What is Ring Signatures?
Learn what ring signatures are, how they hide the real signer in a group, why they matter for privacy, and how Monero uses linkable variants.
Introduction
Ring signatures are a kind of digital signature that prove a message was signed by one member of a chosen group without revealing which member it was. The striking part is not just the anonymity; it is how little setup they require. A signer can take their own secret key, collect other people’s public keys, and produce a valid signature for the whole set without asking permission, creating a group in the moment rather than relying on any administrator or prearranged membership system.
That solves a specific privacy problem ordinary signatures do not solve. A normal digital signature answers the question, “Did Alice sign this?” A ring signature answers a different question: “Did someone in this set sign this?” That change sounds small, but it changes what can be proven and what can be hidden. It is why ring signatures matter in anonymous leaking, in some forms of private authentication, and in privacy-focused cryptocurrencies where the goal is to authorize spending without revealing which previous output is actually being spent.
The core idea becomes easier to see if you start from the tension a signature normally creates. A signature is useful because it ties an action to a key. But privacy often requires the opposite: proving authorization without creating a precise public link to one identity. Ring signatures are one way to resolve that tension. They keep the “someone authorized this” part of a signature while weakening the “we know exactly who” part into “we know it came from this set.”
How do ring signatures prove membership in a set rather than identifying a signer?
A ring signature works by shifting the unit of authentication from an individual to a ring, meaning a set of possible signers. If the ring contains r public keys, a valid ring signature tells a verifier that the signer knows the secret key for one of those public keys, but the verifier should not be able to tell which one with probability better than 1/r from the signature alone.
That is the central invariant: validity proves membership in the set, not identity within the set. If you remember only one thing about ring signatures, remember that. The signer is not claiming “I am key number 4.” The signer is claiming “I am one of these r keys, and that is enough for this purpose.”
This is why the original ring-signature paper emphasized being set-up free. In a group signature scheme, there is typically some enrollment process, a group manager, membership issuance, and often revocation machinery. Ring signatures deliberately remove that structure. Any user can assemble an ad hoc ring out of public keys that already exist. That makes them flexible in exactly the situations where prior coordination is undesirable or impossible.
A simple example is anonymous disclosure. Imagine a journalist receives a signed document that could have come from any one of several senior officials. With a normal signature, the official would be exposed. With no signature, the document is less credible. With a ring signature over the public keys of all those officials, the journalist gets a useful middle ground: the document was signed by someone in that set, but the signer is hidden among them. The mechanism gives authenticity at the level that matters while withholding the narrower fact that would destroy anonymity.
An analogy helps here, though only up to a point. A normal signature is like a handwritten name on a letter. A ring signature is more like a seal that proves the author belongs to a particular circle without identifying which member. What the analogy explains is the difference between individual attribution and set membership. Where it fails is that a ring signature is still a precise cryptographic proof, not a vague social marker: the verifier can check validity mathematically, not just heuristically.
How is a ring signature generated step by step?
At a high level, the signer starts with a message, a list of public keys, and their own secret key corresponding to one key in that list. The signature algorithm must do two things at once.
First, it must convince a verifier that the signer really knows one of the secret keys in the ring. Without that property, anyone could fabricate signatures over arbitrary groups, and the scheme would be useless.
Second, it must arrange the proof so that every public key in the ring looks like a plausible source. That is the privacy side. The verifier should see a single coherent signature object, not a trail that points more strongly to one ring member than the others.
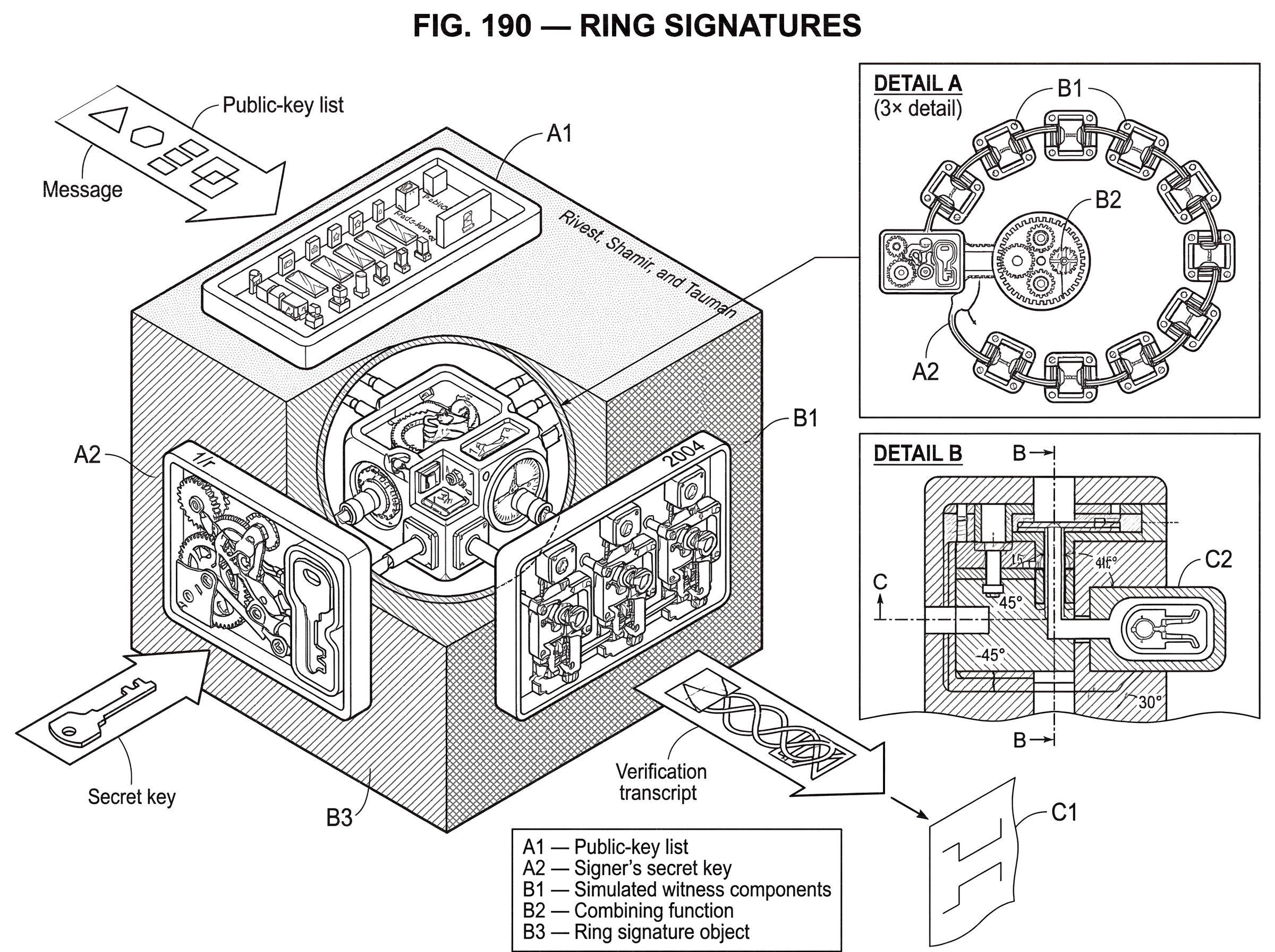
The original formalization by Rivest, Shamir, and Tauman achieved this with a clever “close the loop” construction. Intuitively, the signer simulates the proof components for all the non-signers and then uses their real secret key to make the whole cyclic consistency check come out correctly. The signature is built so that all ring members contribute to one verification equation arranged in a circle. Because the loop closes, the verifier can see that some member had the right witness, but the final transcript does not reveal which member supplied the real secret rather than a simulated value.
That “simulation plus one real witness” pattern is common in anonymous proof systems. The subtle part is making the simulated pieces indistinguishable from the real one. In the original construction, the combining function that ties the pieces together matters a lot. The paper explicitly avoids simple algebraic combiners like XOR or modular sums because those can open the door to offline attacks. Instead, it uses a nested symmetric-encryption-based combiner so the signature components feed into one another in a way that is hard to exploit algebraically.
This is a good place to separate intuition from formal security. The intuition is that the signer fills in most of the ring “from the outside” and then uses the true secret key once to satisfy the remaining constraint. The formal claim is stronger: the construction can be proven unforgeable in the random oracle model by reduction to breaking the underlying trapdoor one-way primitive, and its signer ambiguity can be extremely strong in the original model.
What does a verifier learn from a ring signature, and what remains hidden?
A verifier of a ring signature learns three things.
The first is that the signature is structurally valid for the given message and the listed public keys. The second is that the signer knows at least one corresponding secret key. The third is that the signer intended to sign as a member of that ring, because the ring itself is part of what is signed.
What the verifier does not learn is which ring member signed. In the original ring-signature formulation, this can be very strong: signer ambiguity is described as unconditional in the sense that even an unbounded adversary should not be able to identify the actual signer with advantage better than random guessing among the r ring members, under the stated model and construction. That is stronger than ordinary computational hiding claims, where anonymity holds only against feasible attackers.
There is also an important non-property: a ring signature does not usually tell you anything about whether the same hidden signer produced another different signature. Basic ring signatures give anonymity, but not accountability across signatures. That is why later variants introduced linkable ring signatures, which preserve anonymity while exposing a special linking tag when the same secret key signs more than once under the relevant conditions.
This distinction matters especially in blockchains. A cryptocurrency cannot allow fully anonymous spending proofs if that means the same coin can be spent twice with no detectable relation. The network needs a way to preserve sender ambiguity and detect double-spending. That requirement is what pushes practical transaction systems toward linkable variants rather than the original unlinkable form.
Ring signatures vs group signatures: when and why to use each?
| Aspect | Ring signatures | Group signatures | Best when |
|---|---|---|---|
| Setup | No setup, ad hoc | Managed enrollment | Permissionless anonymity |
| Membership control | Signer picks ring | Central authority issues keys | Ad‑hoc vs governed groups |
| Revocation / opening | No opener or revocation | Opener and revocation possible | When accountability required |
| Signature size | Grows with ring size | Often compact via group state | Large vs small representation |
| Spontaneity | Immediate, permissionless | Requires coordination | Quick anonymous actions |
The cleanest way to understand ring signatures is to compare them with the neighboring idea they were partly reacting against: group signatures.
Both let a verifier know that a signer belongs to some set. But the way that set comes into existence is fundamentally different. In a group signature system, membership is managed. Someone defines the group, admits members, often issues credentials, and sometimes retains the power to “open” a signature and reveal who signed. That model is useful when anonymity exists inside an institution that still wants administrative control.
Ring signatures remove that center. There is no group manager, no setup phase, no enrollment, no revocation procedure built into the primitive, and no opening authority. The signer simply chooses a ring of public keys that includes their own and signs. This makes ring signatures spontaneous and ad hoc.
That freedom comes with a tradeoff. Because the verifier must know which public keys are in the ring, the signature has to include or commit to that list. As the original paper notes, this means ring signatures inherently grow linearly with ring size. That is not just an implementation accident; it follows from the fact that the anonymity set is assembled on the fly and has to be communicated somehow. Group signatures can sometimes be much more compact because the group is predefined and represented by shared structure rather than an explicit list.
So the design choice is not “which is better in the abstract.” It is “which problem are you solving?” If you need spontaneous, permissionless anonymity among arbitrary public keys, ring signatures fit naturally. If you need managed membership, revocation, and perhaps identity opening under policy, group signatures solve a different problem.
What privacy guarantees do ring signatures provide, and where can they fail?
The privacy guarantee of a ring signature is easy to state and easy to overstate.
Cryptographically, the promise is about the signature transcript itself. Given a valid signature and the ring, the verifier should not be able to tell which listed key actually signed, beyond the scheme’s stated leakage. In the classic construction, that leakage is intended to be essentially none beyond ring membership.
But practical privacy depends on more than the cryptographic object. If the ring is badly chosen, the anonymity can collapse without the signature scheme itself failing. Suppose a ring contains one plausible signer and nine obviously irrelevant keys. The signature is still valid, but the real anonymity set is weaker than the nominal ring size suggests. Privacy therefore depends not just on the signature algorithm but on how the ring members are selected and what outside information exists about them.
This point becomes concrete in cryptocurrencies. In Monero-style systems, a transaction input is signed against a ring of candidate previous outputs. Only one is real; the rest are decoys. The ring signature hides which one is being spent. But if the decoy-selection process poorly matches real spending behavior, observers may still guess the real input with high probability using metadata and statistical heuristics. Empirical studies of older Monero transactions found exactly this kind of weakness: historical use of zero-decoy transactions and flawed decoy sampling sharply reduced effective privacy for many transactions even though the ring-signature primitive itself remained intact.
That is a general lesson. Ring signatures provide cryptographic ambiguity, not magical immunity to context. If side information, timing, reuse patterns, or ring-construction rules leak structure, an attacker may narrow the true signer well below the nominal 1/r ideal.
How do linkable ring signatures let systems detect repeat signers without revealing identities?
The next conceptual step is understanding why many deployed systems use linkable ring signatures rather than the original form.
Pure ring signatures hide the signer and do not naturally reveal whether two signatures came from the same secret key. That is perfect for some applications, such as anonymous leaking, where repeated participation should not create a detectable pattern.
But some systems need a hidden signer to be anonymous only up to a point. An e-voting system may want each voter to remain anonymous while still making double-voting detectable. A cryptocurrency may want each spender to remain hidden among decoys while still making double-spending impossible. In both cases, the system wants anonymity plus a limited form of accountability.
This is what LSAG, the Linkable Spontaneous Anonymous Group signature construction, adds. It keeps the ad hoc nature of ring signatures but introduces a linkability tag derived from the signer’s secret key and the ring context. Two valid signatures by the same signer over the same relevant key list produce the same tag, allowing a verifier to link them, while still not revealing which member signed.
That sounds paradoxical at first: how can signatures be linkable without identifying the signer? The mechanism is that the tag is a stable pseudonym tied to the hidden key, not the key itself. You can think of it as learning “the same anonymous member acted twice” without learning which member. The LSAG paper proves anonymity and linkability in the random oracle model under computational assumptions rather than unconditional anonymity as in the original ring-signature construction.
There is a subtle limit here too. In LSAG’s original form, linkability applies with respect to the same public-key list. That is enough for some applications, like a fixed voter roll, but blockchains need stronger behavior because spend detection cannot depend on reusing the exact same decoy set. That leads to further variants.
How do privacy coins use ring signatures to hide which output is spent?
| Component | Purpose | Protects | Mechanism |
|---|---|---|---|
| Ring signature | Hide which input is spent | Sender ambiguity | Ad‑hoc ring of candidate outputs |
| Key image | Prevent double‑spend | Consensus integrity | One‑way tag from signing key |
| Stealth address | Hide recipient identity | Receiver unlinkability | One‑time derived public keys |
| RingCT / MLSAG / CLSAG | Hide amounts and scale proofs | Amounts + multi‑input privacy | Linkable multilayer signatures + commitments |
The most widely known real-world use of ring-signature ideas is in privacy-focused cryptocurrencies, especially the CryptoNote family and Monero.
In that setting, the problem is not anonymous messaging but anonymous spending. A transaction input must prove that the spender controls some previous output. With ordinary signatures, the specific output being spent is obvious. Ring signatures change the statement. The transaction instead proves that the spender controls one output in a ring of candidate outputs, without revealing which one.
On its own, that would create a serious accounting problem. If the network cannot tell which output is real, how can it stop the same real output from being spent twice in two different rings? The answer is the key image. In Monero’s linkable ring-signature family, a key image is a value derived from the real signing key in a way that does not reveal the key itself but stays the same if that key is reused. Verifiers check signatures normally, and the network also checks that no key image has appeared before. If the same output is spent twice, the repeated key image exposes the double-spend attempt.
This is the blockchain version of the earlier paradox. The network learns “this hidden spender is the same as before” without learning who the spender is among the ring members. The key image is what turns anonymous authorization into something compatible with consensus rules.
Monero’s implementations evolved through several ring-signature variants. Expository materials describe SAG as the basic ring-signature form, then bLSAG and MLSAG as linkable and multilayered variants. MLSAG matters because a modern confidential transaction often has to prove knowledge across multiple related keys at once, not just a single secret. Later, CLSAG was introduced as a more concise replacement with smaller transaction size and faster verification while preserving the needed functionality.
Here the internal logic of the system is worth seeing clearly. The ring signature hides the real input among decoys. Stealth addresses handle receiver privacy by making outputs one-time and unlinkable to a public address. RingCT extends the transaction so amounts can be hidden using commitments and range proofs. These are complementary pieces, not substitutes. Ring signatures hide which input is real; stealth addresses hide who received outputs; confidential-transaction machinery hides how much was sent.
Worked example: spending an output with a ring signature and a key image
Imagine Alice wants to spend one output on a privacy-focused chain. Publicly, there are many previous outputs on the ledger that look structurally compatible with being spent the same way. Her wallet chooses several of them as decoys and places the true output among them, forming a ring.
Alice now needs to prove to the network that she controls one member of that ring. The signature she creates shows exactly that: one of these listed outputs is spendable by me, and I know the necessary secret for it. The verifier can check the cryptographic consistency of the whole ring, but cannot tell which listed output is the real one from the signature alone.
At the same time, Alice computes a key image from the real secret key. This key image is published with the signature. It does not reveal which ring member is real, but if Alice tried to spend the same real output again in a different transaction with a different ring of decoys, the resulting key image would repeat. Nodes reject that second spend because the repeated key image shows that the same hidden secret has already been used.
If the transaction also hides amounts, additional proofs are attached. Commitments let the network verify that inputs equal outputs plus fees without revealing the values themselves. Range proofs prevent cheating with negative or overflowed amounts. The ring signature is therefore only one piece of the transaction proof, but it is the part that protects sender ambiguity.
What makes this example important is that it shows both the strength and the limit of ring signatures in practice. The signature can hide the true input cryptographically. But whether observers can still make strong guesses depends heavily on the quality of the decoys, transaction timing, output ages, and historical protocol choices.
What cryptographic assumptions and proof models support ring-signature security?
| Property | What is proven | Assumption / model | Practical strength |
|---|---|---|---|
| Unforgeability | Reduces to breaking trapdoor primitives | Random Oracle Model (ROM) | Strong computational assurance |
| Anonymity | Signer‑ambiguity for listed ring | ROM or information‑theoretic (variant) | High cryptographic hiding; context matters |
| Linkability | Detects reuse via link/tag | Computational (DDH/DL) in ROM | Enables double‑spend detection |
It is tempting to talk about ring signatures as if they simply “guarantee anonymity.” The source material is more careful, and it is worth keeping that care.
The original ring-signature construction of Rivest, Shamir, and Tauman gives a very strong anonymity claim, but its forgery resistance is proven in the random oracle model rather than the standard model. That means the proof treats certain hash-like functions as idealized random functions. This is common in practical cryptography, but it is still a modeling choice, not a theorem about every concrete implementation.
Later linkable variants such as LSAG also rely on random-oracle-model proofs, with anonymity and linkability reduced to assumptions like DDH or discrete log hardness. CLSAG’s proofs likewise rely on the random oracle model and stronger assumptions such as k-OMDL for unforgeability. In recent whole-system analyses of Monero’s RingCT, researchers have argued that standard component definitions alone were not enough and introduced more holistic models, sometimes using the algebraic group model to handle subtle issues in the linkable ring-signature component.
So here is the honest summary: ring signatures are not a hand-wavy privacy trick. They have serious formal foundations. But the exact strength of their guarantees depends on the variant, the proof model, the hardness assumptions, and the surrounding protocol. The cryptography is rigorous, but it is not assumption-free.
What practical limits and trade-offs affect ring-signature deployments (efficiency, decoys, features)?
The first structural strain is efficiency. In classic ring signatures, and in many deployed descendants, cost grows with ring size because the verifier must process evidence relative to each member of the ring. This is the price of getting anonymity from an explicitly listed ad hoc set. Research lines such as CLSAG and Omniring try to reduce these costs, especially in systems where larger rings would improve practical privacy.
The second strain is anonymity-set quality. A ring of size 16 is not automatically “16-way anonymity” in any practical sense if 15 members are poor decoys. This is not a flaw in the abstract signature primitive so much as a warning that privacy engineering lives at the system boundary, where cryptography meets data distribution and user behavior.
The third strain is feature tension.
The more a system asks from the signature the more complicated the construction becomes.
- linkability
- multisignature behavior
- hidden amounts
- shared rings across inputs
- refund logic
- compactness
Monero research shows this progression clearly: from linkable signatures to multilayer signatures, compact variants, and specialized constructions such as DLSAG for dual-key outputs. Each extension solves a real protocol need, but each also creates new assumptions, new checks, or new heuristic risks.
Conclusion
A ring signature is a digital signature that proves someone in a chosen set signed a message without revealing who. Its most important innovation is not anonymity alone, but spontaneous anonymity: the signer can create the group on the fly from public keys that already exist, with no manager, no setup, and no permission.
That simple shift (from authenticating an identity to authenticating membership in a set) is why ring signatures matter. It makes possible credible anonymous disclosure, privacy-preserving authentication, and sender ambiguity in private cryptocurrencies. But the cryptographic object is only part of the story. In practice, privacy depends not just on the signature scheme, but on the ring you build, the metadata you leak, and the assumptions your system relies on.
What should you understand about ring signatures before trading, depositing, or transferring privacy coins?
Understand that ring signatures give membership anonymity but not perfect, context-free privacy. Before trading, depositing, or withdrawing privacy-focused assets, confirm the chain and wallet behaviors that matter and then use Cube Exchange to move funds or trade.
- Check the asset’s privacy model: read the token or chain docs to confirm whether it uses linkable ring signatures (key images/LSAG/CLSAG) and whether amounts or outputs are confidential.
- Inspect recent on-chain transactions or the project’s explorer to confirm default ring size, decoy-selection behavior, and whether linkability tags or key images appear on spend transactions.
- Fund your Cube Exchange account via fiat or a supported crypto transfer on the correct network, then open the deposit or withdraw flow for the privacy asset you plan to use.
- When withdrawing to a personal wallet, send only to a non-custodial wallet that supports the chain’s ring-signature standard and confirm the wallet’s current version; after the transfer, verify the expected ring-size or key-image behavior on-chain and wait for standard confirmations before sharing any transaction details.
Frequently Asked Questions
A ring signature proves that someone who holds a secret key corresponding to one of the public keys in an explicitly listed set signed the message, without revealing which member it was; unlike group signatures, no group manager, enrollment, or setup is required and the signer can assemble the ring ad hoc from public keys. This spontaneity and absence of a central authority is the defining contrast with managed group-signature systems.
Ring signatures hide the signer only relative to the listed ring and the signature transcript; they do not magically hide all external clues. If the ring is poorly chosen (e.g., includes implausible decoys) or observers have side information (timing, reuse patterns, output ages), practical anonymity can be much weaker than the nominal 1/r ideal.
Basic ring signatures do not let verifiers tell whether two different signatures came from the same secret key, but linkable variants (e.g., LSAG, MLSAG/CLSAG used in Monero) add a deterministic tag or key image so repeated use by the same secret can be detected without revealing identity; in Monero the key image is used to prevent double-spends while preserving anonymity.
Most practical ring-signature schemes and their linkable variants are proven secure in the random oracle model under standard hardness assumptions (e.g., discrete log or DDH), and some compact variants (CLSAG) rely on stronger or additional assumptions like k-OMDL for unforgeability; these are formal reductions, not assumption-free guarantees, so concrete security depends on the model and chosen primitives.
A key practical cost is that signature size and verification work grow roughly linearly with the ring size because the ring must be explicitly listed and processed; this is intrinsic to spontaneous/ad hoc rings and motivates compact constructions (CLSAG, Omniring, Triptych) that aim to reduce bandwidth and verification cost.
The verifier must be given or commit to the explicit list of public keys in the ring, so the signature proves membership in that stated set; there is no hidden global anonymity set - that requirement is why ring signatures necessarily include per-signature ring data and why their size grows with ring length.
In deployed privacy coins the cryptographic primitive is only part of the privacy story: Monero combines ring signatures (to hide which input is spent) with one-time stealth addresses (to hide receivers) and confidential-transaction proofs (to hide amounts), and empirical work has shown that poor decoy-selection or protocol choices can sharply weaken anonymity even when the signatures themselves are correct.
Implementations must watch subtle implementation pitfalls: for example Monero nodes must check that l * key_image != 0 to avoid cofactor/subgroup attacks (a check that was historically missing and later fixed), and concrete hashed-to-point or curve choices can affect the assumptions behind key-image and tag constructions.
Related reading