What is a Flash Loan Attack?
Learn what a flash loan attack is, how atomic borrowing enables DeFi exploits, and why oracle, pricing, and accounting design usually fail first.
Introduction
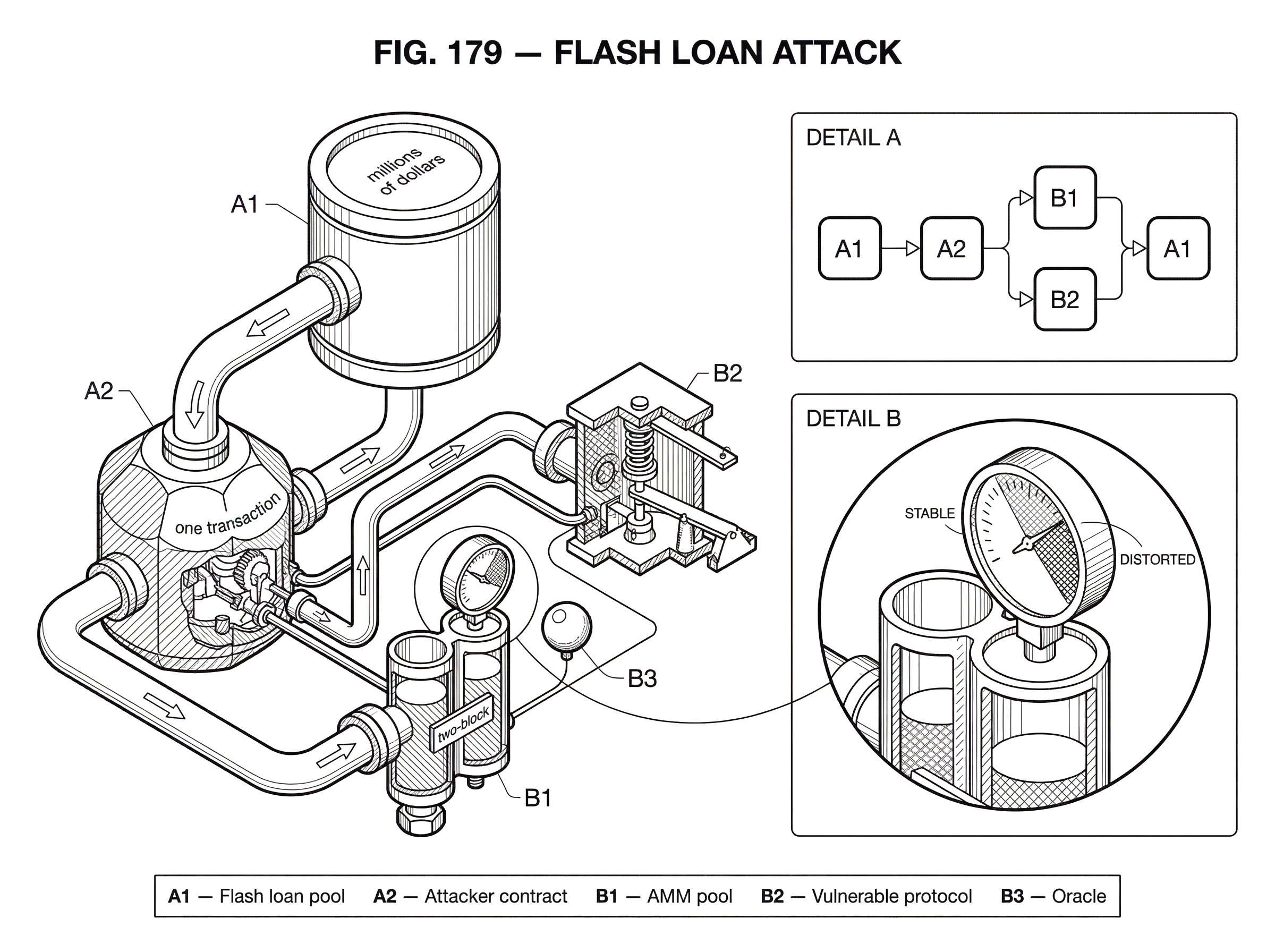
flash loan attack is the name commonly given to a DeFi exploit in which an attacker uses large amounts of temporary, uncollateralized capital inside a single transaction to manipulate a protocol and extract value before the transaction ends. The phrase is catchy, but it is also slightly misleading. In many cases, the flash loan is not the underlying bug. It is the amplifier. The actual weakness is usually that some protocol trusts a state variable that can be pushed out of shape for a moment; a spot price, a share price, a collateral calculation, a reserve balance, or a liquidation path.
That distinction matters because it changes how you defend against the problem. If you think the attack is “someone borrowed a lot of money,” the obvious response is to focus on the lending primitive. But if the real issue is “our contract accepted a manipulable signal as truth,” then the defense has to start with oracle design, accounting invariants, liquidation logic, and transaction-level assumptions. Flash loans only make these weaknesses easier to exploit by removing the need for the attacker to bring their own capital.
The simplest way to see the puzzle is this: how can someone borrow millions of dollars with no collateral, use it, repay it, and still steal money; all in one block? The answer is atomicity. On smart-contract platforms, a transaction either completes in full or reverts in full. A flash loan relies on that all-or-nothing property. The lender can safely hand out funds with no collateral because if the borrower fails to repay principal plus fee by the end of the transaction, the entire transaction is undone as though it never happened. That same property gives attackers a clean environment for complex, temporary manipulations.
How do flash loans and atomic execution enable one‑transaction exploits?
A flash loan is an uncollateralized loan that must be repaid, with any required fee, before the transaction finishes. Aave’s documentation describes it directly: the borrower requests funds from the pool, the pool transfers the assets and calls the borrower’s contract, that contract executes arbitrary logic, and then the pool pulls back the amount owed, all within one transaction. Balancer documents the same essential structure: repayment is checked at transaction end, and if the strategy cannot repay, the whole transaction reverts.
This means the lender is not really taking open-ended credit risk in the way a normal lender would. The loan exists only inside the atomic boundary of one transaction. If repayment fails, state rewinds. That is why flash loans can be offered without collateral at all.
Here is the mechanism that makes attacks possible. A protocol somewhere in the same transaction reads a piece of state and assumes it reflects a fair market reality or a safe internal balance. The attacker uses flash-loaned capital to distort that state just long enough for the vulnerable protocol to act on it. Then, before the transaction ends, the attacker unwinds the distortion, repays the loan, and keeps the difference.
The key invariant for the attacker is simple: after every step, the final transaction must still close with enough assets to repay the lender plus fees. The key invariant for the defender is different: no important protocol decision should depend on a value that can be cheaply distorted within the same transaction.
That is why many exploit reports use the phrase flash-loan attack, but careful analyses often say something more precise: flash-loan-enabled oracle manipulation, flash-loan-assisted insolvency exploit, or flash-loan-funded share-price manipulation. The loan matters, but mostly because it supplies scale.
What legitimate DeFi use cases do flash loans serve?
Flash loans exist for legitimate reasons. Aave explicitly highlights arbitrage, liquidity switching, and liquidations without needing upfront principal. Balancer similarly describes arbitrage and collateral swaps. These are not edge cases. They are natural products of DeFi’s composability.
Suppose a trader sees the same asset priced differently in two venues. Without a flash loan, they need inventory or collateral to exploit that difference. With a flash loan, they can borrow the needed asset, trade through both venues, end up with more than they started, repay the loan plus fee, and keep the spread. If the spread disappears or execution fails, the transaction reverts and the only likely loss is gas.
That property is economically powerful because it turns capital access into transaction design. Instead of asking, “Who already has enough money to do this trade?”, flash loans ask, “Can this sequence of state transitions pay for itself by the end of the transaction?” If yes, anyone can execute it.
That same accessibility is what makes attacks dangerous. An exploit that once required a large treasury, exchange account, or whale-sized inventory now becomes available to any attacker who can write a contract and identify a weak assumption in another protocol.
How can an attacker manipulate an AMM price with a flash loan in a single transaction?
| Attack type | What attacker distorts | Vulnerable action | Profit vector | Flash loan role |
|---|---|---|---|---|
| Lending overcollateralization | AMM spot price | Post inflated collateral value | Borrow excessive assets | Provides transient capital |
| Vault share minting | Underlying asset price | Deposit at inflated share price | Withdraw buffer funds | Amplifies trade size instantly |
| Rewards minting | LP reserve ratio | Trigger inflated reward calc | Mint extra reward tokens | Makes pool trade large enough |
The most common mental model is oracle manipulation. Imagine a lending or rewards contract that decides value by reading the spot price from a single automated market maker pool; for example, by inferring price directly from current reserves. Chainlink’s security guidance treats this as a red flag because a single DEX or AMM spot price is not a robust oracle. It is just the current result of the last trade, which means enough capital can move it.
Now imagine an attacker borrows a large amount of capital with a flash loan. In the same transaction, they trade aggressively against that AMM pool, pushing the spot price far away from the broader market. For a moment, the on-chain reserve ratio says the asset is worth much more, or much less, than it really is. A vulnerable protocol then reads that manipulated spot price and uses it as if it were truth.
What happens next depends on the protocol. If it is a lending protocol, the attacker may post an asset as collateral at an inflated valuation and borrow too much against it. If it is a vault, the attacker may deposit or withdraw at a distorted share price. If it is a rewards system, the attacker may mint too many reward tokens. Once that favorable action is complete, the attacker reverses the price manipulation, restoring the AMM closer to normal, repays the flash loan, and keeps the extracted value.
The flash loan did not create the false price. The AMM trade did. The flash loan made that trade large enough to matter without requiring the attacker to own the capital beforehand.
This is why calling every such exploit a flash loan bug is imprecise. If the vulnerable contract had used a more manipulation-resistant pricing method, the same borrowed capital would not have been enough.
Why are single‑pool AMM spot prices vulnerable to manipulation?
An AMM pool is designed to quote a price from its reserves. That is excellent for executing swaps. It is not automatically excellent for serving as a price oracle for other protocols.
The reason is mechanical. An AMM price is an execution price, not a neutral observation from nowhere. It is the current terms at which the pool will trade given its present reserves. If someone makes a very large trade relative to the pool’s liquidity, the reserves move and the quoted price moves with them. In low liquidity, this can happen dramatically. In deep liquidity, it still happens, just at higher cost.
That means a protocol that reads raw reserve ratios or spot prices from a single pool is effectively saying: “Whatever the last large trader can force this pool to say right now, we will treat as true.” Flash loans make that statement especially dangerous because the attacker can source the required capital only for the moment needed.
Chainlink’s guidance makes the point bluntly: using reserve-based spot prices as an oracle is unsafe. The underlying problem is insecure oracle design, not the existence of flash loans.
When does a TWAP oracle reduce flash‑loan risk, and what are its limits?
| Oracle type | Attack resistance | Data freshness | Attacker cost | Best when |
|---|---|---|---|---|
| Spot price | Low | Real‑time | Cheap to manipulate | High‑frequency needs |
| TWAP (short) | Medium | Near real‑time | Moderate capital | Moderate volatility |
| TWAP (long) | High | Lagging | High capital or multi‑block control | Stable markets |
| Aggregated feed | Very high | Configurable | Very expensive to manipulate | Critical price hooks |
A common response is to use a TWAP, a time-weighted average price, rather than the current spot price. The intuition is straightforward. A flash loan exists for one transaction or one block. If your oracle averages price over many blocks, a momentary distortion has much less effect.
That intuition is broadly right. Chainlink notes that TWAPs mitigate single-transaction flash-loan manipulation because the manipulated price is averaged over time rather than accepted immediately. But this is not a complete solution. During volatile periods, TWAPs can lag real market conditions. They also reflect only the liquidity and trading behavior of the exchange or pool they are built from, so they are still limited if that venue is unusually thin or structurally skewed.
Uniswap’s research on v3 oracles adds a more subtle point. Under Ethereum proof-of-stake, validators can sometimes know enough about upcoming block production to make certain multi-block manipulations more plausible than under older assumptions. The research argues that simple two-block manipulations on major pairs remain prohibitively expensive today, but longer control windows become materially cheaper. In other words, TWAPs do raise attack cost, often dramatically, but their safety depends on the averaging window, available liquidity, validator sequencing power, and the amount of profit available to the attacker.
So TWAP is not “secure” in the abstract. It is a design tradeoff. It converts an easy single-transaction manipulation into a more expensive and time-dependent manipulation. That is often good enough. Sometimes it is not.
How does multi‑venue oracle aggregation defend against flash‑loan manipulation?
If the problem with a single AMM spot price is that it is too local and too easy to move, the obvious remedy is to ask a broader question: what is the market saying across many venues, not just one pool right now?
That is the logic behind decentralized oracle networks and multi-layer aggregation. Chainlink describes a three-layer approach: data-source aggregation, node-operator aggregation, and oracle-network aggregation. At the data-source layer, refined market data can already be volume-weighted and filtered for outliers. At the node layer, operators can source from multiple independent providers and report a median. At the network layer, the feed aggregates many node reports, commonly again by median and with a threshold of responding nodes.
The important idea is not the brand name of one oracle provider. It is the mechanism. A single flash-loan-funded trade can move one on-chain pool. It is much harder for that trade to move the median of many independent observations spanning multiple markets and operators. Aggregation changes the attacker’s job from “distort one place briefly” to “distort enough of the market or oracle pipeline that the aggregate itself moves.” That is a much taller order.
This does not mean aggregated feeds are magical or perfect. They involve choices about update latency, cost, and where aggregation happens. But they defend the right layer of the problem: the protocol’s dependence on a manipulable input.
What other protocol weaknesses can flash loans enable besides oracle attacks?
Oracle manipulation is the most famous pattern, but not the only one. More generally, a flash loan attack occurs when atomic capital lets an attacker push a protocol through a state transition it was not designed to handle safely.
The Euler Finance exploit is a good example of this broader class. According to public incident analysis, the attacker used a flash loan from Aave to build a highly leveraged position inside Euler, then exploited a flaw in donateToReserves() that omitted a liquidity check. The important point is that the attack was not primarily “the oracle was wrong for one block.” It was “there was a code path whose accounting and collateral assumptions could be violated, and flash-loaned capital made it possible to drive the protocol into that bad state and profit from liquidation mechanics in the same transaction.”
This is a useful correction to a common misunderstanding. Flash loan attacks are not a single vulnerability class. They are a style of exploit that combines atomic borrowing with some other weakness: oracle design, share accounting, reserve logic, liquidation rules, governance thresholds, or missing state checks.
The Harvest Finance case illustrates another variant. Least Authority’s audit describes how a flash loan could manipulate the price of underlying assets affecting vault share valuation, allowing profit to be extracted from the vault buffer at other depositors’ expense. Again, the core issue was not that borrowing existed. It was that deposit and withdrawal logic depended on a price path that could be distorted transiently.
How do MEV and transaction ordering affect the success of flash‑loan exploits?
A flash loan attack is usually discussed as if the attacker acts in a vacuum. In reality, they operate in a crowded block-building environment full of arbitrage bots, searchers, and validators competing for ordering advantage.
The Flash Boys 2.0 research documented how bots engage in priority gas auctions to secure early execution and capture opportunities in decentralized exchanges. This matters because many attacks depend not just on what happens, but on when it happens inside a block. If a transaction must manipulate one pool, call another protocol, and then unwind before arbitrage corrects the pool, precise execution ordering matters.
This is why flash loan attacks live naturally alongside the broader topic of MEV. Flash loans provide temporary capital. MEV infrastructure helps secure favorable sequencing. Together they make highly optimized, atomic attacks more practical.
That does not mean every flash loan exploit is an MEV exploit. But it does mean that protocols should not assume a benign transaction environment. If a profitable atomic exploit exists, sophisticated actors will compete to execute it, copy it, front-run it, or sandwich around it.
How do flash‑loan risks differ across blockchains and execution models?
The pattern is not unique to one protocol, and it is not purely an Ethereum phenomenon. Aave and Balancer expose clear flash loan primitives on EVM chains. Uniswap v4’s flash accounting is not itself a flash loan, but it relies on the same broad idea of transaction-level obligations being accumulated and settled before the transaction ends. If the deltas are unresolved, the transaction reverts. That is another form of atomic composability.
Outside the EVM, the shape of the primitive depends more heavily on the execution model. Save’s documentation on Solana notes that flash-loan functionality was limited because of Solana transaction reentrancy and program-calling constraints, and the team described active work on mitigations. Port Finance also lists flash loans as part of its product surface on Solana. In the Cosmos ecosystem, White Whale describes vaults that supply flash-loan capital for arbitrage and liquidations across liquidity hubs.
The common thread is not a specific opcode or interface. It is the presence of an execution environment where many contract calls can compose atomically, and where temporary access to large liquidity can be conditioned on settlement before transaction completion. Once those ingredients exist, the same style of attack becomes possible if downstream protocols trust manipulable state.
What common misconceptions do developers have about flash‑loan attacks?
The first common mistake is blaming the flash loan rather than the vulnerable assumption. If your contract can be exploited only when the attacker has lots of capital, then yes, flash loans widen access. But a whale, market maker, or coordinated attacker could often do something similar with their own funds. Flash loans reduce the cost of becoming dangerous; they do not usually create the underlying weakness.
The second mistake is assuming audits alone will catch the issue. Audits are valuable, but many flash-loan-enabled exploits are not simple coding errors like an obvious arithmetic overflow. They are economic design flaws. As the bZx case made painfully clear, audited code can still fail if it treats poor pricing data as trustworthy.
The third mistake is solving only the last incident. For example, checkpointing prices or adding withdrawal friction may block a specific one-transaction exploit but introduce user-experience costs or new denial-of-service paths. The Harvest audit is particularly useful here because it shows how a mitigation against flash-loan profit can also create operational tradeoffs and even fresh attack surfaces if thresholds are badly set.
The fourth mistake is conflating flash loan attacks with reentrancy. They are different failure modes. A reentrancy attack abuses callback control flow and repeated entry before state is updated safely. A flash loan attack usually abuses economic state inside an atomic transaction. The two can coexist in a larger exploit chain, but they are not the same thing.
Which defensive controls should protocol teams prioritize to reduce flash‑loan risk?
| Control | Primary effect | Attack cost impact | Trade-offs | Best for |
|---|---|---|---|---|
| Oracle aggregation | Multiple market inputs | Raises cost greatly | Higher cost, update latency | Price‑dependent logic |
| TWAP | Time‑averages price | Raises short‑term cost | Stale during volatility | AMM‑sourced prices |
| Deep liquidity | Increase pool depth | Raises slippage cost | Capital intensive | DEX‑based oracles |
| Accounting invariants | Enforce solvency checks | Prevents state exploits | Complex correctness proofs | Accounting‑dependent logic |
| Circuit breakers | Emergency pause | Limits blast radius | Operational friction | Incident containment |
The strongest defenses start by asking what values your protocol treats as authoritative. If the answer includes single-pool spot prices, instantly realizable share values, or any state variable that can be moved dramatically by temporary capital, you have the basic ingredients for a flash-loan-enabled exploit.
For price-dependent logic, broad oracle aggregation is usually the cleanest defense. If that is not possible, a carefully designed TWAP can raise attack costs, though it comes with latency and market-coverage tradeoffs. On AMM-based systems, deeper and wider liquidity can also increase manipulation cost, as Uniswap’s v3 oracle analysis shows.
For accounting-dependent logic, the control is different. Every path that changes reserves, collateral, debt, or claimable balances must preserve the protocol’s core solvency invariants. Euler’s lesson is that an unusual helper path, such as reserve donation, can be just as dangerous as the main borrow or transfer path if it bypasses the checks those main paths enforce.
For vaults and share-pricing systems, defenses often involve preventing users from depositing and withdrawing against the same manipulated state snapshot, or ensuring that transient prices do not immediately determine mint and redeem values. But these protections should be evaluated not only for security but for liveness and user fairness, because hardening one edge can make ordinary operation worse.
Emergency controls still matter. Pausable contracts and other circuit breakers, as documented by OpenZeppelin, can give teams time to contain damage during an unfolding incident. Reentrancy guards are useful where callback-based control flow is a risk. But these are secondary controls. They help reduce blast radius. They do not fix a protocol that fundamentally trusts manipulable economic inputs.
How should I summarize flash‑loan attacks in one sentence?
A flash loan attack is best understood as an atomic capital amplifier applied to a protocol weakness. The flash loan supplies scale without requiring upfront wealth. Atomic execution lets the attacker borrow, manipulate, exploit, unwind, and repay in one all-or-nothing transaction. The true bug is usually the protocol decision that can be tricked by a temporary distortion.
If you remember only one thing, remember this: flash loans are usually the fuel, not the fire. To defend against flash-loan attacks, do not start by asking how to ban borrowing. Start by asking what your protocol would do if an adversary had enormous capital for exactly one transaction; because in DeFi, they often can.
How do you secure your crypto setup before trading?
Secure your crypto setup by hardening account recovery, limiting on‑chain approvals, and verifying destinations before you trade. Cube Exchange uses a non‑custodial MPC signing model so you keep control of your keys while using Cube’s trading flows; follow the checklist below to reduce the risk of atomic exploits, bad destinations, and accidental approvals.
- Create or access your Cube non‑custodial (MPC) account and complete recovery setup; record any recovery factors offline.
- Make a small test deposit of the exact token and network you plan to use to verify on‑chain routing and finality.
- Before approving or submitting a trade, check the token contract address, network, destination address, and set a limited ERC‑20 allowance rather than unlimited approval.
- For execution risk, pick an order type that matches your need (use a limit order to control price/slippage or a market order for immediate fills) and review estimated fees and slippage, then submit.
Frequently Asked Questions
The root cause is usually a protocol trusting a state value that can be cheaply distorted inside one transaction (a spot price, share price, collateral calculation, reserve balance, or liquidation path); flash loans simply supply the temporary capital and atomic execution to make that distortion possible.
No - banning or blaming flash loans is typically ineffective because flash loans are usually the amplifier, not the underlying bug; the right fix is to remove or harden protocol decisions that depend on manipulable inputs like single-pool spot prices or unchecked accounting paths.
TWAPs reduce the impact of single-transaction manipulations by averaging price over time, but they introduce latency, can lag during volatility, and their safety depends on window length, liquidity, and block-proposer sequencing power; they raise attack costs but are not a guaranteed fix.
Because an AMM quotes an execution price derived from current reserves, a sufficiently large trade relative to pool liquidity will move those reserves and thus the quoted price, so reading a raw AMM spot price as an authoritative oracle makes a protocol vulnerable to momentary manipulations.
Aggregating prices across data sources, node operators, and oracle-network feeds (e.g., Chainlink’s multi-layer approach) makes transient manipulation of a single venue far less effective, since an attacker must now distort many independent observations rather than one pool.
No - many flash-loan–enabled exploits exploit accounting, liquidation, or share-pricing logic rather than oracles; examples include Euler’s donateToReserves() accounting flaw and Harvest’s vault share–valuation path, so the class of risk is broader than oracle manipulation alone.
Transaction ordering and MEV matter because attackers often need precise sequencing (manipulate a pool, trigger a vulnerable call, then unwind before arbitrage); priority gas auctions, searchers, and validators can all affect whether an atomic exploit succeeds or who captures the profit.
Start by identifying which protocol decisions treat a manipulable value as authoritative and fix those (use broader oracle aggregation, enforce solvency/accounting invariants on every state-changing path, and design vault mint/redeem flows to avoid acting on transient prices); use emergency circuit breakers as secondary mitigations.
Execution model and toolkit differences change how easy flash-loan patterns are: EVM chains with composable atomic transactions widely expose flash loans, while chains like Solana have different reentrancy and program-calling constraints that have limited or altered flash-loan implementations; cross-chain designs must thus consider local execution semantics and available liquidity.
Related reading