What is a Crypto Wallet?
Learn what a crypto wallet really is, how it manages keys and signatures, how seed phrases work, and why wallets are central to self-custody.
Introduction
A crypto wallet is the tool you use to control blockchain accounts. That sounds simple, but it hides the key idea that makes wallets click: in most blockchain systems, your assets are not stored inside the wallet application itself. They live on a shared ledger, and the wallet’s real job is to manage the secrets that let you prove control over them.
That is why crypto wallets feel both familiar and strange. They are familiar because they show balances, let you send assets, and help you sign in to apps. But they are strange because they are not bank accounts, and they are not just password managers either. A wallet sits at the boundary between human intent and cryptographic authorization. When you click “send,” the wallet does not move coins out of its own database. It uses a private key, or some more advanced signing rule, to authorize a state change that the network will verify.
This difference has consequences. It explains why a wallet can often be restored on a different device from a seed phrase. It explains why wallet providers often say they do not have custody of your funds. And it explains why losing a recovery phrase can be permanent: if no one else controls the signing authority, there may be no one to reverse the loss.
How does a crypto wallet decide who can authorize actions onchain?
A blockchain needs a way to answer a simple question: who is allowed to authorize this action? If anyone could claim anyone else’s funds, the system would be useless. So blockchains rely on cryptographic credentials. A user controls an account because they can produce a valid signature under the right key.
A wallet exists to make that usable.
At the cryptographic level, many systems start from a public/private key pair. The private key must remain secret; it is used to sign transactions or messages. The public key can be shared more freely and is used, directly or indirectly, to derive an address or verify signatures. Ethereum’s user-facing documentation puts this plainly: an account is a pair of keys, where the public side helps create the address you share and the private side signs things. A wallet is the tool that lets you interact with that account using those keys.
That description is accurate, but it helps to sharpen it. The wallet solves three linked problems at once.
First, it must store or mediate access to signing authority. Sometimes that means a raw private key stored in software. Sometimes it means a private key protected inside a hardware device. Sometimes it means a smart-contract account whose rules require multiple approvals, a guardian-based recovery flow, or other logic. The common thread is not the form factor; it is control over authorization.
Second, it must construct valid actions for a specific blockchain. A Bitcoin wallet has to assemble a transaction in Bitcoin’s model. An Ethereum wallet has to prepare Ethereum transactions or signing requests. A Cosmos wallet has to understand that ecosystem’s chains and message formats. The wallet is not just a vault; it is a translator between user intent and chain-specific rules.
Third, it must present this safely to a human being. Humans do not want to inspect byte arrays and signature payloads. They want to see “send 0.5 ETH to this address” or “connect this account to this app.” Wallet design is largely the art of turning dangerous cryptographic power into decisions a person can understand and review before signing.
If my crypto isn't stored 'in' the wallet, where is it and what does the wallet actually do?
| Model | Who controls | Recovery | Ease of use | Main risk | Best for |
|---|---|---|---|---|---|
| Custodial | Provider's keys | Provider-managed recovery | High (password flows) | Counterparty risk | Beginners, fiat onramps |
| Non-custodial | You control keys | Seed phrase backup required | Medium (learning curve) | Personal loss or theft | Self-custody, privacy |
| Hybrid | Shared or escrowed keys | Combined provider + user | High (convenient UX) | Shared trust assumptions | Onramps, regulated services |
The most common misunderstanding is the phrase “my crypto is in my wallet.” It is useful shorthand, but mechanically it is wrong.
What exists onchain is a record of ownership or control according to the protocol’s rules. The ledger says, in effect, that certain outputs, balances, or account state may be spent or modified if a valid authorization is provided. The wallet does not contain the coins the way a physical wallet contains cash. It contains, or brokers access to, the credentials needed to satisfy those rules.
The difference matters because it clarifies what recovery actually means. If you install a wallet app on a new phone and restore from your recovery phrase, the app has not pulled coins out of the old phone. It has regenerated the same controlling keys, scanned the blockchain for the addresses or accounts tied to them, and displayed the assets that were already there on the network.
It also clarifies why many wallet providers say they do not have custody. In the non-custodial model described by Ethereum’s documentation, the provider gives you a window into your assets and tools to manage them, but does not hold the funds for you. If the provider disappears, your assets may still be accessible from another compatible wallet, as long as you still control the recovery material.
That is a powerful property. It reduces dependence on a specific company. But it also shifts responsibility. In a typical self-custodial setup, there is no equivalent of “forgot password, click here.” If the secret that grants signing authority is lost or stolen, the system may have no native way to distinguish accident from legitimate control.
How does a crypto wallet create, sign, and submit transactions?
Here is the core mechanism.
A wallet starts from secret material that can generate or unlock signing keys. When you create a wallet, the software may generate a private key directly, or more commonly today, generate a seed from which many keys can be derived deterministically. The wallet then derives one or more addresses or accounts, queries the network for balances and activity associated with them, and shows you a usable interface.
When you want to act, the wallet prepares a message in the format required by the chain or application. That might be a transaction transferring assets, a signature request proving account ownership, or an approval authorizing a smart contract to spend tokens. The wallet then asks for confirmation, signs the payload using the relevant key material or account logic, and broadcasts the signed transaction or returns the signature to the requesting app.
The network does the final verification. Other participants do not trust your wallet because it is popular or well designed. They trust the mathematical validity of the signature and the protocol rules around it.
A concrete example makes this less abstract. Suppose you open a wallet and send tokens to a friend. The wallet first needs to know which account you are sending from, which chain you are on, and what exact asset and amount you intend to transfer. It then constructs the transaction data the target network expects. Before anything touches the network, the wallet presents this intent back to you in a human-readable form. When you approve, the wallet signs using the authority tied to your account. The signed transaction is then submitted to the network, where validators or nodes check that the signature is valid, the nonce or replay protection is correct, and the account has enough funds to pay what is required. Only then does the ledger update.
That same mechanism also explains wallet-based login. Many decentralized applications do not ask for a username and password. Instead, they ask the wallet to sign a message. If the signature verifies against your account, the app treats that as proof that you control the account. In other words, the wallet has become both a payment instrument and an identity instrument.
Why do wallets use seed phrases and how do they enable recovery?
Early wallets could manage isolated keys, but that created a practical problem. If every new address required a new backup, wallet use became brittle and error-prone. The important improvement was the move to deterministic wallets, especially hierarchical deterministic, or HD, wallets.
The core idea of BIP-32 is simple: start from a single seed and deterministically derive a tree of many keypairs. Because the derivation is deterministic, the same seed always regenerates the same tree. That means one backup can restore an entire wallet structure, including many receiving addresses and change addresses.
This is the reason seed phrases are so central to wallet UX. BIP-39 defines a mnemonic format that turns machine-generated entropy into a list of easy-to-record words, commonly 12 or 24. Those words are not the funds themselves. They are a human-friendly encoding of the entropy that can be converted back into a binary seed, which then feeds deterministic key derivation.
This design solved a real usability problem: how do you let ordinary people back up cryptographic secrets without asking them to write down raw hexadecimal strings? But it also introduced a dangerous simplification. Because the phrase is readable and portable, users may treat it too casually. In practice, that phrase is often the master backup for the wallet. If someone learns it, they may be able to reconstruct the wallet elsewhere. If you lose it and your device fails, recovery may be impossible.
That is why common guidance stresses writing the phrase down and not storing it casually on an internet-connected computer. The exact advice varies by wallet and threat model, but the underlying mechanism is stable: the recovery phrase is valuable because it can regenerate wallet control.
There are also nuances many users miss. An optional passphrase can be combined with a mnemonic to derive a different seed, so the same visible words plus a different passphrase can lead to a different wallet. This can add protection, but it also raises the chance of self-inflicted loss: forgetting the extra passphrase means restoring the wrong wallet, often one that looks valid but is empty.
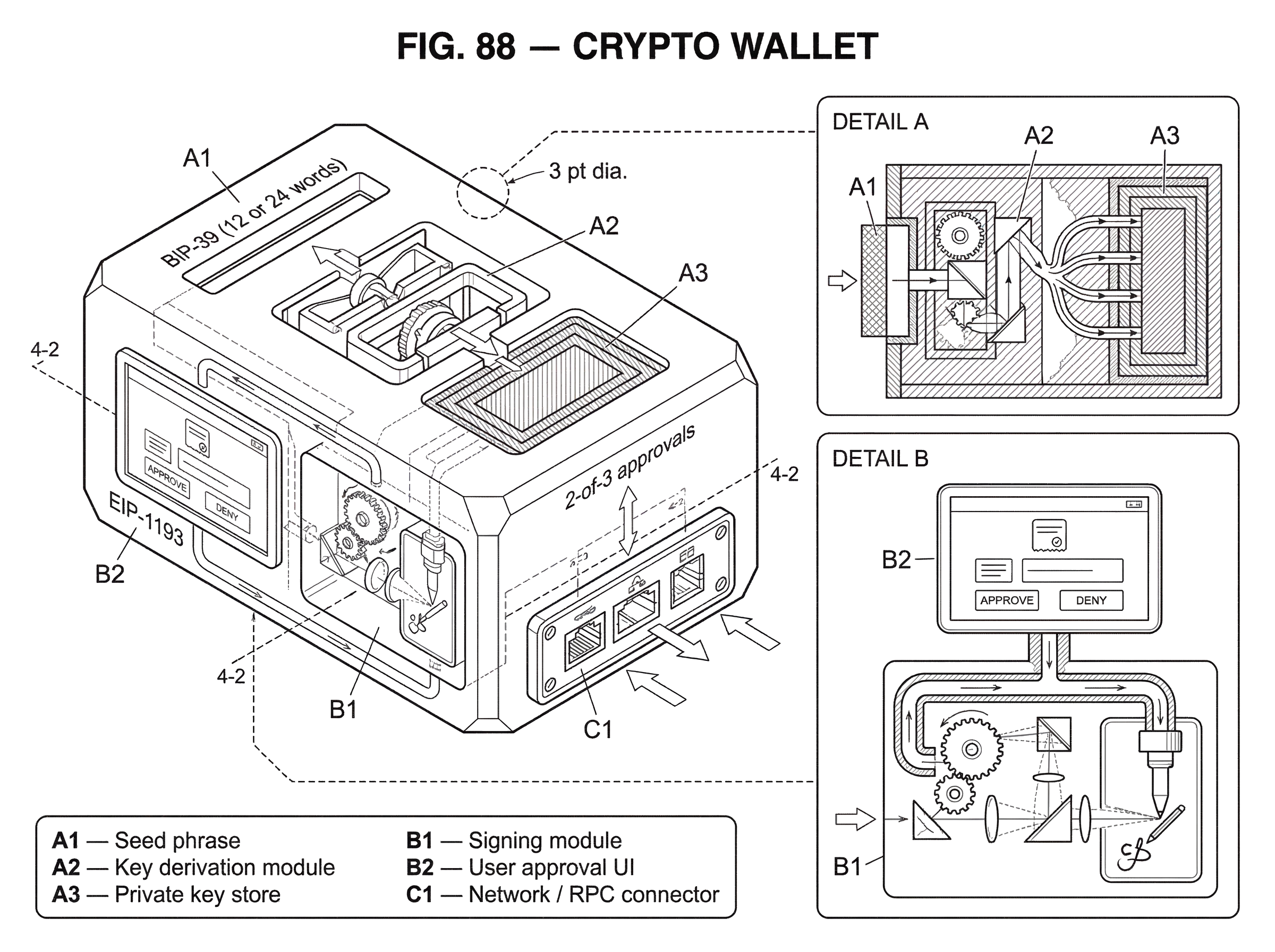
What components make up a crypto wallet (key management, signing, network, integrations)?
People speak of “the wallet” as if it were one layer. In practice, several layers are often involved.
There is the key-management layer, which stores or protects the authority used for signing. There is the signing layer, which produces approvals for transactions or messages. There is the network layer, which talks to nodes or RPC services to fetch balances and broadcast transactions. And there is the application integration layer, which lets websites or apps request actions from the wallet.
Ethereum’s provider standard, EIP-1193, makes this separation explicit. A provider is a JavaScript object exposed to an application so the app can request blockchain interactions. The provider is not itself responsible for private key management; wallet software sits behind it and handles account management and signing. This distinction matters because many users say “MetaMask signed this,” but from a systems perspective the web app requested an action through a provider interface, and the wallet mediated whether and how to sign.
This architecture is why browser-extension wallets became so important. They let a website ask for account access, request signatures, and respond to account or network changes without the website ever directly handling private keys. The wallet becomes a permissioned bridge between the app and the chain.
The same idea appears in mobile and QR-based connection flows. Sometimes the wallet is on your phone, while the app is on your laptop browser. A protocol such as WalletConnect can relay requests between them so the app can ask for a signature and the wallet can display the approval on the device that actually controls the account. The details vary, but the structure is the same: app requests, wallet reviews, wallet signs, network verifies.
Software vs. hardware vs. desktop wallets: what are the tradeoffs in security, convenience, and recoverability?
| Form | Connectivity | Security | Convenience | Recovery need | Best for |
|---|---|---|---|---|---|
| Mobile / Software | Online (phone/pc) | Exposed to malware | Very convenient | Seed or cloud backup | Everyday payments and dapps |
| Hardware | Air-gapped or USB | Isolated signing, strong | Less seamless | Seed backup essential | Large balances, long-term |
| Desktop / Full-node | Direct node connection | Reduced third-party trust | Less mobile | Local wallet + seed | Advanced users, sovereignty |
If the job were only to sign securely, everyone would use the same design. But wallets face a constant tension between security, convenience, and recoverability.
A software wallet on a phone or laptop is convenient because it is always available. It can connect to apps quickly, display QR codes, and support everyday use. But the same general-purpose device is exposed to malware, phishing, theft, and operating-system compromise. Convenience comes from being online and integrated, which is exactly what increases the attack surface.
A hardware wallet narrows that surface by keeping key operations in a dedicated device, usually offline except when approving a signing request. This is why such wallets are often recommended for larger balances. The goal is not magic immunity; it is to reduce the number of ways secret material can be exfiltrated from an everyday computing environment. The tradeoff is friction. Hardware devices are less seamless for quick mobile payments, and losing the device without a proper backup is still a disaster.
A desktop wallet can offer more control, especially when paired with a hardware wallet or even with full-node validation. Bitcoin.org notes that some wallets validate blocks and transactions locally as full nodes, which reduces trust in third parties because the wallet can verify the chain itself rather than depending entirely on someone else’s server. But that demands more storage, more bandwidth, and more technical effort.
This is the pattern behind wallet choice generally. Every increase in sovereignty tends to ask something in return: more setup, more backup responsibility, or more care in daily use.
How do smart wallets and account abstraction change who controls an account?
| Model | Control model | Fault tolerance | Complexity | Recovery options | Best use |
|---|---|---|---|---|---|
| Single-key | One private key | Single point failure | Low | Seed phrase | Personal wallets |
| Multisig | Multiple independent signers | High resilience | Medium | Distributed backups | Treasuries, DAOs |
| Smart-contract account | Onchain policy contract | Flexible (policy-based) | High | Contract-defined flows | Programmable UX, sponsored txs |
The simplest wallet model assumes a single private key directly controls an account. That is still common, but it is no longer the whole story.
On Ethereum and similar systems, smart wallets or smart accounts can move some of the wallet logic onchain. Instead of “a valid signature from this one key means yes,” control can be defined by a contract: perhaps 2-of-3 approvals are required, or a guardian can help recover access, or a spending limit applies, or a sponsor can pay gas for a user.
This is where wallets start to merge with account design itself. A product like Safe is not just a nicer interface for one secret key. It is an account architecture in which multiple owners and policy rules define authorization. That removes a single point of failure, which is why multisig wallets became foundational for treasuries, DAOs, and teams handling meaningful value.
Account abstraction pushes further. ERC-4337 introduces a model in which users can submit UserOperations for smart-contract accounts without changing Ethereum’s base consensus rules. The important point here is conceptual: the wallet no longer needs to be just a key holder for a fixed account type. It can become a programmable controller over richer authorization logic, fee payment rules, and recovery options.
This broadens what wallets are for. A wallet is still about authorizing actions, but the source of authority may be a single key, a threshold of keys, or a contract-defined policy system. The wallet interface remains the human-facing surface; the thing doing the authorizing may be much more sophisticated underneath.
What are the main user-facing security risks with wallets (phishing, backups, contract bugs)?
Cryptography is powerful, but most wallet failures do not come from someone breaking elliptic curve signatures from first principles. They come from compromised endpoints, deceptive interfaces, bad backup practices, or flawed wallet logic.
The most familiar risk is phishing. A wallet can only show you what it believes you are about to sign. If a malicious site tricks you into approving a dangerous transaction or signature, the wallet may faithfully execute your mistaken approval. The security boundary is not just “is the private key safe?” It is also “does the human understand what is being authorized?”
Another class of risk comes from the wallet implementation itself. The Parity multisig hack is a classic example from smart-contract wallet history. The problem was not that multisig as an idea was unsound. The problem was that the contract architecture exposed a re-initialization path through delegatecall to a library, allowing an attacker to make themselves the sole owner and drain funds. This is a useful reminder: a wallet is software, and software can be wrong. Moving from single-key wallets to smart wallets can improve resilience in some ways, but it also creates new implementation risk.
Backup design has its own failure modes. BIP-39 mnemonics make recovery easier, but also create a single secret that is easy to mishandle. Some systems therefore use secret sharing schemes such as SLIP-39, which split recovery material into multiple mnemonic shares so that only a threshold is needed for reconstruction. This can reduce single-point backup risk, but it adds operational complexity. The underlying tradeoff appears again: safer against one failure mode, more complex in day-to-day recovery planning.
Even seemingly advanced features can shift trust rather than remove it. Two-factor authentication in some wallet contexts may improve protection, but often relies on additional services or recovery channels. Full-node wallets reduce trust in third-party data providers, but not the need to secure your own device. Hardware wallets reduce key-extraction risk, but not the danger of confirming a malicious transaction you do not understand.
What do people use crypto wallets for today (payments, logins, multi‑chain management)?
Originally, many people thought of wallets mainly as storage plus payments. That is still part of the picture, but modern wallets do more.
They are used to receive and send assets, of course. They are used to connect to applications, whether for trading, lending, gaming, governance, or identity flows. They are used to sign messages that prove account ownership without spending funds. They are increasingly used as a control panel for multiple networks, where a single interface may support Ethereum-compatible chains, Bitcoin workflows, Cosmos ecosystems, or even non-EVM networks through different internal mechanisms.
This expansion explains why “wallet” can sometimes feel like an overloaded term. In one conversation it means “the seed phrase backup for my Bitcoin.” In another it means “the browser extension that lets me use DeFi apps.” In another it means “the multisig treasury account my organization uses.” These are not unrelated meanings. They are variants of the same core function: mediating control over digital accounts through cryptographic authorization.
What's fundamental about wallets versus implementation details and conventions?
The fundamental part of a wallet is not the app icon, the hardware shell, or even the recovery phrase format. The fundamental part is control over authorization.
If a system lets you prove that an action is approved by the right authority, and a wallet helps you manage and exercise that authority, you are in wallet territory. Public/private keys are the classic primitive. Deterministic derivation trees, mnemonics, browser providers, QR connection protocols, multisig policies, and smart-account standards are all ways of packaging that primitive for different needs.
What is more contingent is the surrounding convention. A 12-word mnemonic is a convention. xpub and xprv serialization in Bitcoin HD wallets is a convention tied to BIP-32. Exposing a provider to a web page is an application-integration convention. Even the idea that one wallet app should support many chains is a product choice, not a law of cryptography.
Keeping that distinction clear helps avoid confusion. When conventions change, the core idea remains: a wallet is the thing that turns your intent into valid, verifiable authorization on a blockchain system.
Conclusion
A crypto wallet is best understood as a key manager and signing interface, not a container for coins. It exists because blockchains need a way for users to prove control over accounts, and raw cryptography is too awkward and dangerous to use directly.
Everything else follows from that: seed phrases exist to back up deterministic key material, hardware wallets exist to isolate signing, browser wallets exist to connect apps to accounts, and smart wallets exist to make authorization programmable. If you remember one thing tomorrow, let it be this: your assets live on the chain, but your wallet is what lets you control them.
How do you secure your crypto setup before trading?
Secure your crypto setup by protecting your recovery material, hardening your devices, and verifying small test transfers before trading. Use Cube Exchange's non‑custodial MPC account model for trading while keeping your seed and device protections under your control.
- Back up your recovery material offline: write your mnemonic (or create SLIP‑39 shares) on a physical medium and store the copies in separate, secure locations.
- Harden the devices you use for signing: set a strong OS passcode, enable biometrics, and install the latest OS and wallet app updates.
- Fund your Cube account with a small test deposit (e.g., $10) and wait for the chain‑specific confirmation threshold or exchange credit to appear.
- Open the relevant Cube market or transfer flow, choose the order/transfer type (limit for price control, market for immediacy), enter amounts, and submit.
- For withdrawals or external transfers, verify the exact asset, network, and destination checksum before confirming the transaction.
Frequently Asked Questions
Restoring a wallet on a new device regenerates the same signing keys from your seed or recovery material and then scans the blockchain for addresses/accounts tied to those keys; the wallet is simply reproducing the authority that already controlled onchain assets rather than 'moving' coins between devices.
A seed phrase (BIP-39 mnemonic) is a human‑friendly encoding of the entropy that becomes a deterministic seed; that seed deterministically derives the private keys used to control accounts, so anyone who learns the phrase can reconstruct your keys, and losing it can make recovery impossible.
non‑custodial wallets give you the keys or the means to sign onchain and typically say they do not hold custody of funds, whereas custodial services (like many exchanges) hold users' assets and rely on account/password recovery processes - losing access in a non‑custodial setup generally cannot be undone by the provider.
Hardware wallets reduce key‑extraction risk by keeping signing operations inside a dedicated device and narrowing the attack surface, but they do not eliminate risks like approving a malicious transaction you don't understand, losing backup recovery material, or vulnerabilities in the surrounding software.
Smart wallets or smart‑account designs move authorization logic onchain (examples: multisig policies, guardian recovery, Safe, and the account‑abstraction ideas in EIP-4337), which enables richer features like gas sponsorship or threshold approvals but also introduces new implementation and contract‑level risks that can be exploited if the logic or libraries are flawed.
Web applications request blockchain actions through a provider interface (EIP-1193) exposed by the wallet; the provider lets the app ask for accounts or signatures while the wallet itself remains responsible for key management and whether to approve requests, keeping private keys out of the web app.
Alternatives to a single BIP‑39 mnemonic include secret‑sharing schemes such as SLIP-39, which split recovery material into multiple shares and require a threshold to reconstruct; this reduces single‑point backup risk but increases operational complexity and has its own compatibility and UX caveats.
Yes - a signed message can be abused: phishing sites or malicious dapps can trick you into signing approvals or messages that grant token allowances or consent to harmful actions, and wallets can only show what they parse and believe you are approving, so human mistakes remain a major risk.
Related reading