What Is a Miner in Blockchain Consensus?
Learn what a miner is in blockchain consensus: how miners create blocks, secure Proof-of-Work chains, earn rewards, and where the model breaks down.
Introduction
Miner is the name for the participant in a Proof-of-Work blockchain that packages transactions into blocks and competes to make one of those blocks accepted by the network. That sounds simple, but it hides the real point: a miner is not just a block producer. A miner is the mechanism by which an open network, with no central membership list, turns resource expenditure into agreement about history.
That is the puzzle miners solve. If anyone on the internet can join, why should the network trust one proposed history instead of another? Proof-of-Work systems answer by making block production costly to fake but easy to verify. A miner spends real-world resources searching for a valid block, and the network treats the chain with the most accumulated work as authoritative. The miner therefore sits at the center of both consensus and security.
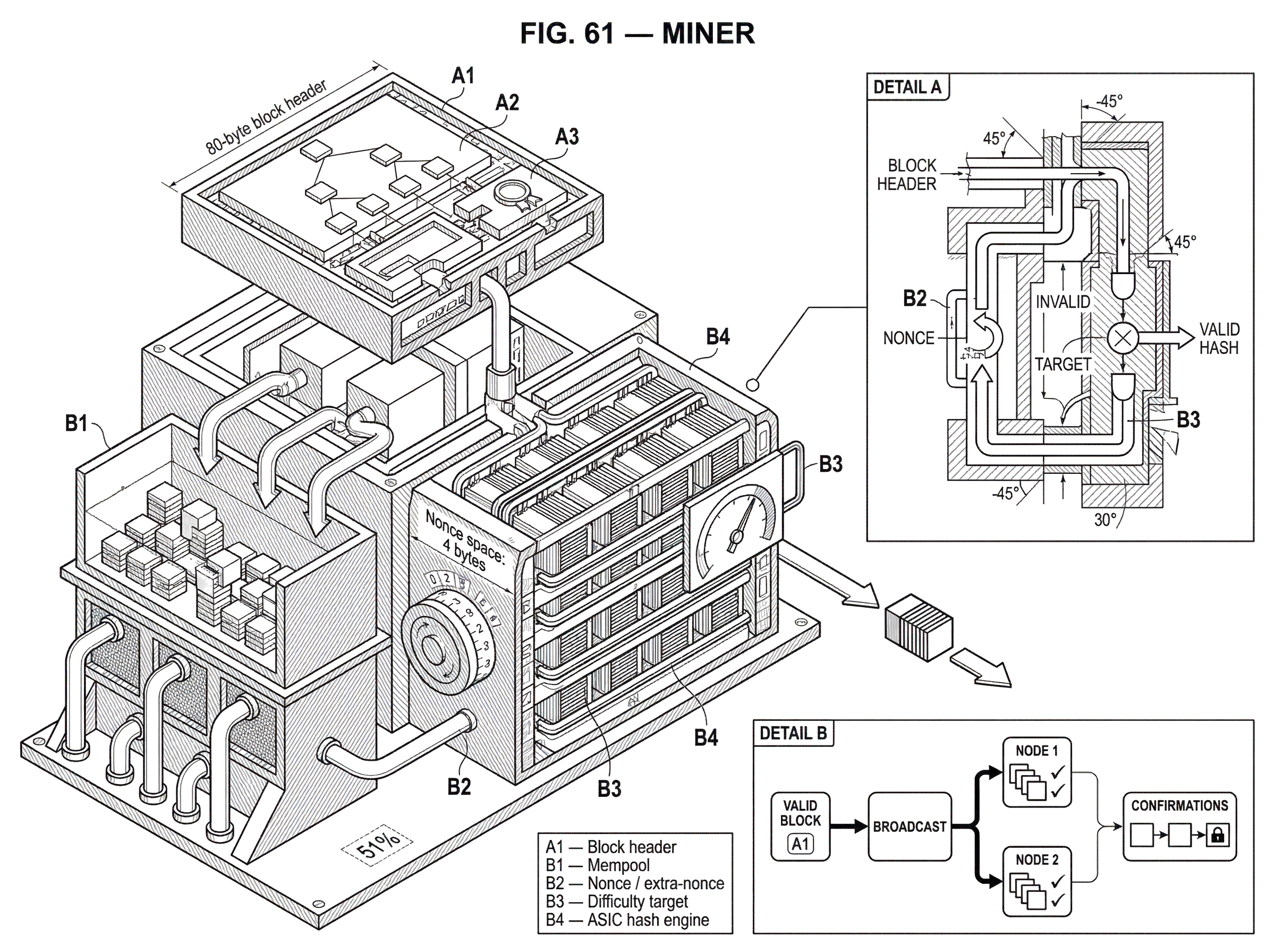
In Bitcoin, this role is explicit. Nodes collect transactions, assemble them into candidate blocks, search for a nonce that makes the block hash satisfy the current difficulty target, and broadcast the result when they succeed. Other nodes verify the block and, if it is valid, extend that chain. The same basic pattern appears across Proof-of-Work systems even when details differ: miners sequence transactions, invest computation, and race to extend the ledger.
The key thing to understand is that mining is not valuable because hashing is intrinsically useful. Hashing is useful here because it creates a scarce, externally costly signal that the network can measure without trusting identities. Once that clicks, the rest of the design (rewards, confirmations, pools, attack models, even energy debates) becomes easier to reason about.
What does a miner actually do in a Proof‑of‑Work blockchain?
At first glance, a miner seems like a machine that guesses numbers very quickly. That is true at the narrowest level, but it misses the broader mechanism. A miner first chooses a set of transactions, builds a block around them, links that block to the previous accepted block, and only then begins the computational search that may allow the block onto the chain. The search is the gatekeeper, not the whole job.
In Bitcoin’s whitepaper description, the workflow is straightforward: new transactions are broadcast, each node gathers them into a block, each node works on a difficult Proof-of-Work for that block, and when one finds a valid proof, it broadcasts the block. Other nodes accept the block only if its transactions and Proof-of-Work are valid, and then they begin working on the next block using that block’s hash as the previous reference. This repeated loop is how miners collectively maintain a shared transaction history without a central operator.
The practical effect is that miners are sequencers under constraint. They choose ordering and inclusion, but they cannot simply declare a block final. They must present a block whose header hashes below the network’s target. Because many miners are racing at once, any individual miner’s proposed ordering only matters if that miner also wins the race or belongs to a pool that wins it.
This is why miners matter for more than issuance of new coins. They determine which pending transactions get confirmed first, which fees are collected, and in many Proof-of-Work systems whether certain transactions are delayed or censored. The network does not ask miners for opinions; it asks them to present valid blocks backed by costly work. But whoever controls block production necessarily has influence over transaction ordering.
Why do Proof‑of‑Work systems require miners?
The deepest reason miners exist is that open consensus has a sybil problem. If voting were based on identities or IP addresses, anyone could create many pseudonyms and outvote honest participants at almost no cost. Proof-of-Work replaces identity-based influence with resource-based influence. In the Bitcoin whitepaper’s phrase, it approximates one-CPU-one-vote; more precisely today, one-unit-of-hashpower-one-vote.
Here is the mechanism. The protocol defines a target threshold. A block is valid only if its hash is below that target. Because secure hash outputs are unpredictable, the only general strategy is repeated trial: vary a field such as the nonce, hash the block header, and check whether the result satisfies the target. Verification is cheap (a node can hash once and compare) but finding a valid result is expensive on average. That asymmetry is the point.
This does two jobs at once. First, it makes block creation probabilistic and costly, so no one can cheaply flood the network with valid-looking histories. Second, it gives the network a way to compare competing histories without relying on reputation. The chain with the most accumulated Proof-of-Work represents the one that required the greatest expenditure of computation. Consensus becomes a contest over work invested, not over who is speaking.
An analogy can help here. Mining is like winning the right to append a page to a public logbook by solving a puzzle whose solution anyone can check instantly. That explains why miners must spend effort before their page is accepted. But the analogy fails in one important way: in a blockchain, the puzzle is tied to the exact block contents and to the previous block hash, so miners are not solving generic puzzles for points. They are solving a puzzle that commits them to a specific proposed continuation of history.
How does the mining race work, step by step?
A concrete example makes the process clearer. Imagine a miner sees a batch of unconfirmed payments waiting in the mempool. The miner chooses some of them (often guided by fee revenue and block constraints) and creates a candidate block that references the current tip of the chain. The first transaction is special: it is the coinbase transaction, which assigns the block reward and collected transaction fees to the block creator.
The miner then computes the Merkle root summarizing the chosen transactions and places that root in the block header along with the previous block hash, version information, timestamp, difficulty target representation, and a nonce. In Bitcoin, miners commonly send the 80-byte block header to ASIC hardware, which repeatedly hashes it while varying the nonce. Because the nonce space is only 4 bytes, miners also vary other fields, such as an extra-nonce in the coinbase transaction, which changes the Merkle root and opens new search space.
Nothing intelligent happens inside the hash search itself. The miner is not “solving” the block in the sense of deriving a clever answer. The miner is sampling possibilities until chance produces a hash below the target. If a found header satisfies the easier threshold a mining pool asked for, that may count as a share. If it satisfies the actual network target, it is a valid block candidate for the chain.
Once a miner finds such a header, it broadcasts the full block. Peers verify the transactions, the block structure, and the Proof-of-Work. If valid, they accept it and start mining on top of it. If two miners find competing valid blocks around the same time, the network temporarily forks. Different nodes may see different tips first, but miners eventually converge by extending whichever branch accumulates more work. That is the practical meaning of the longest-chain rule: more precisely, the valid chain with the most total Proof-of-Work wins.
Why are miners paid block rewards and transaction fees?
Mining would not persist if it were only a public service. Miners spend money on hardware, electricity, facilities, operations, and connectivity, so the protocol has to give them a reason to participate. In Bitcoin, the incentive begins with the block’s first transaction, which creates new coins for the block creator. Transaction fees can be collected as well. Together, subsidy plus fees form the miner’s revenue.
This reward is not an extra feature bolted onto consensus. It is part of the security mechanism. The system needs honest miners to keep extending the chain, and paying them makes honest participation the default strategy under the intended assumptions. New coin issuance bootstraps security in early stages, while fees are expected to matter more over time.
That design creates a subtle but important connection between economics and safety. A miner is not just checking validity; every miner is deciding whether spending additional resources to mine makes economic sense. If rewards are high relative to costs, more hashrate tends to join. If rewards fall or costs rise, some miners shut down. Security in a Proof-of-Work system is therefore tied to market conditions, not only to code.
This is also why halvings matter so much in Bitcoin. The subsidy is periodically reduced, which lowers automatic miner revenue unless price or fee income compensates. Research on fee-only or fee-dominant regimes suggests the incentive picture becomes more fragile: miners may have stronger reasons to fork “wealthy” blocks, delay mining until fees accumulate, or adopt strategies that increase orphaning and instability. The protocol clearly specifies how miners are paid today; the long-run equilibrium when subsidy becomes less important is more uncertain.
How do confirmations and probabilistic finality work, and what do miners secure?
When a merchant says they are waiting for confirmations, they are really waiting for more miner work to accumulate behind a transaction. A transaction is first included in some block. Each later block built on top of that block increases the cost of reversing it, because an attacker would need to redo the Proof-of-Work for the altered block and every block after it, then catch up with and overtake the honest chain.
This gives Proof-of-Work systems a form of probabilistic finality. A block is not final in the absolute sense the instant it appears. Instead, the probability of reversal falls as more blocks are added. The Bitcoin whitepaper models this fall as exponential under the assumption that honest miners control a greater share of hashpower than the attacker. That is why waiting for multiple confirmations reduces double-spend risk.
The miner’s role here is easy to miss. Miners are not merely creating future blocks; they are reinforcing the past. Each new valid block extends the current branch and increases the accumulated work protecting earlier transactions. Security is therefore not only about the next block reward. It is about the continuing willingness of miners to keep building on the same accepted history.
This also reveals what breaks if the key assumption fails. If an attacker controls a majority of hashrate, the attacker can, in principle, outpace honest miners and produce the heaviest chain. At that point the normal security story no longer holds. The network can still verify whether blocks satisfy the rules, but it cannot distinguish honest majority work from malicious majority work if the malicious chain really has more accumulated Proof-of-Work.
Why did mining concentrate into pools and specialized hardware?
| Mode | Income variance | Control over transactions | Search-space access | Best for |
|---|---|---|---|---|
| Solo | High variance | Full transaction control | Full block template (getblocktemplate) | Large independent miners |
| Pooled | Low variance | Limited transaction control | Header-only (Stratum) shares | Stable-income operators |
In theory, any miner can compete directly. In practice, block discovery is a lottery with very high variance. A small miner working alone might contribute real hashrate for a long time and receive nothing, then suddenly find a block and receive a large payout. That variance is economically hard to tolerate, so pooled mining became dominant.
A mining pool coordinates many miners under a shared strategy. The pool distributes work to participants and sets a much easier target for shares, which are proofs that miners performed some amount of hashing even when they did not find a full network-valid block. When one participant eventually finds a header that also meets the network difficulty target, the pool submits the block and distributes rewards according to contributed shares.
This smooths income, which is why miners join pools, but it also changes who actually controls block construction. In solo mining with getblocktemplate, a miner can obtain a block template and choose transactions more directly. In common pooled setups using Stratum, miners often receive only the minimal data needed to construct headers and search over them. That reduces bandwidth and latency, but it means the pool operator, not the downstream hardware owner, usually decides transaction selection.
So mining became specialized in two ways at once. Hardware specialized into ASICs because general-purpose chips could not compete efficiently at large scale. Organizationally, miners aggregated into pools because variance made independent operation unattractive. The result is that a large amount of nominally distributed hardware can behave like a smaller number of coordinated entities.
Empirical studies have repeatedly found substantial mining concentration. In Bitcoin, a small set of entities has often controlled a large fraction of total mining power, even when no single entity dominates outright. That does not mean the system instantly fails, but it weakens the comforting mental image of millions of independent actors each making separate decisions. Security assumptions are about effective control of hashrate, and pools are one of the main places where that control is concentrated.
What attacks or strategic deviations can miners carry out without 51% hashpower?
| Deviation | Approx. threshold | Main effect | Mitigation |
|---|---|---|---|
| Selfish mining | Depends on propagation advantage (γ) | Increases orphaning; skews revenue | Propagate competing branches; random tie-break |
| Undercutting / fee attacks | More likely in fee-only regimes | Fork wealthy blocks; reduce security | Fee‑market design; discourage gaps |
| Transaction censorship | Requires non‑majority coordination | Delays or omits transactions | Economic monitoring; diversify relay/pools |
The common story is that Proof-of-Work is safe unless someone gets 51% of the hashrate. That is too coarse. Majority control is the most obvious threshold for rewriting history at will, but miners can distort incentives and harm the system even below that level.
The clearest example is selfish mining. Instead of publishing a found block immediately, a colluding miner or pool keeps it private and starts building a secret branch. Honest miners continue working on the public chain, unaware they may already be behind. The selfish pool then reveals blocks strategically, trying to invalidate honest miners’ work and gain a larger share of accepted blocks than its proportional hashpower would suggest.
The important insight is not just that this attack exists. It is that miners are economic actors responding to payout rules and network conditions. If deviating from the “honest” publish-immediately strategy increases expected revenue, then the protocol is not fully incentive-compatible. Research shows the profitability threshold depends on propagation advantages and on how honest miners react during ties. Under favorable network conditions for the selfish pool, the threshold can be much lower than many people assume.
This matters because such strategies can create a feedback loop. If a pool earns more than its fair share, rational miners may join it to get more stable or higher returns, increasing its power further. Consensus then becomes vulnerable not only to overt attack but also to migration dynamics driven by incentives.
There are also fee-related deviations. Research on low-subsidy regimes argues that miners may profit from forking blocks rich in fees, undercutting competitors by leaving some fees unclaimed to attract follow-on miners, or even creating “mining gaps” in which it is rational to wait rather than mine immediately after a block. These behaviors are not bugs in the code. They are consequences of how rewards interact with strategic behavior.
How does miner‑based security differ between large and small Proof‑of‑Work chains?
On a large Proof-of-Work network, attacking the chain usually requires enormous sustained hashpower and therefore enormous cost. That is the security intuition most people have in mind. But this intuition does not transfer cleanly to every Proof-of-Work chain.
Smaller chains are much more exposed because what matters is not absolute hashrate, but how expensive it is to control a majority relative to that chain’s own security budget. If a chain’s total mining power is low, miners or attackers from larger ecosystems may be able to redirect hardware temporarily, or rent hashrate, and overpower it. Incident tracking by MIT DCI has documented many deep reorganizations and double-spend attacks on smaller Proof-of-Work cryptocurrencies, some plausibly enabled by hashrate rental markets.
This shows a fundamental property of miners: they are mobile capital. A miner is not always loyal to one chain. If compatible hardware can mine several assets, hashpower can move toward whatever is most profitable or strategically useful. That mobility is efficient from the miner’s perspective, but it means weaker chains may inherit the downside of sharing an algorithm with stronger ones.
So when asking whether miners secure a network, the right question is not “Does it have mining?” The right question is “How much honest, economically committed hashpower is actually defending it, and how expensive is it to displace that?” The answer can differ dramatically between Bitcoin and a thinly defended altcoin even though both are formally Proof-of-Work systems.
How do miners compare to validators, and how do fees and infrastructure shape mining?
| Actor | Resource committed | Influence metric | Centralization drivers | Finality model |
|---|---|---|---|---|
| Miner | Electricity and hardware | Hashpower share | Pools, ASIC manufacturers, cheap energy | Probabilistic confirmations |
| Validator | Staked native tokens | Stake weight | Delegation concentration, custody | BFT-style commits (≥2/3) |
The cleanest comparison is with validators in Proof-of-Stake systems. Miners and validators play the same broad structural role: they are the actors whose participation advances consensus and whose rewards are meant to align them with the protocol. But the resource they commit is different. A miner commits external resources continuously (electricity, hardware wear, operating expense) to win block production rights. A validator commits stake and participates through voting or proposing under a different slashing and reward model.
That difference changes many downstream properties. Miner influence scales with hashpower, which usually must be purchased and operated in the physical world. Validator influence scales with stake, which is native to the system and often easier to reassign administratively. Neither model is automatically decentralized; they simply centralize through different mechanisms. In Proof-of-Work, pools, ASIC supply chains, and cheap energy matter. In Proof-of-Stake, custody, delegation concentration, and validator set dynamics matter.
Miners are also tightly linked to network fees. Fees are not just user costs. They are part of the incentive structure that affects which transactions miners include and, increasingly, whether the network remains well secured as subsidy declines. A high-fee transaction is effectively bidding for scarce block space and for miner attention. That is why miner behavior and fee market design cannot be separated cleanly.
Finally, miners depend on infrastructure that sits outside the bare protocol. Relay networks can improve propagation and reduce stale blocks. Pool protocols such as Stratum shape what miners can see and control. ASIC manufacturers influence who can acquire efficient hardware. These are not side details. They help determine who mining is realistically accessible to, how fast blocks spread, and whether nominally separate miners act independently or through chokepoints.
Conclusion
A miner is the participant in a Proof-of-Work blockchain that turns computation into accepted blocks and, by doing so, helps the network agree on one transaction history. The essential idea is simple: instead of trusting identities, the network trusts the chain that demonstrably required the most work to produce.
From that idea, everything else follows. Miners collect and order transactions, search for valid block hashes, earn rewards, reinforce confirmations, and make rewriting history expensive. But they also introduce the system’s hardest trade-offs: concentration in pools, sensitivity to energy and hardware costs, strategic deviations like selfish mining, and long-run uncertainty as subsidies shrink. If you remember one thing, remember this: miners are not just block finders; they are the economic and physical substrate of Proof-of-Work consensus.
What should I understand about miners before trading or depositing crypto?
Miners influence how hard it is to reverse transactions, how quickly transfers confirm, and how likely censorship or reorg risk is on a chain. Before you trade, deposit, or withdraw on Cube Exchange, check the chain’s recent stability and follow a clear deposit/confirmation workflow so you avoid surprise reversals or long delays.
- Open a reputable block explorer for the chain you plan to use and check recent reorgs and the hashrate trend (look at the last 24–72 hours).
- Confirm the correct network and address on Cube, then fund your Cube account by fiat on‑ramp or by sending the exact asset on the exact chain you verified.
- For Bitcoin use at least 6 confirmations before large transfers; for smaller PoW chains, require many more confirmations or wait for exchange guidance based on recent reorg activity.
- If you’re moving funds off Cube, review current mempool fee pressure and choose a fee or order type (replace‑by‑fee, high priority fee) that fits the urgency to avoid delayed inclusion or fee‑related delays.
Frequently Asked Questions
Miners pick transactions based on fee revenue, block constraints, and the pool or operator’s policy; because they control which transactions appear in the block they mine, they can delay or omit (censor) transactions although any proposed block still needs a valid Proof-of-Work to be accepted by the network.
Proof-of-Work makes block creation probabilistic and expensive to produce but trivial to check: miners repeatedly hash block headers (varying fields like the nonce) until a hash falls below the protocol target, and other nodes verify that single hash quickly - the asymmetry (costly to find, cheap to verify) is what replaces identity-based voting.
Because solo block rewards have very high variance, miners joined pools to smooth income and specialized into ASIC hardware for efficiency; the combination of pooled coordination and specialized hardware shifted effective control toward a smaller set of operators even though the physical hashrate is widely distributed.
Selfish mining is a strategy where a miner or pool withholds found blocks and selectively releases them to orphan honest work, which can increase its relative revenue without a majority; its profitability and the minimum required hashpower depend on network propagation advantages (γ) and tie‑breaking behavior, so damage can occur well below a simple 51% threshold.
Miners secure transactions by continually extending the chain: each new valid block adds accumulated Proof-of-Work behind prior transactions, so the probability of reversal falls (probabilistic finality) as more blocks are built on top of a transaction.
Miners receive block subsidies and transaction fees because they bear real-world costs (hardware, electricity, operations); these rewards align economic incentives so honest mining is typically profitable, but security depends on market conditions and becomes less certain as subsidies shrink and fees must carry more of the security budget.
Miners are economically mobile: compatible hardware can be redirected to other chains or rented, so smaller Proof-of-Work networks are vulnerable because an attacker can temporarily reassign or rent hashpower to overpower them, enabling deep reorganizations and double-spends.
Miners and Proof-of-Stake validators both advance consensus but commit different resources: miners continuously expend external resources (electricity, hardware wear) to win blocks, while validators lock native stake and participate through protocol-defined proposals and voting, so centralization pressures arise from different parts of each ecosystem (pools/ASICs versus stake concentration/delegation).
Related reading