What is Account Abstraction?
Learn what account abstraction is, why wallets need it, and how programmable accounts enable recovery, batching, gas sponsorship, and smart accounts.
Introduction
Account abstraction is the idea of making a blockchain account’s authorization logic programmable instead of hardcoded. That sounds narrow, but it changes one of the deepest assumptions in crypto wallets: whether an account must behave like “one private key equals full control,” or whether it can enforce richer rules such as multisig approval, social recovery, spending limits, session keys, batched actions, or sponsored fees.
The reason this matters is simple. Most wallet pain comes from the fact that traditional Accounts are too primitive. If a wallet is just a keypair, losing the key is catastrophic, stealing the key is catastrophic, and improving user experience usually means adding fragile software around that key rather than changing the account’s actual rules. Account abstraction moves the rules into code, so the wallet can enforce them directly.
On Ethereum, this idea became especially important because the original account model split the world into two very different kinds of accounts. Externally owned accounts, or EOAs, are controlled by private keys and can start transactions. Smart contracts can contain arbitrary logic, but they cannot natively originate transactions in the same way. That division made wallets simple, but it also locked important wallet behavior into the protocol itself. If you wanted a wallet with custom validation, recovery, or fee payment logic, you had to work around the protocol rather than express the behavior directly.
Account abstraction tries to remove that special treatment. The core move is: an account should be able to define for itself what counts as a valid action. Once that becomes true, many wallet features that seemed like separate innovations turn out to be consequences of the same underlying change.
Why are single-key (EOA) wallets risky?
A normal key-based wallet is easy to describe because its rule is so rigid. If you can produce a valid signature from the account’s private key, the network accepts your authority. If you cannot, the network does not. That rule is clean, but it is also extremely blunt.
Here is the mechanism behind the familiar problems. Because authorization is tied to a single signing secret, security is concentrated in one object. Recovery is hard because the protocol does not know the difference between “the rightful owner lost a device” and “an attacker is trying to take over.” Spending controls are hard because the protocol does not know the difference between “a routine payment” and “an unusually large transfer.” Shared control is awkward because the protocol does not naturally express “two out of three approvals” or “phone plus hardware key” or “daily limit unless a guardian approves.”
This is why so much wallet design has historically lived outside the account itself. Developers build browser extensions, relayer systems, backup systems, co-signing servers, and interface-level warnings. Some of these are useful, but they do not change the actual rule the chain enforces. Underneath, the chain still sees a single signer with full power.
That mismatch is the real target of account abstraction. The problem is not merely that wallets need better interfaces. The problem is that the account model bakes in a narrow idea of authorization.
How does account abstraction separate user intent from authorization rules?
The simplest way to understand account abstraction is to separate two questions that are often fused together.
The first question is: what does the user want to do? Transfer tokens, swap assets, approve a contract, create an account, rotate keys, call several contracts at once.
The second question is: what conditions must be satisfied before that action is allowed? A valid ECDSA signature? A passkey assertion? Two of three guardians? A time lock? A sponsor willing to pay fees? A temporary session key that can only trade one game asset for the next hour?
Traditional wallet models tend to hardcode the second question. Account abstraction makes it programmable. Once those two questions are separated, the account can evaluate an intended action against its own rules.
That is why account abstraction is not mainly about “smart contract wallets” as a branding exercise. A smart account is just the implementation vehicle. The deeper idea is that the account’s validity conditions are no longer fixed by protocol convention alone.
An analogy helps here. A key-only wallet is like a building whose front door has exactly one lock and one rule: anyone with the master key may enter every room. Account abstraction is like replacing that with a programmable access system: some people can enter only during certain hours, some rooms require two badges, some emergencies trigger a recovery path, and some visitors are sponsored by the company rather than paying their own way. The analogy explains why flexibility improves, but it fails in one important way: blockchain rules are not managed by a central admin. They must still be enforced deterministically by network participants and paid for economically.
How do smart accounts enable recovery, batching, and sponsored fees?
| Feature | What changes | User benefit | Example |
|---|---|---|---|
| Recovery | recovery built into account | restore access without seed | guardian-approved key rotation |
| Batching | single intent, multiple calls | atomic multi-action flows | one-click approve + swap |
| Fee payment | third-party sponsorship possible | no ETH pre-funding needed | paymaster-funded onboarding |
| Signature flexibility | accept many signature schemes | lock-in UX options like passkeys | passkey-backed wallet login |
| Threshold control | distributed signature approval | avoid single-key compromise | 2-of-3 settlement scheme |
Once the account itself is code, wallet features become consequences of validation logic rather than bolt-ons.
Take recovery. In a key-only account, recovery is fundamentally foreign to the protocol because the protocol only understands possession of the private key. In a smart account, recovery can be part of the account’s own state machine. The account might accept a new signing key if three trusted guardians approve after a delay, or if a recovery process is initiated from a pre-registered device. The mechanism matters: the chain is no longer asked to infer the owner’s intentions from a lost key event. It is simply executing the account’s programmed recovery policy.
Take batching. With a conventional account, a user often signs several transactions in sequence: approve a token, then interact with an application, then perhaps clean up an allowance. With account abstraction, the account can validate one user intent and then execute multiple calls in a single flow. What changes is not just convenience. Atomicity improves because the actions can succeed or fail together under one authorization decision.
Take fee payment. In a traditional model, the sender usually needs the chain’s native gas token. Under account abstraction, a third party can sponsor execution, or the account can coordinate fee payment through custom logic. On Ethereum’s ERC-4337 path, this is done using paymasters, contracts that agree to cover gas for a user operation subject to their own validation rules and deposits.
Take signatures themselves. If an account is programmable, it does not need to be limited to a single signature format. The validation logic can accept multisig approvals, passkeys, aggregated signatures, hardware-backed attestations, or rotating session keys. The protocol no longer insists that every user experience reduce to the same key check.
A concrete real-world pattern is threshold control over high-value actions. Cube Exchange, for example, uses a 2-of-3 Threshold Signature Scheme for decentralized settlement: the user, Cube Exchange, and an independent Guardian Network each hold one key share; no full private key is ever assembled in one place; and any two shares are required to authorize a settlement. This is not identical to every account-abstraction design, but it shows the same principle in practice: authorization can be distributed and programmable instead of concentrated in one raw secret.
Why does Ethereum rely on ERC-4337 for account abstraction?
Ethereum made account abstraction both appealing and difficult. Appealing, because wallets clearly wanted richer behavior than EOAs could offer. Difficult, because changing how transactions work at the protocol layer is invasive. If the base protocol expects a particular transaction format and signature check, replacing that assumption is a hard coordination problem.
That is why there are two broad implementation routes discussed in Ethereum’s ecosystem. One route changes the protocol so externally owned accounts gain more flexible behavior. Another route builds a parallel transaction flow above the protocol. The most important deployed version of the second route is ERC-4337.
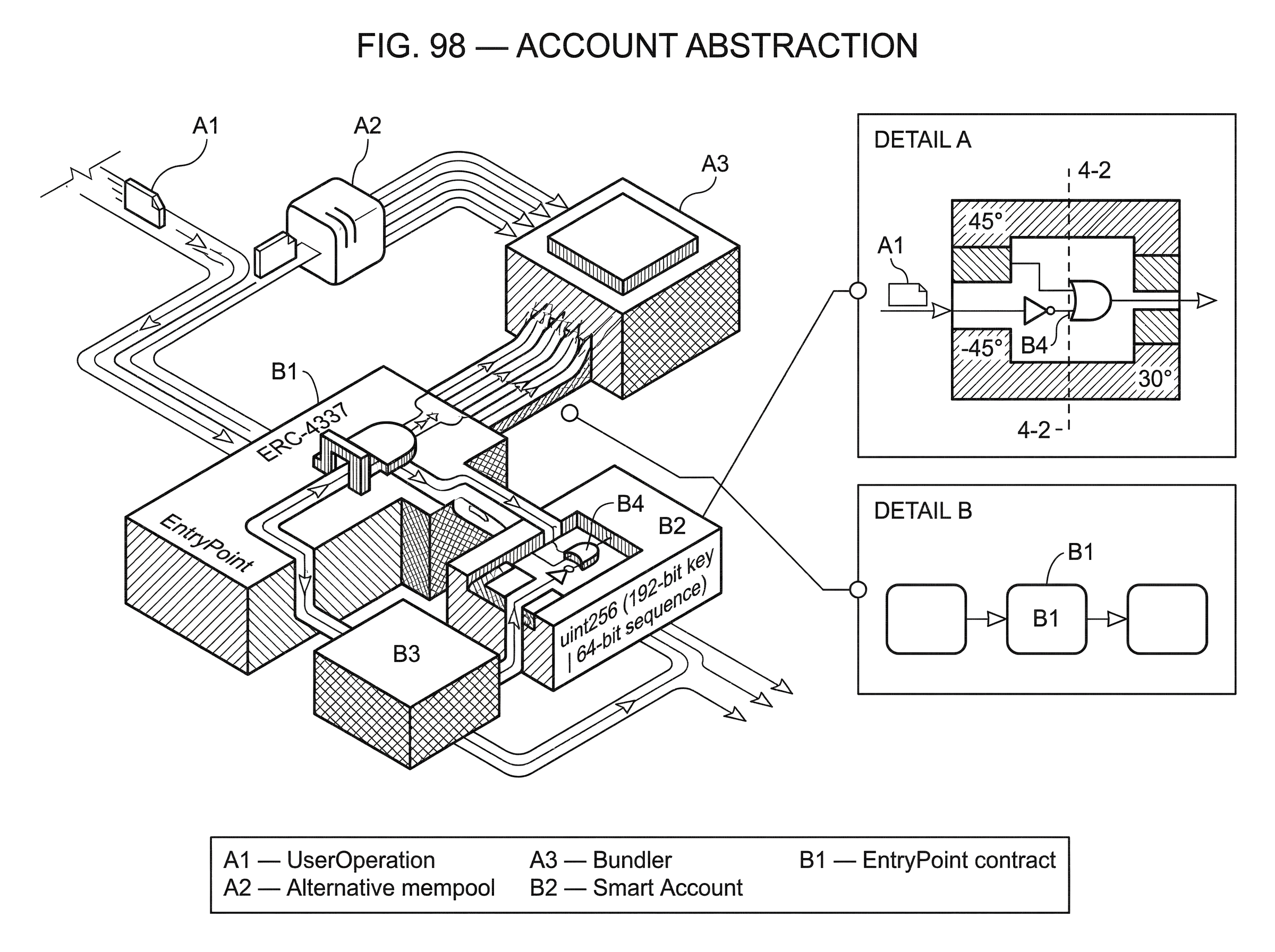
ERC-4337 is crucial because it delivers account abstraction without consensus-layer changes. Instead of asking Ethereum itself to recognize a brand-new native transaction type for smart accounts, it introduces a higher-layer object called a UserOperation. Users send UserOperations into a separate mempool, specialized actors called bundlers collect them, and a shared EntryPoint contract verifies and executes them on-chain.
This design is pragmatic. It says, in effect: if the base protocol will not yet treat programmable accounts as first-class transaction senders, we can still get most of the behavior by wrapping user intent in a transaction-like object and processing it through contracts plus off-chain infrastructure. That is the compression point for understanding modern Ethereum account abstraction: the protocol is not fully abstracted, so the abstraction is built one layer up.
How does ERC-4337 process UserOperations step by step?
| Actor/Artifact | On-chain? | Core role | Economic risk |
|---|---|---|---|
| UserOperation | No (alt mempool) | structured user intent | malleable mempool exposure |
| Bundler | No (off-chain actor) | simulate and bundle operations | loss from invalid inclusions |
| EntryPoint | Yes (contract) | verify then execute ops | critical contract compromise |
| Smart Account | Yes (account contract) | validate signatures and policy | buggy validation exploit |
| Paymaster | Yes (contract) | sponsor gas per policy | fund drain or griefing |
A UserOperation is not an Ethereum transaction in the protocol’s native sense. It is a structured message describing what a smart account wants to do and how it expects validation and fee payment to be handled. The struct includes fields such as the sender, nonce, optional account-creation code, call data, gas limits, fee fields, optional paymaster data, and a signature. The signature must depend on both the chainId and the EntryPoint address so it cannot be replayed across chains or across different entry point contracts.
That detail reveals something important: in account abstraction, “the signature” is no longer a universal protocol object. ERC-4337 explicitly leaves the meaning of the signature field to the account’s own validation logic. The protocol-like infrastructure carries the bytes, but the account decides what they prove.
The EntryPoint contract is the on-chain coordinator. Bundlers submit a transaction that calls handleOps on the EntryPoint with a batch of UserOperations. The EntryPoint then performs two broad phases: verification and execution.
During verification, it may create an account if the UserOperation includes initialization code. It asks the account to validate the operation by calling the account’s validateUserOp function. If a paymaster is involved, it validates the paymaster path too and checks that the relevant deposits exist. During execution, it performs the requested call for each operation, accounts for gas, applies penalties for certain forms of unused reserved gas, and pays the bundler’s designated beneficiary from the collected fees.
A worked example makes this easier to see. Imagine a new user opens an app and wants to swap tokens, but has no ETH for gas. The app generates a UserOperation whose initCode can deploy the user’s smart account if it does not already exist. The operation’s call data says, in effect, “after validation, execute this swap through the target contracts.” Because the user has no ETH, the operation also names a paymaster willing to sponsor fees if the request matches that paymaster’s policy. The user signs according to the smart account’s scheme; perhaps not with a plain EOA signature at all, but with passkey-backed credentials interpreted by the wallet contract.
Off-chain, a bundler receives the UserOperation and simulates it. This simulation matters because bundlers do not want to pay real gas for invalid or malicious operations. If the simulation shows that the account would validate correctly, that the paymaster would accept responsibility, and that execution appears valid under local policy rules, the bundler places the operation into a bundle. On-chain, the EntryPoint may first deploy the account, then call validateUserOp, then validate the paymaster, then execute the swap, then settle fees. The user experiences “create wallet and swap in one action,” but mechanically that smooth experience is built from a carefully staged validation and execution pipeline.
What role do bundlers and alternative mempools play in ERC-4337?
A natural question is why bundlers need to simulate if the EntryPoint will validate again on-chain anyway. The answer is economic. The on-chain validation is the final authority, but by the time it runs, someone is already paying gas for inclusion. Bundlers therefore need strong off-chain filtering to avoid being griefed by invalid operations, expensive reverts, or denial-of-service patterns.
This is why ERC-4337 uses an alternative mempool rather than the normal transaction mempool. UserOperations need specialized handling. Bundlers must simulate validation, often enforce local or shared policy rules, and reason about entities like factories, paymasters, and signature aggregators that do not exist in ordinary transaction handling.
The specification intentionally leaves parts of this system open. The canonical UserOperation mempool rules and the shared validation restrictions are not fully specified in the base EIP; implementers have to define them. Related work such as ERC-7562 is recommended for reputation and DoS mitigation. That openness is useful for iteration, but it also means that “ERC-4337 support” includes real implementation choices, not just a single universal behavior.
This is an important place where smart readers often misunderstand the design. They hear “account abstraction” and imagine a pure on-chain feature. But the practical system is hybrid. Some guarantees come from contracts, some from off-chain simulation, some from mempool policy, and some from the economic incentives of bundlers and paymasters.
How does ERC-4337 handle nonces and parallel operation lanes?
Traditional accounts usually have a simple sequential nonce: transaction 8 must follow transaction 7. ERC-4337 relaxes this model without discarding replay protection. Its nonce is still a single uint256, but conceptually it is split into a 192-bit key and a 64-bit sequence.
Why does that matter? Because smart accounts often want parallel channels of authorization. A wallet might want one stream of operations for routine user actions, another for administrative recovery, another for a temporary session key. If all of them had to compete for one global sequence number, unrelated actions would block each other.
The semi-abstracted nonce design preserves the invariant that each authorized operation must be unique, while allowing the account to choose multiple ordering lanes. This is a good example of what account abstraction usually does at its best: it keeps the fundamental safety property, but loosens the surrounding convention so accounts can express more useful behavior.
How do paymasters enable sponsored transactions and what are their limits?
| Sponsorship model | Requirement | User friction | Main risk |
|---|---|---|---|
| First-time onboarding | paymaster policy match | no ETH needed | unexpected sponsor cost |
| Token-charged sponsorship | token balance or off-chain billing | requires token approval | pricing mismatch |
| App-restricted sponsorship | app allow-list or contract checks | limited to partner apps | abuse of sponsorship |
| Pay-per-use billing | per-op metering and accounting | requires billing agreement | billing estimation errors |
Fee payment is where account abstraction becomes visible even to users who do not care about wallet architecture. A user may ask a simple question: “Why do I need ETH just to use this app once?” Paymasters are one answer.
In ERC-4337, a paymaster is a contract that agrees to pay for a UserOperation instead of the sender. But the key point is not merely sponsorship. The key point is that sponsorship itself becomes programmable. A paymaster can define policies such as sponsoring first-time users, charging the user off-chain, requiring a token balance, restricting supported applications, or attaching custom data and signatures through paymasterAndData.
The mechanism, however, creates new risks. A paymaster needs deposits at the EntryPoint. It may need stake under local reputation rules. It must validate requests carefully and sometimes handle post-execution accounting through postOp. The JSON-RPC standard for ERC-4337 notes that some gas values, especially actual postOpGasLimit, cannot be reliably estimated off-chain and must be enforced carefully by paymasters on-chain.
So gas abstraction is real, but it is not magic. Someone still pays, and the system still needs a robust way to decide when sponsorship is valid and how abuse is prevented.
What are the security risks and trust assumptions of account abstraction?
Account abstraction improves wallet flexibility, but it does not eliminate trust boundaries. It moves them.
The most important trust boundary in ERC-4337 is the EntryPoint. The whole design depends on accounts trusting a particular EntryPoint contract to enforce validation before execution. The EIP is explicit that this contract is critical and must be audited and formally verified. If the EntryPoint were buggy or malicious, the safety of all dependent accounts could fail in correlated ways.
This is not merely theoretical. Security reviews of the reference implementation found issues such as excessive gas consumption from large revert reasons and subtle risks around aggregation and paymaster signing formats. Those findings were addressed in follow-up changes, but they illustrate the basic point: centralizing validation machinery in a shared contract creates a concentration point for security review.
Implementation mistakes at the wallet layer matter too. A disclosed UniPass vulnerability showed how a smart-account module could be taken over when several mistakes combined: empty-signature validation success, permissive default permission handling, and faulty module installation that omitted required permission setup. The exploit’s deeper lesson was not that account abstraction is uniquely unsafe. It was that programmable authorization is only as safe as the code expressing it. When an account’s rules become more flexible, auditing those rules becomes more important, not less.
There is also an architectural subtlety here. In a key-only account, the protocol defines the authorization rule and every wallet inherits it. In account abstraction, wallet behavior can differ materially across implementations. Some of that diversity is a feature; it enables innovation. But some of it means users and integrators must care more about which account implementation they are actually using.
How do Cosmos, Solana, and Substrate implement programmable authorization?
The core idea is broader than Ethereum’s ERC-4337 design. What varies across chains is not whether programmable authorization is useful, but where the chain gives you the leverage to implement it.
In Cosmos SDK systems, modules such as x/authz and x/feegrant let one account grant another account specific execution privileges or fee-paying rights. That is not the same mechanism as ERC-4337, but it expresses the same underlying principle: the signer, the authorized actor, and the fee payer do not have to collapse into one identity. x/authz can define what delegated messages are allowed, while x/feegrant lets one account cover fees for another. The result is a form of account abstraction through modular authorization and fee delegation rather than a shared smart-account entry point.
On Solana, the account model is different again. Accounts are fundamental state objects, and only an account’s owner program can modify its data or debit its lamports. That means smart-account behavior has to be designed around program ownership, program-derived addresses, and rent constraints. The implementation shape differs, but the same question reappears: can authorization be expressed as programmable logic rather than a single raw key?
On Substrate-based systems, multisig dispatch provides yet another pattern. A composite origin can be derived from multiple signers and a threshold, letting a call be dispatched from that combined authority. This is not cryptographic threshold signing, and it is not ERC-4337, but it shows that abstracting “who may act” away from one key is a recurring design goal across blockchain architectures.
Even within EVM ecosystems, account abstraction is not limited to Ethereum mainnet.
Infrastructure and SDKs on networks such as Avalanche expose ERC-4337 and related tooling because the abstraction lives mostly above consensus and can travel wherever the execution model is compatible.
- bundlers
- paymasters
- smart-wallet frameworks
- sponsored transactions
What are the trade-offs between programmable authorization and simple key models?
The promise of account abstraction is easy to state: better security and better UX. The tradeoff is subtler: you are replacing a simple, rigid trust model with a more expressive but more layered one.
Some parts of that new system are fundamental. An account must still have a replay-protection mechanism. Someone must still pay execution costs. Validation must still be deterministic enough for the network to enforce. Those are not optional.
Other parts are conventions or design choices. Whether account abstraction is done through a protocol-level transaction type or a higher-layer flow like ERC-4337 is a design choice. Whether sponsorship is handled by a paymaster, a centralized relayer, or a delegated fee module is a design choice. Whether recovery is guardian-based, institution-assisted, or threshold-controlled is a design choice.
The fundamental insight is stable across all of them: authorization should be a programmable policy, not a hardcoded property of a keypair.
Once you see that clearly, many adjacent ideas fall into place. Smart accounts are the concrete accounts that embody those policies. ERC-4337 is one major implementation route on Ethereum. Threshold signing, delegated authorization, session keys, fee sponsorship, and recovery mechanisms are not separate trends so much as different expressions of the same change.
Conclusion
Account abstraction turns a wallet from a key container into a rule-enforcing account. Instead of asking the chain to trust one private key with total authority, it lets the account define what valid authority looks like.
That single shift explains why account abstraction can support recovery, batching, sponsored fees, passkeys, multisig, and richer application flows. It also explains the cost: more moving parts, more implementation choices, and more code that must be designed and audited carefully.
If you remember one thing tomorrow, remember this: account abstraction is not mainly about hiding blockchain complexity from users. It is about moving the rules of control from fixed protocol assumptions into programmable accounts.
How do you secure your crypto setup before trading?
Account Abstraction belongs in your security checklist before you trade or transfer funds on Cube Exchange. The practical move is to harden account access, verify destinations carefully, and slow down any approval or withdrawal that could expose you to this risk.
- Secure account access first with strong authentication and offline backup of recovery material where relevant.
- Translate Account Abstraction into one concrete check you will make before signing, approving, or withdrawing.
- Verify domains, addresses, counterparties, and approval scope before you confirm any sensitive action.
- For higher-risk or higher-value actions, test small first or pause the workflow until the security check is complete.
Frequently Asked Questions
ERC-4337 avoids changing Ethereum’s consensus rules by introducing a higher-layer object called a UserOperation that flows through an alternative mempool to specialized bundlers; those bundlers submit batches to a shared on‑chain EntryPoint contract which verifies and executes the operations, letting smart accounts define their own validation logic without a protocol-layer transaction type change.
A paymaster is a contract that agrees to cover gas for a UserOperation according to its own policy; this enables sponsored or token‑denominated UX but does not remove the need for someone to pay gas - paymasters must hold deposits at the EntryPoint and handle complex on‑chain/off‑chain validation (including supplying postOpGasLimit), which creates additional attack and accounting surfaces.
Bundlers are off‑chain actors that collect UserOperations from an alternative mempool and simulate them before including them on‑chain so they do not pay gas for invalid or malicious operations; the off‑chain simulation is an economic filter because the EntryPoint’s on‑chain validation happens only after someone already pays for inclusion.
Account abstraction shifts the primary trust boundary from a single private key to the code and coordinated infrastructure that enforce validation - most notably the shared EntryPoint contract in ERC‑4337 - so correctness and audits of that contract and of wallet/account code become critical, and implementation bugs (e.g., UniPass module issues) can lead to takeover risks if combined mistakes occur.
No - account abstraction can remove the user’s need to personally hold ETH only in the sense that a paymaster can sponsor a transaction, but someone (the paymaster or another actor) still pays gas and the system requires deposits, validation rules, and protections to prevent abuse; gas abstraction is therefore programmable but not magical.
ERC‑4337 preserves replay protection and operation uniqueness while allowing multiple parallel ordering lanes by structuring its nonce as a 192‑bit key plus a 64‑bit sequence, enabling separate streams (e.g., routine actions, recovery flows, session keys) without blocking unrelated operations on one global sequential nonce.
Different chains implement the same basic idea in different places: Cosmos achieves delegated execution and fee delegation via modules like x/authz and x/feegrant, Solana relies on owner programs, PDAs and rent rules to express authority, and Substrate pallets provide multisig composite origins - the principle of programmable authorization is shared but the concrete mechanisms and constraints differ by chain.
Related reading