What is Zcash?
Learn what Zcash is, how shielded transactions use zk-SNARKs, and why private blockchain payments require more than simple encryption.
Introduction
For the token explainer, see ZEC.
Zcash is a blockchain network and cryptocurrency designed to make digital payments verifiable without requiring every detail of the payment to be public. That sounds almost contradictory, because blockchains are usually praised for transparency: every node can check the ledger because the ledger is visible. Zcash matters because it asks a deeper question. If the real job of a ledger is to prevent counterfeiting and double-spending, why should that also require publishing the sender, receiver, and amount to the world?
That question is the center of the protocol. Zcash keeps the usual blockchain requirement that independent nodes must be able to verify the money supply and reject invalid spends, but it changes what must be revealed for that verification to happen. Instead of exposing all transaction details, it uses zero-knowledge proofs to show that a transaction is valid while keeping key details hidden. This is why Zcash is often described by its own materials as privacy-protecting digital cash or “HTTPS for money.”
At a high level, Zcash is descended from Bitcoin’s design and code lineage, but it extends that model with a shielded system based on the Zerocash research. The result is not a completely separate idea from Bitcoin so much as a different answer to a Bitcoin-shaped problem. Bitcoin says public visibility is the price of decentralized verification. Zcash says much of that visibility is a design choice, not a law of nature.
Why does Zcash hide transaction details while still letting the network verify payments?
A normal public blockchain makes verification easy by making transactions legible. If Alice sends Bob coins, the network can inspect the inputs, outputs, and amounts, confirm that the inputs exist and are unspent, and confirm that the totals balance. This works well for integrity, but it creates a permanent public record of financial relationships. Even when addresses are pseudonymous, patterns of use, exchange interactions, withdrawals, repeated amounts, and network metadata can make those pseudonyms fragile.
Zcash starts from the observation that money has two separate jobs. One job is accounting correctness: no one should create money from nothing or spend the same asset twice. The other is transactional privacy: ordinary payments should not automatically become public intelligence feeds. Many systems solve the first job and neglect the second. Zcash tries to solve both at once.
The important conceptual move is this: the network does not need to know which hidden coin you spent in order to know that you spent some valid, unspent coin and that the transaction preserves value. Once that becomes believable, the rest of the system clicks into place. Zcash is built around cryptographic objects that let the chain remember hidden value commitments, plus proofs that let a spender show they are authorized and honest without revealing the note they spent.
This is also why Zcash should not be thought of as “encrypted Bitcoin.” The chain is not simply hiding Bitcoin-style UTXO data under a layer of encryption. It uses a different mechanism for proving validity. The privacy is not an afterthought attached to the ledger; it changes how the ledger represents and verifies ownership.
What’s the difference between Zcash transparent coins and shielded notes?
| Type | On-chain record | How spending checked | Privacy | Best choice |
|---|---|---|---|---|
| Transparent coins | Explicit inputs and outputs | Visible input verification | Low | Public payments, exchanges |
| Shielded notes | Note commitments and nullifiers | zk-SNARK proof plus nullifier | High | Private payments, selective disclosure |
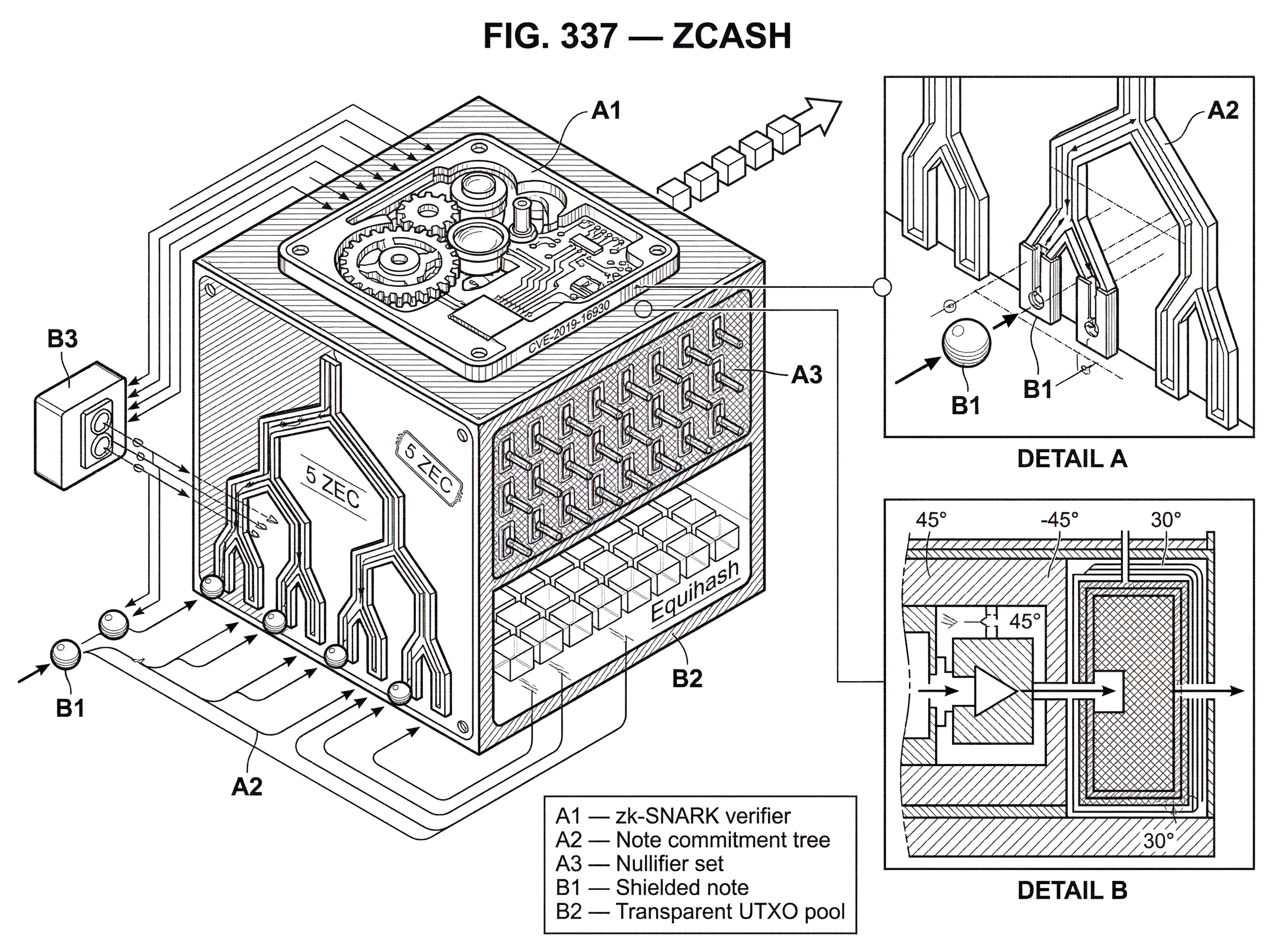
Zcash has historically supported two kinds of value on the same chain. There is a transparent pool, which works in a Bitcoin-like way, and a shielded pool, which works through hidden notes and zero-knowledge proofs. The protocol specification describes Zcash as bridging Bitcoin’s transparent payment scheme with a shielded payment scheme secured by zk-SNARKs.
Transparent funds behave much like they do in Bitcoin. Their movement is publicly visible, and the chain verifies them by checking explicit inputs and outputs. Shielded funds are different. In the shielded system, the spendable object is a note. A note represents value spendable by whoever controls the corresponding shielded spending key, but the note’s contents are not publicly revealed on-chain.
What is revealed publicly is a note commitment. A commitment is a cryptographic way to publish a locked form of data that binds you to that data without showing it. When a shielded note is created, the transaction publishes its commitment, and that commitment is appended to a note-commitment Merkle tree for the relevant shielded protocol. The chain therefore gains a public record that some well-formed note exists, while the note’s recipient and amount remain hidden.
When that note is later spent, the spender does not reveal the note itself. Instead, the transaction reveals a nullifier, a value unique to that note. The nullifier is what prevents double-spending. Nodes maintain a set of nullifiers that have already appeared. If a nullifier shows up twice, the second spend is invalid. The clever part is that the nullifier lets the network recognize repeated spending attempts without learning which commitment in the tree the nullifier came from.
That pair (commitments when value is created, nullifiers when value is spent) is the core accounting structure. It is the invariant that matters most. The network must be able to say, “This spend corresponds to a valid committed note that has not been spent before,” but it need not learn which note that was.
How do zk-SNARKs let Zcash verify transactions without revealing amounts or parties?
The hardest part of Zcash is not hiding data. Encryption alone can hide data. The hard part is letting the whole network verify hidden transactions anyway. That is where zk-SNARKs enter.
A zk-SNARK is a zero-knowledge proof system that lets someone prove a statement is true without revealing the private information that makes it true. In Zcash, the statement is roughly: I know shielded inputs that exist in the note-commitment tree, I am authorized to spend them, the corresponding nullifiers are correctly derived, the output notes are well formed, and value is conserved. If the proof verifies, nodes can accept the transaction without seeing the secret witness behind it.
This is the compression point for understanding Zcash: the chain stops asking for transaction details and starts asking for a proof of transaction correctness. Public blockchains usually verify by inspection. Zcash verifies by proof.
That sounds abstract, so consider a worked example in prose. Imagine a user holds a shielded note worth 5 ZEC. The chain does not publicly show that note sitting at a visible address with a visible balance. Instead, the chain contains a commitment to that note somewhere in its Merkle tree. The user now wants to pay 2 ZEC to someone else and keep 3 ZEC as change, all inside the shielded pool. Their wallet constructs a transaction that creates two new hidden notes (one for the recipient, one for change) and derives the nullifier for the old 5 ZEC note. Then it generates a zk-SNARK proving that the old note really exists in the tree, that the spender knows the spending key authorizing it, that the nullifier is correctly computed from that note, and that the values balance: 5 in, 2 plus 3 out, minus any fee. The chain sees the proof, the new note commitments, and the nullifier. It does not see the sender, recipient, or amounts inside the shielded transfer.
The proof does not replace all public checks. In Sapling and Orchard, the protocol also uses value commitments and binding signatures so the network can enforce balance across shielded and transparent components without exposing the hidden amounts. The exact math is specialized, but the intuitive point is straightforward: the protocol commits to values in a form that can be checked algebraically, and the binding mechanism prevents an attacker from mixing and matching commitments to fake conservation of value.
If this sounds more complex than Bitcoin, it is. Zcash is not trying to get privacy for free. It is deliberately trading protocol simplicity for stronger confidentiality.
Why does Zcash use Sprout, Sapling, and Orchard instead of a single shielded system?
| Protocol | Prover cost | Wallet support | Core primitive | Best for |
|---|---|---|---|---|
| Sprout | High | Limited | JoinSplit descriptions | Historical / legacy compatibility |
| Sapling | Lower | Broad | Spend and Output | Mobile-friendly shielded use |
| Orchard | Efficient | Modern | Action descriptions | Future-proof privacy |
If you read the specification, you will encounter several shielded protocols: Sprout, Sapling, and Orchard. These are not separate chains. They are successive shielded designs introduced through network upgrades.
The reason for this evolution is practical. The original Zerocash ideas were powerful, but early proving systems were heavy for real-world wallets. If shielded transactions are too slow, too memory-intensive, or too awkward for mobile devices, then the protocol may offer strong theoretical privacy while seeing weak practical use. That is not a cosmetic problem. In privacy systems, low adoption weakens the anonymity set.
Sprout was the original shielded system. Sapling improved efficiency and usability substantially, including better support for viewing keys and more practical wallet behavior. Orchard continued that evolution in later upgrades. The protocol specification is careful to distinguish the transaction structures for each generation: Sprout uses JoinSplit descriptions, Sapling uses Spend and Output descriptions, and Orchard uses Action descriptions.
The deeper lesson is that privacy systems are not only about cryptography in the abstract. They are also about whether ordinary devices can generate proofs, whether wallets can scan for relevant incoming notes efficiently, and whether the resulting user experience is good enough that people will actually choose the private path.
How do viewing keys and diversified addresses affect Zcash privacy and disclosure?
A common misunderstanding is to imagine that a shielded system must make information inaccessible to everyone except the spender and recipient. Zcash is more flexible than that.
From Sapling onward, Zcash supports viewing keys. A full viewing key can let someone recognize relevant incoming and outgoing notes without granting spending authority. There are also incoming viewing capabilities for narrower cases. This matters because privacy in real finance is rarely the same thing as secrecy from absolutely everyone. People may need to share transaction visibility with accountants, compliance teams, auditors, family offices, or personal record systems while still not exposing the same information to the public internet.
Zcash also supports diversified addresses, which let one spending authority control many unlinkable payment addresses. This solves a familiar privacy problem. If you reuse one static public identifier for every payment, you leak relationship data. Diversification lets a wallet hand out distinct receiver addresses without creating a new underlying spending authority each time.
So the shielded model is not “nobody can ever see anything.” It is closer to selective disclosure layered on top of public consensus. The network verifies correctness globally, while the user chooses who else, if anyone, gets additional visibility.
What is Zcash's trusted setup and why does it matter for security?
| Approach | Trust model | Main risk | Practicality | When to choose |
|---|---|---|---|---|
| Single trusted setup | Single-party trust | Parameter compromise | Simple to run | Early-stage systems |
| MPC ceremony | Distributed contributions | Collusion if all dishonest | Operationally complex | Reduced single-point trust |
| Transparent proofs | No trusted setup | Larger proofs or slower | Increasingly practical | When trust unacceptable |
Zcash’s privacy mechanism has long been entangled with an important trust question: parameter generation for the zk-SNARK system. The original Zerocash construction required a one-time trusted setup. The research paper is explicit about the consequence: soundness depends on the setup, even though anonymity can remain intact even if the setup is corrupted.
This distinction matters. If setup soundness failed in the worst way, an attacker might be able to create valid-looking proofs for invalid transactions, potentially violating the balance guarantees of the system. That is a very different failure mode from a privacy leak. It is about counterfeit resistance, not confidentiality.
To reduce this trust, Zcash used multi-party computation ceremonies so that no single participant needed to be trusted absolutely. The idea is simple: if many participants contribute randomness, and at least one contribution is honestly destroyed after use, then the toxic secret material needed to subvert the setup does not exist in recoverable form. The public artifacts around the Sapling MPC and Powers of Tau attestations were created to let participants and observers verify that contributions were included.
This is a good place to distinguish analogy from reality. The setup ceremony is sometimes compared to many people each adding entropy into a shared vault and then destroying their own copy of the key material. That analogy helps explain why “one honest participant is enough.” But it fails in one respect: what matters is not merely adding randomness; it is adding it within a formally structured computation whose output becomes the public proving parameters.
More broadly, multi-party computation is not unique to Zcash. It is a general technique for avoiding concentration of cryptographic power. In threshold signing, for example, a system can split control over a signing key so that no complete private key exists in one place. **Cube Exchange uses a 2-of-3 threshold signature scheme for decentralized settlement: the user, Cube Exchange, and an independent Guardian Network each hold one key share, no full private key is ever assembled in one place, and any two shares are required to authorize a settlement. ** That is a different application from Zcash’s setup ceremonies, but it illustrates the same design instinct: move trust from one all-powerful secret toward a distributed process.
Still, trusted setup has always been one of the main conceptual costs of early Zcash-style SNARK systems. It is not fatal, but it is not trivial either.
How does optional shielded usage affect real-world anonymity on Zcash?
Zcash’s cryptography can provide very strong privacy for fully shielded transactions. But that phrase matters. The protocol specification itself warns that privacy guarantees are for fully shielded usage; partially shielded activity can permit probabilistic linkage through the metadata that remains visible.
This is where many readers make the wrong inference. If a protocol has excellent privacy technology, they assume the network as a whole therefore has excellent observed privacy. That does not automatically follow. Privacy systems are collective systems. Your anonymity depends partly on what other users do, how wallets behave, which transaction types exchanges support, and whether funds repeatedly move between private and public states in recognizable ways.
Empirical studies of deployed Zcash usage found that much activity historically remained transparent, and that simple heuristics could often link deposits into and withdrawals out of the shielded pool when users followed predictable patterns. In other words, the cryptography was not broken; the anonymity set was being thinned by behavior. If someone deposits a distinctive amount and soon withdraws the same distinctive amount, public observers may not prove the linkage with mathematical certainty, but they may infer it with high confidence.
This is the central tradeoff of optional privacy. Optional privacy is operationally easier for some users and services because transparent transactions remain available. But optional privacy also means many participants may choose the transparent route, and mixed behavior can leak information across the boundary. This is one of the most meaningful contrasts with systems that enforce privacy by default. Zcash gives users a choice; that choice can weaken the collective privacy outcome.
None of this means shielded transactions are pointless. It means the unit of analysis must be precise. The cryptographic mechanism can be excellent while the ecosystem’s realized anonymity is uneven.
How does Zcash operate as a live blockchain (consensus, nodes, and operational risks)?
Zcash is not only a privacy design; it is also a functioning blockchain with consensus rules, mining, node software, upgrades, wallets, exchanges, and operational hazards.
The network inherited much of its original structure from Bitcoin, including a proof-of-work model, though Zcash uses Equihash, a memory-hard proof-of-work algorithm that was intended to mitigate mining centralization pressures. The protocol specification also defines block subsidy rules and funding streams across network upgrades. These economic rules matter because privacy features do not live outside incentive systems. Someone still has to secure the chain, run nodes, and maintain software.
On the implementation side, zcashd is the reference consensus node and stores the full chain history. Its documentation emphasizes that Zcash is experimental and a work in progress, and that old releases are deprecated on a relatively short schedule. There is also Zebra, an independent consensus-compatible node implementation from the Zcash Foundation. Multiple implementations matter for decentralization because they reduce dependence on a single codebase and can expose specification ambiguities before those ambiguities become network problems.
This point is easy to miss when discussions focus only on privacy features. A privacy-preserving currency still depends on mundane software engineering: correct parsers, safe serialization, robust networking, release management, and incident response. Zcash’s security pages document advisories, signed release channels, and past vulnerabilities. That history is not evidence that the project failed; it is evidence that a privacy protocol is still software and therefore inherits software risk.
A concrete example is the 2019 vulnerability cataloged as CVE-2019-16930, which allowed discovery of the IP address of a full node owning a shielded address under certain conditions. That did not mean shielded cryptography had failed in the narrow sense of proof soundness. It meant privacy can be lost through implementation details and network behavior even when the core proving system remains intact. In systems like Zcash, cryptographic privacy and operational privacy are related but not identical.
Who uses Zcash and what are common real-world use cases?
People use Zcash when they want blockchain-based money with the possibility of keeping payment details confidential. That can mean personal payments, treasury transfers, saving in a privacy-preserving asset, or cases where public transaction graphs would expose counterparties, balances, or business relationships too easily.
The protocol’s viewing-key model also makes it useful in settings where privacy must coexist with selective oversight. A user can preserve confidentiality on-chain without giving up the ability to disclose records intentionally. That is a meaningful difference from systems where privacy is either absent or awkward to share in a controlled way.
Zcash’s official materials also emphasize practical usability: broad wallet and exchange support, faster blocks than Bitcoin, and typically low fees. Those are not side details. Privacy technology that is too costly or too inaccessible becomes a lab success rather than a monetary network. Zcash’s long sequence of upgrades can be understood partly as attempts to make shielded usage practical enough to matter in day-to-day conditions.
What assumptions must hold for Zcash privacy and integrity to work?
Zcash works only if several layers hold at once.
At the cryptographic layer, the zero-knowledge proofs, commitments, nullifiers, signatures, and setup assumptions have to behave as intended. At the consensus layer, all nodes must agree on the same transaction validity rules and state transitions. At the wallet layer, software has to generate proofs correctly, manage keys safely, and avoid leaking metadata. At the network layer, users must consider IP privacy and peer-to-peer exposure. And at the ecosystem layer, enough people have to use shielded transactions in ways that do not make linking trivial.
Change any one of those assumptions and the practical privacy story can change sharply. If fully shielded usage is sparse, anonymity shrinks. If wallet defaults encourage transparent behavior, privacy becomes niche. If a bug leaks metadata, a shielded note can still become associated with a user. If setup assumptions are distrusted, users may worry about integrity even if they still trust confidentiality.
This is not unique to Zcash. It is what happens whenever a protocol tries to make a public system support private behavior. The real achievement is not that Zcash eliminated every assumption. It is that it made the core privacy mechanism compatible with decentralized consensus at all.
Conclusion
Zcash is a cryptocurrency that asks a precise question: can a public blockchain verify money without publicly exposing the payment? Its answer is yes, if the chain verifies proofs of correctness instead of demanding full transaction visibility.
Everything else follows from that idea. Shielded notes replace visible coins, commitments and nullifiers preserve private accounting, zk-SNARKs prove valid spending, and viewing keys make privacy selectively shareable. The result is one of the clearest demonstrations that blockchain transparency is not the only way to get decentralized trust; only the oldest and simplest one.
How do you buy Zcash?
You can buy Zcash (ZEC) on Cube Exchange by funding your account and placing a spot order on the ZEC market. The Cube workflow keeps everything on the exchange: deposit fiat or a supported crypto, open the ZEC spot market, and choose the execution style that fits your goal.
- Deposit fiat (USD/EUR) via Cube’s on-ramp or transfer a supported stablecoin (USDC) into your Cube wallet.
- Open the ZEC/USD or ZEC/USDC spot market on Cube and select the market or limit tab.
- For immediate fills choose a market order; for price control choose a limit order and set your target price.
- Enter the ZEC amount or the fiat/stablecoin you want to spend, review fees and estimated fill, then submit the order.
Frequently Asked Questions
When a shielded note is created the chain publishes a cryptographic note commitment (appended to a note-commitment Merkle tree) and when that note is spent the transaction reveals a nullifier unique to that note; nodes check that the nullifier is new and that the zk-SNARK proves the nullifier corresponds to a committed note without learning which commitment it was, preventing double-spends while keeping the note contents hidden.
Zcash’s zk-SNARKs relied on a one-time parameter generation (a "trusted setup") whose soundness is required to prevent someone from forging valid-looking proofs for invalid transactions, and to reduce trust Zcash ran multi-party ceremonies so that as long as at least one contributor destroyed their secret material the toxic secret could not be recovered.
Compromise of the trusted setup threatens soundness (the ability to create counterfeit valid proofs and break balance guarantees) but does not automatically imply loss of anonymity; the literature and Zcash materials draw a clear distinction between counterfeiting risk and privacy risk.
Sprout, Sapling, and Orchard are successive shielded designs introduced via upgrades because the original constructions were computationally heavy and impractical for many wallets; later generations (Sapling, Orchard) improved prover efficiency, wallet usability, and scanning performance to make shielded usage more practical.
Zcash supports viewing keys (which let a holder see incoming/outgoing shielded notes without spending rights) and diversified addresses (many unlinkable receiving addresses under one key), so shielded privacy is selective disclosure - useful for auditors or accountants - but not absolute invisibility from chosen third parties.
Yes - because privacy is optional, mixed use of transparent and shielded pools can leak linkages: empirical studies showed heuristics could often link deposits and withdrawals when users followed predictable patterns, so partial shielding and reuse patterns can thin the anonymity set.
Generating zk-SNARK proofs is non-trivial: early Zerocash provers took minutes for POUR circuits, and that prover cost motivated Sapling/Orchard optimizations to make proof generation and wallet scanning practical, but prover runtime and resource use remain important trade-offs for client usability.
No - shielded transactions are optional; Zcash supports both Bitcoin-like transparent funds and shielded notes, and the protocol specification warns that privacy guarantees apply to fully shielded usage whereas optional (mixed) usage can weaken collective anonymity.
Yes - there have been implementation-level privacy incidents: CVE-2019-16930 documented a vulnerability that could reveal a full node's IP address when a shielded address (zaddr) was disclosed to a third party, and Zcash security advisories and patches document such operational privacy risks separate from the core cryptography.
Public artifacts and attestations from Zcash ceremony work (e.g., sapling-mpc and powersoftau-attestations repositories) are available, but repository READMEs and listings do not clearly present one consolidated archive of final Sapling parameters or full participant logs, so locating and verifying the complete set of ceremony artifacts can require consulting multiple repositories and attestations.
Related reading