What Is Cryptocurrency?
Learn what cryptocurrency is, why it exists, how it works, and how blockchains, consensus, wallets, fees, tokens, and privacy fit together.
Introduction
Cryptocurrency is digital money whose ownership and transfer rules are enforced by a distributed computer network rather than a bank, payment company, or single database operator. That sounds simple until you ask the question that makes the whole subject interesting: if digital information can be copied, what stops digital money from being copied too? The reason cryptocurrency exists is that ordinary digital files are easy to duplicate, but money only works if the system can maintain a shared answer to a harder question: who owns what, and which transfers are valid, right now, for everyone.
That is the core problem cryptocurrencies solve. They are not merely “internet cash,” and they are not all built the same way. Bitcoin approached the problem by combining cryptographic signatures, a public transaction history, and proof-of-work mining. Ethereum kept the public ledger idea but expanded it into a general-purpose programmable system, so value transfer could be only one kind of state change among many. Other systems made different tradeoffs around speed, privacy, programmability, and finality. But they are all trying to preserve the same invariant: a scarce digital asset should not be spendable twice, and the network should be able to verify that fact without trusting a central bookkeeper.
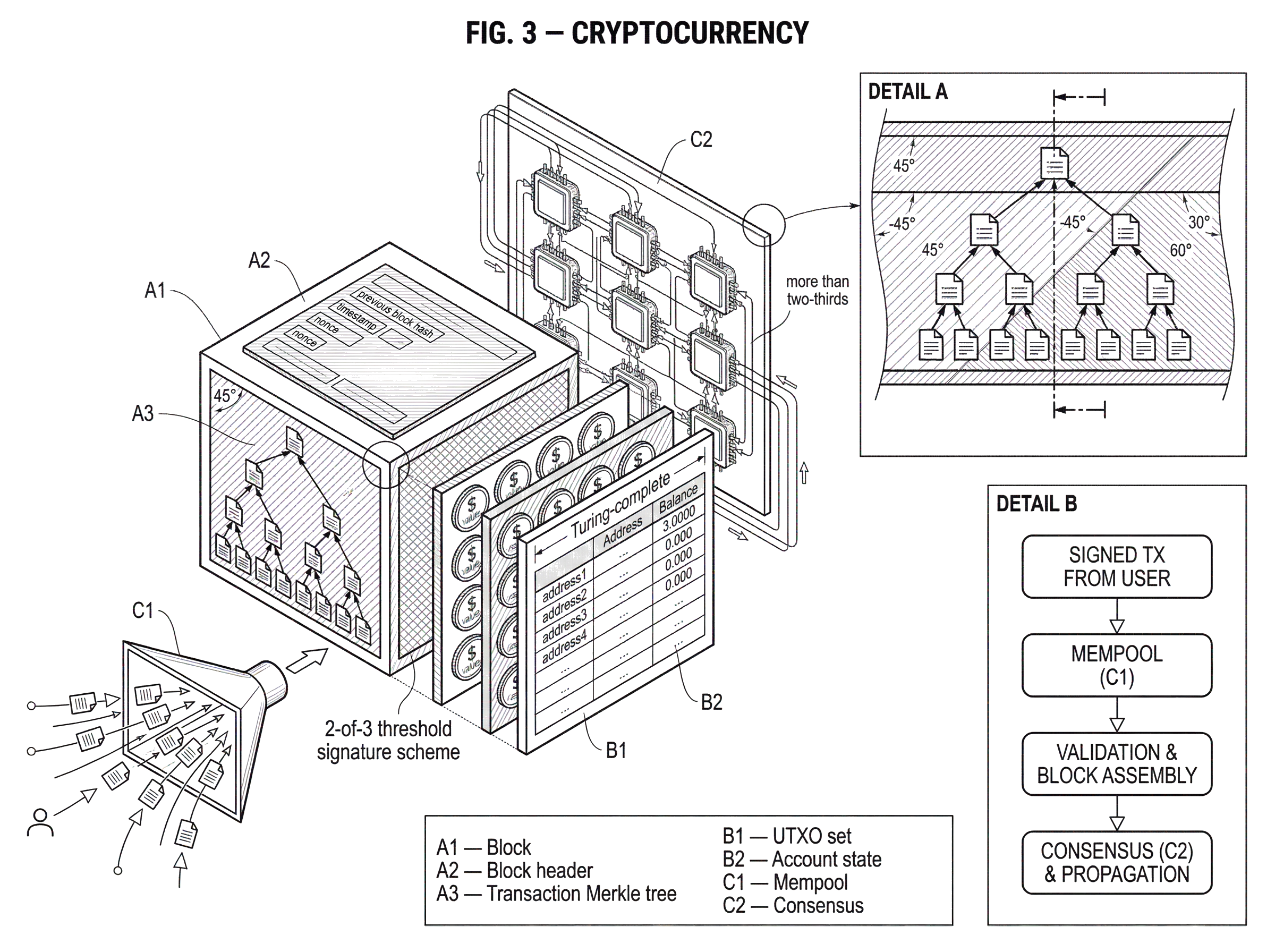
A good way to think about cryptocurrency is as a shared state machine for ownership. The network keeps a record of balances, outputs, accounts, or notes depending on the design. Users propose changes to that record by signing transactions. Nodes check whether those proposed changes obey the rules. A consensus mechanism determines which valid changes become part of the canonical history. Once you see cryptocurrency this way, many surface differences start to make sense. wallets are key managers. Transactions are state transitions. Fees are resource pricing. Consensus is the mechanism that decides which version of the ledger everyone should accept.
How can digital value avoid double‑spending without a bank?
In an ordinary banking system, preventing double-spending is conceptually easy. The bank owns the ledger. If Alice has $10 and sends $7 to Bob, the bank decreases Alice’s balance and increases Bob’s. If Alice tries to send the same $10 again, the bank rejects the second transfer. The scarcity of the money depends on the institution maintaining one authoritative ledger.
If you remove that institution, the problem becomes harder immediately. Alice can sign a message saying “pay Bob,” but she could also sign another message saying “pay Carol” using the same funds. If Bob and Carol receive different copies of those messages, who decides which one counts? A cryptocurrency is a system for answering that question in public, under adversarial conditions, among participants who do not fully trust each other.
That requirement explains why cryptocurrency is built from several pieces at once. Cryptography proves authorization: a valid signature shows that the holder of a private key approved a transaction. A network protocol spreads transactions and blocks among nodes. A ledger structure records the state that everyone is trying to agree on. And a consensus mechanism gives the system a way to converge on one history rather than many conflicting ones. Leave out any of these pieces and the system stops being money-like in the relevant sense.
This also explains a common misunderstanding. Cryptocurrency is not valuable merely because it is encrypted or digital. The important property is not secrecy by itself. In many systems, the ledger is mostly public. The important property is that the network can verify ownership and order transfers without needing a single trusted operator to reconcile disputes.
How do blockchains represent who owns what?
| Model | State unit | Parallel validation | Programmability | Best for |
|---|---|---|---|---|
| UTXO | discrete unspent outputs | easy parallel checks | limited scripting | privacy and concurrency |
| Account | account balances and nonce | largely sequential (nonce) | rich smart contracts | general-purpose dapps |
| Shielded notes | encrypted commitments | proof-heavy, less parallel | complex or limited | strong transaction privacy |
Different cryptocurrencies represent ownership differently, but the logic is the same: the ledger contains some machine-verifiable representation of spendable value, and only authorized users can move it.
Bitcoin popularized the UTXO model, short for unspent transaction output. In that model, coins are not stored as one running balance attached to an account. Instead, the ledger contains discrete spendable outputs created by past transactions. A new transaction consumes some existing outputs as inputs and creates new outputs for future spending. The effect is similar to using cash bills and receiving change. If you control the keys that satisfy the spending conditions for an output, you can spend it.
Ethereum took a different route with an account-based model. The Ethereum whitepaper describes the state as a set of accounts, each with fields such as a nonce, balance, optional code, and storage. In this design, a transaction updates account state directly. That feels closer to a bank ledger: account A decreases, account B increases, and smart contract state may change as part of the same transition. This is especially convenient for programmable applications, because contracts can maintain ongoing internal state rather than reconstructing everything from spendable outputs.
Neither model is simply “better” in all respects. The UTXO model makes some forms of parallel validation and spending logic conceptually clean, while the account model often makes general-purpose programming more straightforward. What matters for a beginner is the deeper point: a cryptocurrency ledger is not storing coins the way a folder stores files. It is storing rules and claims about spendability, and the network continuously checks whether those claims remain consistent.
Privacy-focused systems complicate this picture in useful ways. Monero, for example, uses one-time addresses and ring-signature-based constructions so observers cannot easily link sender, receiver, and amounts, while still allowing the network to verify that no invalid spend occurred. Zcash uses shielded notes, commitments, nullifiers, and zero-knowledge proofs so a spend can be validated without publicly revealing which note was spent. These are still cryptocurrencies, but they solve the “public verifiability versus user privacy” tension differently.
How does a cryptocurrency transaction work step‑by‑step?
The simplest useful mental model is that a transaction says: “I am authorized to move this value, and here is the new state I want the ledger to reflect.” The network then checks both parts.
Imagine a Bitcoin-style payment. Alice’s wallet has discovered two spendable outputs from earlier transactions. She wants to pay Bob. Her wallet constructs a new transaction that references those earlier outputs as inputs, proves control over them with the appropriate signatures, creates a new output spendable by Bob, and usually creates a second output returning change back to Alice. Nodes that receive the transaction check that the referenced outputs exist, have not already been spent, and satisfy the script or signature conditions. If those checks pass, the transaction is valid for inclusion in a block.
In Ethereum-like systems, the narrative is different but the mechanism rhymes. Alice’s account has a balance and a nonce, where the nonce prevents replay and keeps her transactions in order. She signs a transaction that names a recipient, a value, and often data. The network checks her signature, verifies that her account has enough balance to cover the transfer and fees, and confirms that the nonce is correct. If the transaction calls a smart contract, nodes execute contract code as part of validation.
This is where fees become essential rather than incidental. In Bitcoin, fees help prioritize inclusion and compensate miners. In Ethereum, the gas mechanism does something more general: it prices computation and bounds execution. The whitepaper frames STARTGAS and GASPRICE as part of Ethereum’s anti-denial-of-service model. That matters because a programmable chain must not let arbitrary code consume unlimited network resources for free. More broadly, every cryptocurrency needs some way to ration scarce block space, computation, and bandwidth.
Why do blockchains group transactions into blocks?
If transactions can be checked individually, why group them into blocks? Because the network needs a practical way to order many proposed state changes and agree on which batch extends the ledger next.
A block is a package of valid transactions plus metadata that links it to prior history. In Bitcoin and many other systems, blocks are hash-linked, so changing an earlier block changes its hash and breaks the chain of references after it. This makes history tampering detectable. More importantly, blocks give the network a rhythm: transactions are collected, proposed, validated, and then attached to the ledger in chunks rather than as a constant stream of individually finalized events.
The block also becomes the unit around which the consensus mechanism works. In proof-of-work systems, miners compete to produce a block meeting the protocol’s difficulty target. In proof-of-stake systems, validators are selected and coordinated to propose and attest to blocks according to stake-weighted rules. In BFT-style systems such as Tendermint, validators vote on blocks and a block is committed once signatures from more than two-thirds of validator weight are gathered. The details differ sharply, but the purpose is the same: turn a noisy, adversarial network into a sequence of agreed state transitions.
Once this clicks, you can see why “cryptocurrency” is inseparable from the ledger and consensus beneath it. The asset is not a free-floating object. It is the native unit defined by the protocol’s state machine. BTC exists within Bitcoin’s ledger rules. ETH exists within Ethereum’s. Native assets are different from tokens created by smart contracts on top of an existing chain. An ERC-20 token, for example, follows a standard contract interface for balance and transfer logic on Ethereum, but it ultimately depends on Ethereum’s base chain for execution and security.
How do blockchain consensus mechanisms reach agreement and what are the tradeoffs?
| Consensus type | Mechanism | Security model | Finality | Main trade-off |
|---|---|---|---|---|
| Proof-of-work | mining, hash puzzle | accumulated computational work | probabilistic, improves with confirmations | high energy use |
| Proof-of-stake | bonded validators, attestations | economic stake and slashing | faster, often checkpointed | stake centralization risk |
| BFT-style | voting by validator set | safety if <1/3 faulty | instant/deterministic finality | limited validator scale |
Consensus is where many introductions become too slogan-like. “The network agrees” is true, but incomplete. The useful question is: under what assumptions, by what mechanism, and with what tradeoffs?
Bitcoin’s answer is proof of work. Miners assemble candidate blocks and expend computational effort to find a valid block hash below a target threshold. Because producing blocks is costly and verifying them is cheap, the chain with the most accumulated work becomes the focal point for agreement. This design is elegant because it ties history revision to real resource expenditure. But that same mechanism is energy-intensive, and finality is probabilistic rather than instant: a transaction becomes harder to reverse as more work accumulates on top of it.
Ethereum began with proof of work but later changed its consensus mechanism. The Merge joined Ethereum’s execution layer with the Beacon Chain consensus layer and replaced mining with proof of stake. After that transition, validators rather than miners became responsible for block production and confirmation. The Merge changed consensus and sharply reduced energy consumption, but it did not by itself expand base-layer capacity or lower gas fees. That distinction matters because consensus choice affects security and coordination, while throughput depends on additional design constraints.
Proof of stake changes the mechanism of security from expended energy to bonded capital. Validators put value at risk, participate in proposing and attesting to blocks, and can be penalized for certain forms of misbehavior. The attraction is obvious: far lower energy use and often more flexible protocol design. The hard part is making sure the incentives, slashing conditions, fork-choice rules, and recovery mechanisms still preserve safety and liveness under attack or network disruption.
Not every proof-of-stake family works alike. Tendermint-style systems use weighted validator sets and explicit commits from more than two-thirds of voting power, producing a stronger notion of finality once a block is committed. Solana combines proof of stake with Proof of History, a mechanism for cryptographically encoding ordering and passage of time to reduce coordination overhead. These are not just branding differences. They reflect different answers to the same first-principles problem: how does a decentralized system order events and resist conflicting histories?
What determines a cryptocurrency’s value: protocol rules or market demand?
This is partly a technical question and partly an economic one. Technically, a cryptocurrency’s scarcity comes from protocol rules: issuance schedules, validation rules, and the network’s refusal to accept invalid inflation. Bitcoin’s monetary credibility, for instance, depends on nodes enforcing the same consensus rules. If software diverges from consensus, users no longer share the same money.
Economically, value depends on demand for the asset’s role inside or around the network. That role can vary. A cryptocurrency may be used as a payment asset, a reserve asset, collateral, a staking asset, a fee token, or the base asset required to interact with applications on the chain. ETH, for example, is not just a transferable asset; it is also the asset used to pay for computation on Ethereum. That gives it a structural role in the system beyond simple exchange.
This is why the distinction between native cryptocurrency and token matters. A native asset is built into the chain’s consensus and fee logic. A token, such as an ERC-20 asset, is defined by a smart contract interface running on top of the chain. The token may have market value, but its existence depends on the host chain’s rules and continued operation. If the base chain stops finalizing transactions, token balances cannot update either.
None of this means market price is easy to justify from first principles. A cryptocurrency can be technically sound and still poorly adopted. It can be widely used and still be volatile. Protocol-level scarcity explains why an asset cannot be inflated arbitrarily by honest nodes, but it does not guarantee stable purchasing power. That is why stablecoins emerged: they are crypto assets in form, but they aim to behave like fiat proxies in price.
How did smart contracts and programmability change cryptocurrency use and risk?
Bitcoin showed that a decentralized network could maintain a scarce digital asset. Ethereum broadened the idea by making the ledger programmable. Instead of asking only whether a coin transfer is valid, the network can execute code that updates arbitrary on-chain state under shared rules.
That turns cryptocurrency from a single-purpose payment instrument into a more general economic substrate. Tokens, exchanges, lending protocols, DAOs, NFTs, and many other constructions become possible because the same consensus system that tracks balances can also track contract state. The Ethereum whitepaper describes this as a blockchain with a built-in Turing-complete programming language for encoding arbitrary state transition functions. The important practical consequence is not the phrase “Turing-complete” by itself. It is that users can interact with applications whose rules are enforced by the chain rather than by an application server.
But programmability creates new failure modes. Bugs in smart contracts can lock or lose funds. Computation must be metered. State growth creates scaling pressure. And greater expressive power often expands the attack surface. So while programmable cryptocurrency systems are more flexible, they are also harder to secure in practice.
A useful modern example of cryptographic control beyond a single key is threshold signing for settlement. Cube Exchange uses a 2-of-3 threshold signature scheme for decentralized settlement: the user, Cube Exchange, and an independent Guardian Network each hold one key share, no full private key is ever assembled in one place, and any two shares are required to authorize a settlement. This is not a different cryptocurrency altogether; it is a concrete way cryptographic custody and authorization can be structured on top of cryptocurrency rails to reduce single-point-of-failure risk.
What assumptions and failure modes do cryptocurrencies rely on?
Cryptocurrency is often described as trustless, but that word can mislead. The better claim is that it reduces and restructures trust. You do not need to trust a bank to maintain the ledger, but you still depend on assumptions: that cryptographic primitives remain hard to break, that enough honest or economically aligned participants enforce consensus, that your wallet protects your keys, that client software is correct, and that network conditions are not catastrophically adversarial for too long.
Different designs fail in different ways. In transparent systems, privacy may be weaker than newcomers expect because transaction graphs are public. In privacy-preserving systems, usability, proof costs, or metadata leakage may create tradeoffs. In proof-of-work systems, energy cost and mining concentration matter. In proof-of-stake systems, validator concentration, governance over upgrades, and slashing design matter. In smart-contract systems, application risk can dominate base-layer risk.
Operational reality matters too. Official Bitcoin Core advisories, for example, include ordinary software risks such as wallet bugs and implementation vulnerabilities. That is a useful reminder that a cryptocurrency protocol can be conceptually sound while actual users remain exposed to failures in clients, infrastructure, integrations, or custody practices.
And decentralization is not binary. A system can be decentralized in block production but concentrated in client software. It can be decentralized at the protocol layer but highly centralized at the exchange layer where many users actually hold assets. Understanding cryptocurrency requires keeping these layers separate.
What are the common real‑world uses for cryptocurrencies today?
| Use case | Typical chains | Why chosen | Trade-off |
|---|---|---|---|
| Store of value | Bitcoin | scarcity and security | low throughput, volatile |
| Programmable settlement | Ethereum, smart-contract chains | on-chain execution, composability | contract risk, higher fees |
| Private payments | Monero, Zcash | sender/amount confidentiality | regulatory scrutiny, usability |
| High-throughput execution | Solana, Cosmos app-chains | low latency, high TPS | weaker decentralization risk |
People use cryptocurrencies because they make several things possible at once: bearer-style digital ownership, globally accessible settlement, programmable assets, and in some systems stronger financial privacy. Which of these dominates depends on the chain.
Bitcoin is still widely understood primarily as a scarce digital asset and payment network with a conservative protocol culture. Ethereum is often used as a programmable settlement layer where ETH pays for execution and supports an ecosystem of tokens and contracts. Cosmos-style chains emphasize app-specific blockchains built from modular components. Solana emphasizes high-throughput execution. Monero and Zcash emphasize privacy, though by different mechanisms. These are all variations on cryptocurrency, but they optimize for different consequences of the same core architecture.
The point is not that cryptocurrency has one universal use. The point is that once you can maintain scarce digital state without a central ledger owner, many financial and organizational uses become possible. Some are durable. Some are speculative. Some depend heavily on law, market structure, or user behavior beyond the protocol itself. The protocol provides the machinery; it does not determine every social outcome.
Conclusion
A cryptocurrency is digital value maintained by a distributed ledger and enforced by cryptography plus consensus. The essential idea is not the coin graphic, the exchange price, or even the chain name. It is the mechanism that lets many parties maintain one shared answer to who owns what without handing that power to a single intermediary.
If you remember one thing tomorrow, remember this: cryptocurrency is a way of making digital scarcity credible in an open network.
Everything else is built around that problem and the different ways protocols try to solve it.
- wallets
- mining
- staking
- tokens
- privacy features
- smart contracts
What should I understand before using cryptocurrency infrastructure?
Understand the core infrastructure assumptions (finality, custody, smart contract risk, and fee mechanics) before you fund, trade, or transfer crypto. On Cube Exchange you can verify the asset and network, fund your account, and execute trades or transfers using the same workflow while applying those checks.
- Fund your Cube account with fiat or a supported crypto transfer and pick the exact network (e.g., ERC‑20 vs. Polygon) you intend to use.
- Verify the asset and contract address on Cube against the project’s official sources and audit reports before depositing any tokens.
- Check chain‑specific confirmation/finality guidance (for example, wait ~6 confirmations for Bitcoin or the chain’s documented finality threshold) and wait for that threshold before relying on a deposit.
- Open the market or transfer flow on Cube, choose an order type (use a limit order for large or illiquid assets to control price; use a market order for immediate fills), set slippage/fee preferences, review estimated fees and gas, then submit.
Frequently Asked Questions
They combine cryptographic signatures (to prove authorization), a public ledger structure (to record spendable outputs or account state), and a distributed consensus mechanism that orders and finalizes which signed transfers count; nodes reject transactions that would double-spend because the canonical history (agreed by consensus) shows the outputs or balances were already spent. (Article explains this with the roles of cryptography, ledger structure, and consensus.)
UTXO (used by Bitcoin) records discrete spendable outputs that transactions consume and create, which maps conceptually to cash and can make some parallel validation simpler; the account model (used by Ethereum) stores balances and nonces per account and updates them directly, which is more convenient for general-purpose programming and contracts. Neither is universally superior - they reflect tradeoffs between validation patterns and ease of expressing on-chain state. (Article compares UTXO and account models and their tradeoffs.)
Fees ration scarce block space, bandwidth, and computation and compensate validators/miners; Ethereum’s gas mechanism generalizes fees by pricing computation and bounding execution (the whitepaper frames STARTGAS and GASPRICE as part of an anti‑DoS model). (Article explains fees and the gas concept.)
Proof of work makes history revision costly and gives probabilistic finality but is energy‑intensive, while proof of stake replaces energy cost with bonded capital and can reduce energy use and enable different safety/finality tradeoffs; Tendermint‑style BFT gives a stronger notion of finality once >2/3 of validator weight commits. Ethereum’s Merge replaced PoW with PoS and the roadmap cites a very large (≈99.95%) reduction in energy consumption. (Article describes PoW/PoS and Tendermint; roadmap/evidence notes the Merge and the cited energy reduction.)
Not exactly - cryptocurrency reduces and restructures trust but does not eliminate it: you still rely on assumptions that cryptography remains secure, that enough honest or economically aligned participants enforce consensus, that your wallet and client software behave correctly, and that network conditions don’t remain adversarial indefinitely. (Article explicitly frames cryptocurrency as reducing/restructuring trust and lists these remaining assumptions.)
Partly technical scarcity comes from protocol rules (issuance schedules and consensus enforcement), and partly value comes from economic demand for roles the asset plays (payments, staking, collateral, paying fees, etc.); native assets are embedded in a chain’s consensus and fee logic while tokens are smart‑contract constructs that depend on the host chain’s continued operation. (Article discusses protocol scarcity, economic roles, and the native vs token distinction.)
Programmability lets the chain enforce arbitrary application rules, enabling tokens, lending, and complex contracts, but it also introduces new failure modes: bugs in contracts can lock or lose funds, computation must be metered (hence gas), state growth pressures scaling, and the attack surface expands compared with a simple payment chain. (Article discusses how programmability broadened functionality and introduced these risks.)
Monero uses one‑time addresses and ring signatures so observers cannot easily link senders, receivers, and amounts while still permitting validity checks; Zcash uses shielded notes, commitments, nullifiers, and zero‑knowledge proofs so a spend can be validated without revealing which note was spent - both aim for privacy but use very different cryptographic constructions and have different usability and metadata tradeoffs. (Article summarizes these approaches; Monero and Zcash specs provide the implementation details cited.)
A native cryptocurrency is implemented in a chain’s consensus and fee mechanics (so its issuance and finality are enforced by base‑layer nodes), whereas a token (e.g., an ERC-20) is a smart contract that records balances on top of that chain and therefore depends on the base chain’s execution and security for its existence and transfers. (Article explains the native vs token distinction and uses ERC‑20 as an example.)
Related reading