What Is a Price Oracle?
Learn what a price oracle is, why smart contracts need it, how it works, and where oracle designs fail under manipulation, staleness, or bad sources.
Introduction
Price oracle is the name for a system that tells a blockchain application what some asset is worth. That may sound like a small detail, but it solves one of the deepest constraints of smart contracts: blockchains are very good at verifying their own internal state, and very bad at knowing anything about the outside world unless someone brings that information in.
This becomes economically serious the moment a contract needs to decide whether a user can borrow against collateral, whether a perpetual position should be liquidated, or what exchange rate to use when settling a trade. In each of those cases, the contract is not really asking for “data” in the abstract. It is asking for a market judgment that can move money. If the price is stale, manipulable, delayed in the wrong way, or simply wrong, the contract can behave exactly as written and still fail.
The central puzzle is that price is not a native blockchain fact. A token balance on Ethereum is a native fact. A validator signature on BandChain is a native fact. But “BTC is worth x dollars right now” is not stored in any chain by default, and even in traditional markets there is no single universal price floating in the air. There are only trades on venues, quotes from market makers, indexes built from multiple venues, and models that summarize all of that into a number. A price oracle exists because smart contracts need one such number to act on.
Why do smart contracts need a price oracle instead of raw market data?
The key idea that makes price oracles click is this: a smart contract wants a crisp value at a precise moment, while real markets produce noisy, fragmented, time-dependent information. The oracle is the machinery that compresses that messy process into an on-chain value the contract can consume.
That compression involves choices. Which venues count? Do you use spot prices, time-weighted averages, medians across reporters, or some other aggregation? How fresh does the answer need to be? What happens if one source is unavailable? Should the protocol prefer speed or manipulation resistance? These are not implementation details added after the fact. They are part of what the oracle is.
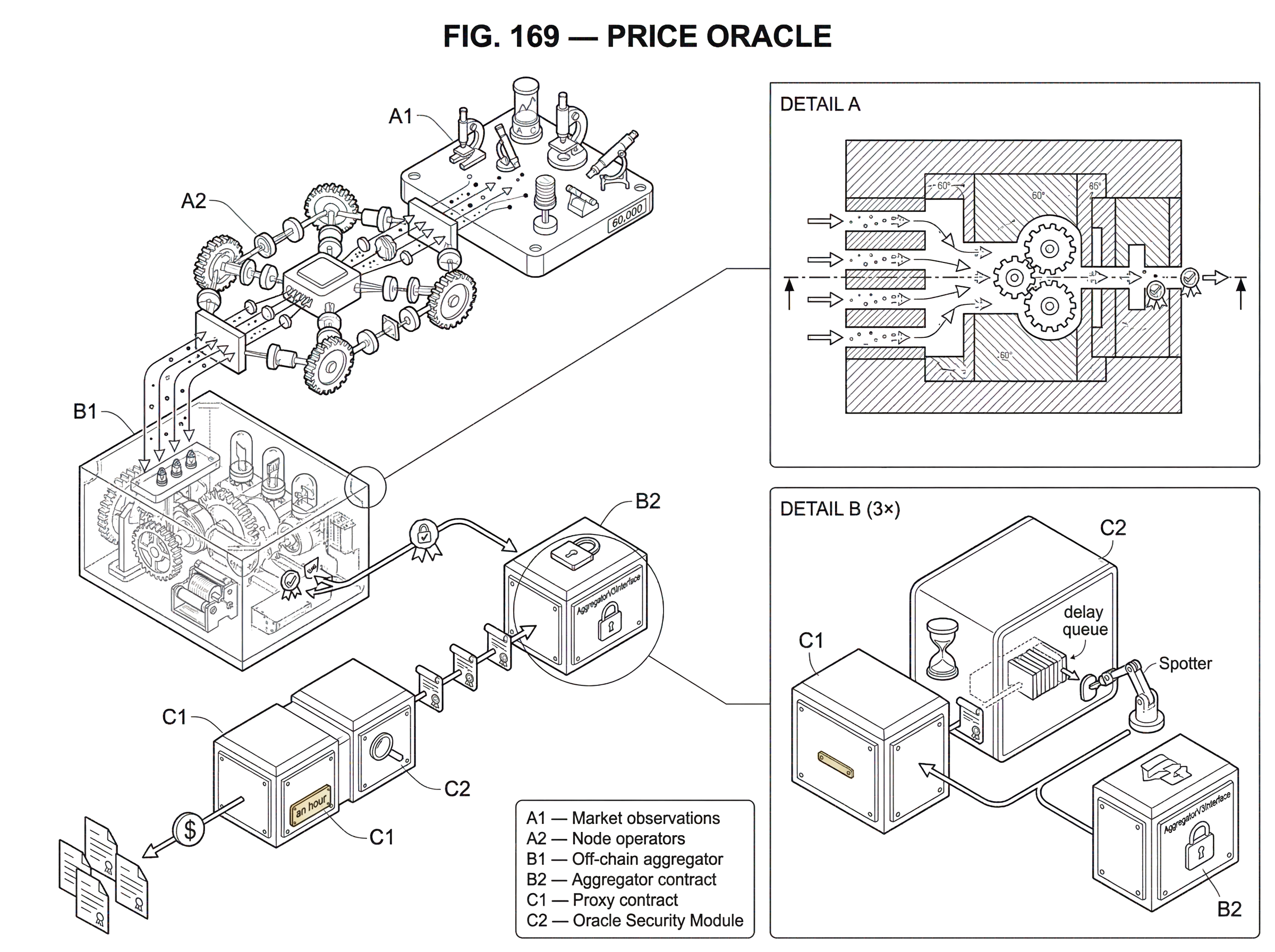
This is why a price oracle should not be imagined as a magical API call that fetches “the true price.” A better mental model is a pipeline with three linked jobs. First, gather candidate observations from some set of sources. Second, transform them into a reference value according to a rule. Third, make that value available on-chain in a form contracts can read. Different oracle systems disagree mostly about how those three jobs should be done, and what tradeoffs are acceptable.
Once you see that, a lot of the surrounding design becomes easier to understand. Decentralization in oracle systems is not only about political ideals; it is a response to the fact that any single source, single operator, or single update path can fail or be manipulated. Time delays are not only inconvenient; sometimes they are deliberate safety margins. And “real-time” updates are not automatically better if they are easier to move with a flash loan or a thinly traded market.
How does a price oracle convert market data into an on‑chain value?
Mechanically, a price oracle takes market information from somewhere and turns it into a value a contract can read during execution. In Chainlink’s data-feed model, for example, smart contracts consume on-chain values stored by an aggregator contract, usually through a proxy contract so the underlying aggregator can be upgraded without breaking consumer integrations. The consumer typically reads through AggregatorV3Interface from the proxy rather than pointing directly at the current aggregator implementation. That detail matters because the oracle is not just “the number”; it is also the delivery path and upgrade surface.
On the input side, oracle networks often aggregate from many data sources and many node operators. Chainlink’s price-feed documentation describes feeds as data aggregated from many data sources by a decentralized set of independent node operators, while also noting that some feeds are exceptions and may rely on a single source or on calculated values. That caveat is important because developers often say “oracle” as if all feeds had the same trust model. They do not. A feed built from multiple independent venues and operators has a different failure profile from one derived from a single specialized source.
Other systems make different architectural choices. Pyth describes its core product as decentralized price feeds with deterministic on-chain delivery, supporting both pull and push update models across many chains. Band positions itself as a cross-chain data platform and exposes both request-based feeds and on-chain price-stream mechanisms. Compound’s Open Oracle takes another route: reporters sign key-value data off-chain, and users can post that signed data on-chain, with on-chain views able to aggregate multiple reports into something like a median. The shared pattern is recognizable even though the operational design differs: gather, attest, aggregate, publish.
How do oracle data sources affect price integrity and attack risk?
| Source type | Manipulation cost | Freshness | Best for |
|---|---|---|---|
| Single exchange spot | Low for illiquid assets | Immediate | Highly liquid assets only |
| Multi-exchange median | Higher (must corrupt many) | Near-real-time | General DeFi and lending |
| AMM TWAP | Higher over window | Time-averaged (lagging) | On-chain native pricing |
| Index / provider | Varies by methodology | Often delayed or batched | Benchmarks and reference rates |
A price oracle is only as meaningful as the market process behind it. If the underlying source is easy to move, then the oracle can faithfully report a manipulated market. That is one of the most common misunderstandings in DeFi: people say “the oracle failed” when the more exact statement is often “the oracle accurately reflected a market that was itself temporarily distorted.”
Consider a token with shallow liquidity. If an attacker can push its price sharply upward on the venues an oracle watches, then a protocol that uses that oracle may overvalue the attacker’s collateral. The CFTC’s complaint about the Mango Markets exploit describes exactly this kind of mechanism: Mango used an oracle that pulled prices from three exchanges and averaged them; because MNGO was relatively illiquid, large purchases on those exchanges moved the quoted spot price enough to inflate the oracle-reported value, which in turn inflated the attacker’s collateral and enabled large withdrawals. The lesson is not merely “averages are bad.” The deeper lesson is that an oracle inherits the market microstructure of its sources.
This is also why many protocols prefer reference prices derived from multiple venues rather than a single exchange, and why they may use medians instead of simple averages. A median does not make manipulation impossible, but it changes the attack surface: an attacker now needs to corrupt enough sources or enough reporters that the middle value moves materially. Maker’s Oracle Module is a clear example of this philosophy. Its Median contract computes a reference price from a governance-controlled whitelist of authorized feeders, and it requires at least a minimum number of valid prices before accepting a new median. The protocol then does something even more revealing: it does not feed that value directly into the core system.
How do protocols trade off oracle speed versus safety?
| Update speed | Manipulation resistance | Human response window | Best for |
|---|---|---|---|
| Immediate (per-trade) | Low (easy to move) | No buffer | Low-latency trading, market-making |
| Conditional updates (deviation/heartbeat) | Medium (thresholds help) | Small buffer | General DeFi price feeds |
| Delayed (OSM / long TWAP) | Higher (time to respond) | Allows manual response | Conservative lending, long-term collateral |
Maker inserts an Oracle Security Module, or OSM, between the medianized reference price and the rest of the protocol. The OSM intentionally delays price updates before the system acts on them, commonly by an hour according to the documentation. At first glance this seems absurd. If markets move quickly, why would a lending system want old prices?
Because the protocol is not optimizing for “most current number” in isolation. It is optimizing for survivable decision-making under adversarial conditions.
If a sudden bad price appears the delay creates time for humans or automated agents to respond before the price is used for collateral valuation and liquidation logic.
- whether from manipulation
- an operational mistake
- a compromised source
Here is the mechanism: the Median computes a current reference value, the OSM queues it, and only after the delay does that queued value become the system-facing price read by the Spotter and ultimately the core accounting contracts. The price is less fresh, but the protocol gains a buffer against abrupt oracle shocks.
That tradeoff is not universal. A fast derivatives venue may need much more responsive prices than Maker can tolerate. A liquidation engine for highly volatile assets may become unsafe if the delay is too long. So there is no single correct oracle latency. There is only a matching problem between the oracle’s update behavior and the application’s risk model.
This point shows up in Chainlink’s documentation in a different form. Chainlink Data Feeds are not streaming prices. They update when the value moves past a configured deviation threshold or when a heartbeat period elapses. That means a feed can be perfectly healthy and still not update for some time if the market has not moved enough; or, depending on configuration, even for hours. As a result, developers are told to monitor timestamps and implement their own freshness checks and circuit breakers. The oracle gives you a value, but your protocol still needs a policy for when that value is acceptable to act on.
How do oracles determine collateral valuation in a lending market?
Suppose a lending protocol lets a user deposit wrapped bitcoin and borrow a dollar-denominated stablecoin. The protocol needs to know how many dollars the posted collateral is worth so it can decide the user’s borrowing limit and whether the position should be liquidated.
Imagine the user deposits 1 unit of collateral. On-chain, the contract can verify that deposit precisely. What it cannot verify natively is the collateral’s dollar value. So it queries a price feed. If the feed returns 60,000, the protocol may treat the collateral as worth 60,000 dollars and allow, say, up to 45,000 dollars of borrowing under its chosen collateral ratio. If the market later falls and the oracle updates to 50,000, the contract can recompute the position’s health and decide whether liquidation is needed.
Now notice what is hidden inside that apparently simple process. The number 60,000 might come from a decentralized oracle network in which multiple node operators fetched data from multiple exchanges, aggregated the observations off-chain, reached a report, and posted the result on-chain to an aggregator contract. Or it might come from a protocol-specific median across designated reporters. Or it might come from an on-chain time-weighted average built from decentralized exchange pools. The lending market does not care about these details in the same way a user interface does not care how electricity is generated. But economically, those details determine whether the protocol can survive stress.
If the oracle is stale, the user may borrow too much against collateral whose market value has already fallen. If the oracle can be manipulated upward for a few blocks, an attacker may post overvalued collateral, borrow real assets, and leave the protocol with bad debt when the price snaps back. If the oracle is too delayed, healthy users may be liquidated too late or too early relative to current conditions. So the oracle is not peripheral infrastructure. It is part of the lending protocol’s balance sheet logic.
Why do oracles aggregate off‑chain before publishing on‑chain?
A naive oracle design would have every data provider post every observation directly on-chain, and then have a contract aggregate them. That is simple to describe but often expensive and slow. It also places more of the communication burden on the chain itself.
A common improvement is to aggregate reports off-chain and publish only the resulting report on-chain. Chainlink’s Off-Chain Reporting, or OCR, is a good example. OCR aggregates oracle reports off-chain and transmits an attested report to the relying contract. The point is not only lower gas cost. By coordinating off-chain first, the oracle network can reduce the number of on-chain transactions needed to keep a feed current while still producing a report with explicit correctness guarantees around the aggregated result.
This pattern helps explain a broader architectural shift toward oracle networks rather than isolated oracle nodes. In the Chainlink 2.0 framing, decentralized oracle networks, or DONs, are committee-operated networks that support oracle functions as a blockchain-agnostic service layer. One implication is that a single oracle network can serve multiple chains with the same feed logic. That matters because the problem “what is the price of this asset?” is not unique to one blockchain. Lending markets, derivatives platforms, and margin systems across Ethereum, Solana, Starknet, Aptos, and others all need some version of the same answer.
Band’s threshold-signature approach highlights a related idea from a different angle. If a group can jointly produce a threshold signature without any one member holding the full private key, then downstream chains or applications can verify a compact cryptographic attestation from the oracle group rather than checking many individual signatures. The mechanism differs from OCR, but the architectural goal is similar: compress many participants’ agreement into something efficient enough to consume on-chain.
When can on‑chain markets (TWAPs) safely serve as price oracles?
Not every price oracle depends on off-chain reporters or external exchanges. Some are built from on-chain markets. The usual example is an AMM-based oracle, especially a time-weighted average price, or TWAP.
Here the insight is straightforward. An AMM pool already contains a continuously updating exchange rate implied by its reserves or tick state. A protocol can sample that price over time and compute an average rather than trusting a single instantaneous spot price. Uniswap’s oracle libraries show the mechanics. In V2-style designs, cumulative prices are tracked over time and consumers derive an average from the change in cumulative price divided by elapsed time. In V3-style designs, helper functions can compute a time-weighted mean tick and derive a quote from that tick over a specified lookback window.
Why time-average? Because instantaneous AMM prices can be moved sharply within one transaction or one block if the pool is not deep enough. Averaging over a longer window means the attacker must hold the distorted price for longer or spend more capital to sustain the manipulation. That raises cost and can make some attacks impractical.
But the protection is not absolute. A TWAP is still built from market states that can be influenced. Its safety depends on the lookback window, pool liquidity, the surrounding protocol logic, and whether the asset is thinly traded. A short-window TWAP may barely help. A long-window TWAP may lag reality too much for volatile assets. And if a protocol treats an AMM spot price as if it were a robust oracle, it may be catastrophically wrong. This is why the distinction in the taxonomy between a general AMM price and a dedicated price oracle matters: a pool’s current swap ratio is a market state, not automatically a safe reference price.
What hidden attributes and checks do developers need when using price feeds?
The easiest mistake is to treat a price oracle as if it were a single scalar with no context. In practice, every useful oracle value has at least three hidden attributes: where it came from, when it was updated, and under what rule it was aggregated.
That is why Chainlink’s docs emphasize reading through the proxy, checking timestamps such as updatedAt, and not relying on deprecated bounds like minAnswer and maxAnswer to protect the application. Those values often do not stop your contract from reading a bad or stale answer. The application must impose its own sanity bounds and operational monitoring.
The same general lesson applies across oracle designs. If you consume a Band cross-chain feed, you need to understand what its threshold signature attests to and what it does not. If you consume a Pyth feed, low latency and deterministic delivery matter, but so do the feed’s confidence or uncertainty semantics where provided in the deeper integration docs. If you use a protocol-specific median, you need to know who the reporters are and how they are governed. If you use an on-chain TWAP, you need to understand the liquidity and manipulation cost of the underlying pool.
In other words, there is no oracle without a threat model. The interface may give you a neat function call. The security comes from everything outside that function call.
What are common failure modes for price oracles?
| Failure mode | Symptom | Cause | Quick mitigation |
|---|---|---|---|
| Staleness | Old timestamp | Infrequent updates or delays | Reject stale values |
| Source manipulation | Sudden anomalous spike | Low liquidity or watched venues moved | Median/TWAP and circuit breakers |
| Governance / operator risk | Unexpected upgrade or owner action | Centralized keys or multisig exposure | Timelock, inspect owners |
| False precision | Too many decimals, misleading exactness | Aggregate approximation or rounding | Sanity bounds, expose uncertainty |
The simplest failure mode is staleness. The oracle does not update quickly enough, the market moves, and the protocol acts on old information. This is especially dangerous in volatile markets and during chain congestion, but it can also arise from design choices like heartbeats or delayed modules.
The second failure mode is source manipulation. If the oracle watches venues that are easy to move, or if the relevant asset is illiquid, the attacker may manipulate the observed market itself. The Mango case shows the pattern clearly for off-chain-source averaging. Many DeFi incidents have shown similar patterns for on-chain oracle manipulation, especially where protocols relied on pool spot prices or weak TWAP constructions.
The third failure mode is governance or operator risk. Oracle contracts can be upgradable. Feed parameters can be changed. Reporter sets can be reconfigured. Chainlink’s docs note that proxy and aggregator contracts have inspectable owner addresses, typically multisigs, and that this upgradability is a tradeoff between flexibility and collusion resistance. That does not mean the system is unsafe; it means the trust model includes operational governance, not only cryptography.
The fourth failure mode is false precision. A price like 1834.271945 looks exact, but the underlying process may be approximate, delayed, filtered, or sourced from venues with their own outages and distortions. Smart contracts must use discrete numbers, but protocol designers should resist the temptation to imagine those numbers as ground truth.
Why are price oracles critical infrastructure in DeFi?
Price oracles began as a bridge problem: how do you get market information onto a chain? They have become something larger. In modern DeFi, the oracle often determines who is solvent, who gets liquidated, how derivatives settle, and whether a protocol remains fully collateralized. That makes the oracle less like an external plugin and more like part of the protocol’s core state machine.
This is why so much engineering effort has gone into oracle-network decentralization, off-chain aggregation, threshold signatures, attested reports, delayed security modules, update-threshold logic, and even services aimed at related problems like front-running and order fairness. Once price feeds move enough value, every weakness around sourcing, ordering, and reporting becomes economically exploitable.
It also explains why price oracle designs vary so much across chains and applications. A lending protocol holding long-lived collateralized debt may rationally prefer slower, more conservative prices. A derivatives venue may prioritize low-latency updates. A cross-chain application may care most about compact verifiable delivery. An on-chain-only protocol may prefer a TWAP sourced from native liquidity it can inspect directly. These are not competing answers to one simple question. They are different solutions to different failure budgets.
Conclusion
A price oracle is a system that turns messy market information into an on-chain value smart contracts can trust enough to act on. Its job is not merely to fetch a number, but to decide which market information counts, how to aggregate it, when to update it, and how to make it available under adversarial conditions.
The memorable version is this: markets produce prices as a process; smart contracts need prices as a fact. A price oracle is the machinery that bridges that gap. If you understand that, you understand why oracle design is really about security, incentives, latency, and market structure; not just data delivery.
What should you understand before using this part of crypto infrastructure?
Before relying on a price oracle, understand its sources, freshness, and aggregation rule so you can judge how much risk a quoted value carries. On Cube Exchange, combine those checks with a clear execution plan: fund your account, confirm the market and order type that match the oracle characteristics, and place an order that protects you from stale or manipulable prices.
- Check the feed provenance and timestamp: look up the oracle or feed docs (Chainlink, Pyth, protocol median, or TWAP) and note the aggregation method and the latest updatedAt value.
- Set a freshness and sanity threshold for the asset (for example, reject quotes older than 5 minutes or outside a ±5% band) and enforce it before trading or depositing.
- Fund your Cube account with fiat or supported crypto and open the relevant market (e.g., BTC/USDC). Use a limit order for volatile or thinly traded assets; use a market order only when the feed is fresh and liquidity is deep.
- Enter the size and price, review estimated fees and slippage, and submit. If oracle uncertainty is high, reduce order size or add a stop-limit with a conservative trigger.
Frequently Asked Questions
Because an oracle reports whatever market process its sources expose: if those venues are thin or easy to move, the oracle will faithfully reflect a manipulated market rather than a “true” price. The article shows this inheritance of market microstructure and the Mango Markets case (CFTC complaint) is a concrete example where spot trades on watched exchanges inflated an averaged oracle price.
Maker’s Oracle Security Module (OSM) intentionally delays reference-price updates (commonly by about an hour) so humans or automated responders have time to react to sudden, possibly adversarial price moves; this trades freshness for survivable decision‑making and is not appropriate for low‑latency derivatives that need near‑real‑time quotes.
The article lists four common failure modes: staleness (updates too slow), source manipulation (watching markets that are easy to move), governance/operator risk (upgrades or privileged owners can change feeds), and false precision (numeric answers appear exact despite approximate sourcing).
Off‑Chain Reporting (OCR) aggregates many node observations off‑chain and posts an attested aggregate on‑chain, which lowers gas and the number of on‑chain transactions while preserving correctness guarantees around the reported aggregate; this is the pattern Chainlink promotes to make feeds efficient at scale.
AMM‑based oracles (TWAPs) can increase manipulation cost by averaging pool prices over a chosen lookback window, but their safety depends on window length, pool liquidity, and asset volatility - a short window or shallow pool gives little protection and a long window may lag reality too far for some applications.
Always check at least three hidden attributes: where the value came from (which sources/reporters), when it was updated (timestamps such as updatedAt), and how it was aggregated (median, average, TWAP, etc.); additionally, implement freshness checks, sanity bounds, and circuit breakers because aggregator fields like minAnswer/maxAnswer often do not prevent bad or stale reads by themselves.
Defenses include using multiple independent venues or reporters, choosing robust aggregation rules (medians or thresholded aggregates), using time‑weighted averages or longer lookbacks where appropriate, adding operational guards (freshness thresholds and circuit breakers), and - where helpful - delaying price effects (e.g., Maker’s OSM); none of these is foolproof and the right mix depends on the application’s risk model.
A feed may not update for hours because many data‑feed designs only write a new on‑chain answer when the value moves past a configured deviation threshold or when a heartbeat timeout elapses; Chainlink’s documentation explicitly warns consumers to monitor timestamps and heartbeats because healthy feeds can still be temporarily unchanged.
Related reading