What is Quorum?
Learn what a quorum is in consensus: why overlapping decision sets prevent conflicting outcomes, and how majority and 2/3 thresholds work.
Introduction
Quorum is the rule that says how many participants are enough for a distributed system to treat a decision as meaningful. In a blockchain or any consensus protocol, that question is not bookkeeping. It is the difference between a network that can survive failures and one that can split into incompatible histories.
The puzzle quorum solves is easy to state and hard to engineer around: if some machines are offline, slow, crashed, or malicious, why should any subset of the remaining machines be allowed to decide anything for everyone else? If the threshold is too low, two different groups may each think they have authority and decide conflicting results. If the threshold is too high, the system may become unable to decide at all whenever part of the network is unavailable. A quorum is the threshold chosen so that the system can keep operating and avoid contradictory decisions.
The central idea is not “majority voting” as a slogan. The deeper idea is intersection. A quorum is useful when any two quorums overlap in enough participants that information cannot diverge unnoticed. That shared overlap is what lets later rounds learn what earlier rounds may already have decided. Once that clicks, a wide range of protocols (Paxos, PBFT, Tendermint-style BFT protocols, GRANDPA-style finality gadgets, and federated systems like Stellar) start to look like variations on the same structural constraint.
Why do consensus protocols use quorums instead of requiring unanimity?
Suppose five validators are deciding whether block B should be accepted. If the protocol required all five to respond, then one crash or one network delay could stall the system. That is too brittle. But if the protocol allowed any two validators to decide, then validators {A, B} might accept B while validators {C, D} accept a conflicting block B', and now the network has two incompatible outcomes. That is too loose.
What you want is a threshold that preserves a simple invariant: two different successful decision sets must overlap. With five participants, a threshold of three works because any two sets of size three must share at least one member. That one shared member cannot honestly support two conflicting outcomes if the protocol is designed properly. The overlap acts as a bridge carrying state from one candidate decision to the next.
This is why quorums are usually discussed as sets, not just percentages. A quorum is not merely “a lot of nodes.” It is a set chosen under rules that guarantee a structural property about how successful decision groups relate to each other. The property that matters most is intersection. Once you have that, you can build safety arguments. Without it, safety typically becomes impossible.
An analogy helps here. Think of a quorum like requiring enough witnesses to sign a document such that any later valid document must share at least one witness with the earlier one. That common witness can stop contradictory versions from both appearing legitimate. The analogy explains why overlap matters. It fails in one important way: in consensus protocols, witnesses are not passive observers. They keep protocol state, may fail and recover, may be weighted by stake, and may themselves be malicious. So the real mechanism is stricter than just “shared signatures.”
How do quorums preserve safety in consensus protocols?
Consensus protocols are usually balancing two goals that people often blur together: safety and liveness. Safety means the system does not decide conflicting outcomes. Liveness means it eventually decides something. Quorums are first and foremost a tool for safety.
Paxos gives the cleanest first-principles example. There, a value is considered chosen once a majority of acceptors has accepted it. Why a majority? Because any two majorities intersect. That overlap ensures that when a later proposer tries to make progress, it must encounter at least one acceptor from any previously successful majority. In Paxos, that acceptor reports the highest-numbered proposal it has already accepted, and the later proposer must respect that information. The protocol is built so that the overlap is not just a mathematical curiosity; it is the channel through which already-chosen information constrains future proposals.
This is the core pattern across quorum-based consensus. The quorum threshold alone does not create safety. Safety comes from quorum intersection plus rules that force overlapping members to carry forward prior state. In Paxos, those rules appear in the prepare and accept phases. Acceptors promise not to accept lower-numbered proposals after responding to a higher-numbered prepare, and proposers that hear about earlier accepted values must propose consistently with them. Without those state-carrying rules, the intersection would exist but might not actually prevent divergence.
A subtle point matters here: quorum safety often depends on participants persisting certain facts across crashes. Lamport’s presentation of Paxos is explicit that acceptors must remember the highest prepare request they answered and the highest-numbered proposal they accepted, even if they fail and restart. If a node forgets that state, it can re-enter the system as though history never happened, violating the very overlap invariant the quorum was supposed to enforce.
So a useful short definition is this: a quorum is a set of participants large enough, and constrained enough by protocol rules, that successful decisions cannot be made independently in contradictory ways.
How do fault models (crash vs. Byzantine) change quorum thresholds?
| Fault model | Quorum rule | Quorum size | Overlap guarantee | Example protocols |
|---|---|---|---|---|
| Crash faults | Majority rule | >50% of nodes | Any two majorities intersect | Paxos |
| Byzantine faults | Supermajority rule | >66% of nodes | Overlap contains an honest node | PBFT, Tendermint |
| Byzantine with auth | Authenticated voting | Stake-weighted supermajority | Signed votes prove honest overlap | Signed-message BFTs |
The next thing that makes quorum click is realizing that the threshold depends on what kinds of failures you are trying to survive.
If failures are only crash faults (nodes stop responding, restart, or become unreachable, but do not lie) then majority quorums are often enough. Paxos lives in this world. With n acceptors, a majority is any set larger than n/2. Two such sets must intersect, and that intersection is enough when honest nodes do not equivocate.
If failures can be Byzantine then simple majority is not enough.
- nodes may lie
- equivocate
- send different messages to different peers
- behave arbitrarily
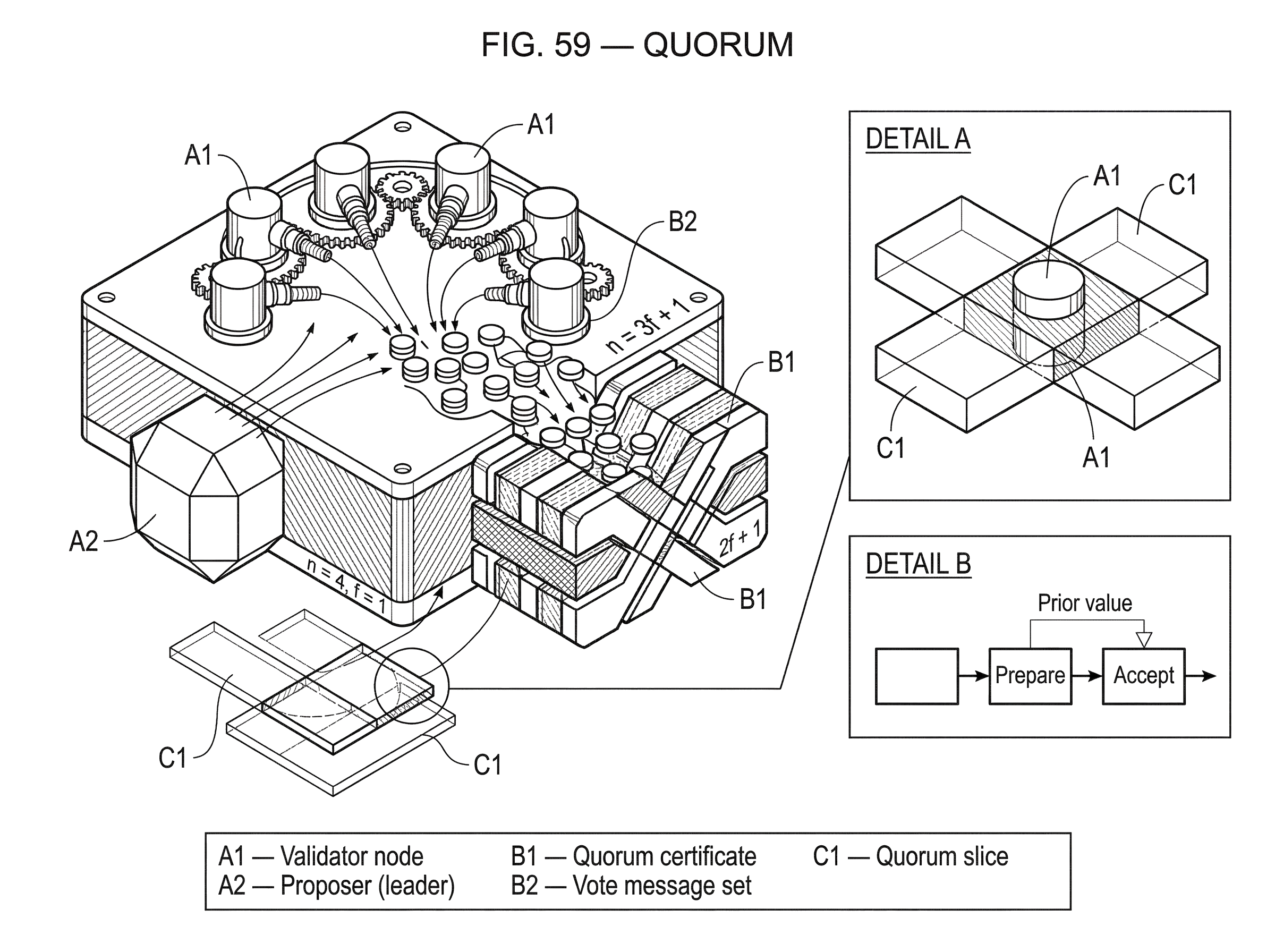
The classic Byzantine Generals result shows that with ordinary unauthenticated messages, tolerating f Byzantine faults requires at least n = 3f + 1 participants. In that setting, protocols typically rely on quorums of size 2f + 1, which is more than two-thirds of the full set.
Why does the threshold rise from “more than half” to “more than two-thirds”? Because in the Byzantine case, overlap alone is not sufficient; the overlap must contain enough honest participants to matter. Two quorums of size 2f + 1 in a system of 3f + 1 participants overlap in at least f + 1 participants. Since at most f can be Byzantine, that overlap must include at least one honest participant. That honest overlap is the minimum anchor safety arguments need.
This is the key arithmetic behind PBFT, Tendermint-style voting, Solana’s two-thirds vote canonicalization, and GRANDPA-style supermajority finality. Different protocols package the rule differently, but the underlying shape is similar: if the system wants to tolerate up to one-third Byzantine participants, then decisive certificates usually need support from more than two-thirds.
Example: how quorum intersection prevents conflicting finalization in BFT systems
Consider a network with n = 4 validators and tolerance for f = 1 Byzantine validator. In that model, the decisive quorum size is 2f + 1 = 3. Imagine one block X is claimed to be finalized by a quorum. That means three validators signed the required messages for X.
Now suppose someone claims a conflicting block Y at the same height also finalized. That would also require three validators. But among four validators, two sets of three must overlap in at least two validators. Since only one validator can be Byzantine, at least one validator in that overlap must be honest.
Here is the mechanism. An honest validator follows locking or voting rules that prevent it from signing conflicting finality paths at the same height or view unless specific safety conditions are met. So if X really gathered a quorum certificate, any later attempt to certify Y runs into the overlap: some honest validator in both candidate quorums refuses to support the conflict. In protocols like PBFT, this is reinforced through prepare and commit stages; in Tendermint-style protocols, through prevote and precommit with locking; in GRANDPA, through supermajority voting over chains and accountable equivocation rules. The protocol details differ, but they all turn quorum overlap into a practical barrier against contradictory finalization.
Notice what is doing the work. It is not the number three by itself. It is the combination of three facts: the quorum is large enough, overlapping quorums therefore share validators, and honest validators are constrained by rules that stop them from endorsing both sides. If any one of those pieces disappears, safety can fail.
What is a quorum certificate and why do protocols need one?
| Evidence type | What it contains | Portable proof? | Requires signatures? | Main limitation |
|---|---|---|---|---|
| Live headcount | Count of responsive nodes | No | No | Not verifiable externally |
| Collected votes | Set of validator signatures | Yes | Yes | Large payload without aggregation |
| Aggregated signature | Compact combined signature | Yes | Yes | Requires aggregation scheme |
In real systems, people often speak of “reaching quorum” as though it means counting live nodes. But consensus protocols usually need something stronger: a quorum certificate, explicit evidence that the threshold was met according to protocol rules.
In PBFT, a replica becomes prepared only after recording a client request, a matching pre-prepare, and enough matching prepare messages from other replicas. It later becomes committed-local after receiving the required commit messages. Those collected messages are not ceremonial. They are the proof that enough replicas saw and endorsed the same operation in the same place in the sequence.
That distinction matters because distributed systems are not centralized observers. No one can simply inspect the network and declare that “a quorum must have happened.” Instead, nodes accumulate signed or authenticated messages and use them as portable evidence. In many modern BFT protocols, this evidence is compressed into a quorum certificate consisting of aggregated signatures or a set of validator signatures.
This is also why cryptography matters. Byzantine agreement with signed messages is easier to structure than with unauthenticated oral messages. The classic Byzantine Generals paper shows that unforgeable signatures dramatically change what is possible. Modern blockchains lean heavily on signatures, MACs, and authenticated voting records because quorum rules are only as strong as the system’s ability to prove who voted for what.
Does having a quorum guarantee liveness (will the system make progress)?
A common misunderstanding is that once you have a quorum threshold, consensus is solved. It is not. Quorums explain when a decision is valid; they do not by themselves ensure the system will reach a valid decision.
Paxos makes this explicit. Majority quorums protect safety, but progress may still stall if multiple proposers keep interfering with each other. To guarantee progress, Paxos typically relies on a distinguished proposer, or leader, that can communicate with a majority. In other words, quorums define the acceptance condition, but some coordination mechanism is still needed to drive proposals through that condition.
The same pattern shows up in BFT systems. PBFT uses a primary and view changes. Tendermint-style protocols use proposers and rounds with timeouts. GRANDPA needs partial synchrony to guarantee termination, because deterministic finality is impossible in full asynchrony. Solana’s Tower BFT uses Proof of History as a network clock to compute and enforce timeout behavior while still depending on a two-thirds validator threshold for canonicalization.
So here is the clean separation: quorum is mostly about who is enough to make a decision safe; liveness is about how the system gets such a set to align in time. The first is a structural property. The second is an execution property. Good protocol design needs both.
How do stake-weighted quorums differ from one-node-one-vote quorums?
So far the examples have treated all participants as equal. Many blockchains do not. In proof-of-stake systems, quorum is usually defined over voting power, not raw node count.
That changes the arithmetic but not the principle. Instead of saying “three out of four validators,” the protocol says something like “more than two-thirds of total stake weight.” A validator with more stake carries more voting power, so quorums become sets whose combined weight crosses a threshold. The safety condition is still about overlap, but now the overlap is measured in honest voting weight rather than the number of identities.
This is why phrases like “two-thirds of validators” can be misleading in production networks. The real rule may be “validators representing at least two-thirds of active stake.” Solana’s description of Tower BFT, for example, frames canonicalization around two-thirds of validators voting on a Proof-of-History hash, but the protocol’s broader operation is stake-weighted. GRANDPA and many proof-of-stake systems likewise reason in terms of eligible voters and supermajority thresholds tied to the protocol’s validator set.
The concept stays the same: a quorum is the minimum support needed such that another conflicting quorum cannot exist without overlapping honest voting power.
How do federated quorum slices (FBAS) work and what are their risks?
| Model | Quorum formed by | Intersection requirement | Configuration complexity | Best for |
|---|---|---|---|---|
| Fixed membership | Global validator set | Simple global intersection | Low | Permissioned chains |
| Stake-weighted | Voting power thresholds | Overlap measured by stake | Medium | Proof-of-stake networks |
| Federated slices | Per-node trust slices | Depends on slice overlap | High | Open-membership systems |
The most familiar quorum model assumes a fixed validator set known to all participants. But not every system works that way. Federated Byzantine Agreement, as used in Stellar’s model, changes the picture by letting each node choose whom it trusts.
In that setting, each node defines one or more quorum slices: subsets of participants sufficient to convince that node. A system-level quorum is then a set U such that every node in U finds at least one of its own slices contained within U. In plain language, a quorum is a group that is internally convincing to all of its members.
This is a powerful idea because it allows decentralized trust configuration rather than a single globally imposed committee. But it comes with a severe requirement: quorum intersection must still hold at the system level. If the chosen slices permit two disjoint quorums, then safety is impossible. The protocol cannot prevent two internally self-sufficient camps from confirming contradictory statements, because there is no shared overlap through which consistency can be enforced.
That is why Stellar’s formal work treats quorum intersection as fundamental, and why later research studies whether an FBAS contains disjoint quorums. In fact, some related decision problems are computationally hard in general. That is a useful warning: federated quorum systems buy flexibility, but they push more responsibility onto configuration. The hard part is no longer only protocol logic; it is also the structure of trust itself.
A related practical example appears in the XRP Ledger’s Unique Node List model. Each server has a list of validators it trusts not to collude. If different servers’ trusted lists overlap too little, they can reach different conclusions and fork. The docs explicitly warn that high overlap is necessary, and that recommended lists exist partly to keep that overlap high enough in practice. Again the same principle appears: local trust choices are only safe when they induce sufficient global intersection.
How do network and implementation issues affect quorum formation and finality?
It is tempting to treat quorum as a purely mathematical threshold, but production systems reveal its operational side.
A protocol may be perfectly safe on paper and still fail to make progress because quorum messages do not propagate quickly enough. Tendermint’s docs point to gossip as critical for liveness. Narwhal and Tusk are built around the idea that reliable dissemination and transaction ordering should be separated so that quorum-based BFT consensus is not bottlenecked by mempool transport. Solana’s outage reports show the same lesson from the negative side: if block propagation degrades badly enough, finalization slows because the votes and data needed to assemble effective quorums are delayed or lost in practice.
The point is not that quorum theory is wrong. The point is that a quorum must be reachable as a protocol event, not merely definable as a set. Networks, storage, write-ahead logs, timeout calibration, leader rotation, checkpointing, and replay protection all affect whether the abstract quorum threshold can actually be met under stress.
This is also why crash recovery and persistence are part of quorum safety, not just performance engineering. A validator that forgets prior votes, loses its lock state, or restarts without durable protocol memory can accidentally undermine the assumptions that make quorum intersection meaningful.
Common misconceptions about quorum and consensus
The biggest misunderstanding is thinking a quorum means “most participants agree.” That is often approximately true, but it misses the mechanism. The meaningful statement is: the protocol requires a set large enough that any two successful sets overlap in a way that preserves safety.
A second misunderstanding is assuming quorums automatically guarantee decentralization. They do not. A system can use quorums and still be operationally centralized if most voting power is concentrated, if most nodes follow the same trusted list publisher, or if liveness depends on a narrow leader set.
A third is treating quorum as a universal constant like “51%” or “66%.” Those numbers come from assumptions. Majority quorums fit crash-fault models like Paxos. Two-thirds-style quorums fit many Byzantine-fault-tolerant models with n = 3f + 1. Federated systems may not have a single global fraction at all; they rely on slice structure and overlap. Change the assumptions and the quorum rule changes with them.
A fourth misunderstanding is confusing safety with finality speed. A low-latency protocol may still use the same quorum principle as a slower one; what changes is how efficiently it disseminates data, schedules rounds, aggregates votes, or leverages clocks and network assumptions.
When do quorum assumptions fail? Key risks and failure modes
Quorum reasoning depends on assumptions that can fail in specific ways.
If too many participants are Byzantine, the threshold no longer guarantees honest overlap. If durable state is lost, previously safe nodes may rejoin inconsistently. If the validator set changes without careful transition rules, old and new quorums may fail to intersect in the right way. If trust lists in a federated system are misconfigured, disjoint quorums may exist even though every individual node thinks its own settings are reasonable.
Even when safety still holds, liveness may fail. A network partition can leave each side below quorum. Multiple competing leaders can keep preempting one another. Adversarial timing can delay termination in partially synchronous systems. Stellar’s own literature notes perpetual preemption concerns in practice. GRANDPA explicitly requires partial synchrony for liveness. Paxos requires a stable leader for progress. These are not edge cases tacked on after the fact; they are part of what quorum-based consensus must live with.
This is why good consensus explanations always separate what is fundamental from what is conventional. Fundamental: successful decision sets must intersect appropriately, and protocol state must flow through that intersection. Conventional: whether the protocol names the phases prepare/accept, pre-prepare/prepare/commit, prevote/precommit, or something else. The naming varies. The underlying safety structure does not.
Conclusion
A quorum is the minimum set of participants whose support is enough to make a distributed decision count. The reason quorums work is not simply that they are large, but that they are chosen so that successful decision sets intersect, and the protocol uses that intersection to carry prior commitments forward.
If you remember one thing, remember this: consensus does not require everyone; it requires enough overlap that the system cannot tell two incompatible stories at once.
Everything else follows from that idea and from the fault model the protocol is trying to survive.
- the exact threshold
- the voting phases
- the role of leaders
- whether votes are stake-weighted or trust-weighted
What should I check about quorum before trading or transferring?
Before trading or moving funds on a chain that uses quorum-based finality, know how that chain defines «enough» support (majority vs. supermajority, stake-weighted, or federated slices) and what proof it emits (quorum certificate or repeated confirmations). On Cube Exchange, follow a short checklist to confirm deposits are truly final and to avoid acting on unsettled state.
Frequently Asked Questions
Because the safety argument depends on overlap: any two successful decision sets must share at least one member so that previously committed information can be carried forward and prevent conflicting outcomes.
With crash faults a majority (more than n/2) suffices because any two majorities intersect; with Byzantine faults the threshold rises because the overlap must contain enough honest participants, leading to the common 3f+1/2f+1 arithmetic so two quorums of size 2f+1 overlap in at least f+1 members and thus at least one honest node.
No - a quorum threshold enforces when a decision would be safe, but it does not ensure the system will reach such a set; liveness typically needs additional coordination (a leader/proposer, timeouts, partial synchrony, or randomness) to drive agreement.
If nodes fail to persist the protocol state they are required to remember (for example the highest prepare answered or highest proposal accepted in Paxos), they can rejoin as if history never happened and break the overlap-based safety invariant.
Quorums are often implemented as quorum certificates: collected signed/authenticated messages (or aggregated signatures) proving the threshold was met, because nobody can inspect the network centrally and portable evidence is needed to show who voted for what.
In stake-weighted systems voting power replaces one-node-one-vote, so quorum size is measured in combined stake (e.g., “>2/3 of stake”) rather than count; the safety principle - sufficient overlap in honest voting power - remains the same even though the arithmetic changes.
Federated models let each node pick quorum slices and define system quorums from those slices, which enables decentralised trust but makes safety contingent on global quorum intersection - misconfigured or poorly overlapping slices can create disjoint quorums and make forks possible.
Changing the validator set or transition rules without care can break intersection between old and new quorums, so reconfiguration must preserve overlap or have explicit transition rules; otherwise old and new quorums might certify conflicting histories.
Operational realities matter: quorum thresholds are only useful if the needed votes and certificates can actually propagate and be persisted; poor gossip, message loss, or misconfigured persistence (and real incidents like Solana outages) can delay finalization or prevent quorums from forming in practice.
Related reading