What Is a Settlement Layer?
Learn what a settlement layer is, how it secures rollups and modular chains, and why commitments, proofs, data availability, and withdrawals matter.
Introduction
Settlement layer is the part of a blockchain stack that turns a system’s claimed state into something other parties can safely rely on. That sounds abstract until you ask a practical question: if a rollup says you own 5 ETH, what makes that claim more than a local database entry? The answer is not simply that transactions were executed somewhere. The answer is that there is a place where commitments are posted, proofs or disputes can be resolved, and withdrawals can be enforced even if the off-chain or higher-layer system misbehaves.
This is why settlement matters. Scaling systems often move execution away from the most secure chain because computation is expensive to do everywhere, all the time. But moving execution away creates a new problem: where is truth ultimately checked, and where can users fall back if the fast layer fails? A settlement layer exists to answer that question.
The easiest misunderstanding is to treat settlement as just “the chain underneath.” Sometimes that is close enough for casual conversation, but mechanically it misses the point. A chain becomes a settlement layer not merely by existing below another system, but by performing a specific job: it must be able to host commitments, verify or adjudicate claims about state transitions, and support final outcomes such as withdrawals, bridge releases, or dispute resolution.
Why a settlement layer is required when execution moves off‑chain
| Layer | Main role | Finality meaning | Trust model | Cost profile | Best for |
|---|---|---|---|---|---|
| Execution layer | Compute transactions | Final inside layer | Layer's own consensus | Low per-tx cost | Fast execution, cheap UX |
| Settlement layer | Enforce accepted claims | Final for withdrawals | Base-layer consensus or proofs | Higher per-claim cost | Security and recoverability |
Here is the basic structure. An execution layer processes transactions, updates balances, runs smart contracts, and produces a new state. A settlement layer does not need to redo all of that work in the normal case. Instead, it needs enough information and enough rules to answer a narrower question: should this new state be accepted for consequences outside the execution layer?
That distinction is the compression point for the topic. Settlement is not primarily about computing every step; it is about making results enforceable. If an L2 executes a thousand trades, the settlement layer usually does not care about each trade as an isolated event. It cares about the commitment to the resulting state, whether the required data is available, whether a proof or challenge process says the state is valid, and whether users can turn that accepted state into actions such as withdrawing assets.
An ordinary analogy is a court recognizing a contract. The parties may negotiate privately, exchange drafts, and behave as if the deal is real long before any court gets involved. But the thing that makes the agreement robust against cheating is the existence of a forum that can enforce it if needed. This analogy helps explain why settlement exists: most activity should happen outside the expensive enforcement venue, but the enforcement venue must be credible. The analogy fails because blockchains do not rely on human interpretation in the same way courts do; they rely on predefined verification rules, signatures, proofs, and on-chain procedures.
This is also why many scaling designs are modular. If a base layer can do consensus, data availability, and adjudication well, then many execution layers can share that security instead of each rebuilding it from scratch. In a rollup-centric view, the base layer increasingly specializes in being a high-security settlement and data-availability layer, while most application execution happens elsewhere.
What are the core responsibilities of a settlement layer?
A settlement layer earns the name by maintaining a small set of crucial invariants.
The first invariant is durable commitment. An execution system must be able to post some compact representation of its claimed state or transaction batch onto the settlement layer. Depending on the design, that may be a state root, an output root, a candidate receipt, or some other commitment. The exact format is a convention. The fundamental point is that the settlement layer records a claim in a form that later proofs, challenges, or withdrawals can refer to.
The second invariant is verifiability. A commitment alone is not enough. The settlement layer must provide a rule for deciding whether that commitment should be accepted. In optimistic systems, this rule may be: accept the claim unless successfully challenged within a dispute window. In validity-proof systems, it may be: accept the claim immediately if accompanied by a valid cryptographic proof. In attestation-based systems, it may be: accept the claim if a threshold of designated parties signs off. These mechanisms differ sharply in trust and latency, but they all serve the same purpose: converting a claimed state into an accepted one.
The third invariant is recoverability for users. A legitimate higher-layer system must let users unilaterally withdraw or otherwise recover assets even if operators censor, disappear, or try to cheat. This property is more than a convenience. It is what prevents the higher layer from collapsing into a custodial system with a blockchain-shaped interface. If users cannot force an exit using the settlement layer’s rules, then the settlement layer is not really settling their claims.
The fourth invariant is availability of the data needed for verification. A system can post a state root cheaply, but if nobody can obtain the underlying transaction data or witness data, then fraud proofs, state reconstruction, and independent verification may become impossible. This is why modern settlement discussions are inseparable from data availability. In many designs, the hardest scaling problem is not computing transitions but ensuring that the data needed to check them is actually published and retrievable.
How are withdrawals from a rollup enforced on the settlement layer?
| Design | Acceptance timing | Proof required | Data availability | User action | Primary trade-off |
|---|---|---|---|---|---|
| Optimistic | Delayed (challenge window) | No upfront proof | Must publish batch data | Wait or submit challenge | Lower normal cost, slower exits |
| Validity-proof | Immediate on verification | Cryptographic proof with batch | Proof + data published | Submit proof once | Faster exits, higher prover cost |
Suppose you bridge ETH from Ethereum into a rollup and then make a series of trades on that rollup. Inside the rollup, your balance changes quickly because the rollup’s execution engine processes transactions much more cheaply than Ethereum itself. So far, however, the part that matters for settlement is not your local wallet view but what the rollup has committed to Ethereum.
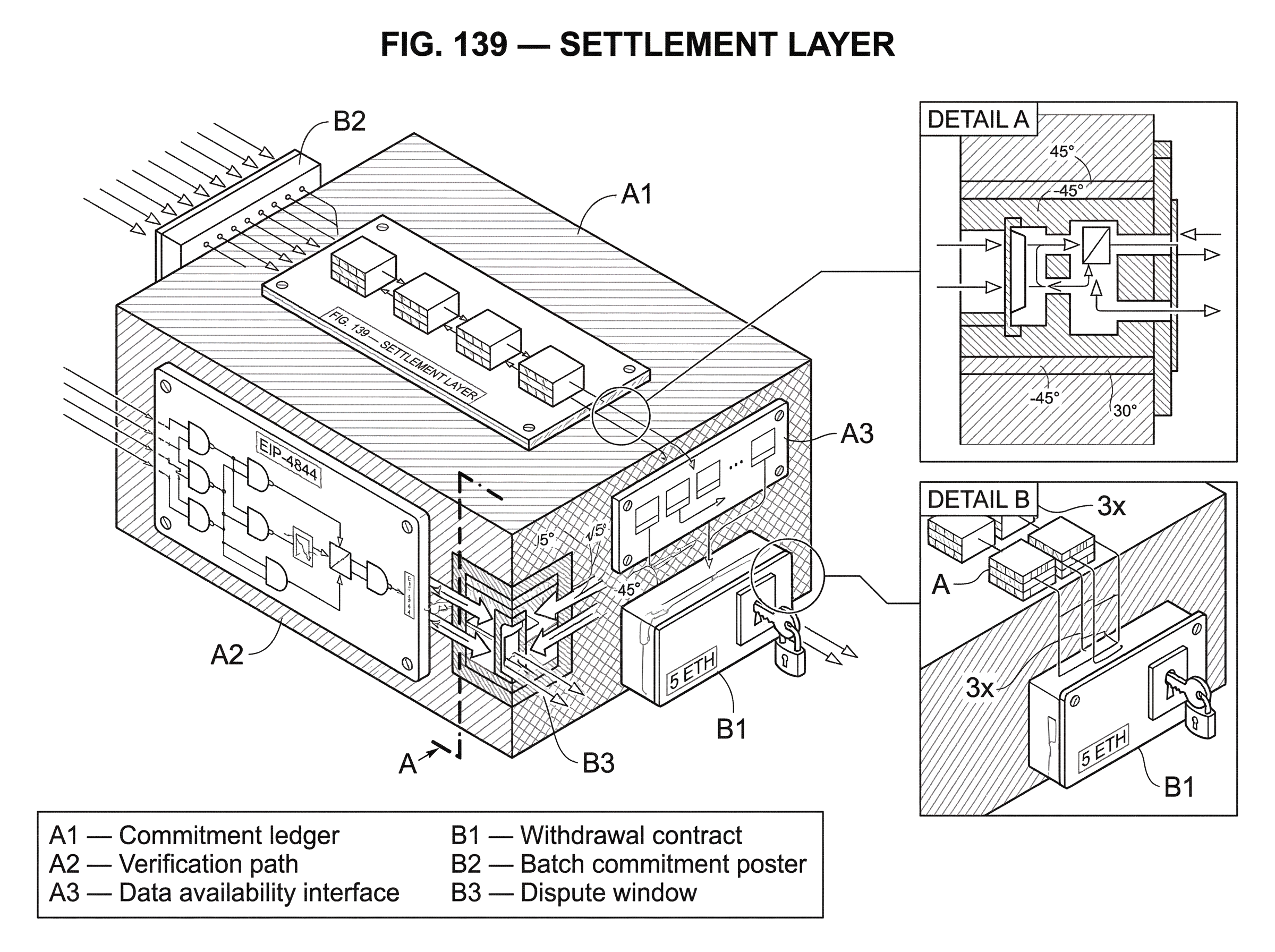
At some interval, the rollup posts a batch commitment to Ethereum. In an optimistic design, this might be a proposed output root representing the rollup’s latest state. In a validity-proof design, it might be a state commitment plus a proof that the transition was computed correctly. If the rollup also relies on Ethereum for data availability, it must publish the necessary batch data there as well. Historically that data might go into calldata; with Ethereum’s blob transactions from EIP-4844, rollups can instead put bulk data into blobs, which are cheaper data containers whose contents are not directly readable by the EVM but whose commitments are available on-chain.
Now you decide to withdraw back to Ethereum. The settlement layer contract does not simply trust your word that the rollup owes you ETH. Instead, it checks whether your withdrawal is consistent with an accepted rollup commitment. In a validity-proof design, acceptance may happen immediately once the proof verifies. In an optimistic design, acceptance may come only after a challenge period passes without a successful dispute. Once the claim is accepted under the settlement layer’s rules, the withdrawal contract releases funds.
Notice what happened. Ethereum did not replay every rollup transaction just to honor your withdrawal. It enforced a narrower claim: that a particular committed rollup state was valid enough, under its chosen verification mechanism, to serve as the basis for moving assets. That is settlement in action.
This also shows why finality can have two meanings that readers often conflate. A transaction may be final inside the execution layer once its data is published and the execution layer considers it immutable. But another chain or contract may still refuse to act on that result until the settlement mechanism has finished its own acceptance process. Optimism’s documentation makes this distinction explicit: data-availability finality on the execution side does not necessarily mean the settlement layer has accepted the resulting state for withdrawals yet.
What are the three components of settlement: commitments, verification, and data availability?
| Component | Purpose | Typical primitive | Main threat | Handled by |
|---|---|---|---|---|
| Commitment path | Anchor execution claims | State root / output root | Missing or ambiguous anchor | Execution → settlement poster |
| Verification path | Decide acceptance | Fraud proofs / ZK proofs / attestations | Wrong acceptance or delay | Settlement adjudicates |
| Data availability | Allow independent checks | Calldata / blobs / DA layer | Unavailable witness data | Consensus / DA provider |
Most settlement systems can be understood through three interacting components.
The first component is the commitment path. Some piece of data representing the execution layer’s claim must be posted where others can reference it. On Ethereum rollups this is often a state root or output root. In Polkadot, parachains do not place full proof-of-validity data directly into the relay chain block; they place a compact candidate receipt containing hashes and roots that commit to the relevant data. In Tendermint-based systems, block headers embed Merkle-root commitments to block contents, validator information, and application results. Different ecosystems choose different commitment objects, but the logic is the same: the settlement layer stores a compact anchor, not the whole world.
The second component is the verification path. A commitment must become actionable through some acceptance rule. There are two broad cryptographic styles here, with a third, weaker style sometimes used in practice.
In optimistic settlement, the system assumes the posted state is correct unless challenged. This is attractive because normal-case costs are low: no expensive proof is needed every time. But the system pays for that efficiency with a delay, because there must be time for challengers to inspect the data and contest invalid claims. Modern optimistic systems increasingly aim for permissionless fault proofs rather than privileged proposers or multisig challengers, because the whole point of settlement is weakened if only a special actor can trigger enforcement. Optimism’s fault-proof upgrade reflects exactly this direction: reduce trust in a privileged proposer, allow permissionless output proposals and disputes, yet still keep emergency guardian controls as a fallback while the mechanism matures.
In validity-proof settlement, the claim arrives with a proof that the state transition is correct. If the proof verifies, the settlement layer can accept the new state immediately and unconditionally under the cryptographic assumptions of the proof system. This removes the challenge window but introduces heavy prover costs. The key tradeoff is not mysterious: optimistic systems shift work into a rare dispute path; validity systems front-load work into every batch.
In attestation-based settlement, acceptance depends on signatures or attestations from a designated set of actors. This can be operationally simpler, but it introduces an explicit trust assumption that those actors are honest above some threshold. It may be a useful transitional design, but it is different in kind from cryptographic validity or fully permissionless fraud-proof settlement.
The third component is data availability, and this is where many settlement designs succeed or fail. If a system posts a commitment without making the underlying data available, verifiers may not be able to reconstruct state, challenge fraud, or prove withdrawals. Ethereum’s EIP-4844 is a concrete example of a settlement-layer upgrade motivated by this problem. It introduces blob-carrying transactions so rollups can post larger amounts of data more cheaply than calldata. The execution layer only sees commitments, while the consensus layer is responsible for persisting blob data, propagated separately as sidecars. That design makes sense once you see the goal: the base layer is being optimized to serve rollups that need affordable, widely available batch data for settlement.
Why do settlement layers prioritize data availability over on‑chain computation?
A recurring surprise in scaling is that the base layer’s bottleneck is often not “smart contract logic” in the usual sense. If execution moves to rollups, the base layer no longer needs to do every application computation itself. What it must do is provide a secure place to order commitments, verify proofs or disputes, and publish enough data that others can independently check the system.
That is why the rollup-centric roadmap argued that base-layer scaling should focus primarily on how much data blocks can hold, rather than on maximizing on-chain computation. Rollup throughput is constrained by how much settlement-layer data they can publish and how affordably they can publish it. EIP-4844 directly follows this logic: it is a stop-gap that improves data availability economics for rollups before fuller sharded designs arrive.
This is also why external data-availability layers matter. Celestia explicitly separates data availability from execution and settlement. In that model, the DA layer orders blobs and keeps them available, while settlement lives above it and uses that published data to verify proofs, resolve disputes, and bridge assets. Data Availability Sampling lets light nodes obtain a probabilistic guarantee that block data is available without downloading the whole block. Namespaced Merkle Trees let an application fetch and prove only its own relevant data. The point is not that settlement disappears. The point is that settlement can be modular too, relying on one layer for availability and another for adjudication.
Blobstream extends this modular pattern further by relaying Celestia data-root commitments to Ethereum with an on-chain light client. That lets an Ethereum-settled rollup use Celestia for bulk data availability while still settling fraud or validity proofs on Ethereum. Mechanically, this decouples two jobs that are often bundled together: where data lives and where disputes are finally resolved.
How do non‑Ethereum systems implement settlement (Polkadot, Tendermint, Celestia)?
The term “settlement layer” is common in rollup discussions, but the underlying idea is not Ethereum-specific.
Polkadot’s relay chain plays a settlement-like role for parachains. Parachain blocks are not simply trusted because a collator produced them. Instead, compact candidate receipts are included on the relay chain, availability is supported through erasure coding, and validity is checked through an approval process in which validators may re-acquire the proof-of-validity data and re-run checks. Finality then comes from GRANDPA once the relay chain finalizes the block. The interesting detail here is that availability does not imply validity. A candidate may be available yet still pending approval. That separation is exactly the kind of thing a settlement perspective makes visible: posting a commitment and making data retrievable are necessary, but not by themselves sufficient, for accepted state.
Tendermint offers another useful contrast. Its core role is BFT consensus with commits from more than two-thirds of validator weight. Block headers include commitments to block contents, validator sets, and application results, supporting efficient verification by light clients. This gives you a strong finality substrate. But by itself it does not define a rollup settlement flow; that must be built on top. This is a good example of the boundary between consensus layer and settlement layer. Consensus answers who agreed on block order and finality. Settlement adds the machinery for external execution layers to post claims, prove them, dispute them, and turn them into outcomes like withdrawals.
What failure modes and limits should you watch for in settlement assumptions?
Settlement layers are powerful, but they are not magic. Their guarantees depend on what exactly is being settled and on which assumptions support the mechanism.
If a system relies on a trusted attestation set, the failure mode is obvious: if that threshold colludes or is compromised, the settlement decision can be wrong. If a system relies on optimistic fraud proofs, then users depend on data being available and on at least one honest party being able and willing to challenge in time. If a system relies on validity proofs, then users depend on the soundness of the proving system and the correctness of the verifier implementation. None of these are “just engineering details”; they define what the security claim really means.
Data availability is an especially sharp edge. A commitment without data can create the illusion of security while preventing independent verification. This is why DAC-based systems, where a small committee promises data availability, have meaningfully different trust assumptions from systems that post data on a broadly verified base layer or use a robust sampling-based DA network.
There are also economic failure modes. Settlement is not only cryptographic; it is priced. Rollups must pay for L1 data availability, L1 gas for settlement or proof verification, and their own L2 execution resources. Research on rollup fee mis-pricing shows that if these resources are charged badly, attackers can exploit the gap. For example, saturating DA batch capacity with data-heavy transactions can cause denial-of-service and finality delays, while prover-killer transactions can stall proof generation. The lesson is simple: if the settlement path is a scarce resource, the fee mechanism is part of the security model.
Operational fallback matters too. Permissionless settlement mechanisms are a goal, but production systems often retain emergency powers while they harden. Optimism’s fault-proof upgrade, for example, reduces trust assumptions yet still preserves a Guardian role that can pause withdrawals or disable the fault-proof system in emergencies. That is not a contradiction so much as a reminder that “trustless” is often an aspiration approached in stages.
Finally, some failure modes are about liveness rather than correctness. If an operator stops posting state roots or batch data, users may be unable to access assets even if no invalid state was ever accepted. That is why escape-hatch designs matter. The whole point of unilateral withdrawal is to give users a path that does not depend on continued operator cooperation.
Which settlement properties are fundamental and which are design choices?
The fundamental part of a settlement layer is not Ethereum, not rollups, not blobs, and not any particular proof system. The fundamental part is this: there must be a place where state claims become enforceable under shared verification rules.
Several things often treated as essential are really design choices. Whether commitments are state roots, output roots, candidate receipts, or header Merkle roots is a design choice. Whether verification is optimistic, validity-based, or attestation-based is a design choice. Whether data availability is provided by the same chain as settlement or by a modular DA layer is a design choice. Whether finality is near-instant BFT finality or slower economic finality is a design choice.
What cannot be designed away is the need for credible adjudication and user recovery. If no layer can verify the relevant claim, resolve disputes, and let users force an outcome, then the system may be fast, but it is not properly settled.
Conclusion
A settlement layer is the layer that makes higher-layer blockchain activity count. It records commitments, ensures the needed data is available, applies a rule for accepting or rejecting claimed state, and gives users a way to cash out those accepted claims even if operators fail.
If you remember one thing tomorrow, remember this: execution is where transactions happen, but settlement is where their consequences become enforceable. That is why settlement layers sit at the center of modern scaling design.
How does this part of the crypto stack affect real-world usage?
The settlement layer determines how and when off‑chain activity becomes enforceable onchain; which directly affects withdrawal delays, who you must trust, and what data you need to keep to prove claims. Before you fund, trade, or move assets that depend on a particular settlement design, run a short checklist and then complete the action on Cube Exchange once you understand the risks and timing.
- Look up the project’s settlement verification model (optimistic, validity proof, or attestation) and note the challenge window length or proof verification requirements.
- Confirm how the system publishes batch data (L1 calldata, EIP‑4844 blobs, or external DA) and whether you can fetch the witness data needed for a fraud/withdrawal proof.
- Read the withdrawal/escape‑hatch procedure and record the estimated wait time and any required evidence (for example: a 7‑day dispute window for optimistic exits, or an immediate on‑chain SNARK verification for validity exits).
- Check fee drivers: expected L1 gas and DA costs for posting batches or submitting proofs, and whether heavy DA usage can delay finality.
- Fund your Cube Exchange account, then place trades or withdrawals on Cube. Use a limit order for price control or a market order for immediate execution, and review the estimated fees and expected withdrawal timing before submitting.
Frequently Asked Questions
A chain only functions as a settlement layer if it does more than sit underneath another system: it must record durable commitments, provide rules and mechanisms to verify or adjudicate those commitments, and enable final outcomes like withdrawals or bridge releases so users can recover assets when the execution layer fails.
Because verifiers need access to the transaction/witness data required to check or reconstruct state, rollup throughput is often limited more by how much settlement-layer data can be published affordably than by on-chain computation; EIP-4844 (blobs) is an example of an L1 upgrade driven by this data-availability bottleneck.
Optimistic settlement minimizes normal-case cost but requires a challenge window and permissionless challengers (trading latency for efficiency); validity‑proof settlement accepts batches immediately if a cryptographic proof verifies but incurs heavy prover costs; attestation‑based settlement is operationally simpler but introduces an explicit trust assumption in the designated signers' honesty.
A proper settlement layer must let users unilaterally withdraw by proving their claim against an accepted commitment; escape‑hatch designs (and resolver contracts) are proposed to locate and allow withdrawal of user assets if operators stop posting or censor state.
No - posting a commitment or making data available does not by itself guarantee the committed state is valid; systems like Polkadot explicitly separate availability from validity so a candidate can be available yet still pending approval.
Yes - settlement and data availability can be modular: Celestia separates DA from execution/settlement, and projects like Blobstream relay DA commitments (Celestia roots) to Ethereum so a rollup can use one layer for bulk DA and another for final dispute resolution on Ethereum.
Common failure modes include collusion or compromise of an attestation set, unavailable data that prevents fraud proofs or reconstruction, bugs or unsoundness in proof verifiers, economic attacks that saturate scarce DA/prover resources, and liveness losses when operators stop posting commitments.
Settlement is a priced resource: rollups must pay for L1 data availability, gas for posting/verification, and prover work, and if fee mechanisms misprice those resources attackers can congest DA capacity or otherwise induce denial‑of‑service and finality delays.
The article identifies four core invariants: durable commitment (compact on‑chain anchors), verifiability (rules for acceptance such as fraud proofs or cryptographic proofs), recoverability (unilateral exits or escape hatches for users), and data availability (publishable, retrievable data needed for verification).
EIP‑4844 blobs are not directly readable by the EVM; only commitments to blob contents are available on‑chain and the full blob contents are carried as sidecars off‑chain, which changes how rollups publish large batch data for settlement.
Related reading