What is Attestation?
Learn what attestation means in proof-of-stake consensus, how Ethereum attestations work, and why they matter for fork choice, finality, and scaling.
Introduction
Attestation is the signed vote a validator makes in a proof-of-stake consensus system to express its view of the chain. If a blockchain wants thousands of independent validators to agree on one history without trusting any single party, it needs a message that says, in effect, this is the block I think the chain should build on, and this is the checkpoint history I recognize as legitimate. That message is the attestation.
The important thing to notice is that a block by itself does not create consensus. A proposer can publish a block, but the network still needs a way to answer two harder questions: should this block become part of the canonical chain right now? and when can some past point in the chain be treated as final rather than merely current? Attestations solve both problems. They are how validators turn local observations into collective weight.
This is most visible in Ethereum’s proof-of-stake design, where attestations feed both fork choice and finality. But the underlying idea is broader. Many consensus systems need validators to produce signed statements about the state of the protocol: Tendermint has prevotes and precommits, for example, which play a similar role even though the message types and timing rules differ. The common structure is that consensus needs accountable votes, not just block production.
The reason the concept matters is simple: blocks propose, attestations decide. If you understand that sentence, much of modern proof-of-stake starts to become legible.
Why do proof-of-stake systems need attestations?
Suppose a network has many validators and a new block appears. Different validators may see that block at different times. Some may have seen another competing block first. Some may be temporarily partitioned from the rest of the network. If each validator just keeps building on whatever it saw first, the chain can drift into persistent disagreement.
So the protocol needs a way to collect and compare validator opinion. Not informal opinion, and not a node-local preference, but a signed, slashable, economically weighted message that can be verified by everyone else. That message has to do more than say “yes” or “no.” It must identify what the validator is voting for, when the vote applies, and how that vote should influence the chain.
In Ethereum, the key design choice is that an attestation carries two kinds of information at once. It contains a vote relevant to fork choice (roughly, which recent block the validator sees as the head of the chain) and a vote relevant to finality; which checkpoints should be justified and eventually finalized. That combination is not arbitrary. It exists because choosing the best current head and proving that an older checkpoint is irreversible are related but different tasks, and the protocol wants one validator action to contribute to both.
This is the compression point for the whole topic: an attestation is not just an acknowledgment that a block exists; it is a structured vote that turns stake into consensus weight.
What fields are in an Ethereum attestation and what do they mean?
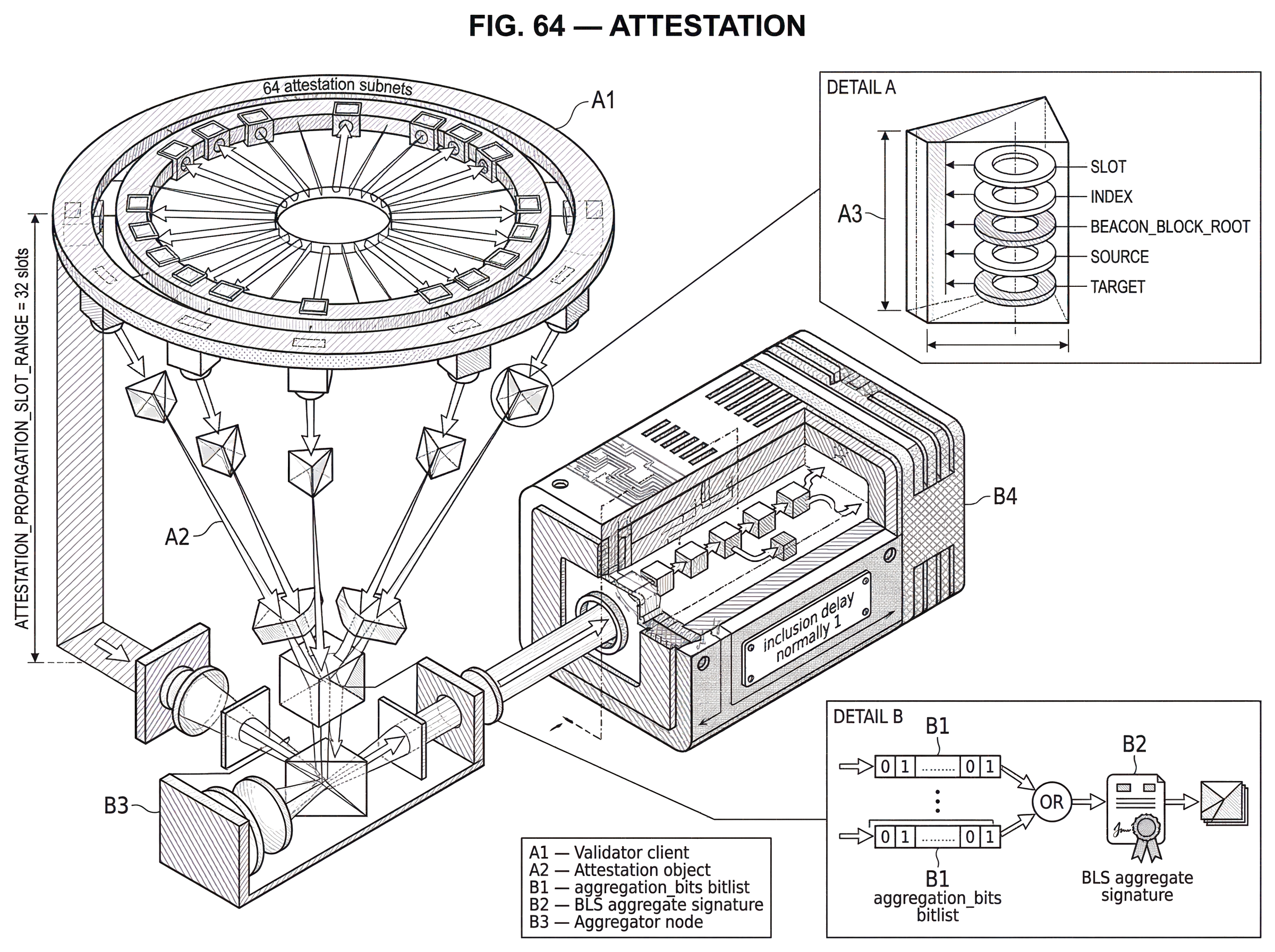
In Ethereum Phase 0, the canonical attestation object has three parts: aggregation_bits, data, and a BLS signature.
The easiest part to understand is data, because that is the actual content being voted on. AttestationData contains five fields: slot, index, beacon_block_root, source, and target. Here slot is the time position the attestation refers to, index identifies the validator committee assigned to attest in that slot, beacon_block_root is the block root the validator is voting for as head, and source plus target are checkpoints used by Casper FFG finality logic.
This is where attestation becomes more than “I saw block X.” The beacon_block_root is the validator’s fork-choice vote. The source and target checkpoints are the validator’s finality vote. In validator duties, the attestation data is constructed from the validator’s view of the chain at its assigned slot: the validator sets beacon_block_root to the current head block root, source to the current justified checkpoint, and target to the checkpoint for the current epoch boundary.
The aggregation_bits field answers a different question: which validators from this committee are represented by this attestation? It is a bitlist aligned with the committee. If the committee has 128 members and bit 17 is set, that means the validator at committee position 17 signed this same AttestationData. This makes aggregation possible, because many validators can vote for identical data and then be compressed into one on-chain object.
The signature proves that the represented validators really did sign that data. In Ethereum this uses BLS signatures, which are especially useful here because many signatures on the same message can be aggregated into a single compact signature and checked efficiently. The consensus specs explicitly use BLS aggregate verification, including FastAggregateVerify for indexed attestations. Without signature aggregation, the raw voting load would be much harder to handle at network scale.
Why does Ethereum aggregate attestations and how does that scale the network?
| Design | Bandwidth | On-chain cost | Scalability | Where used |
|---|---|---|---|---|
| Unaggregated votes | Individual signatures | High per-validator traffic | Many signatures stored | Propagated on attestation subnets |
| Aggregated attestations | BLS aggregate signature | Low, compact proof | Single signature per committee | Included in proposer blocks |
A first-time reader might think aggregation is just an optimization. It is better to think of it as a scaling mechanism without which the design would be much more expensive.
Ethereum’s specifications describe attestations as the primary source of load on the beacon chain. That makes sense. Validators are expected to create, sign, and broadcast an attestation during each epoch for their assigned committee and slot. If every validator’s vote were passed around, stored, and included individually, the network and chain would spend much of their capacity carrying repetitive information: the same AttestationData signed by many different validators.
Aggregation removes that redundancy. If a committee’s validators all agree on the same attestation data, an aggregator can combine their votes by setting the corresponding aggregation_bits and aggregating their signatures into one BLS signature. The resulting message still tells the protocol exactly who voted and for what, but much more compactly.
Mechanically, this happens in two stages on the network. Unaggregated attestations are first propagated on attestation subnets, which are smaller gossip domains. Aggregators gather matching attestations there. Then aggregated attestations are broadcast on the global aggregate topic for proposers to include in blocks. This split matters because it keeps the full network from having to process every individual vote before compression.
The networking spec also shows how deliberate the design is. There are 64 attestation subnets, nodes maintain persistent subnet subscriptions, and gossip acceptance is restricted to recent slots within ATTESTATION_PROPAGATION_SLOT_RANGE, which is 32 slots. These limits are not cosmetic. They bound bandwidth, memory pressure, and denial-of-service surface.
How does a single attestation become protocol weight in Ethereum?
Imagine a validator assigned to a committee for slot s. At the start of that slot, the validator looks at its local fork-choice view and identifies the current head block. It also knows the currently justified checkpoint and the block at the boundary of the current epoch. From those observations it constructs AttestationData: this slot, this committee index, this head block root, this source checkpoint, this target checkpoint.
The validator signs that data and sets exactly one bit in aggregation_bits, the one corresponding to its own position in the committee. That is now an unaggregated attestation. It gets broadcast on the validator’s assigned subnet, where peers verify basic conditions: the committee index must be in range, the slot must be recent enough, the subnet mapping must be correct, the bitlist must match the committee size, and for unaggregated subnet gossip exactly one participating validator bit must be set. A malformed or mistimed message is rejected or ignored rather than amplified.
Now suppose many other validators in the same committee saw the same head and therefore produced attestations with the same AttestationData. An aggregator (selected pseudo-randomly using a slot-selection proof) collects those matching attestations. It forms a new attestation by OR-ing their aggregation_bits together and aggregating their BLS signatures into one signature. The content being voted on has not changed. What changed is that many identical votes have been compressed into one proof object.
A block proposer later sees this aggregate and includes it in a block. When the chain processes that inclusion, it checks that the attestation refers to either the current or previous epoch, that the target epoch matches the attestation slot’s epoch, that the inclusion delay is within allowed bounds, that the committee index is valid, and that the indexed form of the attestation has valid, sorted, unique attesting indices together with a valid aggregate signature. If those checks pass, the attestation is recorded for participation accounting and later reward/finality processing.
At that point the attestation begins doing its real work. The validators represented in it can receive rewards depending on whether they matched the correct source, target, and head, and depending on inclusion delay. Separately, fork choice can use the validators’ latest messages to assign weight to branches, and epoch processing can use matching target attestations to justify and finalize checkpoints.
So the chain does not “count signatures” in the abstract. It takes a signed statement, checks that it is timely and well-formed, maps it to validator identities, and turns those identities’ stake into protocol weight.
How do attestations drive Ethereum's fork-choice (LMD-GHOST)?
Fork choice answers the question: if there are competing valid chains, which one should I build on now? In Ethereum’s design this uses LMD-GHOST, where “LMD” means Latest Message Driven. The idea is that for each validator, the protocol cares about that validator’s latest valid attestation, not its entire history of votes.
The fork-choice specification models this with a latest_messages mapping from validator index to a LatestMessage containing an epoch and root. A block’s attestation score is then computed by summing the effective balances of active, unslashed, non-equivocating validators whose latest message supports that block along the ancestor relation. In ordinary language: a branch gets weight from validators whose most recent vote points into that branch.
This is why the beacon_block_root field matters so much. It is not merely descriptive metadata. It is the payload that lets a validator’s latest message influence the head-selection rule.
The timing rules also matter. An attestation cannot affect fork choice immediately in the same slot it refers to; the spec requires get_current_slot(store) >= attestation.data.slot + 1. That may seem like a small detail, but it reduces ambiguity about which attestations are available when choosing among same-slot proposals. Consensus systems often depend on exactly these sorts of timing boundaries to stay deterministic enough for independent clients to converge.
Fork choice also excludes weight from slashed or equivocating validators. Once an attester slashing identifies conflicting behavior, the store records those validators in equivocating_indices, and their future attestation weight is ignored in scoring. This is a good example of the accountability property of attestation: the message is useful not only when honest, but also because dishonest conflicting messages can be proven and punished.
How do attestations contribute to checkpoint justification and finality?
| Role | Unit | Attestation fields | Timing / epoch | Protocol effect |
|---|---|---|---|---|
| Fork choice | Block head | beaconblockroot | Applies after slot + 1 | Assigns weight to branches (LMD‑GHOST) |
| Finality (Casper FFG) | Epoch checkpoint | source and target checkpoints | Uses previous/current epoch sets | Justifies and finalizes checkpoints |
Fork choice tells the network what to build on next. Finality tells the network when some past checkpoint should be treated as no longer reversible except under severe fault assumptions. These are different jobs, and attestations feed both.
In Ethereum’s epoch processing, attestations are organized into previous-epoch and current-epoch sets. The protocol extracts matching target attestations and uses their stake weight relative to total active balance to determine whether checkpoints become justified and finalized. This is the Casper FFG side of the system.
The source and target fields in AttestationData are what make that possible. The source identifies the justified checkpoint a validator is building from, and the target identifies the epoch checkpoint the validator wants to justify. A reader might wonder why the attestation needs both these checkpoint fields and a separate head vote. The answer is that a chain can have a momentary preferred head without yet having enough coordinated support to justify or finalize the relevant checkpoints. Finality needs a coarser-grained, checkpoint-based structure.
The protocol also ties these pieces together. Fork-choice validation requires the attestation target root to match the checkpoint block of the attested beacon_block_root at that epoch. That consistency condition prevents the head vote and checkpoint vote from floating apart into unrelated claims.
One subtle caveat from the validator spec is that attestations during GENESIS_EPOCH do not count toward FFG finality, even though they still influence fork choice and are rewarded. That is a reminder that “attestation” is a generic message type, but the effect of a valid attestation can still depend on the chain’s phase and state.
How does inclusion delay affect attestation rewards and effectiveness?
Attestations are only useful if they arrive in time to influence the protocol. That is why the spec places narrow windows around when an attestation may be created, propagated, and included.
At state transition time, process_attestation requires the attestation target epoch to be either the current or previous epoch, and enforces an inclusion window: the attestation’s slot plus the minimum inclusion delay must be no later than the current state slot, and the current state slot must still be within the allowed epoch window. A stale attestation is not harmless background data; it is rejected because consensus weight has to be tied to a precise time horizon.
Economically, inclusion delay affects rewards. Ethereum’s reward logic breaks attestation outcomes into source, target, head, inclusion-delay, and inactivity components. The developer docs emphasize that inclusion delay is normally 1, because an attestation for block n is usually included in block n+1. If delay increases, the validator’s reward falls proportionally. This gives validators and proposers a reason to care not just about eventual inclusion, but about fast inclusion.
Operationally, this creates failure modes that are easy to underestimate. A validator can produce a locally correct attestation and still miss rewards or minority inclusion if it saw the head block late, had poor subnet connectivity, or if aggregators and proposers favored a larger majority-compatible aggregate. Operator guidance from Lighthouse makes this concrete: a block or blob arriving too late in the slot can force a validator into a minority head vote, which compresses worse and is less attractive for proposers to include.
This illustrates a broader point: attestation is a consensus object, but its success depends on networking and timing almost as much as on cryptography.
What validation checks reject or accept Ethereum attestations?
Consensus messages are dangerous if admitted loosely. If a client accepts malformed, out-of-window, or ambiguous votes, the protocol can be skewed or overloaded. So attestation validation is intentionally narrow.
At the state-transition layer, the client checks epoch and slot consistency, committee index bounds, inclusion timing, and signature validity. For aggregate attestations, the indexed form must have non-empty, sorted, unique attesting indices and a valid aggregate BLS signature. On gossip, the network spec adds further rules tailored to the context: unaggregated subnet messages must have exactly one participating validator, aggregate-and-proof messages must prove that the sender is actually a selected aggregator, and signatures on both the aggregate and the aggregator proof must verify.
The underlying principle is that an attestation is valuable because it is structured and attributable. If either structure or attribution is weak, the message stops being useful as consensus weight.
This is also where cryptographic caveats matter. BLS aggregation is powerful, but only if implementations handle it correctly. The standards-oriented BLS draft emphasizes rogue-key defenses and requires subgroup checks on public keys and signatures. Ethereum’s use of proof-of-possession assumptions and fast aggregate verification depends on those validation disciplines. An aggregated signature is not “magic compression”; it is a precise cryptographic claim whose safety depends on correct verification rules.
How do attestations compare across consensus protocols (Ethereum vs Tendermint)?
| Protocol | Message types | Head vote | Finality vote | Design trade-off |
|---|---|---|---|---|
| Ethereum (Gasper) | Attestation (aggregated) | beaconblockroot field | source + target checkpoints | Single message for head + finality (compact) |
| Tendermint | Prevote / Precommit | Prevote messages | Precommit messages | Separate phases enforce monotonicity |
| Generic principle | Signed validator votes | Protocol-specific field | Checkpoint or phase-based vote | Tradeoff: compactness versus strict signing rules |
The term attestation is used most prominently in Ethereum, but the idea exists more broadly: consensus needs signed validator votes that are accountable and weighted.
Tendermint makes the contrast useful. Instead of one message carrying both head and checkpoint semantics, Tendermint has distinct signed message types such as Prevote and Precommit, each with strict signing validity and monotonicity rules. Validators must track the last signed height, round, and type to avoid double-signing. Mechanically this looks different from Ethereum’s attestation flow, but conceptually it solves the same problem: validators must emit signed protocol statements that let the network converge and that can be used as evidence if they equivocate.
That comparison helps separate what is fundamental from what is conventional. The fundamental part is that a distributed validator set needs signed, attributable votes. The conventional part is how a protocol packages those votes; whether as Ethereum-style attestations with head/source/target fields, or as Tendermint-style prevote/precommit phases.
Can attestations be used for data availability as well as consensus?
Ethereum’s Phase 0 specs describe attestations as not only proof-of-stake votes for beacon blocks but also, in later upgrades, availability votes for shard data. This matters because it shows that attestation is really a general-purpose validator statement about protocol reality, not just about block preference.
That broader role becomes clearer in blob-based scaling and data-availability designs. EIP-4844 introduces blob-carrying transactions whose data are propagated separately as sidecars. The consensus layer references those blobs without embedding all contents directly in the beacon block body. Longer term, designs such as PeerDAS aim to let nodes verify availability through sampling rather than downloading everything.
Why mention that in an article about attestation? Because the original concept already anticipated it. An attestation can be understood as a validator’s signed claim not just that “this is the head,” but that “this protocol object is acceptable to build on under the rules.” As data availability becomes a first-class consensus concern, attestations naturally become part of how validators certify that the network can safely proceed without every participant holding every byte.
How do attestations interact with slashing risk and custody practices?
Because attestations are signed consensus messages, producing conflicting ones can be slashable. That is why validator implementations are told to persist local slashing history and check it before signing. A validator restored from backup without its slashing database can accidentally sign a conflicting attestation and be penalized even if the operator had no malicious intent.
This signing-discipline point connects to a broader operational lesson in cryptographic systems: the most dangerous message is often a perfectly valid signature on the wrong thing.
A related principle appears outside base-layer consensus in systems that use threshold cryptography. For example, Cube Exchange uses a 2-of-3 Threshold Signature Scheme for decentralized settlement: the user, Cube Exchange, and an independent Guardian Network each hold one key share; no full private key is ever assembled in one place, and any two shares are required to authorize a settlement. That is not an attestation system in the Ethereum consensus sense, but it illustrates the same design instinct: authorization should come from accountable, distributed signing rather than a single trusted key holder. In consensus, attestations are the distributed signatures that authorize chain progression.
What are the main attack vectors and operational failures involving attestations?
Attestations are central enough that weaknesses in how they are counted or timed can threaten the whole protocol. Research on Gasper formalizes the intended safety and liveness properties of combining Casper FFG with LMD-GHOST, while other research has argued that GHOST-style fork choice in proof-of-stake can admit subtle attack surfaces, including LMD-specific balancing attacks under some assumptions. The exact practical significance of those results depends on the model and mitigations, but they underscore an important fact: once validator votes become the engine of consensus, the vote-counting rule itself becomes a critical security boundary.
Even without adversarial breakthroughs, there are ordinary limits. Attestations depend on reasonably synchronized clocks, healthy gossip, competent aggregation, and correct local signing state. They can be valid later even if not yet processable now, which is why the fork-choice spec notes that some currently invalid attestations may need delayed processing rather than outright discard. The message is simple, but the environment around it is not.
Conclusion
An attestation is a validator’s signed, structured vote about the chain. In Ethereum, it simultaneously says which block should count as head and which checkpoints should advance toward finality, and then the protocol turns those votes into fork-choice weight, rewards, penalties, and eventually finalized history.
The memorable version is this: a block proposes a possible future; attestations decide whether the network adopts it. Once you see that, proof-of-stake consensus stops looking like a stream of blocks and starts looking like what it really is; a continuous process of collecting, validating, aggregating, and weighing accountable votes.
What should you understand before using attestation-dependent infrastructure?
Before acting on-chain, understand that attestations determine when history becomes irreversible: check finality and inclusion behavior so you do not trade or move large funds based on a non-final block. Use Cube Exchange to fund, trade, and withdraw while you verify network finality and inclusion timing.
- Check the chain’s current finalized checkpoint and recent attestation/inclusion health on a block explorer or node RPC; confirm the specific deposit or block you rely on is finalized.
- Fund your Cube Exchange account via the fiat on-ramp or a supported crypto transfer on the same network you plan to use.
- For large deposits or transfers, wait for the deposit block to reach a finalized checkpoint before trading or initiating withdrawals; prefer finalized checkpoints over single-block confirmations on Ethereum-like chains.
- When placing trades on Cube, use limit orders for large sizes or thin markets, or split the order to reduce execution risk from transient forks or inclusion delays.
- Request withdrawals only after Cube shows the deposit as settled and you verify the corresponding on-chain state is finalized on the source chain.
Frequently Asked Questions
Because selecting a current head (fork choice) and declaring older checkpoints irreversible (finality) are different tasks, Ethereum packs both into one signed message so a single validator action can contribute to immediate head-weight and to checkpoint justification/finality at the same time.
Aggregation compresses many identical validator votes into one on-chain object by OR-ing aggregation_bits and aggregating BLS signatures, and it is necessary because passing every individual attestation around would create a large, repetitive network and chain load that the protocol would struggle to handle at scale.
If an attestation is included with high delay or outside the allowed windows it may reduce or forfeit attester rewards and - if it violates slot/epoch/inclusion constraints - be rejected by process_attestation; operationally, late or poorly-propagated attestations also weaken a validator’s contribution to fork-choice and finality.
Conflicting or double-signed attestations are slashable evidence, so validators must persist local signing/slashing state and avoid signing far-future or conflicting messages; restoring a validator from backup without its slashing history can cause accidental slashing.
Attestations create several practical failure surfaces: the vote-counting rule itself can be attacked (research on Gasper/LMD-GHOST shows subtle attacks), and non-adversarial failures arise from poor gossip, missed aggregators, or timing issues; implementation mistakes (e.g., improper BLS checks) are another concrete risk.
Fork choice uses LMD-GHOST: each validator’s most recent valid attestation (stored in latest_messages) is what gives weight to branches, so only a validator’s latest message matters for head-selection rather than its full voting history.
BLS aggregation is powerful but requires strict verification disciplines - implementations must enforce rogue-key protections, proof-of-possession or FastAggregateVerify semantics, and subgroup (membership) checks on public keys and signatures; skipping these checks can enable forgeries or other undefined behaviors.
Related reading