What is Blockchain?
Learn what blockchain is, why it exists, and how blocks, cryptography, and consensus create a shared ledger without a central authority.
Introduction
Blockchain is a way to keep a shared digital record when the participants do not want to hand final control to a single trusted operator. That is the real problem it is trying to solve. A normal database is easier, faster, and cheaper when one organization is clearly in charge. A blockchain becomes interesting only when that assumption breaks: when many parties need a common history, but no one party should be able to rewrite it alone.
That is why blockchains are often misunderstood. People hear “distributed ledger” and imagine the key idea is simply that many computers store the same data. But replication alone does not solve the hard part. If two conflicting updates appear, who decides which one is real? If a malicious participant tries to spend the same asset twice, what stops them? If the record is copied everywhere, why does everyone converge on one history instead of fragmenting into many?
A blockchain answers those questions by combining three ingredients. It uses digital signatures so participants can authorize actions, cryptographic hashes so changes become visible, and a consensus process so the network can settle on one accepted order of updates. Different blockchains implement that consensus differently (proof of work, proof of stake, and Byzantine fault tolerant voting are all examples) but the shared goal is the same: maintain a ledger that is hard to tamper with even though no central administrator is supposed to have the final word.
The most useful way to understand blockchain is not as a buzzword or a product category, but as a mechanism for turning disagreement into a single evolving history. Once that clicks, many other features (blocks, confirmations, validators, miners, smart contracts, forks, and even the limits of the technology) make more sense.
What problem does a blockchain solve for digital assets and trustless coordination?
Suppose Alice wants to transfer a digital asset to Bob. In an ordinary online system, a central service keeps the authoritative ledger. If Alice has 10 units and sends Bob 3, the service subtracts 3 from Alice and adds 3 to Bob. The service also prevents Alice from sending the same 3 units to Carol a moment later. This works because everyone accepts one operator as the source of truth.
Without that operator, the problem changes completely. Digital information is easy to copy. If Alice can send signed messages saying “pay Bob” and “pay Carol,” both messages may look authentic. The issue is not whether Alice signed them. The issue is which message came first, and whether the network as a whole agrees that only one of them should count. This is the classic double-spending problem that Bitcoin’s design was built to address.
So the core task of a blockchain is to produce a shared ordering of valid state changes. In Bitcoin’s original framing, those state changes are transactions transferring coins. In Ethereum’s more general framing, the blockchain can be viewed as a state transition system: there is a current global state, and each valid transaction transforms that state into a new one. The important invariant is that honest participants who process the same accepted history should compute the same resulting state.
That sounds abstract, but the idea is simple. A blockchain is trying to answer one repeated question: given many proposed actions from many participants, in what order should the network accept them, and what does the world look like after applying them? If the network can answer that question reliably, it has a usable ledger. If it cannot, the system is just a noisy collection of messages.
Why are blocks linked together, and how does that make tampering visible?
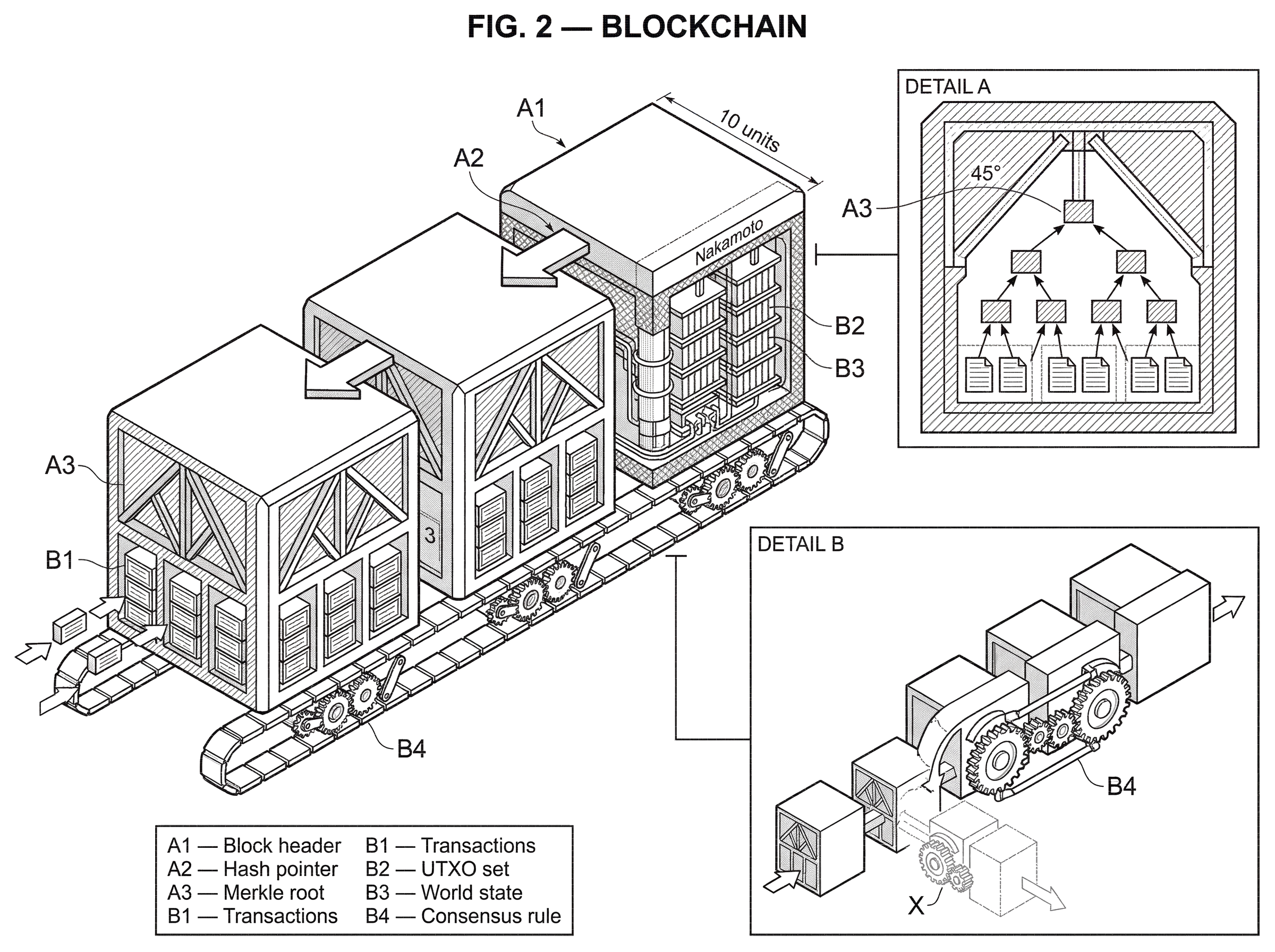
The word blockchain points to the data structure, but the data structure only matters because of the problem above. Transactions are grouped into blocks, and each block includes a cryptographic commitment to the previous block, usually by including the previous block’s hash. That means each new block does not just contain new data; it also reaffirms the history before it.
This creates tamper evidence. If someone edits an old block, its hash changes. That breaks the link in the next block, which in turn breaks the next, and so on. In other words, the chain structure makes history cumulative. The present block indirectly commits to the entire path behind it. NIST’s overview captures this well: blocks are groups of cryptographically signed transactions, and each block is linked to the previous one so modification becomes visible.
But tamper evidence is not the same as impossibility of change. This is a common misunderstanding. A blockchain does not make old data metaphysically unchangeable. It makes changes costly, detectable, and socially difficult to accept. Whether an attempted rewrite succeeds depends on the consensus rules and on who controls the resources that matter in that system. In Bitcoin’s proof-of-work design, rewriting history requires redoing enough work to overtake the honest chain. In BFT-style systems such as Tendermint, conflicting commits would generally require a threshold of validators to violate the protocol, creating both technical and accountability consequences.
So the chain does two jobs at once. It compresses history into a sequence of commitments, and it raises the cost of revision because changing the past means fighting the mechanism that secures the present.
How do digital signatures and node validation create a shared ledger?
Digital signatures are the first ingredient. They let a participant prove that they authorized a transaction without revealing their private key. In Bitcoin’s original model, an electronic coin is described as a chain of digital signatures: each owner signs a transfer to the next owner. That solves the question of authorization. It tells the network who approved this transfer.
But signatures alone do not solve the question of uniqueness. Alice can sign two conflicting transfers. Both signatures may verify correctly. The network still needs a way to decide which valid-looking transaction becomes part of the accepted history.
That is why a blockchain needs more than cryptography in the narrow sense. It needs a way for independent nodes to converge on one ledger. Nodes validate signatures, transaction format, available balances or spendable outputs, and other protocol rules. Then they need some rule for deciding which proposed block, and therefore which ordering of transactions, becomes canonical.
The exact validation model differs across chains. Bitcoin tracks spendable outputs from past transactions. Ethereum tracks accounts, balances, nonces, and contract storage as part of a world state. Hyperledger Fabric, in a permissioned enterprise setting, uses a different governance and participation model altogether. These differences matter, but they sit on top of the same deeper requirement: independent machines must be able to verify updates and arrive at the same accepted ledger.
How does consensus decide which blockchain history becomes canonical?
| Consensus type | Mechanism | Security assumption | Finality | Resource cost | Best for |
|---|---|---|---|---|---|
| Proof-of-work | mining with difficulty target | honest-majority hashpower | probabilistic (confirmations) | high energy / computation | open permissionless networks |
| Proof-of-stake | stake-weighted block selection | honest-majority stake | eventual or checkpointed | low energy, bonded stake | energy-efficient public chains |
| BFT voting | round-based proposer voting | <1/3 Byzantine validators | deterministic finality | low latency, validator coordination | permissioned / validator-set chains |
If the chain structure answers how history is linked, consensus answers which history wins.
In Bitcoin, the original mechanism is proof of work. Miners collect valid transactions into a block and search for a nonce such that the block hash satisfies a difficulty target. The work is hard to produce but easy to verify. The chain with the greatest accumulated proof of work is treated as the authoritative history. Nakamoto describes this as a kind of one-CPU-one-vote system, though in practice specialized hardware and mining pools changed that economic reality over time.
The reason proof of work helps is not mystical. It makes block production expensive in an externally measurable way. If two competing histories appear, the one with more accumulated work represents more expended computational effort. Honest nodes extend that chain, so coordination pressure pushes the network toward one branch. Security then rests on an assumption: honest participants control the majority of relevant hashing power. If an attacker controls the majority, they can potentially rewrite recent history.
A concrete example helps. Imagine Alice pays Bob in a proof-of-work chain, and Bob sees the transaction included in a block. Bob does not immediately assume the payment is final forever. He waits for additional blocks to be added on top. Why? Because each extra block means an attacker trying to replace that history must catch up by reproducing and surpassing the accumulated work. Bitcoin’s white paper explicitly notes that the probability of a successful catch-up attack drops exponentially as more blocks are added, assuming honest miners control more hash power than the attacker.
Other blockchains keep the same goal but replace the mechanism. Proof-of-stake systems tie block production and voting power to bonded stake rather than computation. The Ouroboros line of research is important here because it tried to give proof of stake security arguments comparable in spirit to those of earlier blockchain protocols, while aiming for better efficiency than proof of physical resources. Ethereum itself began with proof of work and later moved its consensus responsibilities to a proof-of-stake consensus layer, while the execution layer continues to define how transactions change state.
And some systems use explicit validator voting rather than probabilistic longest-chain competition. Tendermint, for example, runs repeated rounds of proposal and voting (propose, prevote, precommit) at each block height. Its safety guarantee depends on fewer than one-third of validators by voting power being Byzantine. Here the mechanism is less “follow the most cumulative work” and more “commit only when a supermajority has explicitly voted.” The result is a different notion of finality and a different operational trust model.
This is the key point: blockchain is not identical to proof of work. Proof of work was the first famous solution to decentralized consensus for an open ledger, but the broader concept is a ledger whose history is maintained by cryptographic verification plus a consensus rule, not by a central database administrator.
How do blockchains act as state machines for transactions and smart contracts?
Once you move beyond simple payments, it helps to stop picturing a blockchain as merely a list of transfers and start picturing it as a machine with a shared state.
Ethereum’s whitepaper makes this explicit. A ledger can be viewed as a state transition system: there is a current state S, and a transaction TX is processed by a transition function that outputs a new state or an error. The execution-layer specification sharpens this further: transactions deterministically transform the world state, and blocks apply sequences of transactions in order.
Why does this framing matter? Because it explains what “smart contracts” really are. They are not magical legal objects. They are on-chain programs that participate in state transitions. An externally submitted transaction can call code, move value, update storage, emit logs, or create new contracts. Every full node re-executes that computation and checks that the resulting state matches the cryptographic commitments in the block header.
This is also where resource pricing becomes necessary. In a pure payment chain, validation is relatively bounded. In a programmable chain, arbitrary code can consume arbitrary computation unless the protocol meters it. Ethereum’s answer is gas: computation and storage usage are charged, and transactions specify limits so execution cannot run forever. Here the mechanism is direct. Metering creates a cost for resource use, and that cost protects the network from denial-of-service behavior and infinite loops.
A worked example makes the state-machine picture concrete. Suppose a user submits a transaction to a Decentralized Exchanges contract to swap one token for another. The transaction is signed by the user, includes a nonce so it cannot be replayed indefinitely, and offers a fee for execution. A node checks that the signature is valid, that the sender can afford the upfront cost, and that the transaction is well formed. When the block producer includes it, every validating node executes the same contract code against the same prior state: balances are checked, reserves are read, output amounts are computed, token balances are updated, and logs are recorded. If all honest nodes start from the same prior state and run the same rules, they should compute the same new state. That reproducibility is what gives the ledger meaning. The block is not trusted because a leader wrote it; it is trusted because the proposed state change can be independently recomputed and verified.
Permissioned vs. permissionless blockchains: which trust model fits your use case?
| Model | Who can join | Consensus needs | Privacy | Throughput | Typical use case |
|---|---|---|---|---|---|
| Permissionless | anyone can read or submit | robust, incentive-driven protocols | public by default | lower, depends on scale | public cryptocurrencies |
| Permissioned | approved parties only | trusted validators, BFT options | can restrict visibility | higher, more predictable | enterprise ledgers |
| Consortium | known organizations together | permissioned with governance | partial privacy possible | moderate to high | industry consortia / shared workflows |
Not all blockchains solve the same social problem, so not all of them make the same design tradeoffs.
A permissionless blockchain is open to anyone who wants to read data, submit transactions, or in many systems participate in block production without prior approval. Bitcoin is the archetype. Public openness increases censorship resistance and reduces dependence on a known operator, but it also creates harsher requirements for consensus, spam resistance, and incentive design because participants may be anonymous and adversarial.
A permissioned blockchain restricts who can maintain the ledger, and often who can read or write to it. Hyperledger Fabric is a standard example of this enterprise-oriented model. The trust assumptions are different from a public cryptocurrency chain. Participants are usually organizations with identities, governance agreements, and operational controls outside the protocol. That can improve throughput, privacy, and predictability, but it means the system is no longer trying to eliminate trust in the same way a permissionless blockchain is.
This distinction matters because many arguments for blockchain only make sense under one model. If all validators are known institutions under contract, you may not need proof of work or open staking. If no one should have admission control, you need stronger protocol-level defenses. So when someone says “blockchain,” an immediate follow-up question should be: open to whom, and trusted by whom?
What does finality mean and how many confirmations are enough to trust a transaction?
People often speak as if a blockchain instantly turns a transaction into permanent truth. In real systems, finality is usually messier.
In longest-chain systems, finality is often probabilistic. A transaction becomes safer as more blocks are built on top of it, because replacing it becomes harder. This is why applications speak of “confirmations.” A payment in the latest block is not as strong as one buried under several more blocks. NIST emphasizes this practical point: transactions are often not treated as confirmed until additional blocks are added because blocks can be overwritten by later consensus.
In many BFT-style systems, finality is closer to deterministic or at least explicit: once a supermajority of validators precommits under the protocol rules, reversing that block would require a threshold of misbehavior rather than just a stronger competing branch. That produces a different user experience and different recovery assumptions.
Either way, the important lesson is that immutability is not absolute. It is an operational property arising from cost, consensus, and social acceptance. Hard Fork can change rules. Bugs in smart contracts can create emergencies, as the DAO exploit showed. The Ethereum Foundation’s response at the time made a crucial distinction: the vulnerability was in the DAO contract, not in Ethereum itself. That incident is a reminder that a secure blockchain does not automatically make every application built on it secure.
What real-world use cases do blockchains support today?
The first successful use case was straightforward: a ledger for digital assets that does not rely on a central payment processor. Bitcoin’s design is explicit about this goal. But once a blockchain can support general state transitions, the space widens.
Ethereum showed that the ledger can hold not only balances but also persistent code and storage, enabling tokens, exchanges, lending systems, collectibles, organizations, and other applications whose rules are executed on-chain. Cosmos-style stacks show another direction: modular frameworks for building application-specific blockchains. Solana’s design pushes toward high-throughput execution by reducing messaging overhead around ordering and time. Polkadot pushes toward a multi-chain architecture where many chains share security and communicate through a relay structure.
These examples matter because they show what is fundamental and what is optional. The fundamental part is a shared, verifiable state history maintained without a single all-powerful writer. What varies is how general the computation is, how consensus works, how quickly finality arrives, who can participate, and whether one chain is the whole system or part of a broader network of chains.
When should you not use a blockchain? Key limits and trade-offs
| Scenario | Centralization | Conflict resolution | Cost / throughput | When to choose |
|---|---|---|---|---|
| Single trusted operator | single authority | operator enforces order | low cost, high throughput | use a traditional database |
| Many mistrusting parties | no single trusted party | protocol-level consensus | higher cost, lower throughput | use a public blockchain |
| Known organizations (consortium) | limited set of validators | contractual governance | moderate cost, good throughput | use a permissioned blockchain |
A blockchain is not a universal replacement for databases. If one trusted organization already controls the data and can resolve disputes, the extra machinery may be unnecessary overhead. Consensus across many nodes is expensive. Replicating execution is expensive. Storing and validating long histories is expensive. The technology earns those costs only when reducing dependence on a central operator is genuinely valuable.
Security also depends on assumptions that can weaken in practice. Proof-of-work systems depend on honest-majority hashing power, yet mining can concentrate. Proof-of-stake systems depend on stake distribution, validator behavior, and slashing or incentive rules. BFT systems often guarantee safety only if fewer than one-third of validators are faulty by voting power, and liveness can fail under partitions or coordinated withholding. These are not footnotes; they are the conditions under which the whole promise works.
Key management is another place where the abstraction meets reality. Control over assets is typically control over private keys. Lose the key and the asset may be unrecoverable. Have the key stolen and the attacker may irreversibly move the asset. A blockchain can remove reliance on a central custodian, but that often means users or institutions must assume more operational responsibility themselves.
Interoperability introduces further risk. As blockchains proliferated, bridges were built to move value and messages across systems. But interoperability often reintroduces trust and new attack surfaces. Recent research surveying cross-chain systems found major losses from bridge hacks, with a large share associated with intermediary permissioned networks and weak key operations. That does not mean cross-chain systems are impossible; it means security does not come for free when leaving a chain’s native trust boundary.
A concise definition: what a blockchain really is
A blockchain is best defined as a distributed, append-oriented ledger whose updates are grouped into blocks, cryptographically linked, independently verifiable, and accepted according to a consensus rule rather than a single administrator’s decision.
Each part of that definition matters. Distributed means many nodes can hold and validate the record. Append-oriented means history is extended rather than casually edited in place. Grouped into blocks means updates are batched into consensus units. Cryptographically linked means later blocks commit to earlier ones, making tampering visible. Independently verifiable means participants can check signatures, transactions, and state transitions for themselves. And accepted according to a consensus rule is what turns many local copies into one social and technical history.
If you remove that last part, you do not really have a blockchain in the strong sense. You have replicated data, but not a decentralized way to decide what counts as the ledger.
Conclusion
A blockchain exists to solve a very specific coordination problem: how to maintain one shared history among parties that do not want to trust a single writer. It does this by chaining blocks with cryptographic commitments and using consensus to decide which chain of state changes the network accepts.
Everything else follows from that goal. The power of blockchain is that it can make a ledger public or shared without making it ownerless chaos. Its weakness is that this comes with real costs, real assumptions, and real failure modes. The shortest durable way to remember it is this: a blockchain is not just data stored in many places; it is a system for agreeing on the same evolving record without needing one party to be in charge.
What should you understand before using blockchain infrastructure?
Understand a blockchain’s consensus model, finality behavior, fees, and exact asset/network details before you deposit, trade, or transfer. On Cube Exchange, fund your account on the correct network and then use Cube’s market or transfer flows to execute trades or move assets.
- Identify the chain and confirm its finality model and recommended confirmation count (for example, many Bitcoin services wait ~6 confirmations; some PoS or BFT chains finalize faster).
- Verify the exact asset and network: copy the token contract address for ERC-20 tokens, confirm the network (Ethereum vs. a layer-2), and match it to the project’s official source.
- Fund your Cube Exchange account using the supported deposit path for that network. Select the same network when sending funds and wait for the chain-specific confirmation threshold before trading or withdrawing.
- Place your trade or transfer with execution details in mind: use a limit order for price control or a market order for immediacy; set slippage tolerance and a transaction deadline for on-chain swaps; review estimated gas/fees before submitting.
Frequently Asked Questions
A blockchain combines digital signatures (to prove who authorized a transfer) with a network-wide consensus rule so independent nodes agree on a single ordering; when two valid-looking, conflicting signed transactions exist, the one included by the chain accepted under the consensus rule counts and the other is rejected.
Linking blocks by cryptographic hashes makes any edit to an earlier block change its hash and break subsequent links, so tampering becomes visible; however, it is not impossible to change history - doing so requires overcoming the system’s consensus defenses (for example redoing enough proof-of-work or coercing a validator threshold), which is costly and socially detectable.
In longest-chain proof-of-work systems finality is probabilistic: a transaction becomes exponentially harder to reverse as more blocks accumulate because an attacker must outwork the honest chain; in many BFT-style protocols a block is effectively final after a supermajority of validators precommit, so reversing it would require a threshold of validators to violate the protocol.
Choose a blockchain when multiple parties need a shared, verifiable history but do not want to or cannot trust a single administrator; if a single organization already controls the data and can resolve disputes, a conventional centralized database will usually be faster, cheaper, and simpler.
Programmable chains meter and charge for computation and storage (Ethereum’s gas model is a canonical example) so transactions specify limits and nodes refuse unbounded execution; that metering creates a cost that protects the network from infinite loops and denial-of-service code.
Security rests on explicit assumptions: PoW relies on honest-majority hashing power, PoS on stake distribution and honest validator incentives and slashing, and many BFT systems assume fewer than one-third Byzantine voting power; these assumptions can fail in practice via mining/stake centralization, key compromise, network partitions, or coordinated misbehavior.
Permissioned blockchains restrict who can read or write and typically rely on known organizations and off-chain governance, which lets them trade weaker decentralization for higher throughput, predictability, and privacy; permissionless blockchains are open to anyone and must embed stronger protocol-level defenses and incentive designs to handle anonymous adversaries, which typically reduces performance.
Cross-chain bridges necessarily extend trust beyond a chain’s native boundary (often involving intermediaries, multisigs, or relayers), which increases complexity and attack surface; empirical surveys show a large share of losses in cross-chain systems have come from bridge compromises and weak intermediary key operations.
Related reading