What is a Hard Fork?
Learn what a hard fork is in blockchain, how incompatible consensus-rule changes split chains, and why hard forks differ from soft forks.
Introduction
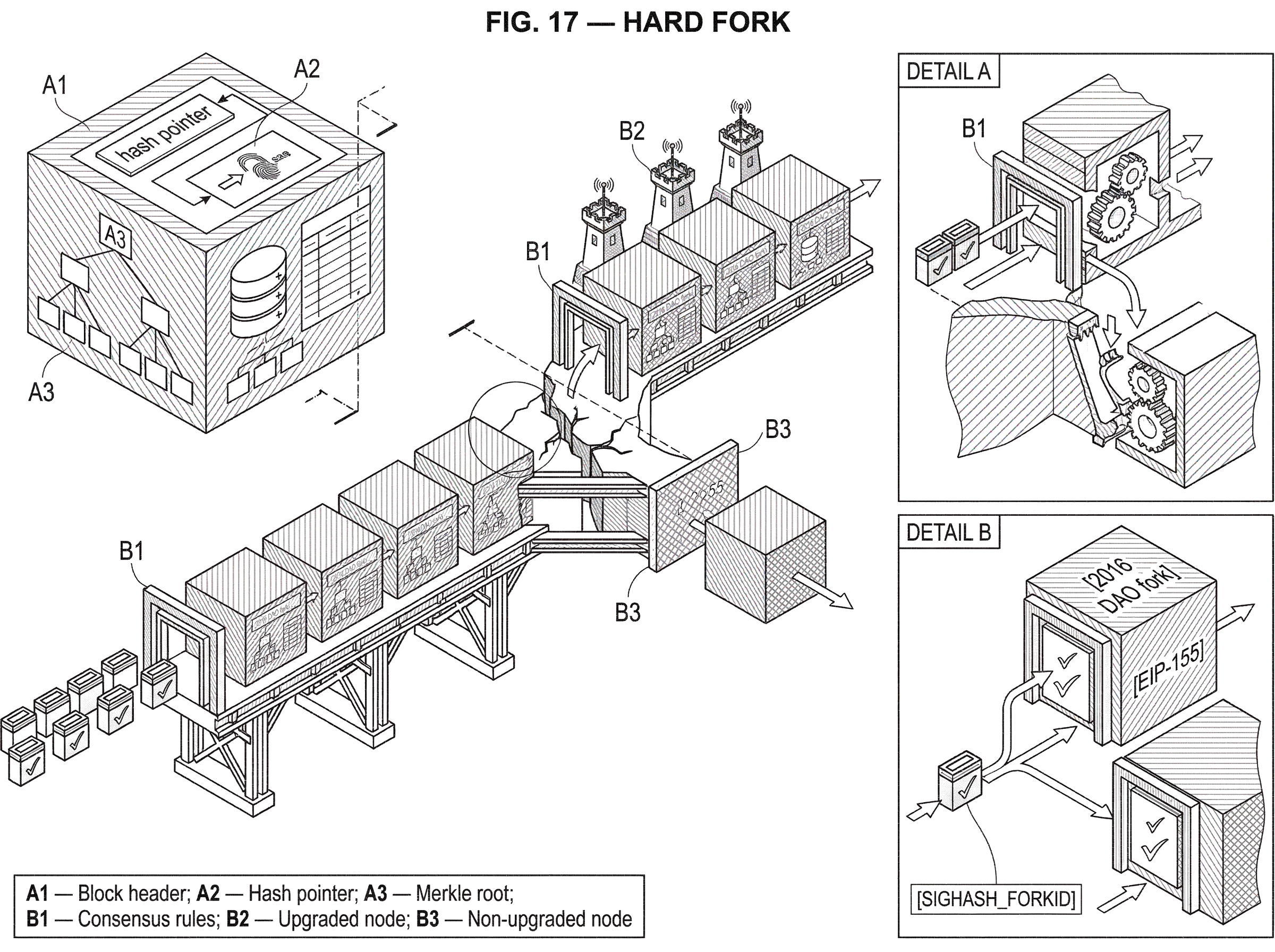
Hard fork is the name for a blockchain rule change that breaks backward compatibility. That sounds like a software engineering detail, but it reaches much deeper: a blockchain exists only because many independent nodes agree on which blocks are valid, so when the validation rules change incompatibly, agreement itself is at stake. The important question is not merely whether software changed, but whether old nodes and upgraded nodes still recognize the same ledger.
This is why the term carries so much weight. Some forks are ordinary and harmless, such as the brief split that happens when two miners produce blocks at nearly the same time. Those usually resolve once one branch accumulates more work or otherwise becomes the accepted chain. A hard fork is different. It changes the rules of validity, so the disagreement is not about which valid block arrived first, but about what even counts as a valid block in the first place.
If you remember one idea, remember this: a hard fork happens when the set of blocks accepted by upgraded nodes becomes larger or otherwise incompatible with the set accepted by non-upgraded nodes, so old software can no longer follow the upgraded chain. Everything else (chain splits, emergency upgrades, governance fights, replay protection, and new coins appearing) follows from that mechanism.
How do validation rules (not brand names) cause a hard fork?
A blockchain is often described as a chain of blocks, but that description is incomplete. The more useful view is that a blockchain is a network of nodes repeatedly applying a shared validation function: given a candidate block, does it satisfy the consensus rules? Those rules cover things like block format, transaction validity, and consensus-specific constraints.
Full nodes stay in sync because they enforce the same rules. If a block violates those rules, the node rejects it no matter who produced it. This is the source of the system’s credibility: users do not need to trust a central operator, because validation is local. Each node checks for itself.
A hard fork changes those consensus rules in a way that old nodes cannot accept. Bitcoin developer documentation defines a hard fork as a permanent divergence in the blockchain that commonly occurs when non-upgraded nodes cannot validate blocks created by upgraded nodes following newer consensus rules. That definition is precise because it focuses on the validation boundary. The fork is not the meeting, the announcement, or the software release. The fork is the moment incompatible rules start producing incompatible judgments.
Consider a simple example. Suppose an old chain says blocks larger than a certain limit are invalid. A new version of the protocol raises that limit. Upgraded nodes may now accept a larger block. Non-upgraded nodes will reject that same block as invalid. From that point on, if enough miners or validators follow the new rules, they can build a chain that old nodes refuse to recognize. Both groups may think they are following the real protocol. The disagreement is now structural.
That is why blockchains are conservative about rule changes. In an ordinary distributed system, a server upgrade can be rolled out unevenly while the service still works. In a blockchain, uneven rollout of consensus changes can create two incompatible realities.
How is a hard fork different from a temporary chain split?
The word fork is overloaded, and that creates confusion. In Bitcoin documentation, fork can refer to a temporary chain split at the same height, a hard fork, a soft fork, or even a software codebase split unrelated to consensus. These are not interchangeable.
An ordinary block fork happens when two blocks appear at the same height, often because miners found them almost simultaneously. Different nodes may see different tips for a short time. But if both blocks are valid under the same rules, the disagreement can be resolved by the chain-selection rule; for example, following the chain with the most accumulated proof-of-work. One branch eventually wins, and the other becomes stale.
A hard fork cannot be resolved that way if the two sides enforce incompatible rules. The reason is subtle but fundamental. Chain-selection rules only choose among blocks a node already considers valid. If old nodes reject new-rule blocks outright, they will never switch to that chain no matter how much work it contains. In Bitcoin Core, nodes can detect that something like this may be happening when they see headers showing substantially more proof-of-work than their best valid chain, yet still cannot accept the corresponding blocks under their own rules. That is a sign not of a routine reorganization, but of likely rule incompatibility.
This is also why block height is not enough to identify a block during a fork. Multiple blocks can share the same height. What matters is which exact block header hash a node is talking about and which rule set it applies when judging validity.
Hard fork vs soft fork: which changes are backward‑compatible?
| Fork type | Compatibility direction | Who must upgrade | Activation typical | Split risk |
|---|---|---|---|---|
| Soft fork | New valid set is subset | Miner majority often | Miner signalling or UASF | Lower if miner majority |
| Hard fork | New set incompatible with old | Wide node & service upgrades | Block-height or trigger | High without full coordination |
The cleanest way to understand a hard fork is by contrasting it with a soft fork. The difference is not political. It is about the direction of compatibility.
A soft fork makes previously valid blocks or transactions invalid. Old nodes still accept the new chain because the new chain remains inside the old validity envelope. Upgraded nodes have become stricter, but non-upgraded nodes are still permissive enough to treat the stricter chain as valid. Under the right conditions (in proof-of-work systems, usually enough miner support) the network can adopt the new rules without a permanent split.
A hard fork moves the other way. It allows blocks or state transitions that old nodes reject. Upgraded nodes may accept a block that non-upgraded nodes consider invalid. Once such blocks are produced, old nodes cannot follow. Backward compatibility is broken.
A compact way to say this is:
- In a soft fork, the new valid set is a subset of the old valid set.
- In a hard fork, the new valid set is not a subset of the old valid set.
That set-based view explains the operational difference. A soft fork can often be enforced by a majority of block producers because old nodes still recognize the resulting chain. A hard fork requires much broader coordination among nodes, wallets, exchanges, infrastructure providers, and often users, because old nodes do not merely lag behind; they become incompatible.
What steps occur when a hard fork activates on the network?
Mechanically, a hard fork usually activates at a specified block height, time, or comparable trigger. Before that activation point, upgraded and non-upgraded nodes may behave identically. At the activation point, upgraded nodes start enforcing the new rules. Non-upgraded nodes continue enforcing the old rules.
Now imagine a network upgrade scheduled for block X. Up to block X - 1, everyone agrees. At block X, an upgraded block producer creates a block that uses a feature or state transition allowed only under the new rules. Upgraded nodes accept it and build on it. Non-upgraded nodes reject it and keep waiting for a different block at the same height that satisfies the old rules.
From here, two paths are possible. If essentially everyone important has upgraded, the old chain quickly becomes irrelevant. Non-upgraded nodes are simply left behind on a minority view of the ledger. In practice, this can feel like an ordinary network upgrade, even though it is technically a hard fork.
If substantial economic or validator support remains on both sides, the fork becomes a persistent split. Each side continues extending its own chain, with its own idea of validity, and users may end up holding assets on both chains. This is the contentious case people usually have in mind when they hear the term.
The key point is that the chain split is a consequence, not the definition. The definition is incompatible validation. A visible split happens when enough participants continue operating under each incompatible rule set.
When and why does a protocol require a hard fork?
If hard forks are risky, why use them? Because some protocol changes simply cannot be expressed as backward-compatible restrictions.
Bitcoin developer documentation gives a straightforward example: increasing the maximum allowed block size above an existing limit requires a hard fork. Old nodes treat oversized blocks as invalid. There is no clever coordination trick that makes them reinterpret those blocks as valid without upgrading the rule set they enforce.
The same logic applies more broadly. A network might use a hard fork to add new transaction or block capabilities, alter state-transition rules, change gas accounting, replace part of the consensus mechanism, or perform a targeted state change that old clients would never infer on their own. Ethereum’s major network upgrades are examples of forks in this broader sense: changes to protocol rules that introduce planned technical upgrades. Some are routine and broadly accepted; others are contentious.
The Ethereum Paris upgrade, better known as The Merge, is a particularly clear example of why hard forks matter. It switched Ethereum’s execution layer from proof-of-work-related assumptions to accepting instructions from the proof-of-stake consensus layer through the Engine API. That is not a cosmetic patch. It changes what kind of chain the software is willing to follow.
At the opposite end, some forks are maintenance-oriented rather than feature-rich. Ethereum’s Glacier upgrades, for example, were used to delay the difficulty bomb. That illustrates an important point: the mechanism of a hard fork is about compatibility, not ambition. A tiny parameter change can still require a hard fork if old nodes would reject the result.
How did the DAO hard fork lead to Ethereum and Ethereum Classic splitting?
The 2016 DAO fork is useful because it shows both the technical and social sides of a hard fork.
After the DAO exploit, part of the Ethereum community wanted the protocol to intervene and move the affected ether into a recovery contract. The proposed fork specified an exact state change at a designated block: ether held by a defined list of DAO-related accounts would be transferred into a recovery contract from which DAO token holders could withdraw according to fixed rules. This was not merely an application-level patch. It was a rule-driven change to the chain’s state that old clients would not produce by themselves.
So what happened mechanically? Upgraded clients recognized the designated fork block and applied the new state transition. Non-upgraded clients did not. From that block onward, the two groups no longer agreed on the state root and therefore no longer agreed on the canonical chain. The result was a permanent split: the upgraded chain continued as Ethereum, while dissenting miners and users continued the old chain, which became Ethereum Classic.
This example matters because it dispels two common misunderstandings. First, a hard fork is not only about changing abstract limits or fee formulas; it can directly alter state. Second, the real boundary is not whether a decision was voted on, but whether all nodes enforce the same post-fork validity conditions. Community support affects which chain survives economically, but consensus software determines whether the chains are compatible.
What are replay attacks after a hard fork and how are they prevented?
| Method | How it ties to chain | When applied | Replay risk | Example |
|---|---|---|---|---|
| No protection | Signatures omit chain identity | Legacy or unmodified clients | High; replays possible | Contentious forks without protection |
| EIP-155 (chain id) | Chain ID included in signing hash | Ethereum hard forks (post‑EIP-155) | Reduces replay risk if adopted | Spurious Dragon / EIP-155 |
| SIGHASHFORKID | Fork id embedded in sighash type | UAHF / Bitcoin Cash-style forks | Reduces replay risk if enforced | Bitcoin Cash UAHF |
Once a hard fork produces two live chains with shared history, a new danger appears: replay attacks. If the two chains use the same transaction format and signing rules, a transaction signed for one chain may also be valid on the other. A user trying to spend funds on chain A may unintentionally authorize the same spend on chain B.
This is not a theoretical nuisance. Community safety guidance around contentious forks has warned that when replay protection is weak or absent, transactions on one chain can often be replicated on the other. That makes routine wallet activity dangerous during and after a split.
The mechanism is simple. A digital signature proves authorization over some message. If both chains consider the same signed message valid, then broadcasting it on either chain can produce the same effect. To prevent that, the signed message must commit to chain identity.
Ethereum’s EIP-155 is a clean example of this design. It adds a chainid into the transaction signing hash and changes signature recovery behavior so a transaction is tied to a specific chain. The important idea is not the exact encoding formula, but the invariant: the signature should include enough context that it is valid only on the intended chain. After a contentious split, that can be the difference between orderly coexistence and user confusion.
Bitcoin Cash introduced an analogous protection through SIGHASH_FORKID, which modifies the digest used for signatures so transactions on different forks produce different signature commitments. Again, the principle is the same even though the implementation differs: a post-fork chain often needs a distinct signing domain.
This is one reason contentious hard forks are operationally expensive. It is not enough to write the new consensus rule. Wallets, exchanges, signers, and custody systems must understand how to keep user actions from leaking across chains.
How does governance interact with hard-fork mechanics?
It is tempting to describe governance as a social layer floating above the technical one. In practice, hard forks show that the two are intertwined.
A blockchain protocol has no central switch that compels everyone to upgrade. Developers can publish code, but nodes choose whether to run it. Miners or validators can signal support, but economic actors decide which chain they treat as valuable. Wallets and exchanges choose naming, deposits, withdrawal policies, and confirmation rules. A hard fork succeeds smoothly only when enough of these actors coordinate around the same transition.
That is why official Ethereum writing about the DAO fork described it as a delicate decision that could not be made by any single entity. The chain split did not happen because someone declared it so. It happened because different groups made different software and legitimacy choices, and those choices were strong enough to sustain two networks.
The Bitcoin ecosystem has seen the same coordination problem from a different angle. During the period leading up to the planned SegWit2x fork, user guidance warned that businesses, miners, and wallets might not align on what to call “Bitcoin,” and that some mobile wallets might blindly follow the longest chain seen from miners rather than the chain users intended to hold. That warning captures an uncomfortable truth: a hard fork is partly a consensus problem and partly a naming problem. Software determines what is valid; markets and institutions determine what is recognized, listed, and trusted.
This is also where neighboring architectures matter. Some systems aim to reduce reliance on disruptive hard forks by moving more upgrade logic on-chain. Polkadot’s OpenGov and Substrate runtime upgrade machinery are examples of a design philosophy in which many changes can be enacted through runtime upgrades rather than through classic off-chain coordination over incompatible client versions. That does not mean incompatibility disappears in all cases, but it shifts where upgrade authority and execution live. The contrast helps clarify what a traditional hard fork is solving: a network needs a way to change shared rules, and if the architecture cannot express that change within existing compatibility boundaries, operator coordination does the work.
What should node operators and users do before, during, and after a hard fork?
| Actor | Main risk | Recommended immediate action | Consequence if ignored |
|---|---|---|---|
| Node operators | Following an incompatible chain | Upgrade client and verify fork rules | Remain on minority chain |
| Users | Duplicated balances and replay risk | Use updated wallets and pause trades | Funds confusion or loss |
| Infrastructure providers | Service outages and mislabelled assets | Coordinate upgrades and enable replay protection | Service disruptions and customer harm |
For node operators, the core risk is straightforward: a non-upgraded node can become confidently wrong. It may continue following a chain that the upgraded majority no longer recognizes. It may relay or accept transactions that upgraded nodes consider invalid. Bitcoin developer guidance explicitly warns that information from nodes not using the current consensus rules should not be relied upon, because they may be following an incompatible chain.
For users, the risk is usually indirect but very real. Wallet balances may appear inconsistent across services. Deposits may be paused. Exchanges may require more confirmations or suspend trading. If two chains survive, users may need careful procedures to separate or “split” coins before spending. If replay protection is weak, spending on one chain can affect the other.
For infrastructure providers, the challenge is broader than flipping an upgrade switch. They need to know which client version they run, which fork rules it enforces, how it detects incompatible chains, what naming conventions they will use if a split persists, and whether their transaction pipelines include chain-specific replay safeguards.
What problems can a hard fork not fix?
A hard fork can change rules, but it cannot force legitimacy, security, or adoption.
It cannot force dissenters to disappear; they may continue the old chain. It cannot by itself fix weak security assumptions; a minority chain may become easier to attack after a split, as the history of Ethereum Classic’s later 51% attacks illustrates. And it cannot erase operational complexity; even a technically successful fork can create confusion for wallets, applications, and markets.
This is why the phrase contentious hard fork matters. The technical recipe may be deterministic, but the outcome depends on whether enough participants converge on one chain. When they do not, the fork becomes not just an upgrade but a secession.
Conclusion
A hard fork is a backward-incompatible change to blockchain consensus rules. The essence is simple: upgraded nodes accept blocks or state transitions that old nodes reject, so old software can no longer follow the upgraded chain.
From that mechanism flow the big consequences: coordinated upgrades when everyone moves together, permanent chain splits when they do not, and post-fork hazards like replay attacks when both chains survive. If you keep in view that a blockchain is defined by locally enforced validation rules, not by a logo or a community slogan, hard forks stop looking mysterious. They are the price a decentralized system pays when it needs to change rules that old participants cannot interpret the same way.
What should I check before trading or transferring during a hard fork?
Before trading, depositing, or withdrawing around a scheduled or contentious hard fork, confirm how the upgrade affects transaction validity, replay protection, and exchange handling. On Cube Exchange you can run the same readiness checks and then fund, trade, or withdraw using conservative execution settings to reduce accidental losses during the transition.
Frequently Asked Questions
A hard fork is a backward‑incompatible change to the consensus rules so upgraded nodes may accept blocks that old nodes reject; a temporary block split (two valid blocks at the same height) is resolved by chain-selection because both blocks are valid under the same rules.
Because a hard fork enlarges or changes the set of blocks considered valid, old nodes cannot follow the upgraded chain no matter how much work it accumulates, so successful activation requires coordinated upgrades across nodes, miners/validators, wallets, exchanges and other infrastructure rather than just miner majority.
A replay attack happens when two live chains share the same transaction format and a signature is valid on both chains, so a transaction broadcast on one chain can be replayed on the other; preventing this requires signing schemes that commit to chain identity (for example, EIP‑155’s chainid or Bitcoin Cash’s SIGHASH_FORKID).
No: a hard fork changes rules but cannot force economic legitimacy or adoption - dissenters can continue the old chain and markets, wallets, and exchanges ultimately influence which chain users treat as the canonical asset.
Nodes can detect likely hard‑fork conditions when they see headers with substantially more proof-of-work than their best valid chain but cannot validate the corresponding blocks; Bitcoin Core also exposes fork warnings via getnetworkinfo and can notify operators with -alertnotify.
When both chains remain live, there is no automatic technical arbiter; social and economic actors - exchanges, wallets, custodians, node operators and users - decide which chain to list, name, and treat as valuable, and those choices determine practical legitimacy.
Infrastructure providers should plan for chain‑specific handling: identify which client and rules they run, halt or delay deposits and withdrawals during the transition if needed, implement replay protection in signing and transaction pipelines, and communicate naming/confirmation policies to users to avoid confusion.
Chain‑ID style schemes bind the signature to a specific chain by including a chain identifier (or fork‑specific digest) in the transaction signing hash, so the same signed message is invalid on the other chain; EIP‑155 (Ethereum) and SIGHASH_FORKID/BCH approaches (Bitcoin Cash) implement this principle differently.
On‑chain runtime upgrade systems (e.g., Substrate/Polkadot’s runtime upgrades or OpenGov) can move many changes into mechanisms that avoid off‑chain client coordination, but they do not universally eliminate incompatibility - some consensus‑level or non‑expressible rule changes can still require hard forks.
Related reading