What Is a Full Node?
Learn what a full node is, why it exists, how it validates blocks and transactions, and how it differs from light clients, validators, and RPC providers.
Introduction
Full node is the name for software that independently checks whether a blockchain’s transactions and blocks follow the protocol’s rules. That sounds almost administrative, but it is one of the few ideas in crypto that directly answers a deep question: when the network says something is true, who actually verifies it?
A blockchain is often described as a shared ledger. The important part is not that many people can read it. The important part is that many machines can reject invalid updates to it. A full node exists for that reason. It does not merely store data or forward messages. It enforces the rules locally, on its own hardware, without needing to trust a remote service to tell it which chain is valid.
That independence is why full nodes matter to ordinary users, developers, businesses, and the network as a whole. If you rely on someone else’s node, you may still be able to read balances or broadcast transactions, but you are outsourcing correctness, availability, and often privacy. Running a full node is the opposite choice: more resource cost in exchange for direct verification.
What does a full node actually do?
| Node type | Verification | Data downloaded | Trust required | Resource cost | Best for |
|---|---|---|---|---|---|
| Full node | Full local validation | All blocks or state | Trustless (self) | High (CPU, disk, bandwidth) | Sovereignty, privacy |
| Light client | Headers or proofs | Block headers + proofs | Some assumptions | Low | Mobile wallets, low resources |
| RPC provider | Provider-verified | Service snapshots | Must trust provider | Minimal local | Quick apps, low maintenance |
The shortest useful definition comes from Bitcoin’s operator documentation: a full node is a program that fully validates transactions and blocks. NIST’s glossary describes the same idea from another angle: a full node stores blockchain data, passes it to other nodes, and ensures newly added blocks are valid and authentic.
The key word is fully. A blockchain is only as trustworthy as the process that decides whether a proposed block is acceptable. Full nodes perform that decision process themselves. They check the chain’s data against consensus rules such as transaction format, signatures, spending conditions, block structure, and whatever additional state-transition rules the protocol requires. If a block breaks the rules, a full node rejects it even if many peers sent it, even if a miner produced it, and even if a popular service says it is fine.
This is the central mechanism behind decentralization. Decentralization is not mainly about there being many copies of data. It is about there being many independent verifiers with the power to say no. If everyone merely mirrored whatever the biggest provider served, the system would look distributed but behave trustfully.
A useful contrast is a light client. A light client usually downloads much less data and asks full nodes for proofs or answers. That can be efficient and sometimes very secure, depending on the design, but it changes the trust model. The full node is the place where the expensive work of universal rule-checking happens.
Why do full nodes follow the rule 'do not trust, verify locally'?
To see why full nodes exist, it helps to focus on the invariant they protect. A blockchain changes over time: new transactions arrive, new blocks are proposed, temporary forks appear, and the visible head of the chain moves forward. What must not change is the rule set that determines which updates are valid.
A full node preserves that invariant by replaying the protocol’s logic locally. It does not ask, “Did an important participant accept this block?” It asks, “If I execute the rules myself, does this block produce a valid next state?” That is a much stronger standard because it turns consensus from social trust into reproducible computation.
This is why full nodes are valuable even when they are not mining, validating, or staking. They may not be the machines producing new blocks, but they are still the machines judging whether produced blocks count. In that sense, block producers propose and full nodes dispose.
That distinction becomes especially important when people casually treat all chains as if they work like Bitcoin. On Bitcoin, the same software stack often handles transaction validation, block validation, storage, and peer-to-peer relay in one package. On Ethereum today, those responsibilities are split. After the move to proof of stake, an Ethereum full node requires both an execution client and a consensus client working together. The execution client handles transaction processing, state management, and the EVM. The consensus client handles block and attestation gossip, fork choice, and staying aligned with the canonical chain. The principle is the same, but the architecture is not.
What happens step-by-step when a full node receives a new block?
Imagine your node is connected to peers and a new block appears on the network. From the outside, it may look like the node simply “receives the latest block.” Mechanically, much more is happening.
First, the node learns about the block from peers on its peer-to-peer network. In Bitcoin, full nodes typically accept blocks and transactions from peers, validate them, and relay valid ones onward. In Ethereum, the consensus client learns about new blocks over its own peer network, while the execution client handles the execution payload and transaction validity. Different architecture, same underlying job: a peer says, in effect, here is the next proposed update.
Then the node begins checking. It confirms the block fits into a valid chain history from its point of view. It verifies that the block’s structure is correct, that its transactions are well-formed, and that each transaction obeys the protocol’s spending or execution rules. On an account-based smart-contract chain, this includes re-executing transactions to ensure the claimed state transition is correct. On a UTXO-based chain, this includes checking that inputs exist, are authorized, and are not double-spent.
Only after those checks pass does the node treat the block as acceptable. If the block is valid and extends the chain the node considers best under the protocol’s fork-choice rules, the node updates its local view of chain state. If the block is invalid, the node rejects it. If it is valid but belongs to a competing branch, the node may keep it temporarily while waiting to see which branch the protocol tells it to follow.
The important point is that this process is local. The node is not outsourcing judgment. Peers provide candidate data. The node provides the verdict.
What other jobs do full nodes perform besides validation?
In practice, most full nodes perform three closely connected jobs: they validate, they store, and they relay. These are related, but they are not equally fundamental.
Validation is fundamental because it is the thing that makes the node sovereign. Storage follows because the node needs enough historical data and current state to validate future updates correctly. Relay follows because peer-to-peer networks need participants to share valid transactions and blocks with one another.
This ordering matters because people sometimes define a full node by secondary behavior. For example, many nodes expose RPC endpoints so wallets, exchanges, indexers, or apps can query balances and submit transactions. That is useful, but it is not the essence of a full node. Likewise, many full nodes help lightweight clients by broadcasting their transactions or notifying them about relevant activity. Bitcoin’s documentation explicitly notes that if not enough nodes do this, lightweight clients are pushed toward centralized services. Still, those service functions depend on the deeper fact that the node has already validated the chain for itself.
A full node can therefore be understood as a private court of first instance for blockchain truth, with optional public-service roles layered on top.
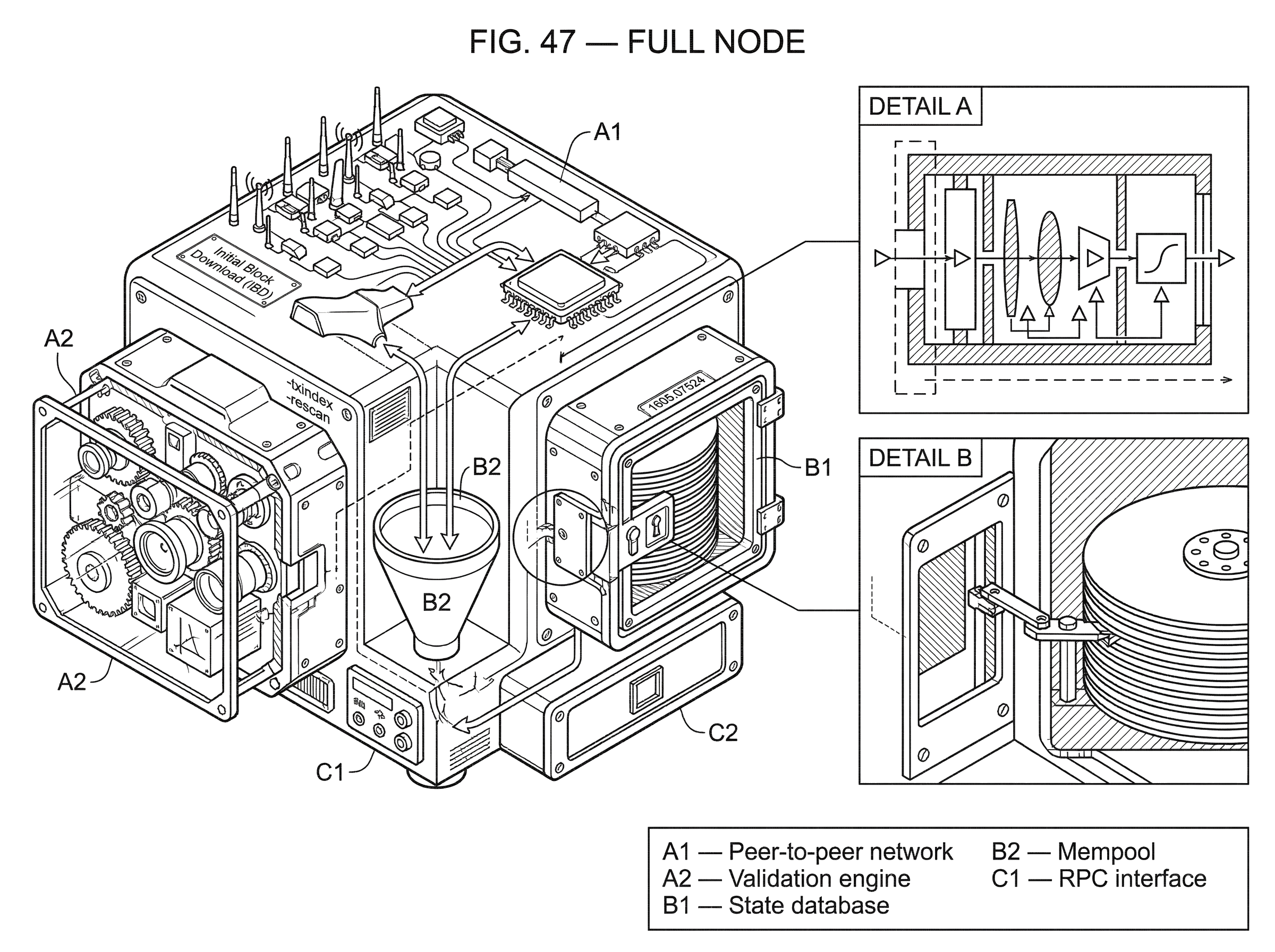
Why does syncing a new full node take so long (IBD and sync modes)?
The first hard reality of full nodes is that independent verification is not cheap. If a new node wants to trust no one, it cannot simply ask for the latest balance snapshot and call it done. It has to acquire enough chain data to verify that the current state was reached legitimately.
On Bitcoin, this process is called Initial Block Download, or IBD. A new node downloads blocks it does not yet have and verifies them. During IBD, Bitcoin Core documentation notes that the node does not accept incoming transactions and does not request mempool transactions. That tells you something important about priorities: before a node can participate fully in the live network, it must first establish confidence in the history leading to the current tip.
Other chains have analogous synchronization processes, though the details differ. Ethereum clients offer multiple sync modes, and the hardware bottleneck is often disk space and I/O rather than just raw CPU. Polkadot documentation similarly warns that syncing a full node can take many hours, with duration depending on machine capacity, disk speed, RAM, and network conditions. Across architectures, the pattern is the same: local verification requires local work.
This is the tradeoff at the heart of full nodes. They reduce trust assumptions by increasing resource demands. There is no magic around this. If you want the right to verify everything yourself, your machine must actually perform verification.
Does a full node have to store the entire blockchain history?
| Node type | Keeps history | Validates fully | Disk need | Historical queries |
|---|---|---|---|---|
| Archive | All historical state | Yes | Very high (TB+) | Full history queries |
| Pruned | Recent state only | Yes | Low (GBs) | Limited or none |
| Full + txindex | Recent + indexed txs | Yes | Medium–high | Address/tx lookup |
A common misunderstanding is that a full node must always store every historical detail forever. That is not universally true.
The concept of a full node is about full validation, not necessarily permanent retention of every historical byte. Some full nodes are archival: they keep extensive historical chain data and can answer deep historical queries. Others are pruned: they validate all blocks as they arrive, but after validation they discard older raw block data that is no longer needed for their configured purpose.
Bitcoin Core’s pruned mode is a clear example. The documentation says pruning can reduce disk usage substantially, but it comes with consequences: pruning is incompatible with -txindex and -rescan, and it disables the RPC importwallet. That tradeoff shows what is fundamental and what is optional. Full validation remains intact. Broad historical query capability is reduced.
The same pattern appears on other chains under different names. Polkadot distinguishes pruned, archive, and light nodes. Ethereum distinguishes full-node and archive-style behaviors with sharply different storage requirements. The architecture changes, but the underlying tradeoff does not: retaining more history makes the node more useful for some workloads, while pruning reduces cost.
So when someone says “run a full node,” the right follow-up question is often not does it validate fully? but what data does it retain after validation?
Full node vs validator: what’s the difference?
Another common confusion is to treat “full node” and “validator” as synonyms. Sometimes a validator runs a full node, but the concepts answer different questions.
A full node answers: does this machine independently verify the chain’s rules? A validator answers: does this machine participate in block production or consensus voting? Depending on the protocol, one may require the other, but they are not identical roles.
Bitcoin makes the distinction relatively intuitive because miners produce blocks, while ordinary full nodes validate them. Ethereum makes it explicit in software architecture: after the Merge, a trustless node requires both execution and consensus clients, but a consensus client does not become a block proposer or attester unless paired with validator functionality and the required stake. Cosmos documentation similarly separates running a full node from running a validator node. Solana/Agave documentation also distinguishes validator operation from RPC-node-style roles.
This distinction matters because the social power of full nodes is often underestimated. Even when they are not producing blocks, they are still enforcing the admissibility conditions for the chain they will accept. A validator can propose something; a full node can still reject it.
Why do users and businesses run full nodes?
Some people run full nodes for ideology, but most real-world uses are more concrete than that.
A self-custodial user may run a full node so their wallet does not reveal every query to a third-party provider. A company may run one so it can broadcast transactions, monitor confirmations, and query chain state without depending on a commercial RPC service. A developer may need one to test software against a locally trusted chain view. An exchange or custody platform may need several for redundancy, policy checks, and operational control. On Polkadot, the docs describe direct interaction, enhanced privacy, and full control over RPC requests, transactions, and data queries as reasons to run your own node. That logic generalizes broadly.
The alternative is often some form of Node-as-a-Service or public RPC. That can be practical and entirely sensible for many applications, but it changes the risk profile. The technical paper on blockchain access models makes the basic point cleanly: traditional RPC assumes a trusted server, and clients have no built-in way to verify many returned results. If the provider is down, stale, censoring, or compromised, your app inherits that problem.
Operational history shows this is not a theoretical concern. Provider status pages regularly report degraded performance, stale data, finalized-head stalls, cloud-region failures, and maintenance windows that affect node-backed services. That does not mean providers are bad; it means outsourcing node access creates a dependency. Running your own full node is how you remove or reduce that dependency.
How do reachable full nodes help the wider network?
A full node is valuable privately, but it also contributes publicly when it is reachable and willing to relay data.
Bitcoin’s full-node guide explains that most full nodes accept transactions and blocks from peers, validate them, and relay them onward. It also notes that accepting inbound connections is necessary if you want to support lightweight clients and other nodes. This is one reason home-node guides talk so much about bandwidth, uptime, port configuration, and connection counts: a node that is only partially reachable is still useful to its operator, but less useful to the network.
That said, public usefulness creates cost. More peers mean more bandwidth and more surface area. Bitcoin Core offers modes such as blocks-only operation and upload limiting precisely because operators may need to trade public service against ISP caps or hardware limits. Ethereum operator guidance similarly warns against casually exposing RPC endpoints to the public internet, because doing so can let strangers control or overload the node. The recurring pattern is simple: every interface that makes a node more useful to others also requires more careful operation.
What risks and attacks should I consider when running a full node?
| Failure mode | Cause | Impact | Mitigation |
|---|---|---|---|
| Eclipse attack | Peer monopolization | Filtered view; double-spends | Diversify peers; feelers; anchors |
| Routing hijack | BGP interception | Delayed or dropped blocks | Multi-homing; BGP monitoring |
| Operational failure | Disk / I/O / bad upgrade | Downtime; stale data | Backups; monitoring; sizing |
The clean mental picture of a full node is “a machine that independently verifies the chain.” In production, that machine still sits inside messy real networks.
One class of failure is isolation. Eclipse attacks on Bitcoin showed that if an attacker monopolizes a victim node’s peer connections, the attacker can filter the victim’s view of the network. That isolation can then enable downstream attacks such as double-spends, selfish-mining advantages, or adversarial forks from the victim’s point of view. The mechanism exploited peer-selection and address-management behavior rather than breaking cryptography. That is a good reminder that node security depends not only on consensus rules but also on network plumbing.
Another class of failure is routing interference. Research on Bitcoin routing attacks showed that Internet routing manipulation, including BGP hijacks, can intercept or disrupt blockchain traffic and meaningfully affect propagation. Here the full node may be validating correctly, but its connectivity to the wider network is being distorted. A correct verifier with a distorted input stream is still vulnerable.
A third class is the ordinary operational burden of running stateful infrastructure: disk exhaustion, slow I/O, stale data, bad upgrades, overloaded RPC endpoints, antivirus false positives, cloud outages, and misconfigured firewalls. These are mundane problems, but they shape whether people can realistically run nodes at all. In practice, decentralization depends as much on operational accessibility as on consensus theory.
When should I prefer a full node over hosted RPC or a light client?
If the goal is to interact with a blockchain while minimizing trust in intermediaries, the full node remains the clearest baseline. It gives you your own copy of the relevant data, your own execution of the protocol’s rules, and your own direct connection to the peer network or client stack.
That does not make full nodes the right answer for every user or every product. They cost storage, bandwidth, maintenance time, and sometimes meaningful hardware budget. Some chains require multiple cooperating clients. Some workloads require archive-style retention that becomes expensive quickly. And many users will reasonably choose light clients or managed RPC instead.
But those alternatives are best understood relative to the full node standard. The full node is the reference point because it is the place where verification is not delegated.
Conclusion
A full node is software that independently validates a blockchain’s blocks and transactions instead of trusting someone else’s verdict.
Everything else a full node may do matters because that core act of local verification happens first.
- store history
- relay data
- serve wallets
- expose RPC
If you remember one thing, remember this: a blockchain is only trust-minimized for you if some machine you trust is actually checking the rules. A full node is that machine.
How does this part of the crypto stack affect real-world usage?
The node layer affects how and when on-chain actions become final, and whether you must trust a third-party RPC provider for correctness or availability. Before funding, trading, or withdrawing, verify the chain’s confirmation and finality expectations and use Cube Exchange’s funding and trade flows while accounting for those constraints.
- Check the chain’s finality model and recommended confirmation count in the protocol or client docs (for example: confirmation counts for Bitcoin, epoch/finality rules for PoS chains).
- Fund your Cube account with fiat or a supported crypto deposit using Cube’s deposit flow.
- Open the asset market or the withdrawal flow on Cube and pick an order type (market for immediate fills, limit for price control) or select the correct network when withdrawing.
- Review network-specific settlement and withdrawal requirements (required confirmations, finality delays, or known RPC outage notes) and adjust confirmations, order type, or withdrawal timing accordingly.
- Submit the trade or withdrawal on Cube and monitor on-chain confirmations until you reach the finality threshold you checked in step 1.
Frequently Asked Questions
A full node independently downloads and re-executes the protocol’s rules to decide whether blocks and transactions are valid; a validator (or block producer) actively participates in proposing or attesting to blocks in the consensus protocol and may require staking or other protocol-specific prerequisites. They often run together (especially on chains like Ethereum), but the roles answer different questions: verification versus participation in consensus.
No - “full” refers to full validation, not mandatory permanent archival storage. Some full nodes are archival and keep complete history, while others prune older block data after validating it; pruning preserves local verification but reduces the node’s ability to answer deep historical queries.
Because a trust-minimized node must replay sufficient history itself, initial synchronization (IBD or equivalent) requires downloading and validating many past blocks and state; the work is CPU-, disk‑I/O‑ and bandwidth‑heavy, so sync times depend strongly on client, sync mode, disk speed, RAM and network conditions.
Relying on a public RPC provider or Node-as-a-Service shifts verification and availability trust to that provider: you can read and broadcast through them, but you no longer perform independent rule checks and inherit their outage, censorship or stale‑data risks. Providers are practical for many use cases, but they change the system’s trust model compared with running your own validating node.
Full nodes face real network and operational risks: eclipse-style peer isolation, Internet routing (BGP) manipulation that distorts propagation, and mundane failures like disk exhaustion, misconfiguration, or overloaded RPC endpoints. These problems don’t break cryptography but can make a correctly‑validating node observe a distorted or stale view of the network.
Light clients trade local work for efficiency: they download less data and depend on proofs or responses from full nodes, so their security depends on the light‑client design and the assumptions about the served proofs or full‑node honesty. In some designs they can be very secure, but they change the trust model compared with running your own full node.
Yes: a reachable full node that accepts inbound connections and relays validated blocks and transactions helps the network’s health by improving propagation and supporting lightweight clients; operators must balance that public utility against extra bandwidth, uptime and exposure costs.
Required resources vary by chain and client - common bottlenecks are disk capacity and I/O, RAM, CPU and sustained bandwidth. Documentation for each client/chain provides recommended modes and disk estimates because there is no one‑size‑fits‑all hardware spec.
For post‑Merge Ethereum, no - a trustless Ethereum node is composed of an execution client and a consensus client working together; running only an execution client does not by itself give a fully trustless node after the protocol changes introduced by the Merge.
Related reading