What is Monero?
Learn what Monero is, why it exists, and how its privacy works through stealth addresses, ring signatures, RingCT, and Bulletproofs.
Introduction
For the token explainer, see XMR.
Monero is a cryptocurrency designed to make payments private by default. That sounds like a narrow feature, but it changes the structure of the system. In a transparent blockchain, everyone can verify transfers by seeing the sender, the receiver, and the amount. In Monero, the network still verifies that coins are valid and not double-spent, but it tries to do so without revealing the transaction graph in public.
That is the central puzzle Monero is solving. A cryptocurrency needs public verification so strangers can agree on who owns what. Privacy seems to ask for the opposite: hide the details. Monero exists because its designers and community took the view that digital cash should work more like physical cash in one crucial respect: outsiders should not automatically learn your financial history just because you used the system.
The official Monero project describes Monero as a private, decentralized cryptocurrency focused on confidential and censorship-resistant transactions. It also presents Monero as electronic cash: something people can hold themselves, send globally, and use without relying on a bank or card network. That framing matters, because Monero is not mainly trying to be a general-purpose smart-contract platform. Its design choices are concentrated around one use case: private transfer of value.
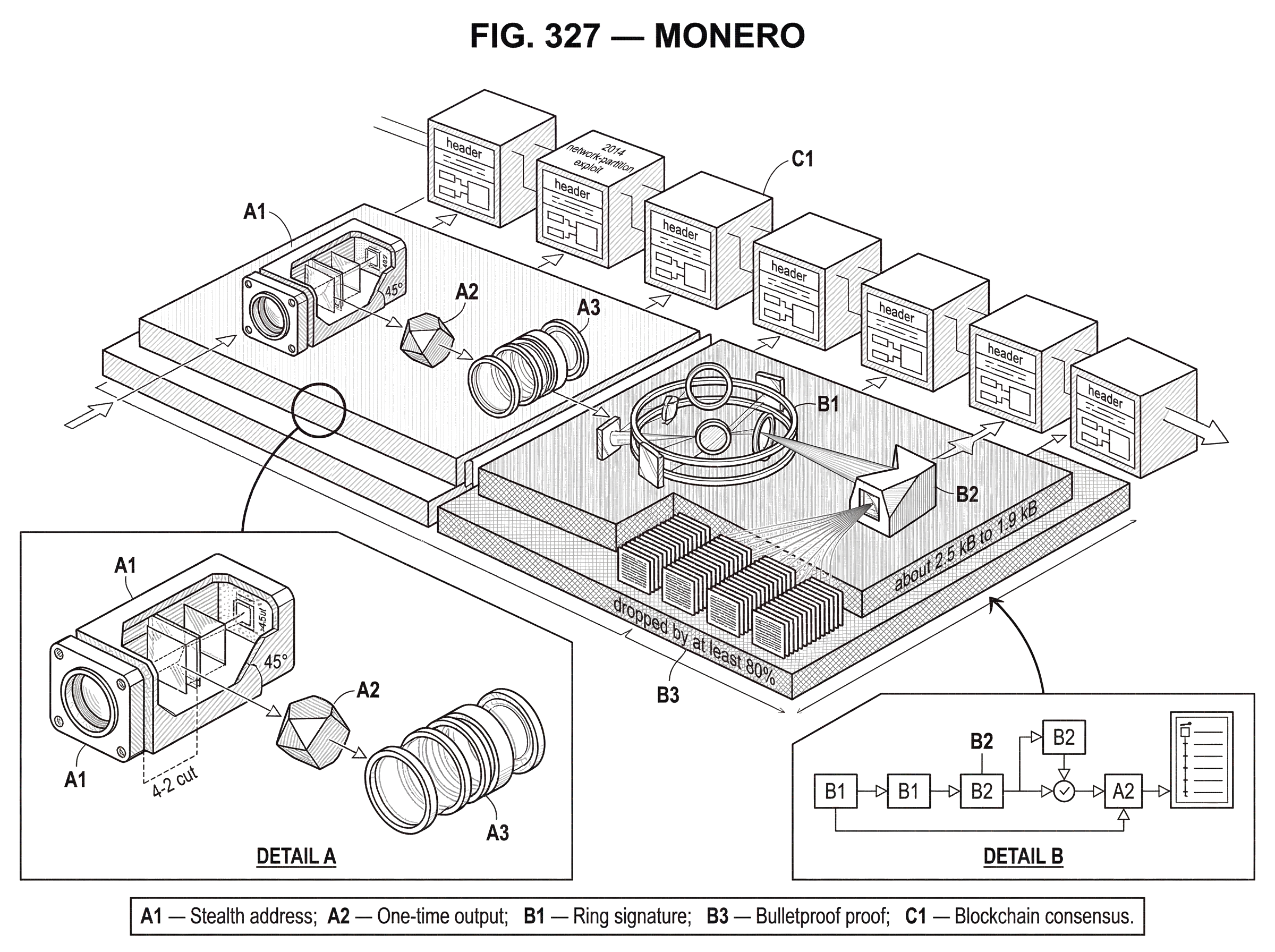
To understand Monero, the key idea is this: it does not bolt privacy onto a transparent ledger. It changes what the ledger exposes in the first place. The sender is obscured with ring signatures, the receiver is hidden behind one-time destination addresses called stealth addresses, and the amount is concealed with confidential transactions, specifically Monero’s RingCT system. Around those pieces, the protocol still has to preserve the normal invariants of a cryptocurrency: no counterfeit coins, no double-spends, and consensus on a shared chain.
Why does Monero exist and what problem does it solve?
A transparent cryptocurrency has an awkward property. It may be decentralized in who can use it, yet deeply centralized in who can analyze it. If every coin carries a fully visible history, then exchanges, merchants, analytics firms, governments, and even curious strangers can sort coins by origin, behavior, and association. That creates a tension with the idea of fungibility.
Fungibility means units of a currency are interchangeable. One dollar is supposed to be as good as another dollar. In a transparent ledger, that can weaken. A coin that once passed through a hack, a sanctioned address, a gambling site, or simply an unpopular counterparty may be treated differently from an otherwise identical coin. Monero’s claim is that privacy is not just about secrecy for its own sake. It is a mechanism for preserving fungibility, because if transaction histories are not publicly traceable, coins are harder to stigmatize based on their past.
That also explains why Monero makes privacy the default rather than an optional mode. Optional privacy often leaks information through contrast. If only some users shield their activity, choosing privacy can itself become a signal. Monero’s approach is to put everyone inside the same privacy set by default. The project explicitly contrasts this with selectively transparent systems. The intended consequence is that privacy is not a special action you take; it is the ordinary way the network works.
This does not mean privacy is absolute in every threat model. The official site sometimes uses language like “cannot be traced,” but that should be read as a design goal and strong claim about default on-chain privacy, not as a license for careless assumptions. Real privacy depends on many layers: protocol design, wallet behavior, network metadata, user habits, and the quality of decoy selection over time. Monero is best understood as a system that works very hard to reduce what the blockchain itself reveals.
How does Monero hide payment recipients using stealth addresses?
Start with the easiest part to picture: the recipient. In Bitcoin-like transparent systems, if you publish an address and many people pay it, anyone can often see that those payments went to the same destination. Even if the person behind the address is unknown, the address becomes a public bucket that accumulates a visible history.
Monero avoids this with stealth addresses. A user has a public address, but that address is not what appears as the final destination on-chain. Instead, for each payment, the sender derives a fresh one-time public key for the recipient. The blockchain records that one-time destination, not the recipient’s reusable public address.
The mechanism comes from the CryptoNote design that Monero inherited and extended. The sender combines the recipient’s public address information with fresh randomness to derive a unique output key. The important consequence is simple: two payments to the same person do not look like they went to the same place. Only the recipient, using their private keys, can scan the blockchain and recognize which outputs belong to them and recover the corresponding one-time private keys needed to spend those outputs later.
A useful analogy is a mailroom that gives a different private mailbox number to every sender, while still letting the intended recipient open the mail. That explains why outside observers cannot group all incoming payments to one person by looking for a common public address. Where the analogy fails is that Monero is not relying on a trusted mailroom. The one-time address is derived cryptographically so that the network can include it publicly while only the intended recipient can claim it.
This property is usually described as unlinkability on the receiving side. If two outputs were sent to the same person, an outside observer should not be able to prove that fact from the chain alone.
How does Monero hide the sender with ring signatures and key images?
| Primitive | Purpose | Reveals | Double-spend check | Trade-off |
|---|---|---|---|---|
| Ring signature | Obscure spent output | Ring members only | Relies on key image | adds signature size |
| Key image | Detect duplicate spend | no output identity | Unique tag per output | must be unique or reject |
| CLSAG (current) | Compact ring signatures | same anonymity as MLSAG | Still uses key images | smaller, faster verification |
Hiding the receiver is only half the problem. A spend also reveals which previous output is being consumed. In a transparent UTXO system, that is usually explicit: this input spends that earlier output. Once that link is public, transaction tracing becomes a graph problem.
Monero breaks that graph with ring signatures. When a user spends an output, the transaction input is formed not as a plain pointer to a single visibly real output, but as a signature over a set of possible outputs. That set is called a ring. One member of the ring is the real output being spent; the others are decoys selected from the blockchain.
The verifier learns that one member of the ring is authorized to spend, but not which one. This is the compression point for understanding Monero’s sender privacy: the chain no longer says “this exact coin moved.” It says, in effect, “one of these plausible coins authorized this spend.” If the decoys are well chosen and the ring structure is sound, the sender gets plausible deniability among the ring members.
But a cryptocurrency also needs to stop double-spends. If the network cannot tell which ring member was real, how can it know whether the same real output has already been spent elsewhere? Monero’s answer is the key image. A key image is a cryptographic tag derived from the real output’s private spend key in a way that does not reveal which output in the ring is real, but does let the network detect reuse. If the same output is spent twice, the same key image appears twice, and the duplicate is rejected.
This separation is elegant. The ring signature says, “I am one of these possible owners.” The key image says, “if I ever try to spend the same hidden coin again, you will catch me.” Privacy and double-spend protection are doing different jobs, and Monero needs both.
Monero’s ring-signature system has evolved. The RingCT research work used MLSAG signatures, and later Monero adopted CLSAG, which the official documentation describes as preserving the same functionality while reducing transaction size and improving verification speed. The Moneropedia page gives a concrete example: a typical 2-input, 2-output transaction fell from about 2.5 kB to 1.9 kB with CLSAG, with roughly 20% faster signature verification. That kind of improvement matters because privacy that is too expensive tends not to scale well.
How does Monero hide transaction amounts with RingCT and Bulletproofs?
| Approach | On-chain visibility | How validated | Main overhead |
|---|---|---|---|
| RingCT + Bulletproofs | amounts hidden | commitments + range proofs | compact aggregated proofs |
| Transparent amounts | amounts public | direct arithmetic checks | no range-proof overhead |
If sender and receiver are hidden but amounts remain public, a lot can still leak. An unusual amount can help correlate transactions. Merchants can be identified by repeated exact-price patterns. Change outputs can become easier to guess. So Monero also hides amounts.
This is what Ring Confidential Transactions, or RingCT, are for. RingCT combines ring-signature-based sender privacy with confidential transactions, which use cryptographic commitments to hide values while still allowing the network to verify arithmetic consistency.
The basic idea is subtle but not mystical. Instead of placing a visible amount on-chain, Monero commits to an amount using a blinding factor. A commitment hides the number, but it still behaves algebraically. That means validators can check whether the committed inputs equal the committed outputs plus the fee, without learning the amounts themselves.
Why is that enough? Because the core monetary invariant of a transaction is not “everyone sees the numbers.” It is “the transaction does not create money from nowhere.” Commitments preserve the ability to check that invariant. In the RingCT paper, the commitment is described in Pedersen-style form, where the hidden amount and a masking value are combined into a point that conceals the amount as long as certain discrete-log relationships remain unknown.
There is an immediate complication. If amounts are hidden inside commitments, a malicious user might try to commit to a negative number or exploit overflow so that the commitments balance while still creating spendable value. That is why Monero also needs range proofs: proofs that each hidden output amount lies in an allowed nonnegative range.
Early range proofs in RingCT were large, which made transactions heavy. Monero later adopted Bulletproofs, a form of short non-interactive zero-knowledge proof with no trusted setup. The official Monero documentation explains why that mattered: Bulletproofs let multiple committed amounts be proven in range efficiently, and after deployment the average Monero transaction size dropped by at least 80%, with fees falling accordingly. That is a rare example where a cryptographic improvement directly changed user experience.
So by this point, the three pieces fit together. Stealth addresses hide who received a payment. Ring signatures hide which prior output was actually spent. RingCT and Bulletproofs hide the amount while still proving that the transaction balances correctly.
What does a Monero transaction look like end-to-end?
Imagine Alice wants to pay Bob in a transparent cryptocurrency. She sends coins from a visible input to Bob’s visible address, and the amount is public. Anyone watching the chain can often follow the movement directly.
In Monero, the same payment looks very different. Alice starts from one of her spendable outputs, but when she builds the transaction, she does not expose that output as the sole obvious source. She forms a ring that includes her real output and a set of decoys from the chain. She then produces a ring signature proving that one member of the ring is legitimately spendable by her, while publishing a key image so the network can reject any later attempt to spend that same real output again.
On the receiving side, Alice does not send directly to Bob’s reusable address in a way the chain can recognize. She uses Bob’s public address data plus fresh randomness to derive a one-time destination key. Observers see an output, but they cannot tell it belongs to Bob or link it to Bob’s other receipts. Bob’s wallet later scans the chain, recognizes that this one-time output is his, and derives the private key needed to spend it.
For the amount, Alice does not publish the numeric value in the clear. She commits to the value, and the transaction includes proofs that the hidden outputs are valid and in range. Validators check the cryptographic equalities and proofs rather than inspecting visible amounts.
The result is not that the network “trusts Alice.” It is the opposite. The network still verifies everything it needs: authorized spending, no double-spend, no hidden inflation. What changes is what counts as sufficient evidence. Monero replaces public transaction legibility with cryptographic proof.
Which standard blockchain features does Monero retain and how do they differ?
It is easy to overfocus on the privacy machinery and forget that Monero is still a blockchain network. It has nodes, wallets, miners, consensus rules, mempool behavior, software releases, and network upgrades. The Monero core repository describes it as the core open-source implementation and notes that consensus changes are introduced through scheduled network upgrades, effectively hard forks that require users and service providers to run current software.
That upgrade model reveals something important about Monero as a living protocol. Privacy is not solved once and then left alone. It depends on parameter choices, transaction structure, proof systems, and implementation quality, all of which may need revision. The move from older range proofs to Bulletproofs, and from MLSAG to CLSAG, are examples of the network changing its internals to improve efficiency while preserving the privacy model.
Monero is also a research-heavy project. The official site highlights the Monero Research Lab, and the ecosystem includes public technical writing such as Mastering Monero and Zero to Monero. That is not cosmetic. A privacy protocol cannot rely on slogans; it has to survive adversarial analysis. The project also maintains a vulnerability response process, which is another healthy sign: serious cryptographic software assumes bugs and attack surfaces exist.
What are the assumptions and limits behind Monero's privacy?
| Assumption | How privacy leaks | Mitigation |
|---|---|---|
| Decoy selection | age bias makes real input guessable | update sampling; enforce larger ringsize |
| Network metadata | propagation timing or IP leaks sender | Tor integration; relay privacy measures |
| Implementation bugs | code flaws can partition or expose data | external audits; vulnerability response |
The clearest mistake a smart reader can make is to treat Monero’s privacy claims as magical or assumption-free. They are not. They are stronger than those of transparent chains at the protocol level, but they still depend on design details.
A good example is decoy selection. Ring signatures protect the sender by mixing the real spend with plausible alternatives. But if the decoys are poorly chosen, the ring can leak clues. An influential empirical study found that older Monero transaction patterns and mixin sampling made many inputs vulnerable to tracing heuristics, including chain-reaction analysis and an age-based “newest output” guess. Monero’s official response agreed with parts of that critique, noted that some vulnerabilities were tied to older transaction formats and older sampling algorithms, and described protocol changes that reduced the problem over time.
This matters for two reasons. First, it shows that privacy is statistical as well as cryptographic. A ring signature can be mathematically valid while still being weakened by bad decoy distributions. Second, it shows why Monero insists on continuing protocol development. The abstract primitive is not the whole story; the surrounding policy choices are part of the privacy system.
Network-level metadata is another limitation. Even if the blockchain hides sender, receiver, and amount, an observer who controls internet infrastructure or watches entry points may still learn something from transaction propagation. The Monero software includes experimental integration with Tor, which reflects the fact that transport privacy is related to, but distinct from, on-chain privacy.
There are also ordinary software and implementation risks. Monero’s history includes a notable 2014 network-partition exploit rooted in a CryptoNote tree-hash bug that allowed two distinct blocks with the same hash. That incident was patched quickly, but it is a useful reminder that privacy protocols do not get a free pass on consensus engineering. A chain can be cryptographically ambitious and still fail in mundane code.
So the right way to phrase Monero’s privacy is not “nothing can ever leak.” It is: Monero is built so that the blockchain itself reveals far less by default, and the community has repeatedly revised the protocol where practical leakage was discovered.
Who uses Monero and what are its common use cases?
Because Monero is designed as private digital cash, its uses follow naturally from that design. People who do not want their payment history exposed to counterparties, analysts, employers, competitors, or the general public find the default privacy attractive. Merchants who do not want customers or suppliers to inspect their full transaction history can care about it for the same reason. The official project site also emphasizes low-fee payments, global transfers, and self-custody through wallets rather than bank accounts.
There is also a philosophical use case. Some users see financial privacy as a normal civil condition, not an exceptional one. For them, Monero is not just a tool for hiding; it is an argument about what digital money should reveal by default. In that sense it sits in contrast with transparent systems where auditability is public and privacy requires extra tools layered on top.
That contrast becomes especially clear when compared with Zcash. Monero’s project materials explicitly note the difference between default privacy and selective transparency. The important point is not that one design is universally superior. It is that they optimize different things. Monero chooses mandatory privacy at the transaction layer, even though that can make auditing, exchange support, and analytics harder. That is not an accidental side effect. It is the design.
How is Monero governed and how does its funding model work?
Monero is unusual not only technically but organizationally. The official site and repository emphasize that it is a decentralized, volunteer-driven project with contributions from hundreds of developers over time. Funding for work often flows through the Community Crowdfunding System, where ideas move through public stages from proposal to funding to work in progress and completion.
That structure has consequences. It tends to align with the project’s anti-centralization ethos, and it lets the community fund research, implementation, audits, and infrastructure. At the same time, it means Monero is not a company with a conventional product roadmap. Much of its resilience comes from open-source continuity, public discussion, and the fact that no single institution fully defines the project.
For a privacy network, that governance style is more than culture. It affects how quickly vulnerabilities are addressed, how audits are funded, and how protocol upgrades are coordinated. The Bulletproofs rollout, for example, involved external audits funded by the community before mainnet activation.
Conclusion
Monero is a blockchain built around one hard idea: a network can verify money without making everyone’s financial history public. It does that by changing the evidence the chain exposes. Stealth addresses hide the recipient, ring signatures and key images obscure the true spender while still stopping double-spends, and RingCT with Bulletproofs hides amounts while preserving the no-inflation checks a currency needs.
The simplest way to remember Monero is this: it is not a transparent ledger with privacy added on top. It is a ledger designed so privacy is the default condition of using the system. That does not make it perfect or assumption-free, but it explains why Monero exists, why it remains technically distinctive, and why it still matters in the broader landscape of digital money.
How do you buy Monero?
To buy Monero (XMR) on Cube, fund your account and place a spot order on the XMR market. The Cube workflow is: deposit fiat or a supported crypto, open the XMR spot market (for example XMR/USDC or XMR/USD), choose an order type, and submit the trade.
- Deposit fiat via the on-ramp or transfer a supported crypto (e.g., USDC) into your Cube account.
- Open the XMR/USDC or XMR/USD spot market on Cube.
- Choose an order type: use a market order for immediate execution or a limit order to target a specific price (enter XMR amount or spend amount and set your limit price).
- Review the estimated fill, fees, and total XMR received, then confirm and submit the order.
Frequently Asked Questions
Monero uses key images: a cryptographic tag derived from the real output’s private spend key that does not reveal which ring member was spent but is identical if the same real output is spent twice, so duplicate key images let the network reject double-spends.
A sender derives a fresh, one-time public key for each payment using the recipient’s public address data plus randomness; the blockchain records only that one-time destination and the recipient later scans the chain with their private keys to recognize and spend outputs addressed to them, preventing observers from linking multiple payments to the same reusable address.
Monero hides amounts with RingCT: values are committed (Pedersen-style commitments) so validators can verify inputs equal outputs plus fee without seeing numbers, and range proofs (now Bulletproofs) prove committed amounts are nonnegative so no money can be illicitly created.
No - Monero’s on-chain privacy is strong by design but not absolute: it depends on protocol choices, wallet behavior, decoy-selection quality, network-level metadata, and user habits; empirical studies found weaknesses in older mixin sampling that the project addressed but which illustrate that privacy is statistical as well as cryptographic.
Bulletproofs replaced earlier large range proofs with much shorter non‑interactive zero‑knowledge proofs (no trusted setup), which cut average Monero transaction size significantly (the article cites an average transaction size drop of at least ~80%) and lowered fees, improving scalability and usability.
Monero’s ring-signature scheme evolved from MLSAG to CLSAG; CLSAG preserves the same anonymity functionality while reducing transaction size and improving verification speed (the article gives an example of a 2-input/2-output transaction shrinking from ~2.5 kB to ~1.9 kB and roughly 20% faster verification), and CLSAG was activated via a network upgrade.
Monero deliberately makes privacy the default so everyone shares the same privacy set, which preserves fungibility and avoids privacy-choices becoming signals; this design, however, trades off easier public auditability and can make exchange support and analytics more difficult compared with selective-transparency designs like Zcash.
There have been notable incidents and analyses: a 2014 CryptoNote tree‑hash bug caused a temporary network partition that was patched, and academic/empirical work (circa 2017) showed deanonymization risks from older mixin-selection rules; Monero’s project publicly acknowledged such findings and revised protocol and client behavior to reduce those leakages.
Related reading