What Is Address Poisoning?
Learn what address poisoning is, how lookalike wallet addresses trick users, why the scam works, and which wallet and user defenses reduce the risk.
Introduction
Address poisoning is a crypto scam that works by planting misleading addresses into a wallet’s transaction history so that a user later sends funds to the wrong destination. What makes it dangerous is that it does not usually break cryptography, hack a private key, or exploit a consensus flaw. Instead, it exploits a simpler fact: blockchain addresses are hard for humans to recognize, wallet interfaces often abbreviate them, and many users rely on recent history when sending funds.
That combination creates a narrow but very real failure mode. If a malicious address is made to look enough like a familiar one (especially in the first and last characters that interfaces tend to display) then a harmless-looking incoming or logged transaction can become a trap. Later, when the user copies an address from history or recognizes only a truncated version, the attacker gets paid.
This is why address poisoning belongs in the same family as phishing, even though it happens on-chain. The attacker is not forcing the protocol to misroute funds. The protocol is doing exactly what it was told to do. The deception happens earlier, at the point where a human decides which address to trust.
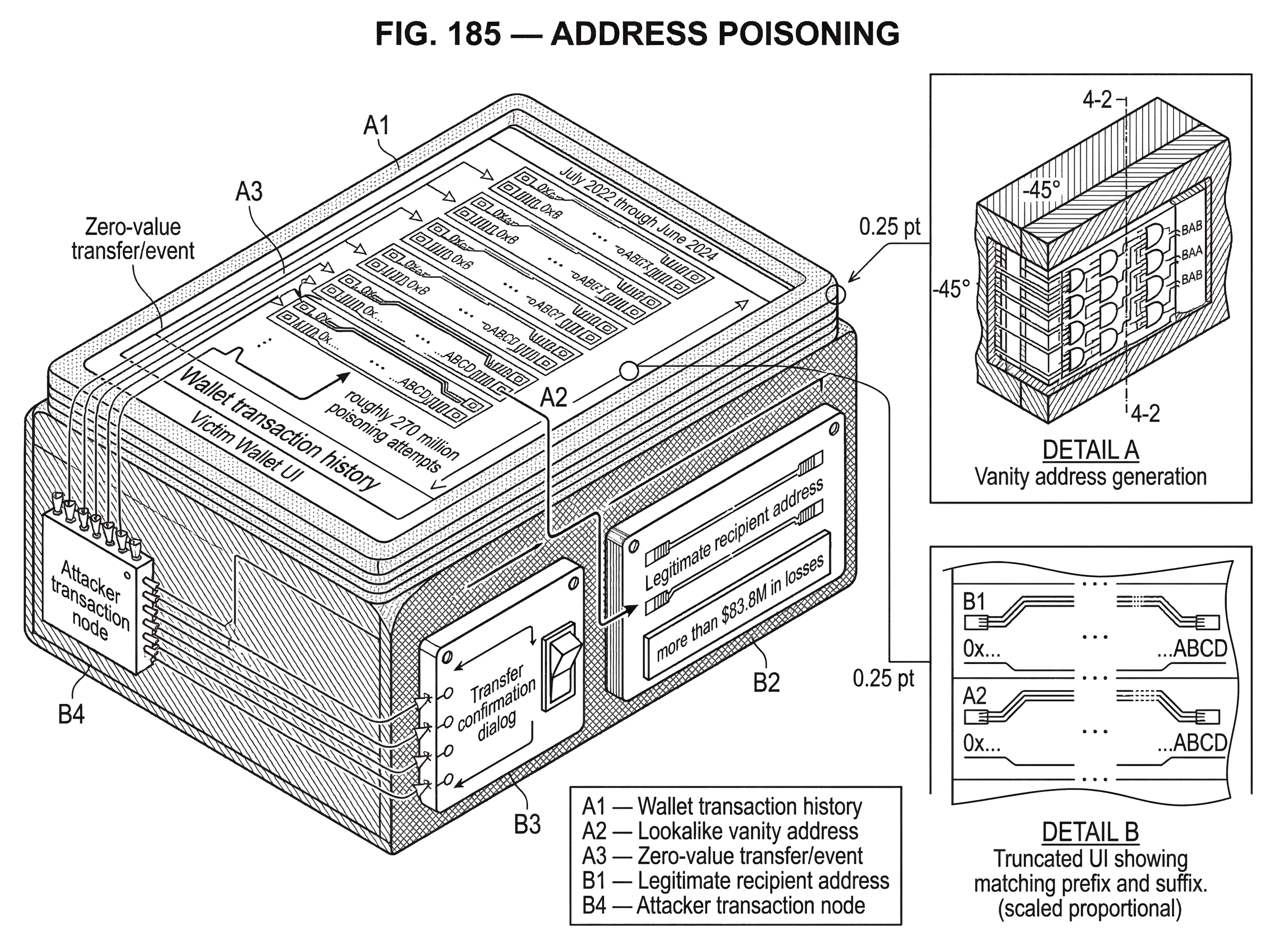
Recent large-scale research shows this is not a niche annoyance. A USENIX Security study that scanned Ethereum and BNB Smart Chain from July 2022 through June 2024 detected roughly 270 million poisoning attempts targeting about 17 million victims, with at least 6,633 confirmed successful incidents totaling more than $83.8M in losses. Those figures are conservative because the measurement focused on major stablecoins and used specific detection windows. Even so, they establish the core point: this is an industrialized attack, not an edge case.
Why blockchain addresses are hard for humans to verify
A blockchain address is designed to be unambiguous for software, not memorable for people. On Ethereum-style chains, for example, an address is a 20-byte value usually written as a long hexadecimal string. That is excellent for uniqueness and routing. It is poor for human recognition.
The practical result is that most people do not verify an address as a whole object. They recognize fragments. They might check the first several characters, glance at the last several characters, and rely on the fact that a wallet or explorer shows those fragments consistently. This is reasonable behavior under time pressure, especially when sending to the same counterparties over and over.
Here is the mechanism the attacker exploits: if users identify addresses by a visible prefix and suffix, then an attacker does not need to copy the entire address. The attacker only needs to generate one that matches the parts the victim is likely to notice. Wallets and explorers reinforce this habit because they often truncate addresses in exactly that way. MetaMask, Trezor, and Etherscan all describe this same usability gap from different angles: long addresses are usually shortened in the interface, and poisoning takes advantage of that shortening.
The important invariant is simple. The blockchain will faithfully send funds to whatever exact address is submitted. There is no semantic notion of “the address you probably meant.” So if the human selection step is corrupted, the protocol offers no correction layer. That is why even a tiny moment of confusion can produce a permanent loss.
How address poisoning works step‑by‑step
At a high level, address poisoning has two moving parts. First, the attacker creates a lookalike address. Second, the attacker causes that address to appear in the victim’s transaction history or token activity so that it becomes available for later copy-paste or visual confusion.
The first part is usually done with vanity address generation. The attacker repeatedly generates keypairs until one produces an address whose visible beginning and ending resemble a target address. This is just brute force. There is no shortcut that breaks the address scheme. The attacker keeps trying random private keys until the resulting address matches enough chosen characters. The cost rises quickly as the attacker asks for more matching digits, which is why most poisoned addresses resemble a target only in the places users are most likely to inspect.
The second part is what turns resemblance into fraud. The attacker sends some form of transaction or event involving the lookalike address so that the victim later sees it in wallet activity or on an explorer page. The transfer itself may be worthless or even zero-value. Its purpose is not to move money now. Its purpose is to create a misleading entry that says, in effect, “this address has interacted with you before.”
That is why the term poisoning is apt. The attacker is contaminating a data source the victim may later trust: recent transaction history, token transfer logs, or an address list. Nothing about the malicious transaction needs to be economically meaningful. It only needs to be visible and plausible.
Address poisoning example: how a lookalike address steals a payment
Imagine Alice regularly sends USDC to a treasury address belonging to her business. She has used that destination many times, so she no longer reads the entire address each time. She recognizes it from the first few characters, the last few characters, and the fact that it shows up in her wallet history.
An attacker watches the chain and notices Alice’s repeated transfers. The attacker then generates an address whose first and last visible characters resemble the treasury address closely enough that, when truncated in a wallet UI, it feels familiar. Next, the attacker sends Alice a tiny token transfer; or triggers a zero-value token event that makes the lookalike address appear in her activity feed.
A few days later Alice needs to make another payment. Rather than opening her saved contacts or checking the treasury address from the original source, she copies what looks like the prior recipient from her recent activity. The visible prefix and suffix match what she expects. She confirms quickly. The chain executes the transfer exactly as requested, and the funds arrive at the attacker’s address.
Nothing in this story requires malware on Alice’s device. Nothing requires compromise of the business treasury. Nothing requires a flaw in USDC itself. The attack succeeds because the wallet history supplied a plausible but false cue, and Alice treated that cue as identity.
That worked example explains why even experienced users can be fooled. Chainalysis observed that a major campaign appeared to target relatively experienced and higher-value wallets, not only novices. The failure mode is less “I do not understand crypto” and more “I performed a familiar task too quickly under an interface optimized for convenience.”
Which types of address‑poisoning attacks should you expect?
| Variant | Signature | Attacker cost | Detection difficulty | Primary deception |
|---|---|---|---|---|
| Tiny transfers | Small genuine-token transfer | Moderate gas/token cost | Moderate | Looks like prior payment |
| Zero-value transfers | Transfer event with zero value | Low gas cost | High | Event appears as real transfer |
| Counterfeit tokens | Fake token contract airdrops | Deployment and minting cost | Moderate | Ticker and logo spoofing |
The surface form of address poisoning varies, but the underlying idea stays the same: place a lookalike address somewhere the victim may later trust. Research and product guidance consistently point to three especially important variants.
Tiny transfers
The most intuitive form is a tiny transfer, sometimes called a dust-like transfer in user guidance. The attacker sends a very small amount of a real token from a lookalike address to the victim. Because the token is legitimate and the transfer is nonzero, it can appear like an ordinary low-value transaction. The victim later sees that address in history and may mistake it for a prior legitimate counterparty.
This version is mechanically simple and works on many chains. Its downside for the attacker is cost. Even tiny legitimate transfers still cost something in gas and token value. That cost matters at scale, which helps explain why attackers often prefer lower-fee chains for mass campaigns.
Zero-value transfers and event spoofing
A more subtle form uses zero-value transfers. On Ethereum-compatible chains, some token implementations permit transferFrom calls with a value of zero in ways that can emit a Transfer event without actually moving assets in the economic sense users care about. Etherscan and academic work both describe how attackers exploit this behavior to create misleading token-transfer records.
The point here is not that zero-value transfers are inherently malicious. The point is that a wallet or explorer may surface the resulting event in a way a user interprets as evidence of a meaningful prior interaction. That interpretation is what the attacker wants. If the UI says, or seems to say, “you sent something here before,” the poisoned address gains credibility.
This is a useful place to separate analogy from fact. A zero-value spoofed event is like forging a receipt in someone’s filing cabinet. The analogy explains the deception: a record exists that should not be trusted as proof of a real relationship. But the analogy fails if taken too far, because on-chain the event is real data produced by real execution. The issue is not falsified bytes; it is misleading semantics.
Counterfeit-token transfers
The third major version uses counterfeit tokens. The attacker deploys a token contract whose name and symbol resemble a legitimate token such as USDC, then sends those fake tokens in patterns meant to look familiar. Trezor, Etherscan, and the NDSS phishing study all note this variant.
This works because many users do not evaluate token identity at the contract level. They see a familiar ticker, a plausible amount, and a lookalike address nearby. If the wallet or explorer does not clearly distinguish verified tokens from imitations, the attacker gets another path to placing misleading entries in front of the user.
The common mechanism across all three variants is worth emphasizing. The attacker is not trying to win by transferring value. The attacker is trying to write a believable story into the victim’s interface: “this address is related to your normal activity.”
Why attackers invest in address poisoning despite low success rates
At first glance, address poisoning seems too flimsy to matter. Most poisoned entries are ignored. Most victims never send money to the attacker. So why does the tactic persist?
Because the payoff distribution is extremely skewed. The attacker can fail thousands or millions of times and still come out ahead if even a handful of victims later make large transfers. Chainalysis described a campaign where the per-address conversion rate was tiny, yet the economics could still be enormous because a single high-value success dominated the returns. Their May 2024 case study centered on a whale who mistakenly sent roughly $68M in WBTC to a lookalike address before most funds were later returned under unusual circumstances.
The USENIX study supports the same economic logic at scale. It found a few large attacker groups, modeled address-generation costs, and concluded that most major groups remained profitable despite variation in tactics and infrastructure. It also found far higher raw attack volume on BNB Smart Chain than on Ethereum, consistent with the idea that lower transaction fees make mass poisoning cheaper.
This is an important security lesson. A scam does not need a high success rate to be dangerous. It only needs a low enough marginal cost and a fat enough tail of victim errors.
Address poisoning vs. credential theft: how this scam is different
Address poisoning overlaps with broader phishing, but it differs from the better-known patterns in an important way. Classic wallet phishing usually tries to steal a secret; a seed phrase, a signature, an approval, or a login credential. Address poisoning usually does not need any of those. It tries to steer an otherwise legitimate transfer toward the wrong recipient.
That distinction matters because it changes the defense model. If the main risk were malware or credential theft, you would focus on keeping attackers out. Here, the attacker can interact with you in public on an open chain. They are allowed to send a zero-value token event or a tiny transfer to your address. You cannot generally prevent that at the protocol level as an end user.
MetaMask and Trezor both make this boundary clear: on a public blockchain, there is no general way to stop strangers from sending transactions or token transfers to your address. So the defense is not “block all incoming poison.” The defense is “avoid treating unsolicited or ambiguous history entries as identity proof.”
That is also why address poisoning sits near the boundary between security and interface design. The protocol is working. The failure happens in the human interpretation layer built on top of it.
How wallets and explorers can reduce address‑poisoning risk
| Mitigation | What it changes | Benefit | Limitation | Best for |
|---|---|---|---|---|
| Show more address chars | Increases visible entropy | Harder to spoof visually | UI space constraints | All users |
| Filter suspicious history | Hide or blur poison txs | Reduces accidental trust | False positives possible | Casual users |
| Address books / allowlists | Trust moves to saved entries | Strong destination anchor | Requires user setup | Recurring recipients |
| Display standards (EIP-55/8117) | Add checksum and zero-count | Machine-checkable clues | Requires adoption | Tooling developers |
Because the attack targets human recognition, interface choices matter a great deal. There are several useful control points.
The first is showing more of the address, more clearly. If a UI only displays a short prefix and suffix, then matching those characters becomes enough for an attacker. Etherscan explicitly recommends increasing visible address characters and adding highlighting features. This does not eliminate the problem (people still may not compare everything) but it raises the amount of visual evidence a lookalike must imitate.
The second is filtering suspicious history entries. Trezor Suite, for example, blurs and marks some poisoning-like transactions as unverified on the client side. Etherscan offers options such as hiding zero-value token transfers and ignoring suspicious tokens. These controls matter because they reduce the chance that poisoned data is treated as routine past activity.
The third is identity layers stronger than raw addresses. Address books and allowlists help because they move trust from “I recognize this string” to “I saved this destination intentionally earlier.” MetaMask recommends saving trusted addresses in contacts rather than copying from history. This is one reason allowlists are a direct mitigation for address poisoning.
The fourth is better address presentation standards. Ethereum’s mixed-case checksum standard, EIP-55, is not a direct anti-poisoning tool, but it reduces accidental acceptance of mistyped addresses by embedding checksum information in letter casing. That matters because any mechanism that helps users or software reject malformed addresses improves address integrity. More recently, ERC-8117 proposes a display convention for EVM addresses with many leading zeros, making those zero counts visible as a UX defense against poisoning in some cases. The basic idea is that if visual structure carries more meaningful information, it becomes harder for a lookalike to pass casual inspection.
These measures are helpful, but they are not magic. They work only if users actually depend on them, and if wallets implement them consistently. A standard that exists but is ignored in the send flow does little good.
How to avoid falling for an address‑poisoning scam
| Action | When to use | Effort | Protection level |
|---|---|---|---|
| Avoid recent history | Always | Low | High |
| Save trusted contacts | After first verification | Low (one-time) | High |
| Small test transfer | Before large sends | Low | Very high |
| Use hardware wallet | High-value transfers | Medium | Moderate |
| Verify full address | Every send | Low | High |
The most reliable user defense is mundane: do not choose destination addresses from recent transaction history unless you verify them independently. This simple rule blocks the central mechanism of the scam.
If you send to the same destinations often, save them in an address book or internal allowlist the first time you verify them from a trusted source. Then reuse that saved entry instead of searching past transactions. This converts an error-prone recognition task into a one-time validation task.
For large transfers, a small test transaction is one of the best practical controls. Chainalysis observed many small test payments in a major campaign and noted that they prevented larger losses when the destination turned out to be wrong.
The reason is straightforward: a test transfer checks the full pipeline before the irreversible amount is sent.
- the exact address
- the receiving wallet
- the user’s assumptions
Hardware wallets can also help, though their protection is limited. They often force a clearer review of the destination address on a separate screen, which can slow down impulsive confirmation. But they do not make poisoning impossible. If the wrong address is what the user intentionally signs, the hardware wallet will faithfully approve the wrong address.
The subtle mistake to avoid is thinking “I’m safe because I know not to share my seed phrase.” That protects against a different class of attack. Address poisoning is about recipient verification, not key theft.
When address‑poisoning defenses fail and why
Address poisoning is powerful, but it depends on assumptions.
It depends on users relying on visible fragments of addresses rather than on stronger identity anchors. If a wallet only lets users send to saved contacts, or if a business workflow requires dual verification against a source-of-truth address registry, the attack loses much of its force.
It depends on the poisoned transaction being surfaced in a credible way. If wallets aggressively hide zero-value spoofing, clearly label unverified tokens, and separate unsolicited activity from ordinary history, many poisoning attempts become harmless noise.
It also depends on the economics of spam. On high-fee environments, some variants become less attractive. That does not eliminate the problem, but it shapes which poisoning methods are favored. The USENIX measurements suggest attackers do adapt to these cost differences across chains.
And finally, it depends on similarity thresholds humans actually use. Attackers do not need mathematical closeness in the abstract. They need perceptual closeness in the interface. That means defenses should be judged not only by cryptographic elegance but by whether they change what users really see and copy.
Conclusion
Address poisoning is a phishing attack on memory and interface trust. The attacker plants a lookalike address into your on-chain history, waits for you to mistake familiarity for identity, and relies on the blockchain to execute your mistake perfectly.
The key fact to remember tomorrow is this: a past transaction entry is not proof that an address is safe to reuse. If you treat raw history as an address book, poisoning can turn convenience into loss. If you verify recipients from trusted saved contacts, check addresses carefully, and use test transfers for meaningful amounts, the attack loses the assumption it needs most.
How do you avoid sending funds to a poisoned address?
Verify the recipient before you paste and send on Cube. On Cube Exchange, fund your account, open the send/withdraw flow, and only submit a payment after independently confirming the full destination address and performing a small test transfer for high‑value amounts. These steps reduce the chance that a truncated UI or recent-history entry tricks you into paying a poisoned address.
- Fund your Cube account with fiat on‑ramp or a supported crypto transfer.
- Retrieve the recipient address from a trusted source (signed invoice, official record, or the counterparty’s verified contact). Copy the full address exactly; do not pick the destination from recent activity.
- In Cube’s send flow, paste the full address, then open an external block explorer and compare the entire address string (not just the prefix/suffix) and the token contract if sending tokens.
- For meaningful amounts, send a small test transfer first. Confirm the test amount arrived at the intended recipient on‑chain before sending the remainder.
Frequently Asked Questions
An attacker generates a lookalike (usually via brute‑force vanity address generation), then creates an on‑chain record - e.g., a tiny transfer, a zero‑value token event, or a counterfeit token payment - from that lookalike so it appears in your wallet or explorer history; later you copy or visually match the truncated prefix/suffix shown there and send funds to the attacker’s address, and the blockchain executes that exact destination without correction.
No - poisoning normally doesn’t break cryptography or take your keys; attackers brute‑force keypairs until an address’s visible fragments (prefix/suffix) look enough like the target, then use on‑chain records to create a believable history entry that fools human recognition.
Zero‑value spoofing uses token calls that emit Transfer events (for example transferFrom with value zero) without moving real value, and wallets/explorers may surface those events as ordinary transfers; attackers exploit that UI interpretation so a lookalike address appears to have had prior legitimate activity.
Because the marginal cost per poisoned entry can be tiny while a single large mistake yields a huge payoff: studies report hundreds of millions of poisoning attempts (USENIX found roughly 270M attempts, ~17M victims) with thousands of confirmed successes and tens of millions in observed losses, so a low hit rate can still be profitable for attackers.
You cannot stop strangers from sending transactions to your address on a public chain, but wallets and explorers can reduce risk by showing more of an address, hiding or flagging suspicious zero‑value/token activity, blurring or marking unverified entries, and encouraging saved contacts/allowlists - practices Etherscan, Trezor, and MetaMask recommend or are implementing.
No - hardware wallets are not immune: they can help by forcing clearer, slower address reviews on a separate device, but if the wrong destination is what you intentionally confirm and sign, the hardware wallet will approve that transaction just like any other.
Do not pick destinations from recent history unless you independently verify them; save verified recipients in an address book or allowlist and reuse those entries, and for large transfers do a small test transaction first - these practices block the central mechanism poisoning relies on.
Research teams have released labeled datasets (e.g., the NDSS PTXPHISH set and a USENIX dataset/Jupyter notebook) and some detectors have been integrated into alerting platforms like Forta, but detection is rule‑based, has documented corner cases, and will miss variants (DEX swap chains, tiny nonzero prices), so coverage is useful but not complete.
Standards help but aren’t a silver bullet: EIP‑55 mixed‑case checksums reduce accidental acceptance but offer limited check bits and only affect letters, while EIP‑8117 display conventions (making leading zeros visible) improve visual integrity for some addresses but depend on consistent, legible rendering and broad adoption - accessibility and deployment remain open issues.
Attack volume and methods vary with cost; empirical studies show much higher raw poisoning volume on lower‑fee chains (USENIX reported far more poisoning transfers on BNB Smart Chain than on Ethereum), so attackers gravitate toward cheaper environments, though they adapt tactics across chains.
Related reading