What Are Shielded Transactions?
Learn what shielded transactions are, how they use commitments, nullifiers, and zero-knowledge proofs, and where their privacy holds or breaks.
Introduction
Shielded transactions are blockchain transactions that keep key details hidden while still letting the network verify that the transfer is valid. That sounds almost contradictory at first. Public blockchains work because many independent nodes can inspect transactions and reject invalid ones. So if the sender, receiver, and amount are hidden, what exactly are validators checking?
That question is the heart of the topic. A normal blockchain transaction is easy to reason about because its logic is mostly visible: these coins came from here, they go there, and the amounts add up. A shielded transaction changes the verification model. Instead of asking the network to inspect the transaction’s contents directly, it asks the network to verify proofs about hidden contents. The important shift is from seeing the facts to checking a proof that the facts satisfy the rules.
This idea exists because transparent ledgers leak much more than many people first expect. Even when addresses are pseudonymous, repeated activity often lets observers reconstruct relationships, balances, spending habits, business flows, and timing patterns. Shielded systems aim to break that visibility. In the strongest form, they try to hide the origin, destination, and amount of a payment while preserving the two things a currency cannot give up: no double-spending and no money creation.
The best-known implementation is Zcash, whose shielded pool is built around zk-SNARKs, note commitments, and nullifiers. But the broader idea is not specific to one chain. You also see related designs in systems that store encrypted UTXOs and prove state transitions privately, such as privacy-focused rollups. The details vary, but the core problem is the same: how do you get public verification without public transaction data?
What privacy problem do shielded transactions solve?
| Model | What is revealed | How verification works | Privacy level | Main trade-off |
|---|---|---|---|---|
| Transparent (Bitcoin‑like) | addresses, amounts, inputs/outputs | Nodes recheck inputs, signatures, amounts | Low (linkable) | Simple auditing but full exposure |
| Shielded (Zcash‑style) | commitments, nullifiers, fees | Zero‑knowledge proofs over hidden data | High when fully shielded | Stronger privacy, higher crypto complexity |
A blockchain has to maintain a simple invariant: value cannot be spent twice, and it cannot appear from nowhere. In Bitcoin-like transparent systems, the way to enforce that invariant is straightforward. Every input points to a previous output, every signature is public, every amount is public, and every node can recompute the balance equation for itself.
The privacy cost of that design is not accidental. It comes from the mechanism itself. If everyone must verify that a particular output is being spent, then everyone learns which output is being spent. If everyone must verify the amount conservation directly, then everyone learns the amounts. Transparency is doing double duty: it gives both correctness and auditability, but it does so by exposing user activity.
Shielded transactions try to keep the correctness while removing the exposure. That means replacing public transaction data with cryptographic objects that preserve just enough structure for validation. The network still needs to know that the spent object existed, that the spender was authorized, that the same object has not been spent before, and that the hidden input values equal the hidden output values plus any public fees or transparent transfers. What changes is how those facts are demonstrated.
This is why shielded transactions are not just “encrypted transactions.” Simple encryption would hide data from observers, but it would also hide it from validators. A blockchain cannot rely on validators saying, “we cannot see inside this transfer, but we will trust it anyway.” The system has to remain trustless. So the real achievement is not secrecy by itself; it is verifiable secrecy.
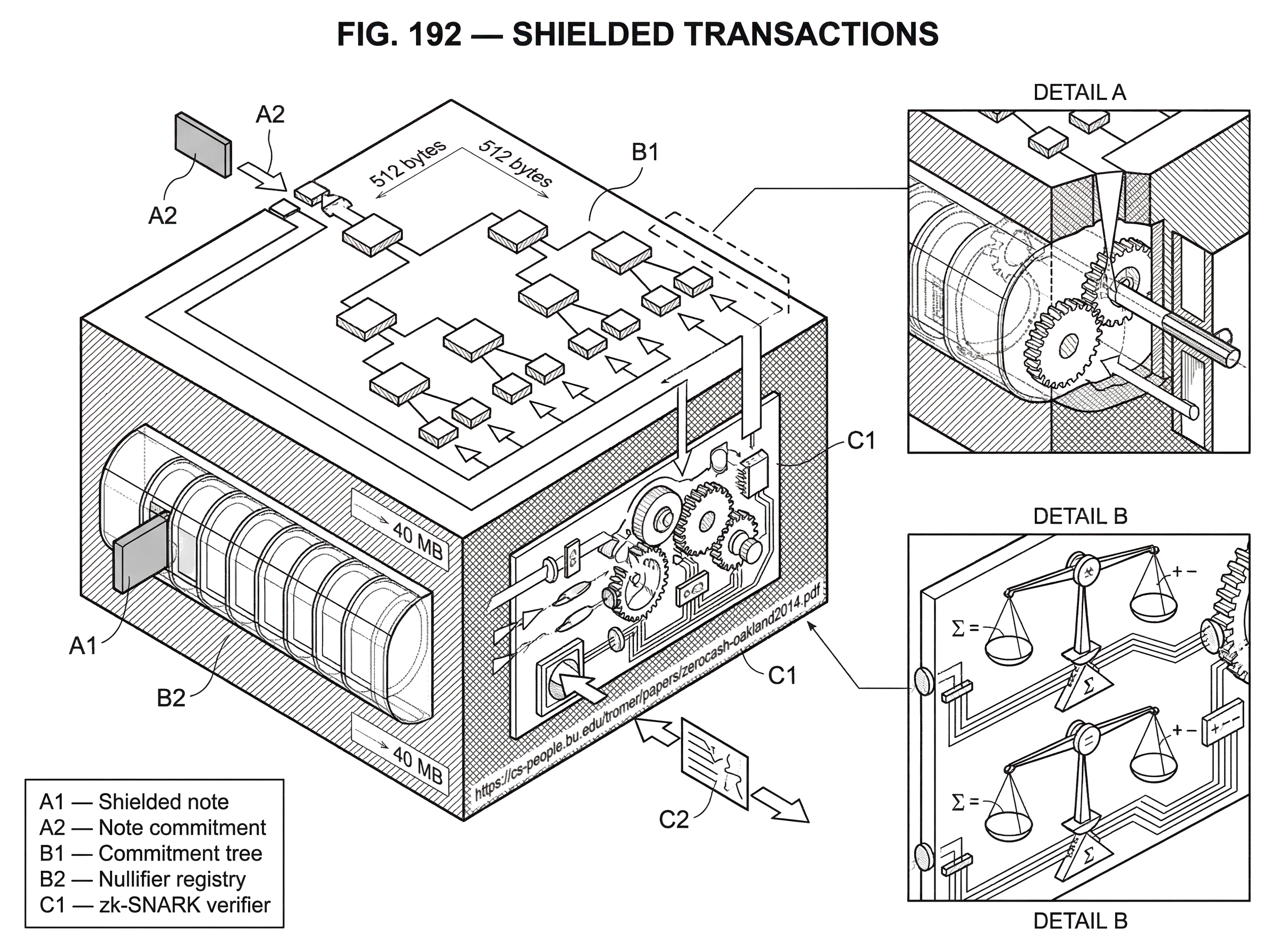
How do commitments, nullifiers, and zero‑knowledge proofs work together?
The easiest way to understand a shielded transaction is to stop thinking in terms of visible coins and start thinking in terms of hidden notes. In Zcash’s design, a note is the unit of shielded value. A note represents an amount that can be spent by whoever holds the corresponding spending key for a shielded address.
When a note is created, the blockchain does not publish the note’s plain contents. Instead, it publishes a commitment to that note. A commitment is a cryptographic object that fixes the note’s contents without revealing them. You can think of it as a sealed, tamper-evident envelope: the chain can store the envelope and later verify statements about what is inside, but observers do not get to open it. The analogy is useful because it captures two important properties at once: the contents stay hidden, and the sender cannot later change them. Where it fails is that real commitments support efficient mathematical proofs in ways paper envelopes do not.
These commitments are appended to a commitment tree, typically a Merkle tree or similar authenticated structure. That tree matters because later, when someone spends a note, they need to prove that their hidden note corresponds to a commitment already present in the ledger. The network does not learn which exact commitment in the tree is theirs. It only learns that some commitment in the accepted tree corresponds to a valid note they are authorized to spend.
But existence is only half the story. A hidden note also must not be spendable twice. Transparent systems solve this by making the spent output itself visible: once the chain sees it referenced, everyone knows it is gone. Shielded systems cannot do that, because revealing the note would destroy privacy. Instead, when a note is spent, the transaction reveals a nullifier. A nullifier is a unique value derived from the note and the spender’s key material. It is designed so that the same note always yields the same nullifier, but the nullifier does not reveal which note it came from.
That lets the network maintain another simple set: all nullifiers seen so far. If a new transaction presents a nullifier already in the set, it is invalid as a double-spend. So the chain never needs to know which note was spent. It only needs to know that this note’s unique one-time spending marker has not appeared before.
Put these pieces together and the pattern becomes clear. Commitments let the chain remember hidden outputs. Nullifiers let the chain reject repeated spending of hidden inputs. A zero-knowledge proof ties the two together by proving that the spender knows a real note in the commitment tree, is authorized to spend it, derived the nullifier correctly, and preserved value; all without revealing the note itself.
How does a shielded payment work step‑by‑step?
Imagine Alice has previously received a shielded note worth 5 units. On-chain, nobody sees “Alice owns 5.” What the chain contains is a commitment to a note whose contents include that value and recipient information, plus encrypted data that lets the intended recipient detect and recover the note.
Now Alice wants to pay Bob 3 units privately. In a transparent system, the transaction would point directly to Alice’s old output and create visible outputs for Bob and for Alice’s change. In a shielded system, Alice instead constructs a proof about hidden objects. She proves that she knows a note already committed in the ledger, that she has the spending authority for it, and that the note’s value is sufficient to fund the transaction. She also creates new hidden notes: one for Bob worth 3 and one for herself worth 2 as change. The chain sees commitments for these new notes, but not their plain amounts or recipients.
To prevent reuse of the 5-unit note, Alice reveals its nullifier. Validators check only two public facts about that nullifier: it is well-formed according to the proof, and it has never appeared before. They also verify the transaction’s proof and any required signatures that bind the hidden arithmetic to the rest of the transaction. If everything checks out, the old hidden note is now effectively consumed, and the two new hidden notes become part of the commitment tree.
Bob still needs to learn that he was paid. That is handled by encrypted note data carried in the transaction. The chain can store ciphertext publicly because only Bob, or anyone Bob authorizes via appropriate viewing capability, can decrypt the note intended for him. Zcash notes also include an encrypted memo field of 512 bytes, whose meaning is up to sender and recipient. The important point is that discovery of incoming payments shifts from “my address appears publicly on-chain” to “I scan ciphertexts and detect notes I can decrypt.”
Nothing in that process required the chain to expose sender, receiver, or amount in the clear. But nothing was left to trust either. The ledger’s integrity still comes from consensus checks, just checks over proofs and commitments rather than open transaction data.
How can validators check amounts if transaction values are hidden?
The hardest part to make intuitive is usually amount conservation. If amounts are hidden, how can validators know that inputs equal outputs plus fees? This is where value commitments enter.
In modern Zcash shielded transfers, hidden amounts are represented using homomorphic Pedersen commitments. “Homomorphic” means these commitments can be added and subtracted while preserving the committed arithmetic. That gives the system a way to check a balance equation without opening the values themselves. If the sum of committed input values minus the sum of committed output values equals the public adjustment required by transparent transfers and fees, the transaction can be accepted.
That sounds abstract, so here is the mechanism in plainer language. Instead of revealing, “this input is 5 and these outputs are 3 and 2,” the transaction carries cryptographic commitments to 5, 3, and 2. Those commitments are constructed so that combining them algebraically mirrors combining the hidden numbers. The prover then shows, together with the zero-knowledge proof and a binding signature, that the resulting net commitment matches the publicly visible balance effects. Validators learn that the arithmetic is correct, but not the hidden operands.
This is one of the central design achievements of shielded systems. Without it, you could hide ownership or hide recipients, but not amounts. With it, the system can preserve the currency invariant (no inflation, no imbalance) while keeping values confidential.
Why are zk‑SNARKs commonly used for shielded transactions?
| Proof type | Proof size | Verify speed | Trusted setup | Best fit |
|---|---|---|---|---|
| zk‑SNARK | very small, constant | very fast | often yes (one‑time setup) | Compact on‑chain proofs |
| zk‑STARK | larger; grows with circuit | fast verification | no trusted setup | Transparent, post‑quantum proofs |
| Bulletproofs | moderate; scales with circuit | slower verify | no trusted setup | Range proofs, moderate privacy use |
The phrase most associated with shielded transactions is zk-SNARK: a zero-knowledge succinct non-interactive argument of knowledge. The shortest useful explanation is that it lets a prover convince everyone else that a complicated statement is true, without revealing the private witness that makes it true, and with a proof small enough and fast enough to verify on-chain.
Succinctness is not a cosmetic feature here. It is what makes private verification practical in a blockchain environment. If private proofs were enormous or slow to verify, every private payment would impose unacceptable bandwidth and validation costs on the network. Zerocash, the research system that strongly influenced Zcash, showed that direct anonymous payments could be made practical by using zk-SNARKs to compress the proof of transaction correctness into something compact and quickly verifiable.
This was a major step beyond earlier privacy constructions such as Zerocoin. Zerocash added variable amounts, direct payments to fixed addresses, and hidden balances, while also drastically reducing transaction size and verification time relative to that earlier approach. In the paper’s framing, the goal was a decentralized anonymous payment scheme: a system where origin, destination, and transferred amount are hidden, yet the ledger remains secure.
There is, however, an important trust-model caveat. Early zk-SNARK systems required a one-time trusted setup to generate public parameters. If that setup were corrupted, soundness could be endangered; in plain terms, the system’s protection against accepting false proofs could fail. The Zerocash paper explicitly notes this tradeoff. Later systems and upgrades have changed the proving machinery, but the broader lesson remains: privacy technologies do not rest only on elegant abstractions; they depend on concrete cryptographic instantiations and operational assumptions.
How did Zcash evolve its shielded design from Sprout to Sapling to Orchard?
Zcash is the canonical case study because it shows that shielded transactions are not one fixed object but an evolving family of designs.
The earliest shielded design in Zcash used JoinSplit descriptions in the Sprout era. A JoinSplit bundled shielded inputs and outputs into a specific transfer form. This worked, but it was relatively heavy and less flexible. Later, Sapling replaced that structure with separate Spend and Output descriptions, which made the model more modular and, more importantly, much more efficient in practice.
That efficiency shift mattered because privacy that is too expensive to use is privacy that will remain niche. The Sapling upgrade was explicitly aimed at making shielded transactions feasible for mobile devices, exchanges, and wallets with tighter resource budgets. Official project materials describe Sapling payments as constructible in as little as a few seconds with about 40 MB of memory. Sapling also introduced improved viewing capabilities and allowed proof construction to be separated from transaction signing, which is useful for hardware security designs.
More recently, Orchard introduced Action descriptions, where each action can optionally perform a spend and/or an output. The exact consensus encoding is protocol-specific, but the bigger point is architectural: shielded transaction design continues to move toward better efficiency, clearer abstraction boundaries, and more usable key-management models.
This history is not just implementation trivia. It shows what the real bottleneck often is. The cryptographic idea may be sound, but if proofs are too slow, memory-hungry, or awkward to integrate into wallets, then users default back to transparent behavior, shrinking the privacy set for everyone else.
When is shielded privacy strongest, and when does it break?
| Flow type | On‑chain visibility | Typical privacy | Deanonymization risk | When to use |
|---|---|---|---|---|
| z → z | commitments only; no addresses | Strong (sender/receiver/amount hidden) | Low if many users use it | End‑to‑end private payments |
| t → z (shielding) | source transparent; new note committed | Partial; source exposed | High if later deshielded quickly | Move funds into shielded pool |
| z → t (deshielding) | destination transparent; nullifier revealed | Weak for unlinkability | High especially with matching amounts/timing | Cash out or send to exchanges |
| t → z → t (round‑trip) | both endpoints transparent; shielded middle | Often defeats privacy gains | Very high; linkable by heuristics | Avoid when privacy is goal |
A common misunderstanding is to hear “shielded transaction” and assume complete invisibility. That is too strong.
In Zcash, the strongest privacy claim applies to fully shielded z-to-z transfers. The protocol specification states the core privacy basis plainly: when a note is spent, the spender proves that some commitment exists in the ledger without revealing which one, implying that a spent note cannot be linked to the transaction that created it. But this is not a claim that all useful metadata disappears.
Some information can still remain visible at the transaction layer or emerge from surrounding context. Developer documentation notes that even shielded transactions still appear on the public blockchain as transactions, and fees are known. More importantly, interactions between transparent and shielded pools can create strong linkage opportunities. A t-to-z shielding step followed soon after by a z-to-t deshielding step of the same or nearly the same amount may be highly linkable even if the funds briefly entered the shielded pool.
Empirical studies of Zcash have shown exactly this problem. Research on round-trip transactions found that many flows into shielded addresses later returned to transparent addresses in ways that made them linkable by timing and amount heuristics. Other analyses found that low overall usage of the shielded pool and regular behavioral patterns by large actors could significantly shrink the effective anonymity set. The protocol can offer strong cryptographic privacy, yet deployed privacy can still be weakened by user behavior, wallet defaults, exchange support, and traffic patterns.
So the right way to think about shielded privacy is not “hidden or not hidden” but how much identifying structure is left around the hidden core. The cryptography may prevent direct linkage of spends to prior note commitments. But if the transaction flow around that shielded core is sparse, repetitive, or partially transparent, observers may still infer relationships probabilistically.
How do view keys and selective disclosure work with shielded funds?
If shielded transactions hid everything with no exceptions, they would be difficult to use in many real settings. Recipients need to detect payments. Wallets need to sync. Sometimes users or institutions need to share transaction details with an auditor, exchange, or counterparty without handing over spending power.
This is why systems like Zcash include view keys. A viewing key gives read access to some transaction information without granting authority to spend funds. In Sapling, full viewing keys were designed to let owners inspect incoming and outgoing shielded transaction details while keeping the spending key separate.
This matters conceptually because it shows privacy and disclosure are not a binary pair. A good shielded design tries to make public disclosure the default to nobody, then permit selective disclosure to specific parties under the user’s control. That is a very different model from transparent ledgers, where everyone gets the data automatically and users can only try to recover privacy through obfuscation.
How do shielded transaction designs differ across chains and rollups?
Although Zcash is the canonical example, the design pattern shows up elsewhere. On privacy-focused rollups such as Aztec, private state is represented as encrypted UTXOs that only the owner can decrypt, and private functions are executed and proved on the user’s device. The surrounding architecture is different because this happens in an L2 environment rather than a standalone base-layer currency, but the underlying move is familiar: store hidden state commitments on-chain, let owners recover the private contents off-chain, and use zero-knowledge proofs so the network can accept state transitions without seeing confidential data.
That comparison helps separate what is fundamental from what is conventional. What is fundamental is the trio of hidden state, public commitments, and validity proofs. What is conventional is the exact proof system, transaction encoding, tree structure, address scheme, or whether the system lives on a base chain or rollup.
A useful contrast is Monero’s RingCT. RingCT also hides transaction amounts and aims to obscure origins and destinations, but it reaches privacy through a different combination of cryptographic tools, notably ring-signature-based constructions rather than the specific zk-SNARK note-commitment/nullifier model used by Zcash. The comparison is not about picking a winner here. It clarifies that “shielded transactions” names a problem class and a family of solutions, not a single protocol recipe.
What can break shielded transaction security, and which assumptions matter?
The security of shielded transactions depends on several layers holding at once.
At the protocol level, consensus rules must be implemented correctly. The Zcash specification is explicit that security depends critically on following consensus; divergence, bugs, or unexpected network behavior can destroy security. This is especially important because shielded systems are harder to inspect manually than transparent ones. A bug in proof verification, nullifier handling, or commitment logic can have consequences that are difficult to detect from public chain data alone.
At the cryptographic level, the chosen proof system and supporting primitives must actually deliver the claimed properties. The specification itself notes that it does not prove every concrete primitive choice is sufficient in every case. The history here matters: pre-Sapling Zcash used an earlier proving system that was later disclosed to have had a serious flaw that could potentially have enabled counterfeiting, even though the project stated it believed no such exploitation occurred. That incident is a reminder that the privacy layer and the integrity layer are inseparable. If soundness fails, private money can become untrustworthy money.
At the implementation level, wallet software and client behavior matter. Privacy-preserving protocols often push complexity toward key management, note scanning, proof construction, and local state tracking. That creates room for ordinary software failures, side channels, and metadata leaks even if the core protocol is sound. The broader privacy-coin ecosystem has seen wallet-level failures that did not break the protocol itself but still caused severe practical harm.
And at the usage level, anonymity depends on crowd size and behavior. If only a small minority of users transact privately, the anonymity set is thin. If users repeatedly enter and leave the shielded pool in recognizable ways, they create linkable edges around the private interior. Privacy is therefore partly a property of the protocol and partly a property of the surrounding ecosystem.
Conclusion
Shielded transactions are a way of making a public blockchain verify private payments. They do that by replacing visible transaction contents with commitments, nullifiers, and zero-knowledge proofs: the chain remembers hidden outputs, blocks double-spends of hidden inputs, and checks that the concealed arithmetic still obeys the currency rules.
The idea matters because transparent verification leaks financial graphs by default. Shielded systems change that default. But their privacy is strongest when use is genuinely shielded end-to-end, widely adopted, and carefully implemented. The short version to remember is this: a shielded transaction does not ask the blockchain to trust what it cannot see; it asks the blockchain to verify, cryptographically, what it does not need to see.
What should you understand before using shielded transactions?
Understand the privacy trade-offs and the network support you need before using shielded flows, then use Cube Exchange to fund and execute the transfer or trade. On Cube you fund your account, open the relevant transfer or market flow for the asset, and choose the shielded or transparent option that matches your privacy needs.
- Fund your Cube account with fiat or a crypto transfer, choosing the correct network (for example, ZEC on Zcash mainnet vs. an ERC‑20 wrapper) when you send funds.
- Open Cube's transfer or withdraw flow for the asset and select the shielded (z) transfer option if the chain and destination support it; confirm the destination accepts shielded addresses.
- Prefer fully shielded (z→z) transfers for stronger privacy; if you must move between shielded and transparent pools, avoid immediate round‑trips and use a limit order when trading to reduce timing‑based linkability.
- Review on‑chain details and confirmations (confirm chain finality and nullifier visibility), and if you need selective auditability, generate and securely share a viewing key or encrypted memo only with the intended auditor or counterparty.
Frequently Asked Questions
Commitments record hidden notes on-chain (typically in a Merkle-style commitment tree) without revealing their contents; when a note is spent the spender reveals a nullifier, a unique spending marker that cannot be linked back to the note by itself; a zero-knowledge proof then demonstrates that the spender knows a committed note, is authorized to spend it, derived the revealed nullifier correctly, and preserved value - all without revealing the note’s plaintext.
Shielded systems use homomorphic value commitments (for example, Pedersen commitments) so committed amounts can be algebraically combined; the prover shows in zero‑knowledge that the sum of committed inputs minus committed outputs equals the public net change (fees or transparent transfers), letting validators check balance without learning the hidden amounts.
Early zk‑SNARK constructions required a one‑time "trusted setup" to generate public parameters; if that setup is compromised it can undermine soundness (potentially allowing false proofs or counterfeiting), which is why the trusted‑setup requirement and its mitigation (e.g., multi‑party ceremonies or later proving systems) are an important trust assumption to consider.
No - cryptographic privacy is strongest for fully shielded z‑to‑z flows, but metadata like transaction timing, fees, the fact a transaction occurred, and links between transparent↔shielded operations can enable probabilistic linkage; empirical studies of Zcash have shown heuristics that recover substantial linkages when usage is sparse or patterns are repetitive.
Senders include encrypted note data (ciphertexts and an optional encrypted memo) in the transaction; recipients (or holders of the appropriate viewing capability) scan and try to decrypt these ciphertexts, which is how a recipient detects and recovers a payment even though the chain itself never reveals the recipient.
Zcash‑style shielded transactions use a note‑commitment/nullifier model with zk‑SNARKs, whereas Monero’s RingCT hides amounts and obscures origins using ring signatures and different cryptographic building blocks; both aim for transaction privacy but rely on distinct primitives and trade-offs.
Practical limits include wallet and exchange support (many services still prefer transparent addresses), proof generation and memory costs that historically made shielded use harder, and usability choices that push users toward transparent flows - all of which shrink the effective anonymity set and weaken deployed privacy.
Yes; protocol bugs, incorrect consensus implementation, flaws in the chosen cryptographic instantiation (for example, a broken proving system), or wallet/client errors and side channels can all break either privacy or monetary integrity - the literature documents both a serious pre‑Sapling proving‑system concern and multiple implementation/usage risks.
Succinctness is the main reason zk‑SNARKs became central: they produce small, fast‑to‑verify proofs that make private verification practical on a blockchain, and subsequent protocol upgrades (e.g., Sapling, Orchard, and research into Halo) have focused on reducing prover cost and improving usability so shielded transactions are practical on phones and exchanges.
Related reading