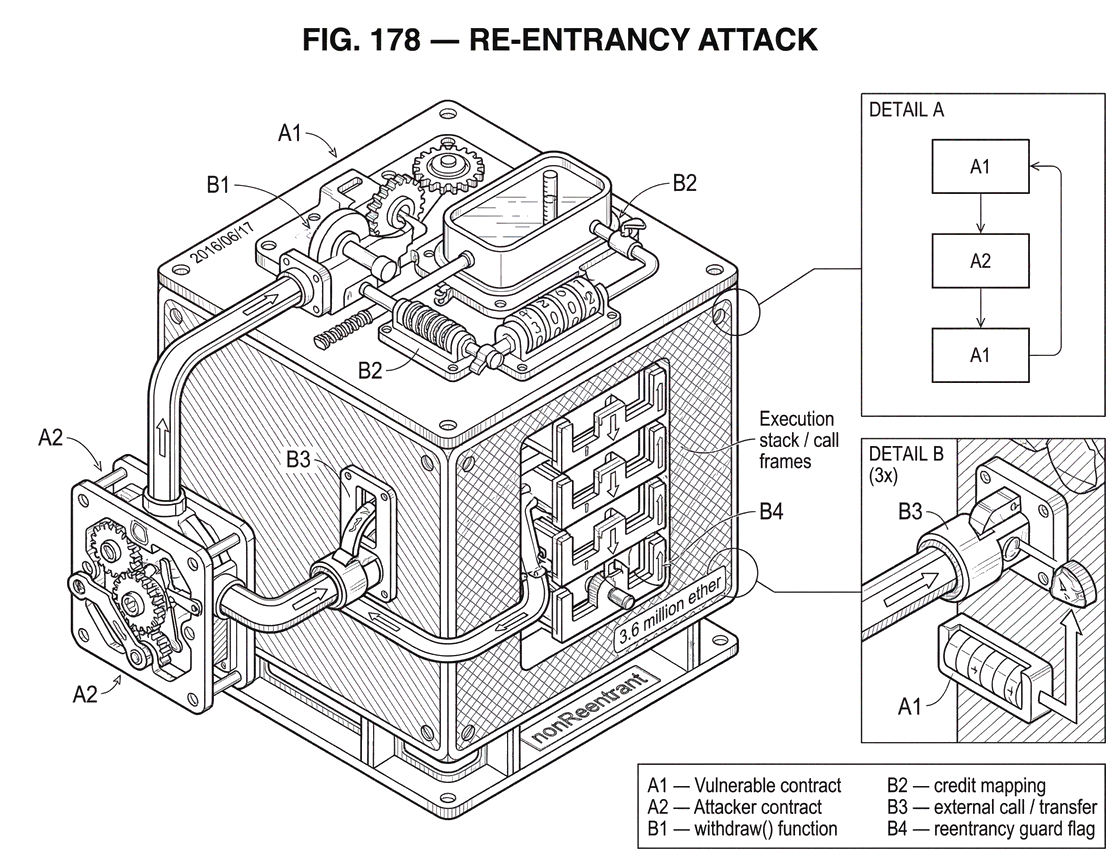
What is a Re-Entrancy Attack?
25 min read
Category archive
The building blocks of crypto: wallets, private keys, consensus mechanisms, and the core concepts underpinning blockchain technology.
Articles
Page 6 of 20
25 min read
26 min read
23 min read
23 min read
25 min read
24 min read
23 min read
24 min read
26 min read
23 min read
22 min read