What is WASM (WebAssembly)?
Learn what WebAssembly (Wasm) is, how its sandboxed execution model works, why it exists, and where it fits in browsers, servers, and smart contracts.
Introduction
WebAssembly, or Wasm, is a binary instruction format for a stack-based virtual machine that was designed to be portable, compact, and efficient. That definition is accurate, but it hides the real reason Wasm became important: software usually has to choose between being portable and being close to the machine. Source code is portable, but it still needs a compiler and a target platform. Native machine code is fast, but tied to a CPU and operating system. JavaScript is ubiquitous in the browser, but it was not designed to be a universal compilation target for every language.
Wasm sits in the middle of that tension. It gives compilers a low-level target that is structured enough to validate safely, compact enough to ship efficiently, and constrained enough to run inside a sandbox. That is why it shows up in very different places: in browsers next to JavaScript, in server-side runtimes through WASI, and in some blockchain execution environments where developers want a safer, more general-purpose virtual machine than a chain-specific one.
The key idea is simple: Wasm is not an operating system, not a programming language, and not a full application platform by itself. It is an execution format with precise semantics. Everything interesting follows from that separation. A Wasm module can compute, but it cannot read a file, open a socket, or touch the outside world unless its host explicitly offers those abilities. That boundary is what makes Wasm portable and sandbox-friendly, and it is also what makes embeddings like browsers, Wasmtime, WasmEdge, or blockchain runtimes differ so much in practice.
Why does WebAssembly exist and what problem does it solve?
To see why Wasm exists, start from the problem it solves for a compiler and a runtime.
A compiler wants a target that is stable and widely available. If it targets x86 machine code, that output will not run on ARM. If it targets a particular operating system ABI, that output inherits all the assumptions of that system. If it targets a high-level language runtime, such as JavaScript, it must express low-level ideas like memory layout, numeric operations, and control flow through abstractions that were not designed for them. The result may work, but it is awkward.
A runtime wants the opposite side of the bargain. It wants code in a form that is easy to decode, quick to validate, and safe to isolate from the host. If you accept arbitrary native code, you inherit the full danger of arbitrary machine instructions. If you accept only a high-level scripting language, you may lose predictable compilation from languages like Rust, C, or C++. Wasm was designed as the narrow waist between these needs: low-level enough to compile into efficiently, but constrained enough to validate and sandbox.
That is why the official project describes Wasm as a portable compilation target and a memory-safe, sandboxed execution environment. Those two goals are not separate. They support each other. Portability comes from defining a virtual machine with standard semantics instead of targeting a specific CPU. Safety comes from restricting what code can do unless the host gives it capabilities explicitly. Compactness and load-time efficiency matter because Wasm was designed to be shipped and instantiated frequently, especially on the web.
How does WebAssembly sandbox modules and interact with the host?
The easiest way to think about a Wasm module is as code packaged in a sealed box with labeled sockets on the outside.
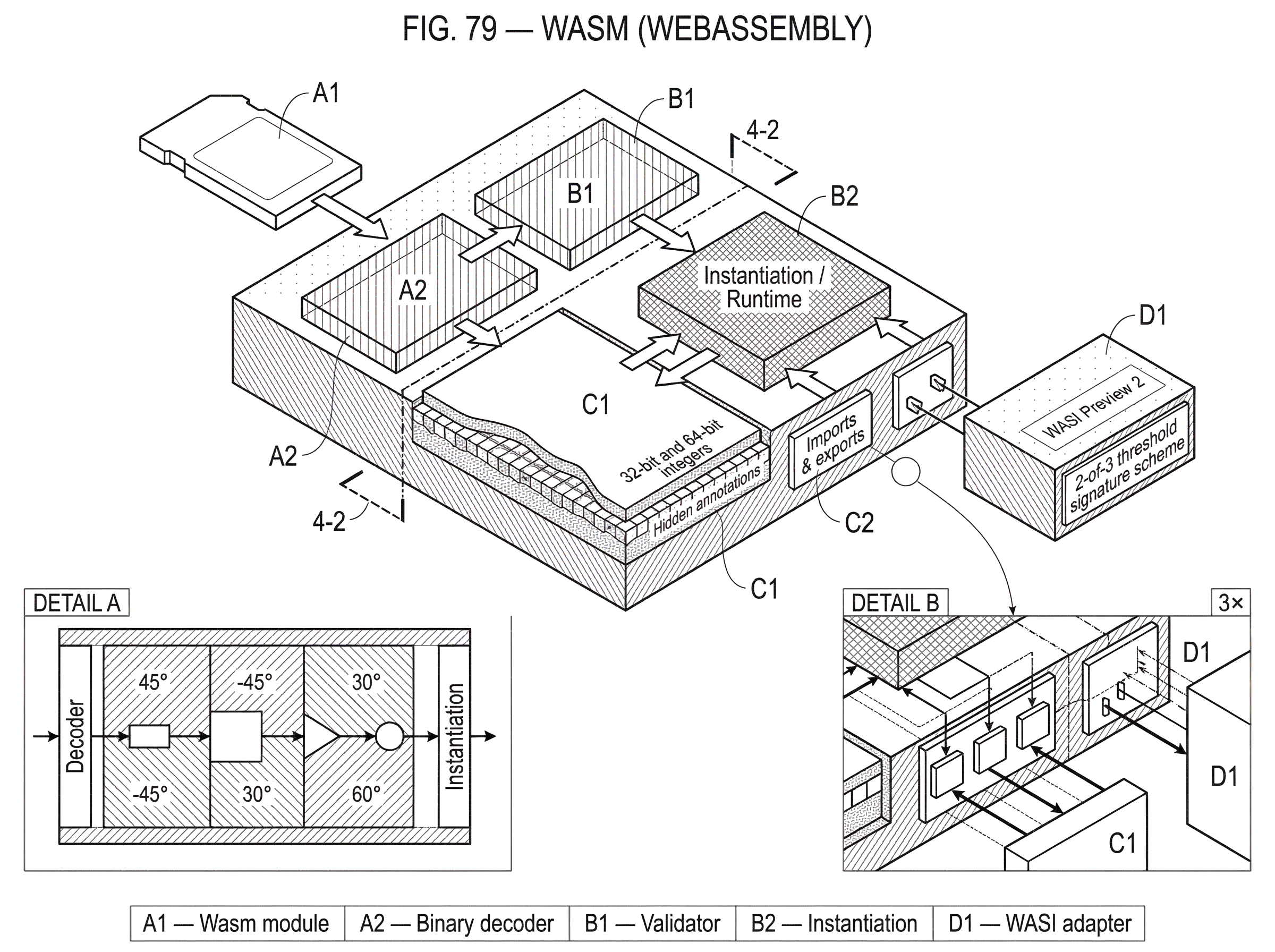
Inside the box are functions, globals, tables, and usually a linear memory. The code can call its own functions, read and write its own memory, and compute on primitive value types such as 32-bit and 64-bit integers and floating-point numbers. But the box does not come with built-in power outlets to the real world. If the module wants to log something, fetch data, read a file, or ask for time, the host must expose an imported function or interface for that purpose.
This explains several facts at once. It explains why Wasm is sandboxed: there is no ambient authority. It explains why the same module can run in different places: the core semantics are embedding-independent, while the host-specific capabilities are attached from outside. It also explains why people sometimes misunderstand Wasm. They hear “runs anywhere” and imagine a fully self-sufficient binary. In reality, Wasm code is portable at the computation layer, but practical programs still depend on the host interfaces they import.
The analogy of a sealed box is useful because it captures the security boundary. It fails, however, if taken too literally. A Wasm module is not physically isolated; it is only as safe as the runtime and the host policy implementing the sandbox. The core specification says Wasm has no ambient access to the environment, but the host still decides which imports exist, how memory is limited, how time is measured, and which side channels matter.
What are the parts of a Wasm module (memory, imports, exports, tables)?
A Wasm binary is organized as a module, and the module is the basic unit of distribution and instantiation. The core spec describes modules as containing definitions for functions, tables, linear memories, globals, imports and exports, data or element segments, and an optional start function.
The most important pieces are easiest to understand by their role.
Functions hold the executable logic. Exports are the names the outside world is allowed to call or inspect. Imports are the placeholders the host must fill in before the module can run. Globals hold small pieces of state. Tables are used for references, especially indirect function calls. And linear memory is the module’s raw byte-addressable region for data structures, buffers, strings, and language runtime state.
Linear memory matters because most mainstream languages assume a flat address space for heaps, stacks, arrays, and pointers. Wasm provides that as a contiguous mutable array of bytes that starts at an initial size and can grow dynamically. This is one of the places where Wasm feels low-level. A Rust or C program compiled to Wasm can still manage its own layout inside linear memory. Wasm’s safety guarantee is that code cannot break the Wasm memory model itself; it does not guarantee that unsafe code cannot corrupt its own data structures inside its allocated memory.
That distinction is easy to miss and important to keep. Wasm prevents arbitrary memory access outside the sandboxed model. It does not magically make unsafe languages safe at the application level.
How does WebAssembly execution work: decode, validate, instantiate, invoke?
| Phase | What happens | Main goal | Typical result |
|---|---|---|---|
| Decoding | Parse binary to IR | Efficient load | Internal module representation |
| Validation | Type and structural checks | Enforce safety | Module accepted or rejected |
| Instantiation | Wire imports; allocate state | Bind to host | Live module instance |
| Invocation | Call exported functions | Execute logic | Function returns or side effects |
The core specification conceptually divides Wasm processing into three phases: decoding, validation, and execution, where execution includes instantiation and invocation. This sequence is the mechanical heart of Wasm.
Decoding takes the compact binary format and turns it into an internal representation. Wasm’s binary encoding is designed to be size- and load-time-efficient, which matters both on the web and in other environments that care about startup latency.
Validation is where Wasm earns much of its safety story. Before execution, a decoded module is checked for type correctness and structural well-formedness. The runtime verifies that instructions are used with the right kinds of values, that control flow is valid, that imports and exports line up with their declared signatures, and that memory/table accesses obey the rules of the abstract machine. This means many mistakes that would become undefined behavior in native code are rejected before the module is ever instantiated.
Instantiation is the moment the sealed box is wired into a particular host environment. Imports are connected. Memory, tables, and globals are created. Initialization segments are applied. If the module has a start function, it may run at this stage. Only after instantiation do you have a live module instance rather than a static piece of code.
Invocation is then just calling an exported function on that live instance.
A concrete example makes this clearer. Imagine a small image-processing routine written in Rust and compiled to Wasm. The compiled module exports a function that takes a pointer and a length in linear memory, then transforms the bytes in place. In a browser, JavaScript loads the .wasm binary, validates it, instantiates it, and provides any imports the module expects. JavaScript then allocates a byte buffer in the module’s linear memory, copies pixel data into it, and calls the exported function. The Wasm code runs over raw bytes inside its own memory, returns, and JavaScript reads the result back out. Nothing here required the module to know whether it was in Chrome or Firefox, on x86 or ARM. But just as important, nothing here gave the module automatic access to the DOM, the filesystem, or the network. Every such interaction would need a host-provided interface.
Why is WebAssembly a stack machine and what are the trade-offs?
Wasm is defined as a stack-based virtual machine. That means instructions conceptually consume operands from a stack and push results back onto it. For example, rather than naming many general-purpose registers directly, instructions operate through a structured operand stack.
Why do this? Because a stack machine can be encoded compactly and validated cleanly. The type checker can reason about the values flowing through instructions in a disciplined way. This helps with fast validation and portable semantics. It also makes the bytecode less entangled with the quirks of any one hardware architecture.
But design choices always come with tradeoffs. Some blockchain designers have argued that a stack machine can be a poor fit for deterministic and efficient on-chain execution compared with formats that are closer to modern hardware, such as register-based designs. Polkadot’s move toward a RISC-V–based virtual machine for smart contracts was motivated in part by concerns about Wasm’s computational cost and the difficulty of achieving identical behavior across binaries in a consensus-critical setting. That does not make Wasm “bad.” It means Wasm was optimized for a broad portability-and-sandboxing problem, not for every possible execution environment equally.
This is an important pattern to remember: the right virtual machine depends on what invariants matter most. For the web and many off-chain runtimes, Wasm’s compactness, validation model, and portability are excellent tradeoffs. For some blockchains, determinism and metering constraints may push designers toward additional restrictions, custom tooling, or even a different VM.
Why is WebAssembly intentionally low-level instead of including high-level APIs?
People often ask why Wasm feels so bare. Why not include strings, files, sockets, or rich objects directly in the core specification?
Because those are not universal machine concepts. They are host concepts.
The core Wasm spec intentionally defines a small low-level machine: primitive number types, a vector type, reference types, functions, memories, tables, globals, and precise execution rules. This keeps the core portable across embeddings. A browser can expose Web APIs through JavaScript and WebAssembly integration. A standalone runtime can expose operating-system-like capabilities through WASI. A blockchain can expose host functions for storage reads, event emission, or cryptographic precompiles. If these were hard-coded into the core, Wasm would stop being general.
This separation also explains why Wasm has both a binary format and a textual format. The binary .wasm form is what machines ship and load efficiently. The textual .wat form exists for debugging, inspection, teaching, experimentation, and writing small modules by hand. The text form is not the primary deployment target; it is the readable window into what would otherwise be opaque bytes.
What is the Wasm host boundary and how do browser APIs and WASI differ?
| Host type | Typical imports | Permission model | Portability | Best for |
|---|---|---|---|---|
| Browser | DOM, fetch, timers | Same-origin & browser perms | High on the web | Web apps and UIs |
| WASI | Files, sockets, clocks, random | Host-granted capabilities | Portable across runtimes | Server, edge, tooling |
| Standalone runtimes | WASI-like extensions, plugins | Configurable host policy | Portable if using WASI | Plugins, serverless, edge |
| Blockchain runtimes | Storage, crypto, block metadata | Strict consensus rules | Portable with runtime constraints | Smart contracts and chains |
Once you understand that Wasm itself has no ambient host access, the ecosystem becomes easier to parse.
In the browser, Wasm is embedded alongside JavaScript. The JavaScript API defines how JS code validates, compiles, instantiates, and interacts with Wasm modules. The Web API adds browser-specific behaviors such as streaming compilation and instantiation from Response objects. On the web, the browser’s existing origin and permission model governs what the combined application can do.
Outside the browser, the most important standard effort is WASI, the WebAssembly System Interface. WASI is a modular system interface for running WebAssembly outside the web and providing access to things like files, network connections, clocks, and random numbers. The point is not to recreate a full POSIX environment exactly, but to define portable host capabilities in a way that suits Wasm’s sandbox model.
This matters because non-web Wasm would otherwise fragment immediately. Every runtime could invent its own host API, and compiled modules would stop being portable in practice. WASI tries to solve that by giving runtimes and modules a shared vocabulary for outside-world interaction. The project is still evolving; Preview 2 is described as a stable modular collection of APIs defined with WIT, with broader language support and better virtualizability than earlier versions.
Standalone runtimes like Wasmtime and WasmEdge sit on top of this host boundary. They execute Wasm outside the web, expose WASI or WASI-like capabilities, and can also be embedded as libraries inside larger applications. This is where Wasm becomes useful for plugins, edge functions, serverless workloads, local automation, and application sandboxing.
Why are blockchains adopting WebAssembly for smart contracts?
Blockchains need an execution environment that many nodes can run consistently, while also containing untrusted code. That makes Wasm attractive almost by construction. A blockchain runtime wants a portable bytecode format, explicit imports, a constrained memory model, and a sandbox. Those are all things Wasm already provides.
That is why Wasm-based smart contract platforms exist. CosmWasm, for example, is a Wasm-based smart contracting platform integrated with the Cosmos SDK. More broadly, newer chains and execution layers have often treated Wasm as an alternative to the EVM when they want broader language support and a more general-purpose VM model.
The interesting point is not merely that Wasm can run smart contracts. It is why it is appealing there. Smart contracts are just a special case of untrusted programs running inside a host-defined environment. The chain becomes the embedder. Storage access, event emission, block metadata, and cryptographic helpers are exposed as imports or host functions rather than ambient privileges. Gas accounting or metering can also be layered in by the runtime.
A concrete example helps. Suppose a decentralized exchange wants settlement logic that is highly isolated, auditable, and portable across deployment environments. A Wasm-based execution layer can package that logic into a module whose external powers are tightly defined: it may read a provided market state snapshot, verify signatures through host-provided cryptographic calls, and produce a settlement result. In systems that use threshold cryptography around settlement, the surrounding host can enforce strong authorization boundaries. For instance, Cube Exchange uses a 2-of-3 threshold signature scheme for decentralized settlement: the user, Cube Exchange, and an independent Guardian Network each hold one key share, no full private key is ever assembled in one place, and any two shares are required to authorize a settlement. Wasm is not what creates threshold signing, but it fits naturally with the same architectural instinct: keep critical logic inside narrow, explicit interfaces rather than relying on broad, implicit trust.
At the same time, Wasm is not automatically the perfect blockchain VM. Consensus systems care about strict determinism, metering precision, and denial-of-service resistance in ways that browser and server embeddings often do not. That is why blockchain uses of Wasm often add restrictions, custom runtimes, or domain-specific tooling.
What performance can you expect from WebAssembly in real workloads?
| Mode | Startup | Warm-path latency | Image size | Best fit |
|---|---|---|---|---|
| Ahead-of-time (AoT) Wasm | Fast cold start | Low warm latency | Very small images | Edge and serverless |
| Interpreted Wasm | Slower cold start | High warm latency | Small modules | Prototyping or constrained toolchains |
| Native containers | Slower cold start | Low warm latency | Large images | Long-running services |
Wasm is often described as aiming for near-native speed. That is a design goal, and in many workloads it is directionally true enough to be useful. But the mechanism matters more than the slogan.
Wasm gets good performance because it is low-level, structured, and easy for runtimes to compile efficiently. A runtime can validate the module once, then interpret it, compile it just in time, or compile it ahead of time depending on the engine and deployment model. Because the semantics are precise and the code format is compact, startup and loading can be efficient too.
But “Wasm performance” is not a single thing. It depends on the runtime, the compilation mode, the host interfaces, and the workload. Research on serverless workloads has found that ahead-of-time compiled Wasm images can be much smaller than container images and can reduce cold-start latency, while interpreted Wasm can suffer severe warm-path overhead and heavy I/O serialization costs. That pattern makes sense from first principles: if startup footprint matters, compact modules help; if your workload spends time crossing host boundaries or running without strong compilation, the costs can dominate.
So the right conclusion is narrower and more useful than marketing language. Wasm is a strong fit when you care about portability, sandboxing, and compact deployment, and its performance can be very good when the runtime strategy matches the workload. It is not a magic replacement for native code or containers in every scenario.
How do the Component Model and WIT improve Wasm interoperability across languages?
Classic Wasm solved portability at the execution level, but not fully at the component level. A .wasm module can export functions, but cross-language composition becomes awkward when different languages have different string layouts, memory ownership rules, and calling conventions.
This is the problem the WebAssembly Component Model tries to address. The idea is to move from “here is a low-level module with raw imports and exports” to “here is a component with typed interfaces that other components can understand across languages.” The Component Model work is being standardized separately and is being developed and stabilized as part of WASI Preview 2.
The interface language here is WIT, the Wasm Interface Type language. WIT defines contracts, not behavior. A WIT file describes interfaces and worlds: what a component imports, what it exports, and the data types those boundaries use. It includes primitive and compound types and a notion of resources for non-copyable external entities.
This matters because many real applications are not single modules. They are compositions of parts written in different languages, running in different hosts, with clear boundaries between them. Raw Wasm gets you portable execution. The Component Model aims to get you portable composition.
You can think of the difference this way. Core Wasm says, “Here is how code executes.” The Component Model adds, “Here is how independently built pieces of code describe their contracts so they can fit together.” That is a very different layer of the stack.
When do WebAssembly's assumptions fail and what risks should you watch for?
The cleanest way to understand Wasm is also to see its limits.
Wasm assumes there is a trustworthy embedder that enforces the sandbox, supplies imports, and decides resource limits. If the host is badly designed, Wasm does not save you. The safety boundary lives partly in the runtime and host policy, not only in the bytecode format.
Wasm also assumes that low-level portability is more valuable than exposing rich host features in the core language. That is why host interaction must be layered in separately. The benefit is portability. The cost is that practical interoperability depends on surrounding standards like the JavaScript embedding APIs, WASI, and increasingly the Component Model.
In blockchain settings, another assumption becomes fragile: that the standard Wasm execution model is naturally aligned with consensus determinism and metering. Sometimes it is; sometimes it requires substantial adaptation. This is why some ecosystems embraced Wasm for contracts or chain runtimes, while others moved toward alternative VMs.
And finally, Wasm does not erase the semantics of the source language. A Rust module, a C module, and a Go module may all compile to Wasm, but their memory models, runtime assumptions, panic behavior, allocator choices, and host bindings still matter. Wasm gives them a common execution substrate, not identical language behavior.
Conclusion
Wasm is best understood as a portable, sandboxed execution format with explicit host boundaries. That is the idea to remember tomorrow.
Its power comes from a careful split of responsibilities. The core format defines how code is represented, validated, and executed. The host defines what outside-world capabilities exist. That split is why Wasm can run in browsers, servers, edge runtimes, and smart contract systems without becoming tied to any one of them.
If you keep that picture in mind (a compact low-level module inside a sandbox, connected to the world only through explicit imports) most of the ecosystem starts to make sense: JavaScript APIs in the browser, WASI outside the web, component interfaces for cross-language composition, and blockchain runtimes that either adapt Wasm or decide its tradeoffs are not the right ones for consensus-critical execution.
How does WebAssembly (Wasm) affect real-world network usage and risk?
Wasm changes how a network executes code: it affects determinism, gas/metering, host APIs, and how portable smart contracts are; all of which matter for node behavior, upgrade paths, and asset risk. On Cube Exchange, follow a short research-and-test workflow that checks a Wasm-based network’s execution assumptions before you fund, trade, or increase exposure.
Frequently Asked Questions
Wasm enforces sandboxing by design: modules have no ambient access to the outside world and can only call functions or use resources explicitly provided by their host via imports; the runtime/host is responsible for implementing and enforcing policies such as which imports exist, memory limits, and time measurements.
Wasm prevents code from accessing memory outside the module’s linear memory, but it does not make unsafe source-language behavior impossible - a C or Rust program compiled to Wasm can still corrupt its own data structures inside its allocated linear memory if it contains undefined or unsafe operations.
WASI (WebAssembly System Interface) is a modular set of host APIs designed to give non-browser Wasm programs controlled access to system-like capabilities (files, clocks, networking, randomness), and it aims to standardize those host features so modules remain portable across standalone runtimes; the project is community-driven and evolving (Preview 2 is a current milestone).
The Component Model and WIT add a typed interface layer over low-level Wasm modules so independently built parts can interoperate across languages and embeddings: WIT describes typed contracts and resources while the Component Model packages components for cross-language composition, and both are being developed and stabilized (part of WASI Preview 2 efforts).
Wasm’s stack-machine design yields compact encoding and easy validation, which are good for portability and fast load/validation, but some consensus-critical blockchain projects find stack-based bytecode harder to make deterministic and cost-efficient on-chain and have explored alternatives like RISC-V–style VMs for those priorities.
Wasm can approach native speeds because it is low-level and easy for engines to compile efficiently, but real performance depends heavily on the chosen runtime, whether code is ahead-of-time compiled or interpreted, and how often the workload crosses host boundaries; for example, serverless research shows AOT-compiled Wasm can reduce cold-starts while interpreted modes often incur higher overheads.
Wasm’s core spec intentionally omits high-level host concepts like files, sockets, or strings so the same low-level module can run in browsers, servers, and blockchains; practical I/O and rich features are provided by the embedder (browser APIs, WASI, or blockchain host functions) rather than being baked into the core format.
Wasm assumes a trustworthy embedder to enforce resource limits, expose imports, and manage side channels; if a runtime or host is poorly designed or configured, Wasm’s guarantees are limited to the abstract machine and do not automatically protect against host-level or hardware-level threats.
Standardization and tooling are addressing fragmentation - WASI provides a common vocabulary for system-like capabilities and the Component Model/WIT aims to standardize cross-language interfaces - but these efforts are modular and still evolving, so practical portability often depends on which Preview/WASI features and component-model implementations a runtime supports today.
Related reading