What Are Schnorr Signatures?
Learn what Schnorr signatures are, how they work, why their linearity matters, and how BIP-340 uses them for compact, secure signatures.
Introduction
Schnorr signatures are a digital signature scheme built around a simple idea: prove knowledge of a secret key in a way that anyone can verify, without revealing the secret itself. They matter because they combine three properties that rarely line up so neatly: a compact signature format, a comparatively clean security story, and an algebraic structure that makes advanced constructions like key aggregation and multisignatures much easier than with older schemes.
That last property is the one that makes Schnorr signatures feel different. Many signature systems let one person sign one message with one key. Schnorr does that too, but its equations are linear in a useful way. Because of that, multiple parties can often cooperate to produce a single signature that verifies like an ordinary one. In practice, this is why Schnorr signatures became central to designs such as Bitcoin’s Taproot, where compactness, privacy, and efficient verification all matter at once.
To see why Schnorr works, it helps to start with the problem a signature scheme is solving. A signer has a secret key and publishes a corresponding public key. Later, they want to attach a short piece of data to a message so that anyone can check two things: the message really came from someone who knows the secret key, and the signature cannot be copied onto a different message. Schnorr solves this by turning an interactive proof of knowledge into a non-interactive signature using a hash function. The mechanism is simple enough to explain from first principles, but precise enough that tiny implementation mistakes (especially around nonce generation) can completely break security.
How does a Schnorr signature prove knowledge of a secret key?
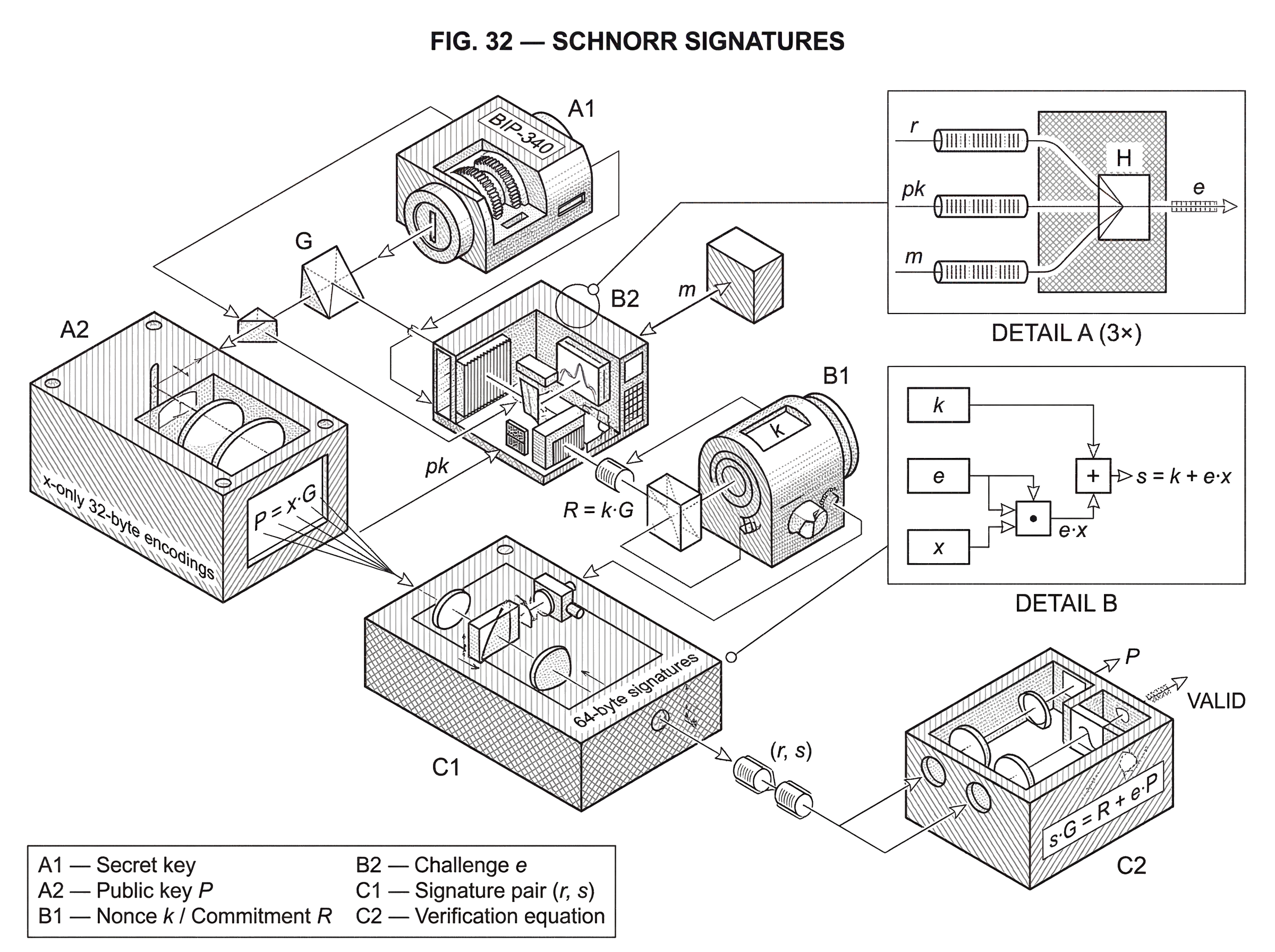
At its heart, a Schnorr signature lives in a group where discrete logarithms are believed to be hard. In modern deployments this group is usually an elliptic-curve group, such as the secp256k1 curve used by Bitcoin’s BIP-340. The setup begins with a generator point G. A secret key is an integer x, and the corresponding public key is P = x*G. Computing P from x is easy. Recovering x from P is assumed to be hard.
The challenge is to prove knowledge of x without revealing it. The mechanism starts with a fresh random secret called a nonce, written as k. From k, the signer computes a public commitment R = k*G. You can think of R as a temporary public footprint of a secret the signer knows only for this message. If the signer now revealed k, anyone could check that R was honestly formed. But revealing k would not prove anything about the long-term secret key x.
So Schnorr mixes the long-term secret and the fresh nonce together. A challenge value e is computed by hashing the commitment, the public key, and the message. In modern BIP-340 form, this is effectively e = H(r || pk || m) with domain separation through a tagged hash, where r is the encoded x-coordinate of R, pk is the encoded public key, and m is the message. The signer then responds with s = k + e*x modulo the group order.
Verification checks a single equation: sG = R + eP. This works because substituting the signer’s construction gives (k + ex)G = kG + e(xG) = R + eP. That is the whole mechanism. The signer demonstrates knowledge of a value s that ties together a fresh nonce and the secret key in exactly the way the public equation demands.
The compression point is this: a Schnorr signature is convincing because the verifier can check a linear relation in public points that could only have been assembled correctly by someone who knew the secret scalar hidden inside the public key.
Everything else exists to make that relation non-malleable, non-replayable, and unambiguous.
- the hash
- the nonce rules
- the encoding conventions
Why does hashing (Fiat–Shamir) convert Schnorr’s interactive proof into a non‑interactive signature?
The equation above may look almost too simple. If the signer can choose R and s, what stops them from making up values that satisfy the equation without knowing x? The answer is the challenge e.
In the original identification setting behind Schnorr, a verifier would send a random challenge after seeing the commitment R. The signer could answer correctly only if they knew the secret key. A signature scheme needs to remove the live verifier and replace that challenge with something anyone can recompute later. The standard move is the Fiat-Shamir transform: compute the challenge by hashing the transcript so far. In Schnorr, that means the challenge depends on the commitment and the message, and in modern designs often also the public key.
This matters because it stops the signer from choosing the response first and then adapting the challenge afterward. The hash function acts like a public, unpredictable challenge generator. The signer commits to R, the message is fixed, the public key is fixed, and the hash binds them together into e. Only then does the response s make sense.
This is also why the exact hash inputs matter. BIP-340 specifies tagged hashes for domain separation and uses key prefixing in the challenge computation. The verification condition is written as sG = R + tagged_hash(r || pk || m)P, with exact byte-level rules for lifting x-coordinates to points, checking parity, and rejecting out-of-range values. Those details are not cosmetic. They ensure that every correct implementation interprets the same bytes as the same mathematical objects, which is essential in consensus systems where two verifiers cannot be allowed to disagree.
Step-by-step example: signing a message with Schnorr (the 'pay Bob' walkthrough)
Suppose Alice has secret key x and public key P = x*G. She wants to sign the message “pay Bob.” She first derives a fresh nonce secret k and computes R = k*G. At this point, R is just a commitment: it says, in effect, “I know some temporary secret tied to this signature attempt.”
Next, Alice hashes together the encoded form of R, her public key, and the message. That produces the challenge e. The important point is not just that e is a number. It is a number that nobody, including Alice, gets to choose freely once R, P, and the message are fixed. The hash pins the signature attempt to this exact context.
Alice then computes s = k + e*x. She sends the signature, which in modern Schnorr form is typically the pair (r, s), where r is an encoding of R and s is the scalar response. A verifier reconstructs the challenge from the same public inputs and checks whether s*G equals R + e*P. If Alice knew x, the equality holds automatically. If she did not, then producing s after the challenge is fixed would require solving the discrete-log-style problem the scheme relies on.
Notice what is doing the real work. The nonce contributes freshness. The hash contributes binding to the message and context. The public-key term e*P forces the response to reflect knowledge of the secret behind P. Remove any one of those pieces, and the mechanism stops being a signature in the strong sense people need.
What does BIP-340 change about Schnorr on Bitcoin?
The original Schnorr paper described the scheme in a finite-field setting. Modern cryptocurrency systems typically use elliptic curves instead, because they provide the same kind of hardness with much smaller keys and signatures. Bitcoin’s standard Schnorr construction is BIP-340, which specifies 64-byte signatures over secp256k1.
BIP-340 makes several design choices that are worth understanding because they show the difference between “the Schnorr idea” and “a standardized Schnorr signature format.” Public keys are x-only 32-byte encodings. Instead of encoding the full elliptic-curve point, the scheme takes the x-coordinate of the point whose y-coordinate is even. The nonce point R is handled similarly. This removes one bit of redundancy while keeping the representation canonical.
The signature itself is the pair (r, s), where r is the x-coordinate of the nonce point R and s is the scalar response. Verification conceptually reconstructs R from the equation R = sG - eP, then checks that R is not the point at infinity, has even y, and has x-coordinate equal to r. BIP-340 defines these checks exactly, including lift_x for recovering the unique even-y point from an x-coordinate when it exists.
The result is a compact, fixed-size signature format with very little ambiguity. That is a practical advantage over ECDSA, whose DER encodings are more awkward and whose algebra is less cooperative for higher-level protocols.
Schnorr vs ECDSA: what advantages does Schnorr offer?
| Aspect | Schnorr | ECDSA |
|---|---|---|
| Algebra | Linear, single public equation | Nonlinear, inverse-heavy relations |
| Security proofs | Cleaner SUF-CMA in ROM | Historically more intricate analyses |
| Composability | Native key/signature aggregation | Aggregation possible but complex |
| Signature encoding | Fixed-size, x-only-friendly | Variable-size DER encodings |
| Implementation | Easier to reason about | More fragile to subtle bugs |
| Best for | Protocol composition and multisig | Legacy support and existing stacks |
Schnorr and ECDSA can both be built on the same elliptic curve, and both are signature schemes based on the hardness of discrete logarithms. So why did Schnorr become such an important upgrade in systems that already had ECDSA?
The first reason is conceptual cleanliness. The verification equation in Schnorr is direct and linear. In ECDSA, the verifier works through modular inverses and a more intricate relation between signature components. That does not make ECDSA insecure by default, but it makes the scheme harder to reason about and less convenient to compose into larger protocols.
The second reason is provable security. BIP-340 explicitly notes that Schnorr signatures are provably secure; more precisely, strongly unforgeable under chosen-message attack in the random oracle model, under the hardness of the elliptic-curve discrete logarithm problem. That statement should not be overstated: the proofs live in a model, and later research shows limits on how tight generic reductions can be. But compared with the historical security analysis of ECDSA, Schnorr has long been viewed as the cleaner and more analyzable design.
The third reason is the one practitioners care about most: linearity. Because the response has the form s = k + e*x, signatures and public keys combine naturally. That is the mechanism that enables compact multisignatures, threshold constructions, and related protocols. With ECDSA, similar goals are possible, but the protocols are typically more complicated and fragile.
How does Schnorr linearity enable key aggregation and compact multisignatures?
| Option | Rounds | On-chain footprint | Concurrency security | Nonce requirement |
|---|---|---|---|---|
| Single-signer | 1 | 1 signature | N/A | Single fresh nonce |
| Simple additive aggregation | 1–2 | 1 aggregate signature | Broken under concurrent attacks | Deterministic nonces unsafe |
| MuSig2 (two-round) | 2 | 1 aggregate signature | Secure under concurrent sessions | High-quality randomness; no reuse |
| Provable large-scale (mBCJ) | 2 | 1 aggregate signature | Provable ROM security for many signers | Random nonces; protocol-specific rules |
To see why linearity matters, imagine two signers with secret keys x1 and x2 and public keys P1 = x1*G and P2 = x2*G. If they form an aggregate public key P = P1 + P2, then a signature under the corresponding aggregate secret x = x1 + x2 would satisfy the usual Schnorr equation. The remarkable part is that the parties do not need to reveal or even explicitly combine their secret keys to produce such a signature.
Each signer can choose a nonce, publish the corresponding nonce point, and later contribute a partial response of the form “my nonce plus the challenge times my secret share.” Adding those responses gives a final s that verifies against the sum of public keys. This is not an accidental trick layered on top of Schnorr. It follows directly from the linear structure of the signing equation.
That property has real consequences on chain. In a Taproot key-path spend, a cooperative spending condition can often appear on chain as a single public key and a single Schnorr signature. The verifier just sees an ordinary BIP-340 signature. The internal coordination among participants is hidden. This improves space efficiency and, when used appropriately, privacy.
The same structure shows up beyond Bitcoin. Schnorr-style multisignature and threshold designs are attractive wherever systems want many participants to authorize the same message without publishing many separate signatures. But here an important boundary appears: the basic single-signer Schnorr equation is simple, while secure multiparty Schnorr signing is not automatic. The algebra makes aggregation possible; it does not make every aggregation protocol safe.
Why is nonce generation critical for Schnorr and what happens if it fails?
| Method | When used | Security risk | Recommendation |
|---|---|---|---|
| Fresh random | Standard multisig and single-signer | Low if RNG is strong | Use high-quality RNG; never reuse |
| Deterministic (single-signer) | RFC6979-style single-signer flows | Generally safe for single-signer | OK for single-signer only; add randomness for extra safety |
| Deterministic (multisig) | Naïve reuse across multi-party protocols | Catastrophic key leakage | Avoid entirely for multisig; require randomness |
| Nonce reuse | Accidental or buggy implementations | Immediate private-key recovery | Detect and rotate keys; fix RNG/state |
The most dangerous misunderstanding about Schnorr signatures is to treat the nonce as a mere implementation detail. It is not. The nonce is a secret one-time value, and reusing it can reveal the private key immediately.
The reason is visible from the signing equation. If the same nonce k is used to sign two different messages, the signer produces s1 = k + e1*x and s2 = k + e2*x. Subtracting gives s1 - s2 = (e1 - e2)*x. If e1 ! = e2, then x can be solved directly. This is the classic catastrophic failure mode shared by Schnorr-like schemes.
BIP-340 therefore specifies nonce derivation carefully and recommends that the 32-byte randomness input used in derivation be fresh and unpredictable. It also warns against careless cross-scheme reuse. If the same secret key is used in multiple signing systems with overlapping nonce logic, correlations can leak the key. The specification also standardizes tagged hashes partly to keep contexts separate.
An important subtlety is that deterministic nonces are not universally good or bad; they are context-dependent. For single-signer BIP-340 signatures, carefully specified deterministic derivation with fresh randomness input can be a sensible engineering choice. But BIP-340 explicitly warns that deterministic nonce generation is insecure in general for multisignature signing protocols. The reason is that in interactive protocols, adversaries can manipulate session data and try to force dangerous nonce reuse patterns. That is why MuSig2 and BIP-327 require high-quality randomness and strict state handling instead of simply reusing the single-signer approach.
Even if nonce reuse never occurs, side channels can still leak partial nonce information. Research on ECDSA nonce leakage shows how timing information as small as nonce bit-length can be enough for lattice attacks to recover secret keys. The exact papers often study ECDSA, but the lesson carries over: repeated signatures plus partial nonce leakage is a dangerous combination. Good implementations therefore aim for constant-time arithmetic, fixed control flow where possible, and side-channel-resistant libraries such as libsecp256k1.
Which edge cases do standards like BIP-340 resolve for Schnorr signatures?
Once the core equation is understood, the rest of a standard can look bureaucratic. In reality, those details are where interoperability and consensus safety live.
BIP-340 defines exact byte encodings, integer ranges, parity conventions, the lift_x operation, and verification failure conditions. It also specifies batch verification: when verifying many signatures, a verifier can combine equations using random-looking coefficients and check one larger relation instead of many separate ones. If all signatures are valid, the combined equation holds. If at least one is invalid, batch verification should still fail except with negligible probability.
This is a good example of the difference between mathematical truth and engineering truth. Mathematically, a Schnorr signature is the relation sG = R + eP. Engineering-wise, a signature standard is a complete agreement about encodings, hash domains, accepted points, and failure behavior. Without that, two honest implementations can disagree about whether the same byte string is valid.
Why do multisignatures need extra protocol safeguards despite Schnorr’s aggregation?
Schnorr’s linearity invites a tempting but wrong conclusion: if responses add, then multisignatures must be trivial. The hard part is not the final algebra. The hard part is preventing malicious participants from choosing keys or nonces in ways that let them forge signatures or bias the protocol.
This is why modern Schnorr multisignature protocols such as MuSig2 include more structure than “everyone signs and we add the parts.” They use careful key aggregation, multiple nonce components, hash-derived coefficients, and strict rules against nonce reuse. The literature documents that earlier two-round Schnorr multisignature designs had subtle flaws under concurrent sessions, and later work introduced constructions with stronger proofs and better defenses.
BIP-327 standardizes MuSig2 for BIP-340-compatible multisignatures. It produces ordinary Schnorr signatures under an aggregate key, but it requires genuine randomness for nonce generation and warns that the same secret nonce state must never be reused. This is the right way to think about Schnorr multisignatures: not as a free bonus, but as a powerful capability enabled by Schnorr’s algebra and made safe only through additional protocol design.
How far do formal security proofs for Schnorr signatures actually reach?
It is fair to say that Schnorr signatures have a strong formal foundation. It is not fair to say that every practical question about them is settled.
The standard security claim is that Schnorr signatures are strongly unforgeable under chosen-message attack in the random oracle model assuming discrete logarithms are hard. That is a meaningful and widely respected result. At the same time, later research shows limits on proving such security with tight generic reductions from standard group problems. In plain language, the security story is good, but not infinitely neat. There are boundaries to what existing proof techniques can show.
That does not make Schnorr fragile. It means one should distinguish between three levels of statement. First, the basic mechanism is elegant and well studied. Second, standardized forms like BIP-340 are carefully engineered and deployed. Third, advanced protocols built on top of Schnorr (especially multisignatures and threshold systems) need their own analysis and should not inherit trust automatically just because the base signature equation is simple.
Where are Schnorr signatures deployed and what real systems use them?
In practice, Schnorr signatures are used anywhere people want a compact signature scheme with good algebraic composability. In Bitcoin, BIP-340 Schnorr signatures are part of the Taproot upgrade, where they enable key-path signatures and make aggregation-friendly designs practical. Bitcoin Core integrated BIP340–342 validation ahead of activation, and libsecp256k1 includes optional modules for both BIP-340 Schnorr signatures and BIP-327 MuSig2.
Outside Bitcoin, the broader pattern is similar. Systems that need efficient threshold control, compact authorization, or flexible multi-party signing often prefer Schnorr-style constructions or close relatives. The exact curve, encoding, and protocol may differ, but the attraction is the same: the signing equation is simple enough to compose.
That said, portability is not automatic. BIP-340 explicitly warns that adapting its exact specification to other curves is not straightforward and can produce insecure variants. The high-level Schnorr idea is general. A concrete Schnorr standard is not plug-and-play across every algebraic setting.
Conclusion
A Schnorr signature works because a signer can produce a response s that satisfies the public equation sG = R + eP, where e is a hash-derived challenge tied to the message and context. That is the fundamental mechanism. From it come compact signatures, a clean verification rule, and (most importantly) a linear structure that makes aggregation possible.
The reason Schnorr signatures matter is not just that they are elegant. It is that their elegance survives contact with real systems well enough to support important things: fixed-size standardized signatures, efficient verification, and practical multisignature protocols when designed carefully. The part to remember tomorrow is simple: Schnorr makes signing look like one linear equation, and that equation is why the scheme is both powerful and dangerous to implement carelessly.
What should you understand before using Schnorr signatures?
Understand the practical risks and deployment details of Schnorr before you trade, deposit, or withdraw assets that rely on it. On Cube Exchange, you can fund and move assets while verifying whether the chain, wallet, and destination use BIP-340 (x-only Schnorr) and follow secure nonce and multisig practices.
- Check whether the chain and wallet you plan to use implement BIP-340 (secp256k1 x-only 64-byte signatures) or a compatible Schnorr variant by reading the wallet/service docs or transaction format (e.g., Taproot/Bech32m for Bitcoin).
- Fund your Cube account (fiat on‑ramp or crypto transfer). When withdrawing, paste the exact destination address that matches the expected Schnorr address type (e.g., a Taproot/Bech32m address for BIP-340 key-path spends).
- For custody or multisig setups, choose wallets or services that explicitly support MuSig2 or a vetted multisig standard, and confirm they state use of fresh randomness and vetted libraries such as libsecp256k1.
- Before moving large amounts, review recent security advisories for the wallet/service, confirm the signing implementation advertises side-channel mitigations and proper nonce handling, and send a small test transfer first.
Frequently Asked Questions
Reusing the same secret nonce k for two signatures leaks the secret key because s1 - s2 = (e1 - e2)*x, allowing x to be solved when e1 != e2; BIP-340 therefore treats nonce derivation as a critical part of the spec and recommends fresh unpredictable randomness.
Schnorr’s response formula s = k + e⋅x is linear in the public points, so partial responses from multiple signers can be added to produce a single signature that verifies against the sum of public keys, but secure multisignature protocols must add key-aggregation, nonce handling, and hashing rules to prevent malicious key or nonce choices from enabling forgeries.
BIP-340 standardizes Schnorr for secp256k1 with 64-byte signatures comprising an x-only 32-byte nonce coordinate and a 32-byte scalar s, uses tagged hashes and 'lift_x' semantics (even-y convention) to make encodings canonical, and specifies exact failure checks and batch-verification behavior for interoperability.
Deterministic nonce derivation can be acceptable for single-signer BIP-340 when done carefully, but deterministic nonces are explicitly warned against for multisignature protocols because interactive adversaries can exploit deterministic behavior to force dangerous reuse patterns; therefore MuSig2 and related standards require fresh randomness and strict state handling.
Schnorr enjoys strong provable-security statements in the random-oracle model under the discrete-logarithm assumption, which is cleaner than historical ECDSA analyses, but later research shows limits on tight/generic reductions (security proofs are model-dependent and not infinitely tight).
Beyond nonce reuse, practical pitfalls include side-channel leakage of nonce bits (which can enable lattice attacks), incorrect byte-level encodings or parity checks, and inconsistent handling of invalid inputs - these are why implementations emphasize constant-time code, canonical encodings, test vectors, and vetted libraries like libsecp256k1.
No; BIP-340 warns that adapting its exact specification to other elliptic curves is not straightforward and can produce insecure variants, so the high-level Schnorr idea is portable but concrete standards like BIP-340 must be adapted with care.
Batch verification combines many Schnorr verification equations using random coefficients so one combined relation is checked instead of many, which is efficient and correct when all signatures are valid, but a failing batch can occur with negligible probability and implementations must follow the BIP’s exact rules for randomization and failure behavior.
An adaptor signature is produced by offsetting the signer’s public nonce with a known point T = t⋅G so that learning the adaptor secret t is equivalent to learning a full valid signature, enabling atomic swaps and similar constructions by embedding a secret in a signature-like object.
Related reading