What Is Multisig?
Learn what multisig is, how `m-of-n` wallets work, why they improve security and recovery, and where multisig setups add complexity and risk.
Introduction
Multisig is a wallet design in which spending requires multiple approvals instead of a single private key. That sounds like a small change, but it solves a deep problem in crypto custody: a single key is simple, yet it is also a single point of failure. If one person is compromised, one device is hacked, or one backup is lost, the whole wallet can be at risk.
The core idea of multisig is to separate control from any one secret. Rather than saying “whoever has this key can spend,” multisig says “these funds may be spent only if a defined subset of participants agrees.” That lets a wallet express governance directly: two founders must approve, or any two of three personal devices, or a buyer and seller plus an arbitrator in case of dispute. In practice, multisig sits at the boundary between cryptography and operations. The cryptography can enforce an approval rule, but the safety of the setup still depends on how keys are generated, stored, coordinated, and recovered.
What makes multisig worth understanding is that it is not just an extra password prompt. It changes the structure of risk. Some attacks become much harder because compromising one signer is no longer enough. Some failures become more survivable because losing one backup may not destroy access. But the price of that resilience is complexity: more devices, more metadata, more coordination, and more ways for setup mistakes to matter. The rest of the topic becomes clear once that tradeoff is visible.
How does m-of-n multisig control access?
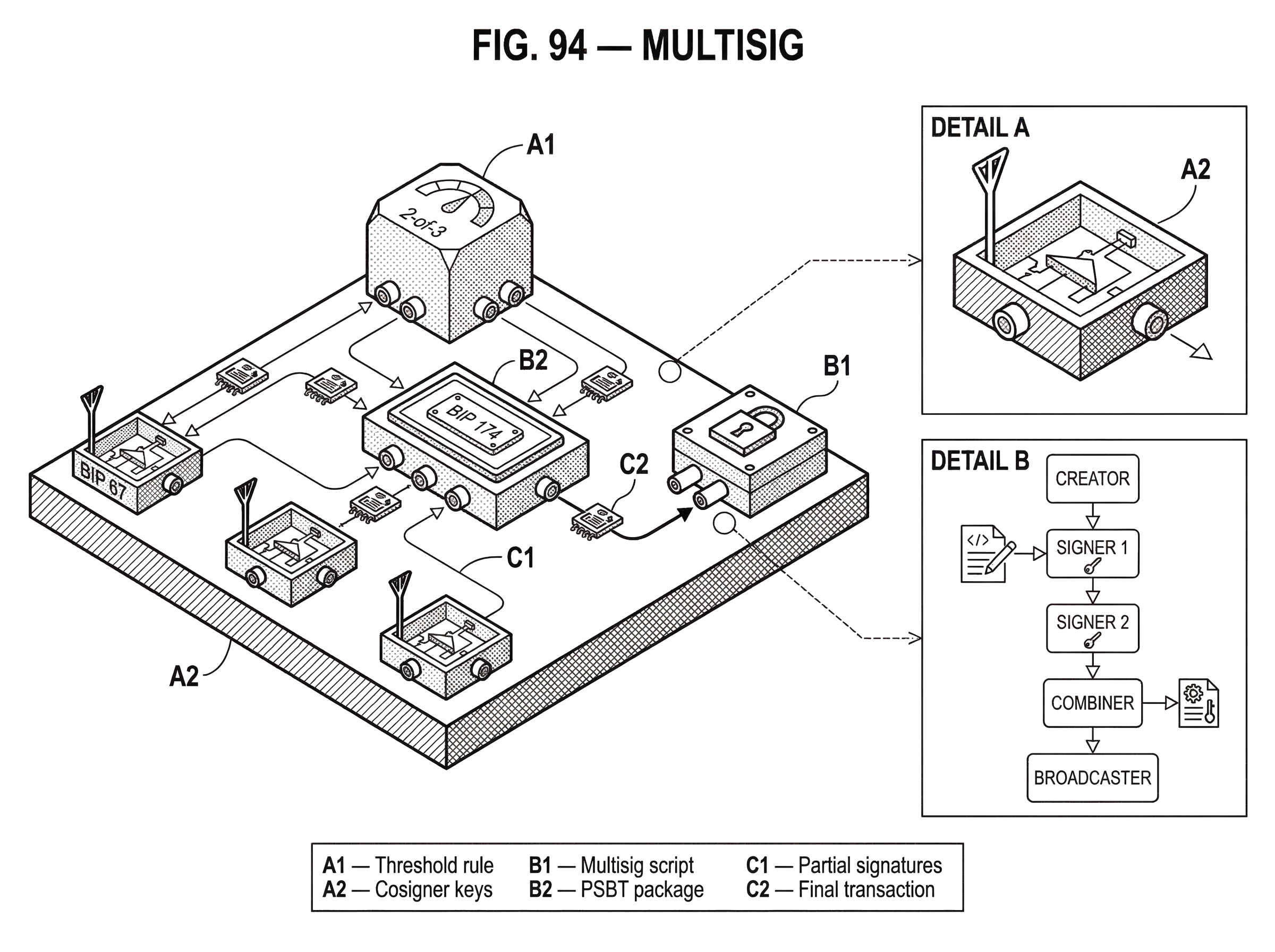
At the heart of multisig is a simple rule written as m-of-n. Here, n is the total number of authorized signers, and m is the number of signatures required to spend. A 2-of-3 wallet, for example, has three possible signers but only needs any two of them to approve a transaction. A 3-of-5 wallet has five possible signers and requires any three.
The important point is that ownership becomes a policy, not a person. In a single-signature wallet, the spending condition is effectively “produce one valid signature from this one key.” In a multisig wallet, the spending condition becomes “produce enough valid signatures from this set of keys according to this rule.” That policy is what the blockchain ultimately enforces. The chain does not care whether the signers are three people, one person with three devices, or a company plus a recovery provider. It only checks whether the required number of valid approvals exists.
This gives multisig two levers at once. The first is security against compromise: an attacker may need to steal several keys, often from different places or people, rather than just one. The second is resilience against loss: if the rule is 2-of-3, losing one key does not necessarily destroy access. The Bitcoin Wiki describes this backup tolerance as redundancy, which in a simple sense is n - m: the number of keys you can lose while still potentially spending. A 3-of-5 setup can survive the loss of two keys; a 2-of-3 setup can survive the loss of one.
That sounds unambiguously better, but it is only better if the operational design matches the threat model. If all three keys in a 2-of-3 wallet live on the same laptop, the policy looks decentralized on paper while remaining centralized in reality. Multisig only improves security when the signers are meaningfully independent; different devices, different storage locations, different administrators, or ideally some combination of those.
Why is 2-of-3 a common multisig choice?
The easiest nontrivial example is a 2-of-3 wallet. It is common because it balances two competing goals that single-key wallets cannot satisfy at once: resistance to theft and tolerance for loss.
Imagine someone storing substantial bitcoin with three hardware wallets. One is kept at home, one in a secure office location, and one in a bank safe deposit box or with a trusted recovery provider. The wallet is configured so any two of the three can authorize a spend. If a thief steals the device at home, that is not enough to move funds. If the safe deposit box becomes inaccessible, that is inconvenient but not fatal, because the home device and office device can still sign together. The same structure also works for an organization: three directors each control a signer, and any two must agree before treasury funds move.
What makes this arrangement work is not magic in the number three. It is the fact that the policy deliberately separates failure modes. Theft of one key and loss of one key no longer have the same consequence they would in a single-key wallet. But the example also shows what readers often underestimate: the wallet now depends on more than private keys alone. Each signer must know what wallet it is participating in; which cosigners exist, what threshold applies, what script or account structure is expected, and how to verify that an output is legitimate change rather than a malicious destination. In multisig, configuration becomes part of security.
How is multisig implemented on Bitcoin (P2SH, P2WSH)?
| Format | On-chain appearance | Address hint | Signer visibility | Main trade-off |
|---|---|---|---|---|
| P2SH | Script committed, revealed at spend | Starts with '3' | m-of-n visible at spend | Compatibility over efficiency |
| P2WSH | SegWit script commitment | No '3' prefix | m-of-n visible at spend | Better efficiency, larger signer sets |
| Threshold Schnorr | Single-sig appearance | Standard single-key | Signer count hidden | Privacy plus protocol complexity |
On Bitcoin, multisig has historically been implemented as a script condition: funds are locked in a way that can only be unlocked by satisfying a script that checks for enough valid signatures from a specified key set. Earlier common forms used Pay-to-Script-Hash, or P2SH, where the address hides the full redeem script until spending time. The Bitcoin Wiki notes that these P2SH multisig addresses commonly started with 3. Later SegWit-based constructions, especially P2WSH, improved efficiency and allowed larger signer sets; the Wiki describes P2SH multisig as largely superseded by SegWit forms for modern use.
The underlying mechanism is straightforward. The wallet first defines a script containing the threshold and the participant public keys. When funds are sent in, the chain only sees a commitment to that rule. When funds are spent, the spender reveals the script and enough signatures to satisfy it. The network validates that the revealed script matches the committed one and that the supplied signatures satisfy the rule.
A subtle but important implementation detail appears as soon as multiple wallets or services need to derive the same multisig address from the same set of participants. If different software orders the public keys differently, they can end up constructing different scripts and therefore different addresses, even though the human participants think they are talking about the same wallet. BIP 67 addresses this by standardizing how public keys should be encoded and sorted for deterministic P2SH multisig address generation. It requires compressed public keys and lexicographic sorting by binary representation before building the redeem script. The point is not elegance; the point is interoperability. Without a canonical ordering rule, coordination itself becomes a source of bugs.
This is a good example of what multisig really is at a systems level. It is not just “many signatures.” It is a shared agreement about a precise spending policy, a precise set of keys, and a precise encoding of that policy so every participant derives the same result. If even one part differs, users may fund the wrong address or fail to recognize valid change outputs.
How do PSBT and hardware wallets coordinate multisig signing?
| Role | Primary task | Typical actor | Output |
|---|---|---|---|
| Creator | Build unsigned tx | Wallet UI/node | Unsigned PSBT |
| Updater | Add UTXO metadata | Wallet/node | Enriched PSBT |
| Signer | Verify and sign | Hardware wallet | Partial signature |
| Combiner | Merge PSBTs | Coordinator software | Combined PSBT |
| Finalizer | Assemble final tx | Wallet or node | Final signed tx |
Once several parties must cooperate to sign, a raw transaction format is not enough. Each signer needs context: what inputs are being spent, what scripts are expected, which partial signatures already exist, and what still needs approval. In Bitcoin, PSBT (the Partially Signed Bitcoin Transaction format defined in BIP 174) exists for exactly this purpose.
A PSBT is a transaction package that carries the unsigned transaction plus the metadata signers need in order to inspect and partially sign it. The specification describes roles such as creator, updater, signer, combiner, finalizer, and extractor. Those roles are conceptually useful because they separate concerns. Someone proposes the transaction, someone enriches it with UTXO and script data, multiple signers add partial signatures, a combiner merges those contributions, and finally a finalizer turns the result into a fully valid network transaction.
This workflow matters because multisig is usually not sequential in a neat, linear way. Two hardware wallets may sign in parallel. Different software may each add some metadata. An air-gapped device may inspect a PSBT from a QR code or SD card, sign it offline, and return an updated PSBT for combination. Bitcoin Core’s PSBT documentation explicitly frames PSBT as a format meant to simplify cooperation in cases like hardware wallets, multisig setups, and CoinJoin.
That practical layer is easy to miss if one only learns the on-chain script. In real custody systems, the spend path often looks like this: an operator constructs a transaction, exports it as PSBT, each signer device verifies outputs and change, each device adds its partial signature, and then software combines and finalizes the transaction once the threshold is met. The threshold is enforced on-chain, but the user experience is mostly a coordination protocol off-chain.
Hardware wallet tooling reinforces this. HWI, the Bitcoin Hardware Wallet Interface, exists to let software interact with many hardware wallets in a standardized way, rather than reinvent device-specific support. Product documentation like COLDCARD’s multisig guide shows how much wallet metadata those devices need in order to sign safely: threshold m, signer count n, cosigner extended public keys, fingerprints, address type, derivation path, and often wallet descriptors. This is why experienced users say multisig is not just about backing up seeds. You must also preserve the wallet description that tells each signer what it is signing for.
When should you use multisig and for what purposes?
People reach for multisig when they want to remove a single point of failure without handing complete control to a single custodian. That broad motivation shows up in several concrete patterns.
For individuals, multisig is often a form of self-custody with recovery. A 2-of-3 setup can protect against both theft and accidental loss in a way a single seed phrase cannot. One signer may be on a hardware wallet used for daily access, another in long-term storage, and a third with a service that helps recover funds but cannot move them alone. BIP 67 even notes this as a common wallet-as-a-service pattern: the provider may cosign day-to-day transactions, while the user retains an offline backup key and can recover without the provider if needed.
For organizations, the appeal is governance. Treasury funds should not depend on one executive’s laptop or one employee’s honesty. A board or operations team can require multiple approvals before money moves. That is why multisig appears so often in DAO operations, protocol councils, and corporate custody: it turns “we should require multiple approvers” into a rule the wallet itself enforces. In early-stage protocol governance, token votes may approve an action, but a multisig often still serves as the execution backstop because someone must actually sign and broadcast the final transaction.
For transactions between parties who do not fully trust one another, multisig can support escrow-like designs. The classic Bitcoin example is a buyer, seller, and arbitrator in a 2-of-3 arrangement. If the sale completes normally, buyer and seller sign. If there is a dispute, either side can resolve it with the arbitrator. Here the mechanism matters more than the label: the wallet embeds a dispute-resolution structure without requiring the arbitrator to hold unilateral custody.
What are multisig’s operational and implementation risks?
The common misunderstanding is to treat multisig as automatically safer because it involves more keys. In reality, multisig removes some risks by introducing others.
The first new risk is operational complexity. Every signer must be set up correctly, and every device must agree on the wallet’s policy and derivation details. If one cosigner has the wrong configuration, it may derive different addresses or fail to recognize change outputs. COLDCARD’s documentation is unusually candid on this point: a PSBT may not contain all the metadata a device wants, and the device may need pre-imported wallet details in order to verify and sign correctly. In other words, the cryptography may be right while the user still gets into trouble because the surrounding metadata is incomplete or inconsistent.
The second new risk is coordination failure. A 3-of-5 wallet may be robust against single-key loss, but it is also harder to use under pressure. If signers are geographically distributed, unavailable, deceased, or simply disorganized, the threshold that protects the funds can also delay legitimate action. Security and liveness are in tension: increasing the number of signers can make compromise harder, but it can also make timely spending harder.
The third risk is implementation risk, especially on smart-contract platforms. On Bitcoin, multisig is largely a native spending condition with mature standards around scripts, descriptors, and PSBT. On Ethereum-like systems, what users call “multisig” is often a smart contract account that maintains a set of owners and a threshold in contract storage. That can be powerful (it enables richer logic than native script conditions) but it also means the security of the wallet depends on contract correctness. The Parity multisig incidents made this painfully clear. In one case, an attacker abused an initialization flaw to take ownership and drain funds. In another, an uninitialized shared library was taken over and self-destructed, permanently locking funds in hundreds of wallets. The lesson is not that smart-contract multisig is bad; it is that once multisig becomes an application rather than a narrow native primitive, the attack surface expands dramatically.
This contrast between Bitcoin-style script multisig and contract-based multisig is worth keeping in view. They solve a similar governance problem, but they fail differently. Bitcoin multisig tends to concentrate risk in key management, metadata, and workflow. Contract multisig adds all of that plus code risk, upgrade risk, initialization risk, and dependency risk.
How do multisig, threshold signatures, and MPC differ?
Readers often hear multisig mentioned alongside MPC wallets, threshold signatures, MuSig2, or FROST and assume these are interchangeable. They are related, but the mechanism is different.
Traditional multisig exposes the fact that multiple keys are participating. On Bitcoin, the spending policy is represented as a script condition, and satisfying it usually means providing multiple distinct signatures or witnesses according to that script. Threshold signature schemes, by contrast, aim to let multiple participants jointly produce what looks on-chain like a single signature under a single aggregate public key. BIP 340, which standardizes Schnorr signatures for secp256k1, highlights the key property that makes such schemes possible: linearity. Multiple parties can collaborate to produce a valid signature for the sum of their public keys.
Why does this matter? Because it can improve efficiency and privacy. A threshold-Schnorr construction can make cooperative spending look like an ordinary single-signer signature on-chain, rather than advertising a visible m-of-n script. But that elegance comes with protocol complexity. Nonce handling in multisignature and threshold signing is delicate; BIP 340 explicitly warns that naive or deterministic nonce generation from the default signing algorithm is insecure in these protocols. So while threshold signatures may sometimes replace classic multisig at the interface level, they are not just a simpler version of the same idea. They trade one kind of complexity for another.
That is also the right way to compare multisig with MPC wallets. Multisig uses multiple independent keys and a policy the chain can verify directly. MPC typically splits the signing process off-chain so participants jointly control what appears externally as one key. The security goal can be similar (no single party should be able to spend alone) but the visibility, trust assumptions, recovery model, and implementation risks differ.
How do I pick m and n to match my failure model?
| Policy | Theft resistance | Recovery tolerance | Coordination friction | Best for |
|---|---|---|---|---|
| 1-of-1 | Low | None | None | Single user |
| 2-of-3 | Moderate | Lose one key | Low | Individuals & small teams |
| 3-of-3 | High | None | High | Maximum theft resistance |
| 3-of-5 | Very high | Lose two keys | Higher | Organizational governance |
A wallet policy is a statement about what failures you expect and which ones you can tolerate. That is why there is no universally best m-of-n setup.
If m is too low, compromise becomes easier. A 1-of-3 wallet with three devices is basically not multisig in the security sense; one compromised signer is enough. If m is too high, recovery and availability become fragile. A 3-of-3 wallet removes redundancy entirely: no single signer can steal funds, but losing one key can lock the wallet forever. This is why 2-of-3 is so common for personal custody and small teams. It preserves one unit of redundancy while still preventing unilateral spending.
The right question is not “what threshold is strongest?” but “which combination of theft, loss, and unavailability do we want to survive?” For a family inheritance setup, you may prioritize recoverability over fast day-to-day access. For a protocol treasury, you may prioritize resistance to insider abuse and require signers under separate administrative control. For a trading operation, you may need a threshold low enough to stay operational during travel, device failure, or time-sensitive transactions.
In all of these cases, the threshold is only one part of the design. A 2-of-3 policy with all keys in one office is weaker than a 2-of-2 policy with hardware isolation and strong process controls in some scenarios. Multisig does not eliminate the need to think about adversaries; it forces you to be more precise about them.
What is fundamental to multisig versus what is an implementation convention?
The fundamental part of multisig is simple: the wallet requires multiple independent approvals according to a threshold rule. That is the essence.
Much else is convention or implementation choice. On Bitcoin, whether the policy is represented through older P2SH multisig, newer SegWit constructions, descriptors, or PSBT workflows is partly a matter of evolving standards and wallet interoperability. BIP 67’s key sorting convention is not fundamental to the idea of multiple signers, but it is fundamental to getting different software to derive the same address. PSBT is not the essence of multisig, but it has become a practical necessity for robust multi-device coordination. On smart-contract chains, owner sets and thresholds may be stored and managed in contract state rather than encoded in a native script, which gives flexibility at the cost of code risk.
This distinction helps prevent confusion. If you remember only the conventions, multisig looks like a grab bag of wallet file formats, address types, and device quirks. If you remember only the abstract idea, you miss where real systems actually fail. The durable understanding is to keep both levels in view: the invariant is cooperative authorization; the implementation details determine whether that invariant is usable and safe.
Conclusion
Multisig is the idea that a wallet can enforce shared control instead of trusting one key. Its power comes from changing the shape of failure: compromise of one signer may no longer be enough to steal funds, and loss of one signer may no longer destroy access. That is why multisig is used for personal self-custody, treasury governance, escrow, and institutional security.
But multisig is not free security. It moves part of the problem from pure key secrecy into coordination, metadata, device interoperability, and sometimes smart-contract correctness. A good multisig design is therefore not just “more signatures.” It is a carefully chosen failure model, backed by tools and procedures that let multiple signers verify the same wallet, the same transaction, and the same recovery path.
If there is one sentence to remember tomorrow, it is this: multisig makes a wallet into a rule for cooperation, and that rule is only as strong as both its cryptography and its operations.
How do you secure your crypto setup before trading?
Securing your crypto before trading means verifying your custody setup, backups, and signing devices, then funding and executing trades through Cube Exchange’s non-custodial MPC workflow. Cube uses MPC key management so trades execute without a single private key being exposed, but you still must confirm multisig descriptors, signer availability, and network details before you move meaningful funds.
- Confirm and record your custody metadata: export and store cosigner extended public keys (xpubs), fingerprints, derivation paths, address/descriptor type, and a short recovery checklist.
- Verify signer interoperability: create a test PSBT or a small unsigned transaction, have each signer add a partial signature, and confirm the combined result finalizes.
- Fund your Cube Exchange account with fiat or a supported crypto transfer and complete a small test deposit on the correct chain and token.
- Open the relevant market on Cube and select an order type (use a limit order for price control or a market order for immediate execution).
- Enter your trade size, review estimated fill, fees, and slippage, then submit the order.
Frequently Asked Questions
There is no universally best m-of-n; choose m and n to reflect which failures you want to tolerate (theft, loss, unavailability). Lower m makes unilateral theft easier, higher m reduces redundancy and can make recovery or timely spending fragile, which is why 2-of-3 is a common balance for personal and small-team custody. This guidance is described throughout the article’s section on choosing thresholds and failure models.
You must preserve the wallet description and metadata in addition to any seed or private keys - that includes cosigner extended public keys (xpubs), fingerprints, derivation paths, address type/descriptor, and the threshold so devices agree on what they are signing. The article stresses that multisig security depends on configuration metadata, and vendor guides (e.g., Coldcard, HWI) list the exact items hardware wallets need to verify and sign safely.
If different software orders public keys differently you can derive different redeem scripts and therefore different addresses, which can lead to funding the wrong address or failing to co-sign; BIP67 standardizes compressed-key lexicographic sorting to avoid this. The article explains the interoperability problem and cites BIP67’s deterministic public-key ordering as the practical fix.
Smart-contract multisig adds code and lifecycle risk on top of key management: bugs in contract initialization or libraries can let attackers take ownership or can permanently lock funds, as shown by the Parity multisig incidents. The article contrasts Bitcoin-style script multisig (key/metadata risks) with contract multisig (adds code, upgrade, and dependency risks) and the referenced incident analyses document concrete failures.
Threshold-signature schemes let participants produce a single on‑chain signature that looks like one key, improving efficiency and privacy, but they replace visible script simplicity with protocol complexity such as delicate nonce handling and interactive signing steps. The article explains this distinction and BIP340 warns naive or deterministic nonce generation is insecure for these protocols.
Multisig reduces single-key compromise risk but introduces operational complexity, coordination failures, and implementation risk; every signer must be correctly configured and available, or legitimate spending can be delayed or fail. The article’s sections on operational complexity, coordination failure, and implementation risk summarize these trade-offs.
PSBT workflows are essential for multisig but have interoperability pitfalls: combiners may encounter duplicate/conflicting PSBT key-value pairs and resolve them arbitrarily, and signers may refuse to sign inputs if required UTXO metadata (e.g., non-witness UTXO) is missing. The PSBT spec (BIP-174) documents these behaviors and the article highlights that PSBT metadata completeness is crucial for safe signing.
On Bitcoin, legacy P2SH multisig (addresses starting with ‘3’) has largely been superseded by SegWit constructions like P2WSH, which are more efficient and support larger signer sets, so modern multisig wallets typically use SegWit forms. The article describes this evolution and the Bitcoin Wiki and other references note P2SH’s older status compared with SegWit multisig.
Related reading