What is a Validator?
Learn what a validator is in blockchain consensus: how validators use stake, signatures, and protocol rules to propose blocks, vote, and secure proof-of-stake networks.
Introduction
Validator is the name most proof-of-stake blockchains give to the participants who help decide which blocks are valid and in what order the chain advances. The stakes are high because a blockchain is not just storing data; it is trying to maintain a shared history among machines that do not fully trust one another. A validator exists to solve that problem under explicit rules: check proposed blocks, vote or sign according to the protocol, and sometimes propose blocks itself.
The easy way to picture a validator is as a replacement for the miner in proof-of-work. That comparison is useful, but only up to a point. A miner proves commitment by burning external resources such as electricity. A validator proves commitment by putting protocol-recognized capital at risk. That difference changes almost everything: how participants are selected, how safety is enforced, what kinds of failures matter, and why misbehavior can be punished after the fact.
The central idea is this: a validator is not merely a server running software. It is a protocol role backed by cryptographic keys, scheduled duties, and an economic bond that can be reduced if the validator violates consensus rules. Once that clicks, the rest of the concept becomes much easier to organize. The machine matters because it signs messages on time. The stake matters because those signatures have consequences.
What problem do validators solve in blockchain consensus?
A blockchain needs a way to answer two questions repeatedly: *What is the next block? and When should everyone treat that decision as settled? * In an ordinary centralized database, one operator answers both questions. In a decentralized system, no single operator is supposed to have that power. Validators are the mechanism that spreads this responsibility across many actors while still allowing the network to converge on one history.
That job has two parts. First, someone has to examine candidate blocks and reject invalid ones. A block may contain bad signatures, invalid transactions, or state transitions that do not follow the rules. Second, someone has to help coordinate agreement so that the network does not splinter into many competing histories. These are related but distinct tasks. A block can be individually valid yet not become part of the canonical chain if the validator set does not sufficiently support it.
This is why validators are usually both checkers and voters. They do not simply verify local correctness like a passive full node. They also produce messages that other participants treat as consensus input. In Ethereum, those messages are attestations and occasional block proposals. In Tendermint-style systems such as the Cosmos stack, validators propose and vote on blocks, and a commit is formed once more than two-thirds of validator weight signs. In Solana, validators process transactions and send stake-weighted votes that the cluster uses to pick among forks. The details differ, but the structure is the same: validators turn individual verification into collective agreement.
How does a node become a validator on a blockchain?
At first principles, a validator is defined by three things: it is recognized by the protocol, it has weight in the consensus process, and it can produce authenticated messages that others can verify.
Recognition by the protocol means the network has a rule for who counts as a validator right now. That rule might come from a deposit contract, a staking module, a validator registry, or an active set maintained in state. Ethereum recognizes validators after they deposit ETH and are activated under consensus rules. Tendermint-based systems maintain a known weighted validator set whose membership and weight may change over time. Polkadot assigns validators to relay-chain and parachain duties by runtime logic. In every case, validator status is not social reputation alone; it is state recognized inside the protocol.
Weight means not all signatures are equal. Consensus systems usually aggregate validator influence according to stake or validator-set voting power. That matters because safety thresholds are defined in weighted terms. Ethereum checkpoint finality depends on votes representing at least two-thirds of total staked ETH. Tendermint commits require signed messages from more than two-thirds of validator weight. The protocol does not ask, “How many people signed?” but rather, “How much recognized consensus weight signed?”
Authenticated messages are the mechanism by which validators do their job. A validator signs proposals, votes, or attestations with a key that the protocol associates with that validator identity. That gives the network something objective to check. If a validator signs correctly and on time, the signature can be counted. If it signs two incompatible messages, that contradiction can often be proven later. This ability to prove misbehavior is what makes slashing possible in many Proof-of-Stake designs.
Why do validators stake capital and how does staking enforce honest behavior?
Why not just let anyone vote equally? Because then dishonest behavior is cheap. A participant could create many identities, sign conflicting messages, or abandon one fork and join another with little cost. Proof-of-stake tries to make consensus weight scarce and costly by tying it to bonded capital.
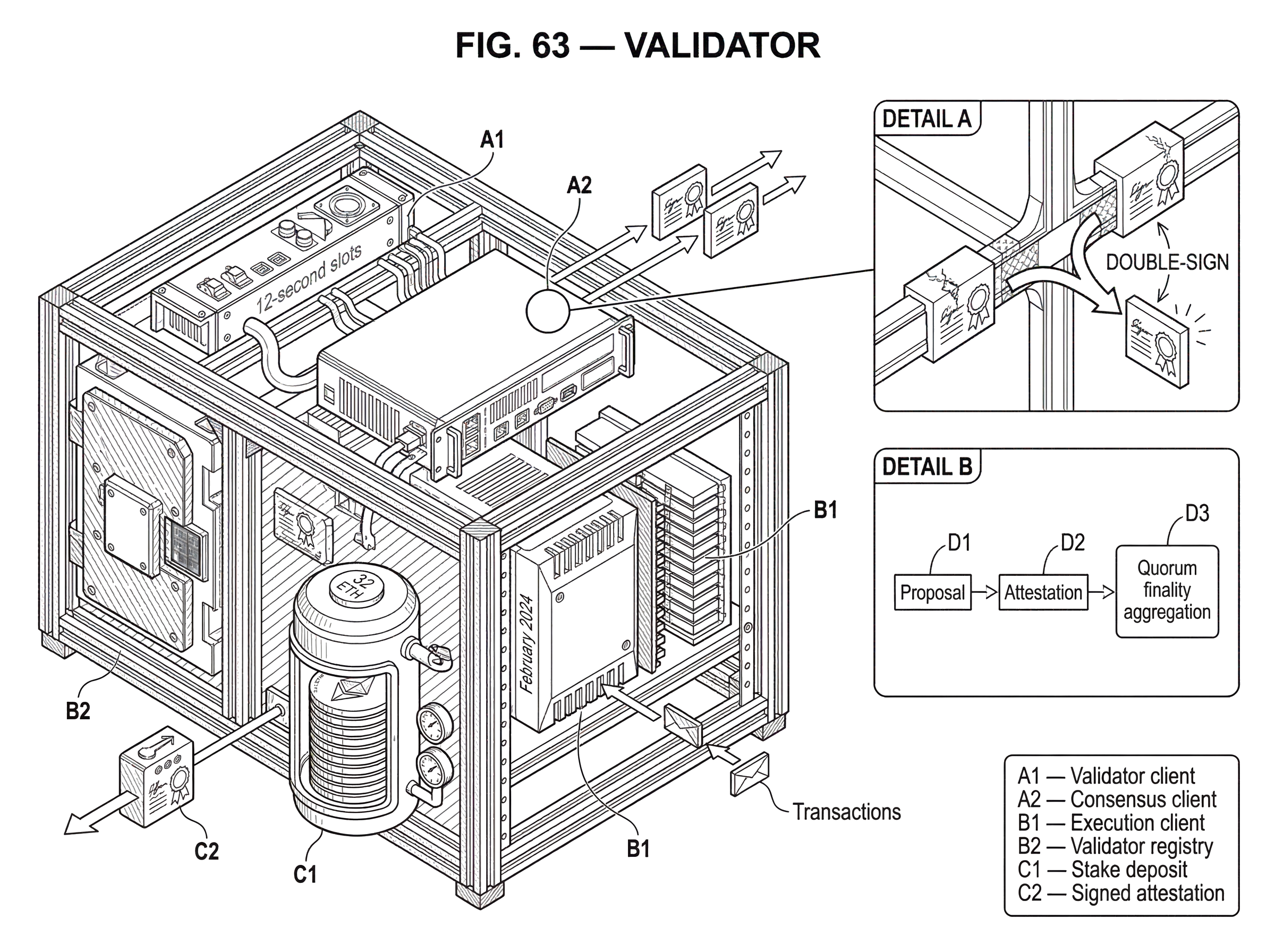
In Ethereum’s proof-of-stake design, validators explicitly stake ETH that can be destroyed if they act dishonestly. To participate directly as a validator, a user deposits 32 ETH and runs an execution client, a consensus client, and a validator client. That 32 ETH number is Ethereum-specific, not universal, but the general pattern appears across many systems: validator influence comes from capital committed under protocol rules, not from free-floating identities.
The economic logic is straightforward. If a validator can gain from violating the protocol, the protocol wants the expected loss from being caught to outweigh the gain. Stake is the thing the protocol can actually touch. It cannot confiscate a validator’s reputation, but it can reduce a balance in state. That gives consensus rules a credible enforcement mechanism.
There is also a subtler reason stake matters: it aligns validators with the chain’s continued health. If your wealth is locked into the system’s native asset or bonded position, attacks that damage confidence in the chain also tend to damage your own position.
That alignment is imperfect but it is stronger than a system in which consensus identities are nearly free.
- validators can hedge
- short
- have external motives
How do validator duties operate in practice (proposals, attestations, voting)?
A validator’s life is mostly repetitive. The protocol divides time or progress into units, assigns duties, and expects signatures within specific windows. The validator’s software watches the network, checks what it receives, and signs only when the relevant rules are satisfied.
Ethereum provides a clean example. Time is divided into 12-second slots and 32-slot epochs. In each slot, one validator is randomly selected to propose a block, and committees of validators are randomly selected to attest. When acting as proposer, the validator’s execution client assembles transactions into an execution payload, executes them locally, and passes the result into the consensus flow so it can be wrapped into a beacon block. Other participants re-execute and verify what they received, and validators in the assigned committee attest if the block and chain state satisfy the rules.
Those attestations do more than say “this block looks valid.” They also help answer “what is the current head?” and “which checkpoints should be justified and finalized?” In Ethereum, validators vote on checkpoints under Casper FFG, while fork choice uses attestation weight to pick the head. In a Tendermint-style chain, the same broad mechanism appears in another form: validators take turns proposing blocks and vote on them, and once more than two-thirds of validator weight signs, the block is committed. In Polkadot, validators not only participate in relay-chain consensus but may also be assigned to validate parachain candidates, distribute availability information, and later approve those candidates through secondary checks.
The pattern is worth noticing. A validator is not a generic “yes/no” machine. It performs narrowly defined duties at specific times under protocol-defined eligibility rules. Proposal, attestation, voting, data availability checking, approval, and synchronization support may all be validator duties depending on the architecture.
Here is a concrete narrative. Imagine a new Ethereum slot begins. One validator has been selected as proposer for that slot. Its software asks the execution layer for a candidate payload built from transactions in the local mempool, executes those transactions to compute the resulting state transition, and packages that information into a beacon block. The block is broadcast. Other nodes receive it, re-run the relevant checks, and validators assigned to that slot’s committee evaluate whether the proposal matches protocol rules and whether it extends what they currently see as the best chain. If so, they sign attestations and broadcast them. Those attestations then become input both to immediate fork choice and to the slower process that can justify and finalize checkpoints once enough stake supports them. Nothing mystical happened; the protocol advanced because a specific validator proposed, many specific validators checked, and enough weighted signatures accumulated.
How do validators produce finality and why does finality matter?
New readers often think validation is mainly about catching invalid transactions. That matters, but it is only half the story. The harder problem is settlement: when can the network stop worrying that an alternative branch will replace the current one?
Validator votes are what make stronger notions of finality possible. In Ethereum, checkpoint finality is achieved when a pair of checkpoints attracts votes from at least two-thirds of total staked ETH; the target checkpoint becomes justified, and later finalized under the protocol’s rules. The important consequence is not just that “many validators agreed.” It is that reverting finalized history would require either an extraordinary failure or economically catastrophic validator misbehavior.
In Tendermint, the same basic threshold appears in a more direct form: a commit is a set of signed messages from more than two-thirds of validator weight. Safety and liveness are guaranteed so long as less than one-third of the total validator weight is malicious or faulty. This is the classic Byzantine threshold showing up in practice. The exact message flow differs from Ethereum’s beacon-chain design, but the underlying invariant is similar: once a supermajority of recognized validator weight has signed in the required way, the network can treat the result as settled unless assumptions have broken badly.
This is also why the two-thirds threshold appears so often in proof-of-stake discussions. It is not just a convenient convention. It is the weight needed in many Byzantine-fault-tolerant constructions to preserve safety while still tolerating up to one-third faulty or malicious weight.
What validator actions lead to slashing and on‑chain penalties?
| Failure type | Provable? | Penalty | Typical severity |
|---|---|---|---|
| Equivocation / double signing | Yes | Slashing + forced exit | High |
| Surround voting | Yes | Slashing + staged exit | High |
| Missing attestations / offline | Usually no | Lost rewards / minor penalty | Low to medium |
| Failing to propose | No | No penalty beyond reward loss | Low |
Because validators sign messages that affect consensus, some forms of misconduct are objectively provable. If the same validator signs two different blocks for the same slot, or contradictory votes that cannot both be valid under the protocol, that evidence can be shown to the network. Once provability exists, penalties become enforceable at the protocol level.
Ethereum’s slashing rules illustrate the idea clearly. Dishonest behaviors such as proposing multiple blocks in a single slot, double voting, or surround voting can be slashed. A slashed validator loses some stake immediately, enters a forced exit process, and can face additional penalties whose magnitude depends on how many others are slashed around the same time. That last part matters: correlated failures are treated more severely because they signal broader danger to consensus.
Not every failure is slashable. Missing an attestation, failing to propose a block, or going offline is often handled as a weaker penalty or lost reward rather than a slash, depending on the system and failure type. Ethereum, for example, penalizes some missed voting duties and forgone rewards, but there is no penalty for failing to propose a block beyond missing the associated reward. Cosmos Hub documentation emphasizes that validators can be slashed for unavailability or signing blocks at the same height, and jailed if they miss too many recent blocks or double sign. Different systems draw the line differently between malice, dangerous equivocation, and ordinary unavailability.
That distinction exists for a reason. Consensus wants to punish actions that threaten safety more harshly than actions that merely reduce throughput or participation. Signing incompatible histories is dangerous because it undermines agreement itself. Being temporarily offline is harmful, but usually in a more recoverable way.
What are the consequences when validators go offline or disagree about the chain?
A common misunderstanding is that validator systems fail only when validators act maliciously. In practice, ordinary operational failures are at least as important. Software bugs, clock drift, network partitions, disk failures, client misconfiguration, and correlated outages can all cause validators to miss duties or process the chain incorrectly.
Ethereum’s consensus specifications explicitly prioritize remaining live through major network partitions and when very large portions of nodes go offline. That design choice leads to mechanisms such as the inactivity leak. If the chain fails to finalize for more than four epochs, inactive validators gradually lose stake until active validators once again represent more than two-thirds of stake and finality can resume. The mechanism is harsh, but the logic is clean: if too much validator weight disappears, the protocol slowly reduces the influence of the absent portion so the chain can recover.
Incidents in production systems show why validator operations matter as much as validator theory. Prysm postmortems describe failures where beacon nodes were overwhelmed processing certain attestations, leading to CPU and memory exhaustion, missed duties, lower participation, and material reward losses. The lesson is not merely that one client had a bug. It is that a validator is an economic role implemented by software, and software can fail in correlated ways.
Solana’s February 2024 outage showed the same point in a different architecture. A bug in validator-side execution and replay logic caused nearly all validators running a common version to stall, which halted consensus until operators coordinated a restart and upgrade. Again, the mechanism differed from Ethereum, but the structural lesson was identical: if too much consensus weight depends on one flawed implementation, validator incentives alone cannot save the chain in the moment.
Why is client diversity important for validator and chain safety?
| Client marketshare | Finality risk | Validator impact | Operator action |
|---|---|---|---|
| <33% | Finality preserved | Low systemic risk | Run minority clients |
| 33–66% | Can prevent finality | Chain stalls possible | Reduce concentration |
| >66% | May finalize wrong chain | Catastrophic slashing risk | Migrate away quickly |
From the outside, “run the spec” sounds like enough. In reality, validators run implementations of the spec, and implementations have bugs. If too much validator weight concentrates on a single client, that client effectively becomes a hidden single point of failure.
This is why client diversity is not an abstract nice-to-have. It is a consensus safety requirement. If a buggy client controls more than one-third of validator weight, it can prevent finality. If it controls two-thirds or more, it may be able to finalize an invalid chain under some failure scenarios. The danger exists for both consensus clients and execution clients.
Ethereum’s ecosystem has learned this repeatedly. client-diversity advocates emphasize the practical thresholds: keep any one client below one-third if possible, because one-third is enough to interfere with finality; above two-thirds is dangerous because finality itself can be reached on the wrong branch. Prysm’s own postmortems explicitly note that diversity reduced the severity of incidents and warn about the consequences of a single client exceeding those thresholds.
For a validator operator, this means choosing software is not just a private operational decision. It is also a public contribution to network resilience. Running a minority client may slightly increase operational complexity, but concentration risk is worse.
How do validator roles differ across blockchains like Ethereum, Tendermint, Solana, and Polkadot?
| Architecture | Membership model | Commit rule | Typical duties | Stake model |
|---|---|---|---|---|
| Ethereum | Deposit contract activation | Checkpoint finality ≥2/3 stake | Propose, attest, committees | Self-bond (32 ETH) |
| Tendermint / Cosmos | Active weighted validator set | Commit when >2/3 weight signs | Propose, vote, commit | Direct bonded stake or delegated |
| Polkadot | Runtime-selected in-core set | Parachain approval + relay-chain rules | Relay + parachain validation, approval | Bonded DOT, assigned duties |
| Solana | Per-node vote accounts | Stake-weighted fork voting | Replay ledger, vote, process txs | Delegated stake, vote accounts |
| Cardano | Stake pools (delegation) | Ouroboros slot leader selection | Stake-pool block production | Pledge plus delegated ADA |
The word “validator” travels across blockchain systems, but it does not always mean exactly the same thing. The underlying role is consistent: a recognized participant with weighted influence over consensus. The surrounding mechanics vary.
In Ethereum, validators are individual protocol identities with explicit deposits and scheduled duties such as proposing blocks, attesting, and sometimes serving on sync committees. In Tendermint and Cosmos-style systems, validators form a weighted set that proposes and votes on blocks, with commits formed by supermajority signatures and an active-set concept that determines who currently participates. In Polkadot, validators secure the relay chain while also taking on parachain-related tasks such as candidate backing, availability distribution, and approval checks. In Solana, validators replay the ledger, vote through per-node vote accounts, and those stake-weighted votes help the cluster decide among forks. In Cardano, the role is operationally expressed through stake pools: delegated stake influences who is chosen to add blocks and receive rewards.
These are genuine differences, not cosmetic branding. Some systems make validator membership highly granular; others concentrate stake through pools or active sets. Some use immediate BFT-style commits; others separate fork choice from finality. Some tie validator identity to a fixed self-bond; others emphasize delegated stake. But the shared idea remains visible: validators are the protocol-recognized carriers of consensus weight.
What operational tasks and risks do validator operators face?
It is tempting to treat validation as passive income attached to stake. That picture is incomplete enough to be misleading. A validator is an always-on operational role.
On Ethereum, running a validator directly means maintaining at least three cooperating software components: an execution client, a consensus client, and a validator client. Operators also need slashing protection, backups, monitoring, alerting, and careful upgrade procedures around Hard Fork. Prysm and Lighthouse documentation both point operators toward these disciplines, and Prysm explicitly provides slashing-protection tooling and operational runbooks for backup, migration, and monitoring.
Other ecosystems show the same pattern in their own vocabulary. Cosmos validators monitor signing info, protect keys, manage availability, and recover from jailing if downtime thresholds are crossed. Polkadot validators deal with staking, assignment, and relay-chain as well as parachain-facing responsibilities. Solana validators must manage performance-sensitive infrastructure because the validator role includes heavy transaction processing and replay. Cardano stake pool operators keep nodes updated, manage performance, and compete on reliability because missed production lowers attractiveness and rewards.
So while the concept of a validator is abstract, becoming one is very concrete: keys, clients, updates, telemetry, failover plans, and disciplined change management. The protocol can define incentives, but the operator has to meet them in the real world.
When does the validator model fail; key assumptions and trade‑offs to watch?
Validators are powerful, but they do not magically solve trust. They shift trust into a specific structure: trust that enough validator weight is economically aligned, that the protocol’s penalty and reward rules are well designed, that implementations correctly follow the spec, and that stake distribution is not dangerously concentrated.
If those assumptions weaken, the validator model weakens with them. A highly centralized validator set may remain technically proof-of-stake while losing much of its decentralization value. A chain with poor client diversity can be one bug away from severe disruption. A protocol with badly calibrated penalties might fail to deter dangerous behavior or might punish benign mistakes too harshly. And proof-of-stake itself is younger and less battle-tested than proof-of-work, so some long-term tradeoffs remain less proven.
There is also a design tension between efficiency and caution. More validator duties, richer checks, and tighter safety rules can improve security but increase complexity, bandwidth, and operational burden. Ethereum’s ongoing proposer-builder separation work shows this clearly: changing how blocks are built and revealed can alter validator duties again, potentially adding committee responsibilities around payload timeliness while deferring some execution validation. The validator role is therefore not fixed forever; it evolves with the consensus design.
Conclusion
A validator is a protocol-recognized participant that uses staked economic weight and signed messages to help a blockchain decide what history counts. It exists because decentralized systems need more than transaction checking; they need a way to turn many local views into one shared chain.
The memorable version is simple: a validator is the unit of accountable consensus in proof-of-stake. It checks, signs, and sometimes proposes. Its signatures matter because the protocol gives them weight. Its behavior matters because that weight is backed by stake that can be rewarded, reduced, or destroyed.
What should you understand about validators before interacting with a chain?
Before relying on validators for staking, large transfers, or interpreting settlement, you should understand their slashing rules, finality thresholds, and client-concentration risks. Fund your Cube Exchange account and use the platform to execute trades or transfers once you’ve checked those infrastructure details.
- Fund your Cube account with fiat on‑ramp or a supported crypto transfer.
- Look up the chain’s validator rules: minimum stake (e.g., 32 ETH), finality conditions, and explicit slashing offenses.
- Inspect candidate validators or pools on public explorers: check recent uptime percentage, any past slashes, and the operator’s client implementation.
- Wait for the chain’s finality/confirmation threshold before treating incoming deposits as settled (for example, wait for the required number of epochs or supermajority attestations).
- On Cube, open the relevant market or transfer flow, choose order or withdrawal details (limit vs market, destination address), review fees and destination, then submit.
Frequently Asked Questions
Staking ties a validator’s consensus weight to bonded capital that the protocol can reduce or destroy; unlike a PoW miner who proves commitment by burning electricity, a validator proves commitment by risking on-chain stake, which lets the protocol credibly punish misbehavior and align operator incentives with chain health.
Protocols punish objectively provable equivocations (for example signing two different blocks for the same slot or double‑voting) with slashing, while many operational failures like missing an attestation or failing to propose usually result only in lost rewards or lighter penalties rather than immediate slashing; exact punishable offences and penalty magnitudes vary by chain and spec.
client diversity reduces systemic risk from buggy implementations: if a single client controls more than one‑third of validator weight it can prevent finality, and if it controls two‑thirds or more it can become dangerously capable of finalizing a bad branch in some scenarios, so operators are encouraged to spread weight across implementations.
If too much validator weight goes offline the protocol may use recovery mechanisms that reduce absent stake influence (for example Ethereum’s inactivity leak) so active validators can restore finality; these mechanisms can be harsh and were historically triggered in testnet incidents, illustrating that large correlated outages can force stake reductions to resume liveness.
Validators do more than check transactions: their signed votes and attestations are the inputs that let the network choose a head and achieve stronger settlement guarantees (finality); finality typically requires a supermajority of weighted signatures so reverting a finalized checkpoint would imply severe or economically catastrophic validator misbehavior.
The validator role is similar in purpose across systems - a recognized, weighted participant that signs consensus messages - but implementations differ: Ethereum uses slot proposers and attestations, Tendermint uses proposer/voter commits with >2/3 weight, Solana relies on replaying the ledger and stake‑weighted votes, Polkadot adds parachain validation duties, and Cardano expresses the role via stake pools.
Running a validator is an operationally intensive, always‑on responsibility: operators must run and coordinate multiple software components (consensus and execution clients, validator clients), maintain slashing protection and backups, monitor telemetry, apply upgrades carefully, and manage performance and security - failure to do so risks missed rewards or slashing depending on the failure mode.
Because validator misbehavior can be proven with signed messages, protocols implement on‑chain enforcement like slashing and forced exits; for example Ethereum’s slashing includes immediate burns and a multi‑day exit process with correlation penalties that can scale with concurrent slashes, though exact formulas can vary and some details remain implementation‑specific.
Emerging designs around MEV and proposer‑builder separation change validator economics and duties by separating block construction from proposer selection and introducing builder markets; these approaches can increase revenue options but also add operational complexity and specific risks that validator guides warn about, so they are considered advanced configurations.
Related reading