What is Ed25519?
Learn what Ed25519 is, how its deterministic signatures work, why it is fast and practical, and where validation rules matter for security.
Introduction
Ed25519 is a digital signature scheme designed to let someone prove, with a public key, that a message came from the holder of a matching secret key. That sounds like a standard cryptography problem, but Ed25519 became important because it solves it in a way that is unusually friendly to real implementations: it is fast, uses small keys and signatures, and avoids one of the classic failure modes of older signature systems; dependence on fresh randomness for every signature.
That last point is worth pausing on. In many signature schemes, the math is secure only if every signature uses a new secret random value that is never repeated and never biased. If that randomness goes wrong, the private key can leak. Ed25519 was designed so the per-message secret value is derived deterministically from the private key and the message itself. The goal is not to remove all implementation risk (side channels and fault attacks still matter) but to remove a very common and very damaging source of failure.
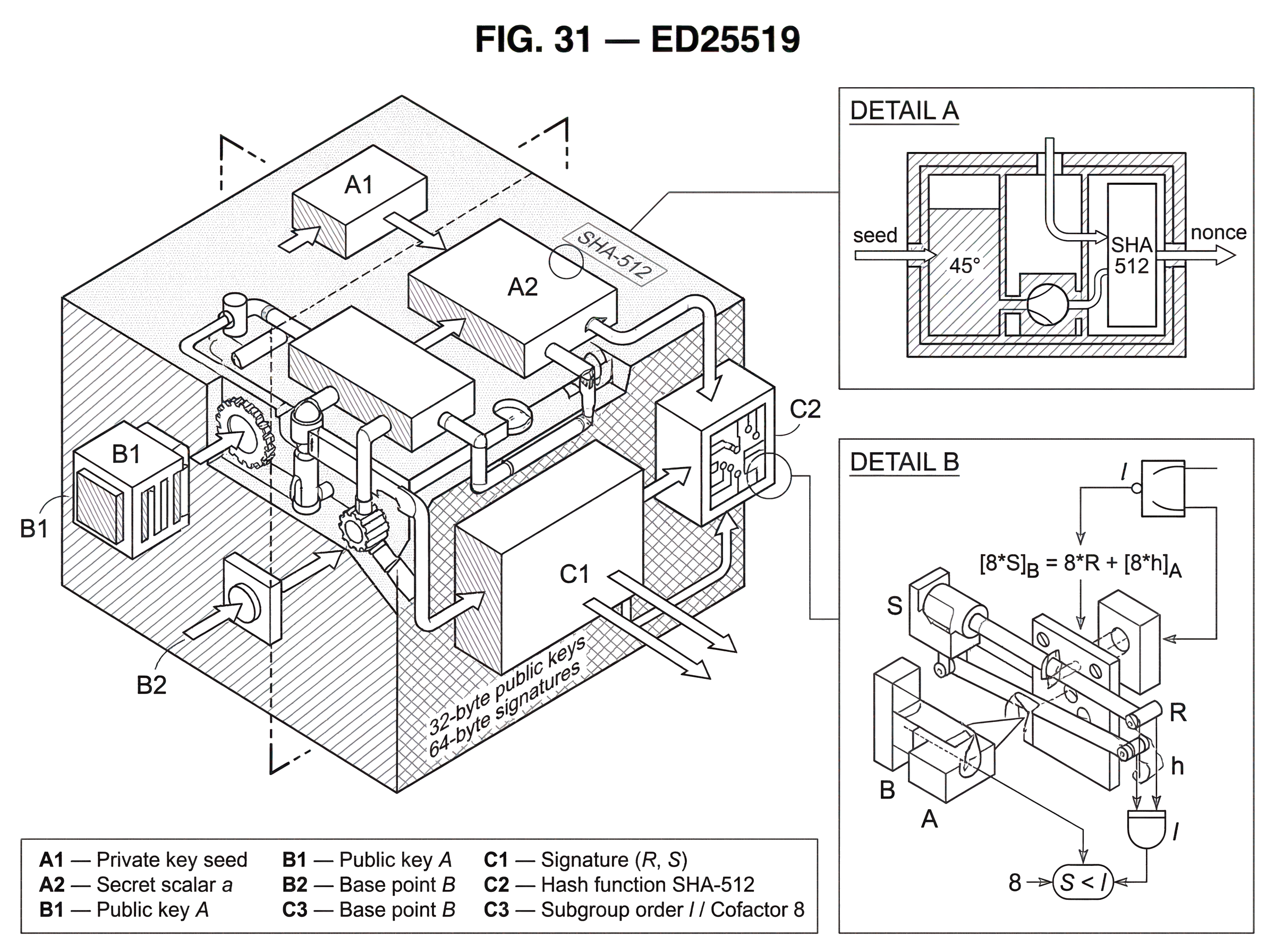
Ed25519 is not a hash function, not an encryption scheme, and not the elliptic curve itself. It is an instance of EdDSA, the Edwards-curve Digital Signature Algorithm, using a particular curve and parameter set intended for roughly 128-bit classical security. In the standard form described in RFC 8032, it uses 32-byte public keys and 64-byte signatures. Those compact sizes, together with good performance, are a large part of why Ed25519 appears in wallets, consensus systems, developer libraries, and network protocols.
The core idea is simple: a signature should convince a verifier that the signer knew a secret scalar tied to the public key, without revealing that scalar. The reason Ed25519 works well in practice is that it does not just have sound algebra. It was engineered so that the algebra matches the reality of software: complete formulas, fixed encodings, deterministic nonce generation, and relatively few sharp edges compared with earlier designs.
What implementation and operational problems does Ed25519 solve?
A digital signature scheme has to do two jobs at once. It must make forgery computationally infeasible, and it must make correct implementation realistic. Many systems succeed more at the first than the second. On paper, an algorithm may be secure under clear assumptions; in deployed code, it may still fail because the implementation mishandles randomness, point validation, edge cases, or serialization.
Ed25519 was designed in response to that gap between theory and deployment. The underlying signature family is Schnorr-style: the signer commits to an ephemeral public value, the message and that commitment determine a challenge, and the response proves knowledge of the secret key. This structure is attractive because it is conceptually clean and efficient. But the particular Ed25519 instantiation goes further by choosing an Edwards curve and formulas that are complete; valid for all curve points, with no exceptional cases in the arithmetic formulas themselves. That matters because exceptional cases are exactly where implementations often become complicated, slow, or wrong.
So the design target was not merely “secure signatures on an elliptic curve.” It was “secure signatures where the normal implementation path is also the safer path.” High performance matters because signatures are verified constantly in real systems. Small encodings matter because signatures are carried in transactions, certificates, and messages. Deterministic signing matters because a bad random number generator should not silently destroy the secret key.
This is why Ed25519 often replaces older choices such as ECDSA in new systems. ECDSA can be secure, and it is widely deployed, but its interface makes nonce generation a critical hazard. Ed25519 keeps the same broad purpose (public-key signatures) while changing the mechanism enough to remove some painful implementation risks.
How does Ed25519 use a temporary commitment (Schnorr-style) to prove possession of a key?
The easiest way to understand Ed25519 is to start from the structure it inherits from Schnorr signatures.
A signer has a secret scalar, which you can think of as a secret number a, and a public key A, which is the corresponding public point obtained by multiplying a fixed base point B by that scalar. In shorthand, A = [a]B. Here B is a standard public base point agreed on by everyone using the scheme, and [a]B means scalar multiplication on the elliptic curve group.
To sign a message M, the signer first creates a temporary secret scalar r and turns it into a temporary public commitment R = [r]B. Then the signer hashes together R, the public key A, and the message M to get a challenge h. Finally the signer combines the temporary secret and the long-term secret into a response S = r + h*a mod l, where l is the prime order of the main subgroup.
The signature is the pair (R, S).
Why does this prove knowledge of the private key? Because anyone can check the matching public equation. If S = r + h*a, then multiplying both sides by B gives [S]B = [r]B + [h][a]B = R + [h]A. So the verifier recomputes h from R, A, and the message, then checks that the group equation holds.
That is the heart of Ed25519. The signer cannot fake a valid S for a chosen R and h without implicitly knowing a, unless they can solve the hard discrete logarithm problem in the underlying group. The message enters through the hash, so the challenge is tied to the exact bytes being signed. Change the message, and the challenge changes, so the same response no longer works.
That is the intuition. Ed25519 adds crucial details around how r is derived, how points are encoded, and exactly what verification equation is accepted.
Which curve, encodings, and parameters define Ed25519 (keys, signature sizes, and hashes)?
| Scheme | Curve/field | Pubkey size | Sig size | Nonce model | Implementation risk |
|---|---|---|---|---|---|
| Ed25519 | twisted Edwards (25519) | 32 bytes | 64 bytes | deterministic (SHA-512) | reduced risk from complete formulas |
| Ed448 | twisted Edwards (448) | 57 bytes | 114 bytes | deterministic (SHAKE256) | higher classical security |
| ECDSA | Weierstrass curves | 33–65 bytes | variable (64 bytes) | requires fresh randomness | nonce-related failure risk |
Ed25519 is EdDSA instantiated with a particular Edwards curve and parameter choices. The “25519” refers to the underlying field size associated with Curve25519-family arithmetic. In the Ed25519 form, points are handled on the twisted Edwards curve used by the signature scheme, not in the Montgomery form associated with X25519 key exchange, even though these constructions are closely related.
The standard encoding is compact. A public key is 32 bytes. A signature is 64 bytes, consisting of the encoding of R and the scalar S. Point encoding stores the y coordinate and one sign bit for x. This sounds like a low-level detail, but it matters a lot: interoperability depends not just on the algebra but on exactly how bytes map to points and scalars.
RFC 8032 describes Ed25519 in an implementation-oriented way, including test vectors and reference code, precisely because digital signatures are a place where “almost the same” is not good enough. Two implementations that disagree on accepted encodings or verification edge cases can produce nasty failures. In a normal client application that may look like mysterious incompatibility. In a blockchain consensus system, it can become a consensus split.
The signature system is also deterministic. Instead of drawing a fresh random nonce for each message, Ed25519 derives the effective per-message secret from the private-key material and the message using hashing. For Ed25519, the standard hash function is SHA-512. This makes signatures reproducible for the same key and message under the standard algorithm, and it removes the need for a high-quality external random nonce generator during signing.
Deterministic does not mean carefree. If an attacker can observe timing, power, memory faults, or other side channels, deterministic signing can still leak key material. Standards guidance explicitly warns that implementations must still defend against side-channel and fault attacks, especially in hardware, embedded, or constrained environments. Determinism removes one failure mode; it does not remove the need for careful implementation.
Step-by-step: how an Ed25519 signature is generated
The most useful way to make the mechanism concrete is to walk through one signature as a narrative.
Suppose a wallet or validator starts from a 32-byte Ed25519 private key seed. The algorithm does not use that seed directly as the signing scalar. Instead, it hashes the seed with SHA-512 and splits the result conceptually into two parts. One part is processed into the secret scalar used for the long-term key, and the other part serves as secret prefix material for deriving the per-message value. This design separates the stable signing key from the secret data used to generate the deterministic nonce-like value for each message.
Now the signer wants to sign a message M. It hashes the secret prefix together with the message to derive r, the per-message secret scalar. That r is then reduced modulo the subgroup order l, and the signer computes R = [r]B. At this point, R plays the role of the commitment: it is the public image of a temporary secret that only the signer could have formed from the secret prefix and message.
Next, the signer hashes `ENC(R)
| ENC(A) | M, where ENC(...) is the byte encoding of a point and | means concatenation. This produces the challenge h, again reduced appropriately into the scalar field. Because h depends on R`, the public key, and the message, the signer cannot choose these parts independently after the fact. They are now cryptographically tied together. |
Finally, the signer computes S = r + h*a mod l, where a is the secret signing scalar. The output signature is ENC(R) || ENC(S), totaling 64 bytes.
Notice what changed and what stayed fixed. The long-term secret a stays fixed for the keypair. The temporary scalar r changes with the message. The challenge h changes because it depends on both the message and R. And the final response S changes because it combines both of those changing pieces with the long-term secret. That structure is why signing the same message under the same key deterministically reproduces the same signature in the standard scheme, while different messages produce different commitments and responses.
How does Ed25519 verification work, and why do encoding and cofactor rules affect validity?
| Rule | Cofactor handling | Canonical encoding | Batch compatible | Consensus fit |
|---|---|---|---|---|
| RFC 8032 | cofactor-multiplied recommended | ambiguous | may disagree with batch | needs explicit rules |
| ZIP-215 | requires cofactor multiplication | accepts non-canonical encodings | yes | designed for consensus |
| Ristretto (Decaf) | removes cofactor concern | enforces canonical encodings | yes | best for protocol primitives |
Verification sounds simpler: recompute the challenge and check the equation. But with Ed25519, the details around decoding and subgroup structure are where many practical subtleties live.
A verifier receives public key A, message M, and signature (R, S). It decodes A and R as curve points, decodes S as an integer, recomputes h = H(ENC(R) || ENC(A) || M), and checks a group equation. RFC 8032 describes verification using a cofactor-multiplied equation of the form [2^c S]B = 2^c R + [2^c * h]A, where for Ed25519 the cofactor factor is 8. It also requires that decoded S be less than the subgroup order l; this check is important for preventing signature malleability.
Why is the cofactor there at all? Because the full group of curve points is not prime order; it has a small cofactor. Most of the security argument lives in the large prime-order subgroup, but the actual curve contains a little extra structure. Multiplying both sides of the verification equation by the cofactor projects away some of the nuisance introduced by that small subgroup. In ordinary applications you may never notice this. In protocol design and edge-case validation, it matters a great deal.
This is exactly why two implementations can disagree at the edges while both claiming compatibility with “Ed25519.” RFC 8032 gives a standard verification rule, but some ecosystems discovered that choices around canonical encodings, small-subgroup handling, and batch verification compatibility were not pinned down tightly enough for consensus-critical use. Zcash addressed this with ZIP-215, which explicitly defines accepted Ed25519 signatures using the cofactor-multiplied equation and allows certain non-canonical point encodings that earlier expectations might have rejected. The motivation was not theoretical novelty. It was practical determinism: every node must agree on validity, and batch verification must not accept a different set of signatures than single verification.
That lesson travels beyond Zcash. CometBFT documentation also points to ZIP-215 adoption for Ed25519 verification. More generally, any distributed system where signature validity affects consensus needs exact validation rules, not just a family resemblance to the RFC.
Why do complete formulas and strict validation rules matter for Ed25519 implementations?
One of the strongest implementation advantages of Ed25519 is that the underlying Edwards formulas are complete. That means the addition formulas work for all input points without exceptional cases. In many elliptic-curve systems, exceptional cases force special checks or alternate code paths. Special cases create branching. Branching creates complexity, timing differences, and opportunities for mistakes.
Complete formulas do not eliminate all validation concerns, but they simplify the dangerous part of the surface area. RFC 8032 explicitly notes that this helps avoid expensive point validation on untrusted public values. That is a large reason Ed25519 earned a reputation for being easier to implement robustly than some alternatives.
But “easier” is not “automatic.” The hard part moved from arithmetic exceptions toward definition of validity. Does the implementation require canonical point encodings? Does it accept points that decode onto the curve but lie outside the prime-order subgroup? Does batched verification behave identically to individual verification? These are not cosmetic choices. They determine whether libraries interoperate and whether higher-level protocols inherit hidden ambiguity.
The broader cryptographic community responded to these cofactor-related headaches in another way too: by defining prime-order abstractions such as ristretto255. Ristretto is not Ed25519, and you cannot simply swap the names. But it exists for a related reason: many protocols want a clean prime-order group abstraction without ad hoc cofactor fixes at every use site. The fact that such abstractions became popular tells you something important about Ed25519’s boundary: the signature scheme handles its own cofactor issues carefully, but if you start using the underlying curve group for other protocols, you should not assume the same simplicity carries over unchanged.
When should you use Pure Ed25519 versus the Ed25519ph (prehash) variant?
| Variant | Input mode | When to use | Performance | Interop risk |
|---|---|---|---|---|
| Pure Ed25519 | one-shot message | default for typical messages | efficient for normal sizes | low if spec followed |
| Ed25519ph | prehash / streaming | large or streaming messages | better for very long messages | higher interoperability risk |
| HashEdDSA | hash-based prehash | FIPS or very large messages | faster after prehashing | exposed to hash collisions |
The standard Ed25519 mode is a PureEdDSA scheme: the message itself is part of the hash inputs inside signing and verification. There are also prehash variants such as Ed25519ph, where a hash of the message is signed instead. This can be attractive when messages are very large or arrive in a streaming interface.
But the distinction is easy to misunderstand. Prehashing is not merely “run SHA-512 on the message and then do ordinary Ed25519.” Library documentation is explicit that Ed25519ph(m) is intentionally not the same as Ed25519(SHA512(m)). The internal domain separation and variant rules differ. So if a library exposes a streaming or multi-part API that uses Ed25519ph, that is a different signature variant, not just an implementation trick.
There is also a tradeoff. NIST’s standard notes that HashEdDSA can be faster for long messages because the signature operates on a fixed-size hash output rather than the whole message. But it also points out that prehash variants are more exposed to the collision resistance of the chosen hash in a way pure EdDSA is not. RFC 8032 goes further and says the prehashed variants should not be used. That is a strong signal: use the pure form unless you have a clear, protocol-specific reason not to, and then specify the variant exactly.
This affects APIs in practice. OpenSSL exposes Ed25519 as PureEdDSA one-shot signing and verification: you pass the message in a single call, and you do not specify an external digest. Libsodium offers both single-part Ed25519 and multi-part Ed25519ph APIs, but it documents the difference carefully. So when people say “Ed25519 support,” they may really mean different operational modes with different interoperability boundaries.
Where is Ed25519 used in wallets, blockchains, and libraries?
Ed25519 is common because its properties line up with the needs of real systems. In developer libraries, it is attractive because key generation and signing APIs can be compact and hard to misuse. Libsodium exposes straightforward crypto_sign_* interfaces, and the secret key format conveniently contains both the seed and public key for efficient use. OpenSSL supports Ed25519 through its EVP interface with RFC 8410-compatible key formats.
In blockchain and distributed systems, Ed25519 is often used where many signatures must be verified quickly and consistently. Solana is a well-known example of a chain built around Ed25519 transaction signing. CometBFT-based systems represent Ed25519 public keys and raw 64-byte signatures explicitly in their encoding rules. Cardano uses BIP32-Ed25519 in its HD wallet derivation model rather than ordinary BIP32, which is a reminder that “using Ed25519” can also affect how keys are derived and serialized, not just how signatures are checked. In Substrate tooling, Ed25519 sits alongside other key types such as sr25519 and ECDSA as a first-class supported account scheme.
The common thread is not that these systems are identical. It is that Ed25519 offers a favorable package: compact signatures, efficient verification, and a mature ecosystem of implementations. That package is especially useful where signatures are frequent enough that developer ergonomics and throughput become architectural concerns, not just coding details.
What risks and limitations does Ed25519 NOT address?
The cleanest way to understand Ed25519’s limits is to separate fundamental assumptions from engineering choices.
The fundamental assumption is classical hardness of discrete logarithms in the chosen elliptic-curve setting. If that assumption fails, the scheme fails. In particular, both RFC 8032 and NIST state plainly that a sufficiently large quantum computer would break Ed25519. So Ed25519 is not post-quantum. It remains widely trusted in the classical setting, but it is not a long-term answer to quantum-capable adversaries.
The engineering choices are where most day-to-day failures happen. Deterministic nonces remove one class of randomness bugs, but side-channel leaks can still reveal the key. Validation ambiguities can still cause interop failures or consensus risk. Batch verification must be specified carefully so it agrees with single verification on exactly which signatures are valid. The existence of bugs and incident reports around batch-versus-single verification behavior in real software is a reminder that the cryptography and the API contract have to line up exactly.
There is also a subtler limit: Ed25519 is a signature scheme, not a general recipe for doing arbitrary cryptographic group operations on Curve25519-family arithmetic. If you need signatures, Ed25519 gives a mature answer. If you need a prime-order group abstraction for broader protocol design, you may want something like ristretto255 instead. If you need key exchange, that is X25519, not Ed25519. The family resemblance is real, but the constructions serve different purposes.
Conclusion
Ed25519 is a Schnorr-style signature scheme on an Edwards curve, engineered so that strong cryptographic ideas survive contact with real software. Its importance comes from the combination, not any single feature: deterministic signing to avoid nonce failures, complete formulas to reduce implementation hazards, small 32-byte public keys and 64-byte signatures, and fast performance suitable for systems that verify signatures constantly.
The most important thing to remember tomorrow is this: Ed25519’s success is not just about elegant math; it is about making the secure implementation path comparatively natural. And the place where readers should stay alert is verification: exact encoding and validation rules matter, especially in consensus systems, because two implementations that “both do Ed25519” can still disagree at the edges if those rules are left implicit.
What should I understand about Ed25519 before transferring or trading?
Before depositing, transferring, or trading assets that rely on Ed25519 keys, verify the exact encoding and validation rules the destination expects (encoding, cofactor handling, and whether it accepts prehash variants). On Cube Exchange, you can perform those checks, fund your account, and execute a small test transfer or trade to confirm acceptance before moving larger amounts.
- Check the destination network or counterparty documentation to confirm it uses Ed25519 and whether it follows RFC 8032 or ZIP-215; record the required public-key/address encoding (32 bytes) and signature format (64 bytes).
- Export the public key or address from your wallet and produce a short signed test message; use the destination's verifier or a local verifier to confirm the encoding and signature validate exactly as expected.
- Fund your Cube account with fiat or a supported crypto transfer so you can perform on-chain transfers or market trades.
- On Cube, open the transfer flow for the asset, paste the exact encoded address/public key bytes, review network fees and encoding notes, and submit a small test transfer.
- After the test transfer confirms on-chain or with the counterparty, proceed with larger transfers or trading, monitoring confirmations and any service-specific validation rules.
Frequently Asked Questions
Ed25519 derives its per-message secret deterministically by hashing a secret seed prefix with the message (the standard uses SHA-512), so signatures do not rely on a fresh external random nonce; this removes the common failure class where bad RNGs leak keys, but implementations still must defend against side-channel and fault attacks.
Because RFC 8032 left some edge-case behavior underspecified (encoding, subgroup/cofactor handling) different implementations made incompatible choices; ZIP-215 therefore fixes a single verification rule (the cofactor-multiplied equation) and permits certain non-canonical encodings so all nodes agree on which signatures are valid in consensus systems.
The curve group has a small cofactor (8 for Ed25519), so RFC 8032 specifies multiplying the verification equation by 2^c (for Ed25519, 8) to project onto the prime-order subgroup; this cofactor-handling prevents small-subgroup attacks and is a frequent source of interoperability and malleability issues if omitted or handled inconsistently.
No - Ed25519 is an EdDSA signature instantiation on an Edwards-form curve and uses different encodings and APIs than X25519 (which is a Montgomery-form Diffie–Hellman key-exchange); if you need a clean prime-order group abstraction for other protocols, use ristretto255 rather than assuming Ed25519’s group is interchangeable.
No; like other common elliptic-curve signatures, Ed25519 relies on the classical hardness of discrete logarithms and both RFC 8032 and NIST note that a sufficiently large quantum computer would break Ed25519.
Ed25519ph (the prehash variant) signs a hash of the message using different internal domain separation rules and is explicitly not equivalent to simply signing SHA-512(message); RFC 8032 and the article advise preferring the pure (one-shot) Ed25519 mode and treating prehash variants as protocol-specific exceptions.
Complete Edwards addition formulas in Ed25519 eliminate exceptional arithmetic cases so implementations avoid special-case branching and expensive point-validation paths, reducing a common source of bugs and timing/fault vectors; however, correct encoding and validation rules (canonical encodings, subgroup checks) still matter for interoperability and security.
Implementations should enforce that the scalar S is reduced (S < l), decode points using the standard canonical encodings when required by the protocol, and apply the cofactor-handling verification rule; mismatches in these checks or in batch-versus-single verification behavior are known causes of malleability or consensus mismatches.
Yes - under the standard Ed25519 algorithm a given key and message deterministically produce the same 64-byte signature because the per-message scalar is derived from the secret seed and message; this reproducibility is intentional to avoid RNG failures but does not eliminate side-channel risks.
When you need only signatures, Ed25519 is appropriate; when protocols require a prime-order group abstraction (to avoid cofactor reasoning across many uses), ristretto255 was designed to provide that abstraction and is preferable for multi-purpose group protocols rather than reusing Ed25519’s curve directly.
Related reading