable size. The second reason is standardization and security engineering: it gives the signature algorithm a regular input format and lets the hash function do the work of condensing the message in a way designed to preserve the binding between “this message” and “this signature.”
But this also creates a dependency. The security of the overall signature process is not just about the signing algorithm. It also depends on the hash function used with it. If the hash function becomes weak against collisions, an attacker may be able to exploit that weakness in some settings. That is why standards are careful about which hash functions are approved with which signature schemes.
How does a wallet sign a blockchain transaction step-by-step?
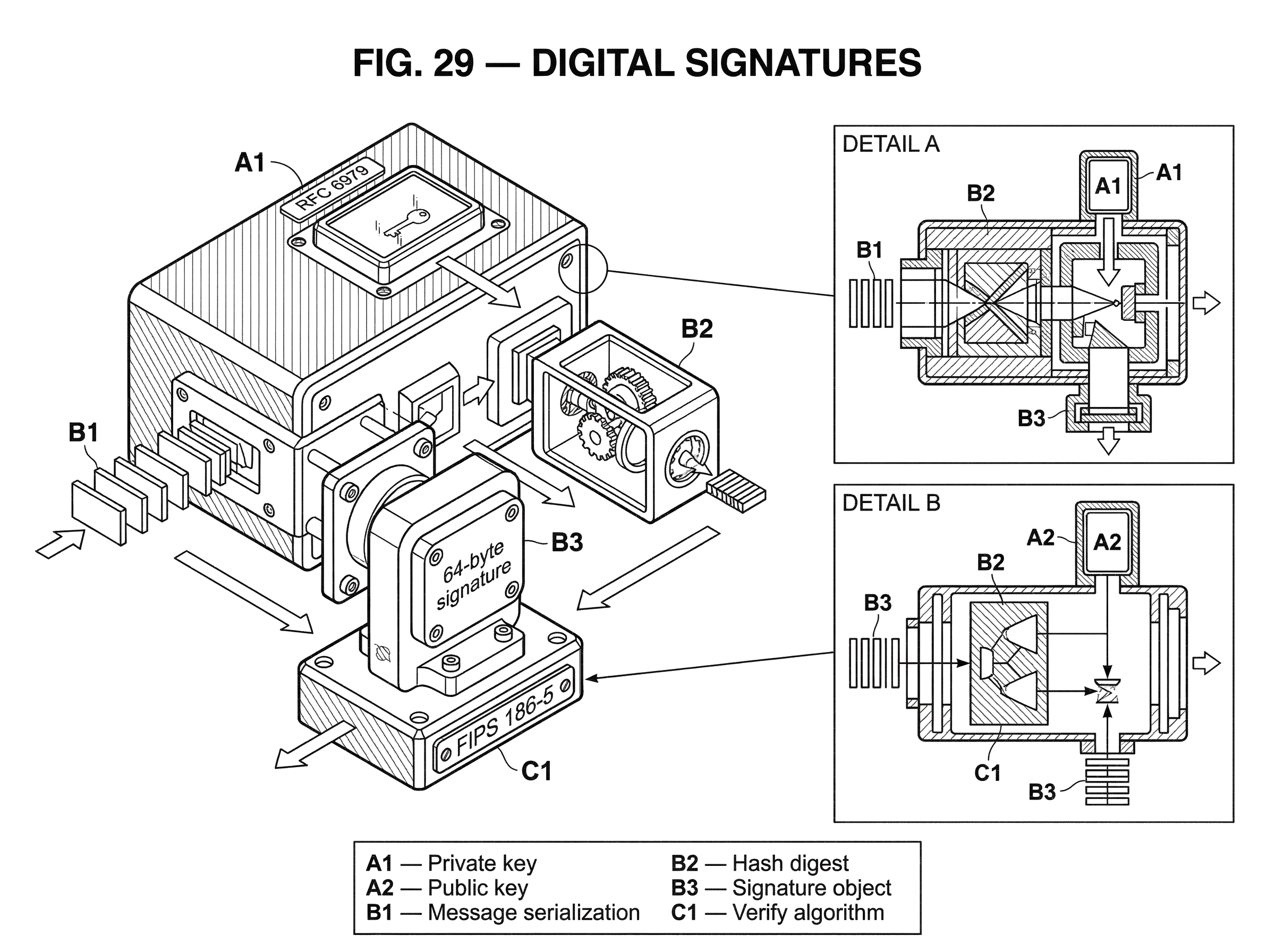
Imagine a wallet preparing a blockchain transaction. The transaction says, in effect, “move these funds from this account to that recipient,” along with other fields the protocol requires. Before broadcasting it, the wallet serializes the transaction into a precise byte sequence. This exact serialization matters, because signatures bind to bytes, not to informal human meaning.
The wallet then hashes that byte sequence. If the transaction bytes change (perhaps because the recipient address changes, the amount changes, or even a field is encoded differently) the hash changes too. Next, the wallet uses the private key to sign that hash, producing a signature object. That signature is attached to the transaction and sent to the network.
A validator or full node receives the transaction, reconstructs the same message bytes according to the protocol rules, hashes them the same way, and verifies the signature using the sender’s public key. If verification succeeds, the node learns that the holder of the corresponding private key approved that exact transaction message. If verification fails, the transaction is rejected.
Notice what the signature did and did not do. It did not encrypt the transaction. Everyone on the network can still read it. It also did not by itself prevent the same signed message from being replayed later in a different context. Those are separate problems, solved by other protocol fields such as nonces, sequence numbers, or recent blockhashes.
That last point is easy to miss, so it is worth making concrete. Solana transactions, for example, include Ed25519 signatures and also include a recent blockhash; that blockhash gives the transaction a limited validity window. The signature proves authorization, while the recent blockhash helps the protocol reject stale replays. Those are different mechanisms doing different jobs.
What guarantees do digital signatures provide (and what they don't)?
| Property | What it proves | Limitations |
|---|---|---|
| Authenticity | Signer possessed private key | Depends on public-key identity binding |
| Integrity | Message unchanged since signing | Depends on exact bytes signed and hashing |
| Non-repudiation | Evidence signer created signature | Depends on key management and policy |
A good digital signature scheme is trying to preserve three linked properties.
The first is authenticity of origin. More precisely, it shows that the signer possessed the private key corresponding to the public key used in verification. Whether that means “this exact human being signed it” depends on how confidently the public key is bound to that identity. In a blockchain wallet, the binding is often simply “whoever controls this account key.” In a certificate-based system, there may be a richer identity story around that key.
The second is integrity. Because the signature is tied to the message, changing the message should invalidate the signature. This is why signatures are such an effective defense against tampering. If an attacker alters the message after it is signed, verification should fail.
The third is non-repudiation, but this is the property most often overstated. Cryptography can show that a valid signature was produced by someone with the private key. It does not, by itself, prove everything people casually mean by “the signer cannot deny it.” NIST is careful here: stronger non-repudiation claims depend on proper implementation and supporting infrastructure and policy. If keys are shared, stolen, or badly managed, the social and legal force of “you signed this” becomes more complicated than the mathematics alone.
This narrower view is healthier. The primitive gives a key-based proof. Broader claims depend on how keys are generated, stored, certified, and controlled.
What can’t digital signatures protect you from?
A common misunderstanding is to treat signatures as a general-purpose security blanket. They are not. NIST explicitly notes that digital signatures provide authenticity, integrity, and non-repudiation support, but not confidentiality and not replay-attack protection.
No confidentiality means that signing a message does not hide it. If you need secrecy, you need encryption as well. A signed email can still be readable by anyone who intercepts it. A signed blockchain transaction is normally public by design.
No replay protection means that if an attacker captures a valid signed message, the signature itself does not stop them from resending that same message later. To prevent that, systems add context that makes a message usable only once or only within a narrow window: counters, nonces, timestamps, recent blockhashes, chain IDs, domain separators, and similar fields.
There is also a subtler limit: a signature only says something about the exact message the protocol defines. If a system signs the wrong bytes, omits context, or allows ambiguous encodings, the signature may be valid but attached to something different from what users thought they were approving. Many real-world failures happen there; not because signature math failed, but because the signed message format was underspecified or misleading.
How do message format and domain separation affect signature security?
Once you see that signatures bind to exact bytes, message design becomes part of security. Two messages that look the same to a human may serialize differently. Worse, two different protocols might accidentally interpret the same bytes in different ways. If the same key can sign in both contexts, a signature meant for one domain might be replayed or misapplied in another.
That is why mature protocols include explicit context inside the signed data. A blockchain transaction often signs not just the payment instruction but also the chain identity, account nonce, fee parameters, and other fields that pin down where and how the authorization is meant to apply. In more specialized systems, domain separation tags serve a similar role by making sure the same primitive used in different places does not accidentally accept the same signed object as valid in both.
This concern appears especially clearly in newer schemes built on elliptic curves and pairings. BLS signatures, for example, rely on hashing messages into curve points using standardized hash-to-curve methods, and those methods require domain separation tags. The goal is not ornamentation. The goal is to make “signing in protocol A” cryptographically distinct from “signing in protocol B,” even if the visible message text is similar.
RSA vs ECDSA vs EdDSA: how signature schemes differ in trade-offs
| Key type | Key size | Per-signature risk | Performance | Best for |
|---|---|---|---|---|
| RSA | Large keys (≥2048 bits) | Low per-signature risk | Slower, larger signatures | Legacy systems, compatibility |
| ECDSA | Small keys (elliptic curves) | Requires fresh per-signature k | Fast, compact signatures | Cryptocurrencies, established ecosystems |
| EdDSA | Small keys (Ed25519/Ed448) | Deterministic signing removes k risk | High performance, small signatures | New chains, constrained devices |
The basic job of a signature scheme is constant, but the engineering tradeoffs differ.
RSA signatures are built from arithmetic modulo a large composite integer. They have long been widely deployed and are still approved in modern standards, but they tend to use larger key sizes than elliptic-curve systems for comparable classical security.
ECDSA uses elliptic-curve groups and became the dominant signature system across much of cryptocurrency infrastructure. Bitcoin and Ethereum rely on ECDSA-based signing. Its appeal is that elliptic curves give strong security with much smaller keys and signatures than RSA. But ECDSA has a delicate operational requirement: each signature needs a fresh per-message secret value, commonly called k. If k is reused or generated badly, the private key can be exposed.
That requirement is not theoretical trivia. It is one of the most famous failure modes in practical signature systems. RFC 6979 was created to address exactly this issue for DSA and ECDSA by deriving k deterministically from the private key and the message hash instead of drawing fresh randomness each time. The verifier does not need to change; only the signer’s internal method changes. The point is to remove a dangerous dependence on high-quality randomness at signing time.
EdDSA, including Ed25519 and Ed448, pushes further in that direction. RFC 8032 specifies EdDSA as a deterministic signature scheme, and NIST now approves EdDSA, including HashEdDSA, in FIPS 186-5. Deterministic signing reduces one major class of implementation failure: bad per-signature randomness. EdDSA is also known for high performance, small keys and signatures, and implementation choices that can improve robustness against some side-channel problems.
That helps explain why different blockchains choose different signature schemes. Solana uses Ed25519 signatures in transactions, with each signer contributing a 64-byte signature. Bitcoin and Ethereum historically used ECDSA because those ecosystems were designed around secp256k1 long before Ed25519 became the default choice in many newer systems.
What extra checks are needed beyond signature verification?
A smart beginner might think verification is just “plug the message, signature, and public key into the formula.” In real systems, that is not enough.
Standards require additional assurances before treating a verified signature as meaningful. NIST’s Digital Signature Standard says the verifier should have assurance of the signer’s claimed identity, the validity of domain parameters for elliptic-curve schemes, the validity of the public key, and assurance that the signer possessed the private key at signing time. The exact operational procedures are left to supporting guidance, but the principle is clear: a mathematically valid signature is only part of validation.
Elliptic-curve systems make this especially concrete. Public keys live on mathematical groups with structural rules, and implementations need to check that a supplied public key is actually a valid group element of the right form. SEC 1 emphasizes that conformant implementations must perform the specified cryptographic checks because they prevent subtle attacks. Skipping public-key validation can open the door to invalid-curve or subgroup attacks.
The same lesson appears in BLS-based systems. The current CFRG BLS specification requires public-key validation and subgroup checks, and warns that skipping them can enable forgeries or unpredictable pairing behavior. Ethereum’s consensus specifications and proposed BLS12-381 precompiles carry the same theme: aggregation is powerful, but only if the implementation is strict about validation.
How do aggregated signatures (like BLS) work and what risks do they add?
| Aspect | Single signature | Aggregated (BLS) |
|---|---|---|
| Size | One signature per signer | One compact aggregated signature |
| Verification cost | Verify each signature separately | Verify many signers with few pairings |
| Complexity | Simple signing and checks | Requires hash-to-curve, PoP, subgroup checks |
| When useful | Few signers or simple flows | Many signers, consensus or mass attestations |
Most people first meet signatures in the simple form: one signer, one message, one signature. But some signature schemes support richer structure.
BLS signatures are the clearest example. They are pairing-based signatures with a striking property: multiple signatures can be aggregated into a single compact signature. Given several signatures, anyone can combine them into one object that still authenticates the underlying set of messages and public keys. This is why BLS attracts so much interest in blockchains: it can reduce bandwidth and storage when many parties need to attest to something.
That power is not free. BLS requires careful handling of message hashing to curve points, domain separation, subgroup checks, and defenses against rogue-key attacks. In proof-of-possession variants, participants must first prove they actually hold the private key for their advertised public key before certain fast aggregate-verification shortcuts are safe. The mechanism is more complex because the capability is richer.
This is a good example of a larger truth: a signature scheme is never just “math that verifies.” It is a package of algebra, encodings, hash conventions, key validation rules, and protocol assumptions. If any of those pieces are mishandled, the whole construction can fail even when the core equation is correct.
What common failures make signatures insecure in practice?
The easiest failures to understand are key theft and key misuse. If an attacker gets the private key, they can produce valid signatures. From the verifier’s perspective, those signatures look legitimate, because cryptographically they are. This is why secure key generation, storage, and access control matter as much as the signature algorithm itself.
A second class of failures comes from bad randomness or side channels. ECDSA is the classic warning: weak or repeated k values can reveal the private key. Deterministic variants reduce that specific risk, but they do not eliminate the need for secure key generation or careful implementation. RFC 6979 is explicit on this point.
A third class comes from malleability and encoding ambiguity. Bitcoin historically faced transaction malleability issues partly because the signatures authorizing a transaction did not provide integrity for the signature data itself in the way users might assume. That allowed third parties to modify a transaction representation without invalidating the underlying authorization, changing its transaction identifier and confusing software that tracked payments by ID. The broader lesson is that a valid signature does not automatically imply a unique, immutable outer representation unless the protocol is designed to enforce that.
A fourth class comes from changing threat models. NIST notes that the approved classical signature algorithms in FIPS 186-5 are not expected to resist attacks from a large-scale quantum computer. That does not mean they are broken today. It means their security assumptions are classical, not post-quantum. The mathematics that protects them is tied to problems like integer factorization or discrete logarithms, and large quantum computers would change that landscape.
How do blockchains use digital signatures in transactions and consensus?
Blockchains make the role of signatures unusually visible because authorization is public, explicit, and machine-checked.
In a typical account-based chain, a transaction is a signed instruction from an account holder. The network verifies the signature against the account’s public key, checks replay-prevention fields such as a nonce, and then executes the state change if everything is valid. In UTXO-style systems, signatures authorize spending particular outputs under specified locking rules.
The details vary by chain, but the logic is stable. Ethereum and Bitcoin built around ECDSA. Solana uses Ed25519, with each signer contributing a 64-byte signature and the transaction carrying a recent blockhash as part of the signed payload. Ethereum’s consensus layer uses BLS signatures for validator attestations because aggregation helps compress many validators’ approvals into less data.
These are not arbitrary choices. They reflect different pressures. User transactions care about compatibility, hardware support, existing ecosystems, and message size. Consensus systems often care about verifying many attestations efficiently. That is why the same broad idea (a digital signature) appears in several algorithmic forms across the blockchain stack.
Conclusion
A digital signature is best understood as a cryptographic proof of approval for exact data. The private key creates that proof; the public key lets others verify it. From that mechanism come the core guarantees of authenticity and integrity, and sometimes a stronger practical form of non-repudiation when the surrounding key-management system is sound.
The main thing to remember tomorrow is this: **a digital signature does not mean “this data is safe in every sense.” It means “someone controlling this private key approved this exact message.”
** Everything else depends on the rest of the system built around that core idea.
- secrecy
- replay protection
- identity binding
- aggregation safety
- resistance to implementation bugs
- future quantum resilience
What should you understand about digital signatures before transferring crypto?
Understand the concrete implications of digital signatures before moving funds: signatures prove who approved specific bytes, but they don’t hide data or automatically prevent replay. Use Cube Exchange to fund, trade, or withdraw while you confirm the chain- and asset-specific signing details that affect safety and recoverability.
- Check the chain’s signing and replay protections (for example, whether it uses ECDSA on secp256k1, Ed25519, BLS, a nonce, or a recent blockhash) and note any Confirmations or finality guidance.
- Verify the recipient address format, checksum, and any required memo/tag or chain ID by copying and validating the whole string before pasting it into Cube’s transfer form.
- Fund your Cube account with fiat or a supported crypto deposit so you have the asset available to send or trade.
- In Cube’s transfer/withdraw flow, select the exact network that matches the recipient address, confirm any memo/tag and the on-chain confirmation threshold shown, then submit the transfer.
Frequently Asked Questions
Signing proves who approved a specific message and that it wasn’t changed, but it does not hide the message contents - signatures do not provide confidentiality, so anyone who can read the message can read a signed message unless you also encrypt it.
Modern practice is hash-then-sign: the message is hashed to a fixed-size digest for efficiency and standardized inputs, but this makes the overall security rely also on the hash function - if the hash becomes weak to collisions an attacker may exploit that weakness.
A digital signature by itself does not prevent replay; to stop captured signed messages being resent, systems add context such as nonces, sequence numbers, timestamps, chain IDs, or recent blockhashes so a signed message is valid only once or only within a narrow window.
Non-repudiation in cryptography means a valid signature was produced by someone holding the private key, but stronger legal or practical non-repudiation claims depend on how keys are generated, stored, certified, and controlled - if keys are shared or stolen the social/legal force of “you signed this” is more complicated.
Elliptic-curve and pairing-based systems require extra checks beyond the core equation: verifiers must validate that public keys are valid group elements and perform subgroup checks because skipping those checks enables invalid-curve or subgroup attacks and can lead to forgeries or unpredictable pairing behaviour.
Deterministic signing (RFC 6979 for ECDSA/DSA and EdDSA per RFC 8032) removes the dangerous reliance on per-signature randomness and so mitigates one common failure mode, but it does not remove the need for secure randomness at key generation, can change some protocol properties, and does not eliminate side-channel risks.
Aggregation (e.g., BLS) can compress many signatures into one, saving bandwidth, but it requires careful hash-to-curve methods, domain separation, subgroup checks, and protections (such as proof-of-possession) to avoid rogue-key and other aggregation-specific attacks.
NIST and related standards warn that currently approved classical signature algorithms (RSA, ECDSA, EdDSA) are not expected to resist attacks from a large-scale quantum computer, so their long-term security assumptions are classical rather than post-quantum.
Related reading