What Is an Ethereum Validator?
Learn what Ethereum validators are, how they stake ETH, attest and propose blocks, earn rewards, face slashing, and handle withdrawals.
Introduction
Ethereum validators are the participants that keep Ethereum’s proof-of-stake system running by locking up ETH, signing protocol messages, and helping the network agree on which blocks are valid. That sounds simple, but the interesting part is why Ethereum needs a special role for this at all: once Ethereum stopped relying on proof-of-work miners, it still needed some way to decide who gets to propose blocks, who checks them, and what happens when those participants are offline or dishonest. Validators are the answer.
The core idea is not “a validator is a server.” A validator is better understood as a staked identity inside the consensus protocol. That identity has a public key, a balance, assigned duties, and rules about what it may and may not sign. The server you run, the consensus client you choose, and the signer that holds your key are all implementation details around that protocol identity.
This distinction matters because Ethereum’s design is trying to solve two problems at once. It needs a large number of participants for decentralization, but it also needs those participants to coordinate tightly enough to finalize blocks. The consensus specifications explicitly aim to support large validator participation while keeping hardware requirements low enough that a consumer laptop can participate as a node. Much of the validator design (from BLS signatures to attestation aggregation to churn-limited activation) exists to make those two goals compatible.
What do Ethereum validators actually do (attest vs propose)?
| Duty | Frequency | Selected / Assigned | Purpose | Main network effect |
|---|---|---|---|---|
| Attestation | Frequent (per epoch) | Committee assignment | Vote on head and target | Enables fork choice and finality |
| Proposal | Rare (per slot) | Proposer selection | Package execution payload into block | Introduces new blocks for attestations |
A blockchain needs a repeated answer to a narrow question: what is the next canonical state of the chain? In Ethereum proof of stake, validators answer that question by making signed statements at well-defined times. Most of the time, a validator is not creating a block. Most of the time, it is attesting; saying, in effect, “this is the block and chain view I consider valid for this slot and epoch.” Occasionally, when selected, it also proposes a block.
That division of labor is the first thing many readers miss. If you imagine every validator constantly producing blocks, Ethereum’s validator set would be unmanageable. Instead, the protocol separates rare proposal opportunities from frequent attestations. The Phase 0 validator spec describes these as the two primary responsibilities: proposing blocks when selected for a slot, and creating attestations, typically once per epoch for assigned committees.
The mechanism behind this is time-structured consensus. Ethereum organizes time into slots and epochs. At each slot, one validator may be chosen to propose a block, while many others are assigned to committees that attest to what they saw. Those attestations do two things at once. They help the network choose a head chain in the short term, and, when enough accumulate consistently, they help the chain reach stronger finality.
So the validator’s job is not generic “validation.” It is timed, signed participation in fork choice and finality. That is why an Ethereum validator is a protocol object with strict signing rules, not just a node that passively checks transactions.
How do you become an Ethereum validator (deposits, activation, churn)?
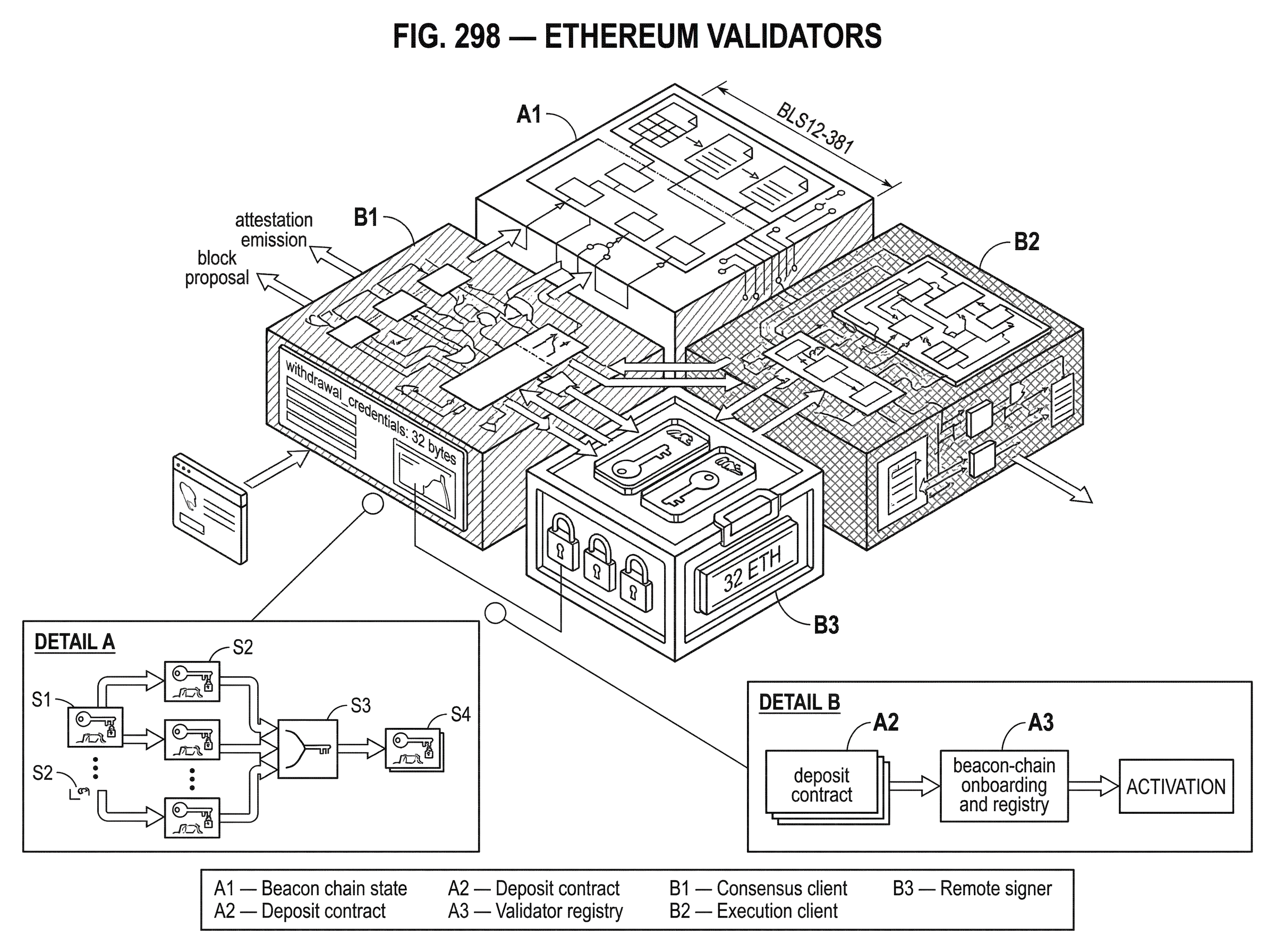
An Ethereum validator starts with a deposit. The canonical entry point is the deposit contract on the execution chain. A depositor sends ETH to that contract and supplies deposit data including a BLS public key, Withdrawal credentials, a signature, and a deposit data root. The contract emits a DepositEvent, and the beacon chain later processes that information.
This is one of the cleaner examples of Ethereum’s split architecture. The money enters through the execution layer, but the validator lives on the consensus layer. The deposit contract intentionally does only minimal validation. In particular, it does not perform all of the onboarding checks itself; much of that logic is deferred to the beacon chain. That keeps the contract simpler and pushes validator admission logic into consensus rules, where it can be reasoned about alongside the rest of validator state.
A validator is not activated the moment ETH is sent. Deposits must first be observed and incorporated into beacon-chain state, and activation is further limited by the protocol’s validator churn rules. The specs emphasize that this timing is variable: deposit processing is delayed by the way Eth1 data is incorporated, and activation itself depends on how many validators are already waiting to join and how much churn is allowed per finalized epoch. In other words, staking creates a claim on future validator status; it does not instantly create an active validator.
There is also an important threshold condition. Deposits for the same public key are treated as belonging to the same validator, and activation only occurs once the total deposited amount for that public key reaches the protocol’s maximum effective balance threshold. In practice, this is why Ethereum validators are commonly discussed as 32 ETH units: the protocol treats validator participation in fixed-size chunks rather than as arbitrary stake accounts.
How do validator keys, balances, and withdrawal credentials work?
The simplest useful mental model is that a validator has three distinct concerns: signing, balance accounting, and withdrawal destination. Ethereum keeps these related, but not identical.
For signing consensus messages, validators use BLS12-381 public keys and signatures. This is not a cosmetic choice. Ethereum needs hundreds of thousands of validators to attest regularly without overwhelming bandwidth and verification costs. BLS signatures are attractive here because many signatures on the same message can be aggregated compactly. The consensus specs explicitly include extensions for aggregate public keys and aggregate verification, because this aggregation property is part of what makes large validator participation practical.
The validator also has a balance tracked by the beacon chain. Rewards and penalties modify that balance over time. But the balance that matters for duty weight is not simply “whatever ETH sits there right now” in a naive sense. Ethereum uses an effective balance abstraction to smooth some behavior and keep incentive accounting manageable. The evidence you provided does not require going into every numeric detail, but the key idea is that duty assignment and rewards are tied to protocol-defined validator balances, not directly to a wallet’s spendable ETH.
Then there are withdrawal credentials. These tell the protocol where withdrawals are meant to go. The withdrawal_credentials field is 32 bytes, and its first byte is a prefix that determines how the rest should be interpreted. The supported forms described in the specs include a BLS-based withdrawal key prefix and an execution-address prefix. This separation is conceptually important: the key used to sign attestations and proposals does not have to be the same as the authority that ultimately controls withdrawals.
That separation is not just elegance. It is a risk-management tool. It lets operators keep a hot signing key online for validator duties while holding more sensitive withdrawal authority more carefully. It also explains some of the operational complexity introduced later by withdrawals.
How do validator attestations work (committees, subnets, aggregation)?
Attesting is where Ethereum validators spend most of their lives. An attestation is a signed statement about the validator’s view of the chain at a particular slot and epoch. Rather than every validator broadcasting independently to the whole network in the same way, the protocol organizes validators into committees and maps those committees onto attestation subnets.
Here is the mechanism in plain language. For a given slot, the protocol assigns a validator to a committee. The validator observes the beacon chain, determines the block and checkpoint information it should attest to, signs the attestation, and broadcasts it on the appropriate attestation subnet. Other participants in the same committee are doing the same thing. This is not merely gossip for its own sake; the network structure is designed so that attestations can be distributed efficiently without every node needing every raw attestation immediately.
Then aggregation happens. Some validators are selected as aggregators using a slot-based selection proof derived from a signature. An aggregator collects attestations from the committee, combines them, and broadcasts a SignedAggregateAndProof on a global aggregate channel. This is where BLS aggregation matters mechanically rather than abstractly. If Ethereum required every attestation to remain standalone all the way through processing, large validator counts would put far more pressure on networking and verification.
A concrete example makes this easier to picture. Imagine your validator is assigned to a committee for a given slot. Your validator client asks the beacon node for the duty, constructs the attestation for the head and target it sees, signs it with your validator key, and sends it to the committee’s subnet. If your validator also happens to be selected as an aggregator for that slot, it does something extra: it listens for the other committee members’ attestations, combines compatible ones into an aggregate, produces the proof showing it was eligible to aggregate, and broadcasts that aggregate for wider consumption. The point of this extra step is not prestige; it is bandwidth compression in service of scalable consensus.
How do Ethereum validators propose blocks after the Merge?
Proposing a block is the other major validator duty, but it only makes sense in post-Merge Ethereum if you understand that validators now sit at the seam between the consensus layer and the execution layer.
Before the Merge, block production and execution were bundled under proof of work. EIP-3675 changed that by deprecating proof of work and replacing it with beacon-chain-driven proof of stake. After the transition, the consensus layer determines which block should be proposed and accepted, while the execution layer still handles transaction execution and EVM state transitions. A proposer therefore does not invent a block from nothing. It coordinates with an execution engine to obtain an execution payload and wraps that payload into a beacon block.
This is why validator operation depends on both a consensus client and an execution client. The consensus specs and execution APIs together define the bridge between them. If the validator is selected as proposer for a slot, its software prepares the block body, obtains the execution payload from the execution engine, and publishes the resulting block for attestation by others.
Capella made this seam even more visible by adding withdrawals into the execution payload flow. The validator-side Capella spec notes that get_payload returns the upgraded ExecutionPayload type, and that payload attributes now include expected withdrawals derived from consensus-layer state. So a proposer is not merely packaging user transactions. It is also carrying protocol-level outcomes (such as validator withdrawals) from the consensus layer into the execution layer.
Why does Ethereum slash validators and how do rewards and penalties work?
| Behavior | Description | Consequence | Severity | Mitigation |
|---|---|---|---|---|
| Honest | Correct, timely participation | Earns rewards | None | Normal operation & monitoring |
| Offline | Missed duties | Reduced rewards | Low–Medium | Redundancy and alerts |
| Equivocation | Signing conflicting messages | Stake slashed and exit | High | Slashing-protection and cautious failover |
If validators only earned rewards for honest behavior but faced no meaningful penalty for contradictory behavior, Ethereum’s proof-of-stake security would be weak. A participant could sign multiple conflicting views of history at little cost. Slashing exists to make certain forms of equivocation expensive enough that the protocol can rely on signed votes as real commitments.
The clean way to think about this is that Ethereum distinguishes between being absent and being contradictory. If a validator is offline, misses attestations, or fails to perform duties, it is penalized, but this is generally a liveness problem. The validator is failing to help. Slashing is reserved for more serious safety violations; signing messages that should never both be signed by the same validator.
In the Phase 0 validator guidance, the two slashing paths are proposer slashing and attester slashing. At a high level, a validator must not sign conflicting blocks for the same proposal opportunity, and it must not sign conflicting or surround-voting attestations. If it does, part of its stake can be burned and it is ejected from the active validator set.
That is why operator practice focuses so heavily on slashing protection. The spec guidance explicitly recommends persisting signed-message records to disk so a validator does not accidentally double-sign after restart or failover. This concern became important enough that Ethereum standardized a slashing-protection interchange format in EIP-3076, so operators can export and import signing history when switching clients. The underlying principle is simple: if your validator key moves between machines or software stacks without a trustworthy memory of what it already signed, the protocol cannot tell the difference between operator error and malicious equivocation.
How do validator withdrawals work after Capella and EIP-4895?
For a long time, staking ETH meant locking it into the validator system without ordinary execution-layer withdrawal. Capella, together with EIP-4895 on the execution side, changed that.
The key design choice in EIP-4895 is that validator withdrawals are pushed from the beacon chain into the execution layer as a system-level operation. They are not user-submitted transactions. A Withdrawal object contains an index, a validator index, a recipient address, and an amount in Gwei. Execution payloads gained a withdrawals field, and execution payload headers gained a withdrawals_root commitment. These withdrawals are processed after user transactions, increase account balances unconditionally, and must not fail.
That mechanism tells you something important about Ethereum’s architecture. Withdrawals are not modeled as a validator “sending a transaction to claim funds.” They are modeled as the consensus layer deciding that certain balances should reappear on the execution layer, and then forcing the execution layer to reflect that decision deterministically. This keeps withdrawal logic rooted in validator state transitions rather than turning it into another category of user action.
Capella also changed validator operations in a practical way. Exited validators can have their full balance withdrawn automatically, while active validators can have the portion above the maximum effective balance withdrawn periodically. But this automatic flow depends on withdrawal credentials pointing to an execution-layer address. Validators that still had BLS-withdrawal credentials needed to submit a one-time BLSToExecutionChange, signed by the withdrawal BLS secret key, to switch to execution-address credentials. The spec is explicit that this change is one-way and should be handled carefully.
What software do validator operators run (consensus client, execution client, remote signer)?
| Component | Role | Required post‑Merge? | Security risk | Typical mitigation |
|---|---|---|---|---|
| Consensus client | Beacon state, duties, attestations | Yes | Desync or missed/invalid duties | Keep updated; monitor and alert |
| Execution client | Provide execution payloads to proposer | Yes | Bad or incompatible payloads | Version compatibility checks |
| Remote signer | Hold BLS keys and sign | Optional (recommended) | Key compromise or double-signing | HSMs, EIP-3030, slashing-protection |
A validator in the protocol sense is just state plus keys plus rules. To make that state actually participate, operators run software around it. At minimum, this means a consensus client and, after the Merge, an execution client. In practice, many setups also separate signing into a dedicated remote signer.
This separation exists because the risks are different. A consensus client needs to stay in sync with the beacon chain, compute duties, and react quickly. An execution client needs to validate and serve execution payload data. A signer’s job is narrower: hold the validator’s BLS secret key and produce signatures when asked. EIP-3030 standardizes a minimal HTTP API for such a remote signer, with endpoints for status, key listing, and signing requests.
The remote-signer design makes a useful point about what is fundamental and what is convention. The protocol fundamentally requires valid signatures from the correct validator keys. It does not fundamentally require those keys to sit in the same process as the validator client. So operators can move signing into tools such as Web3Signer or hardware-backed systems, reducing exposure of hot keys. But the EIP also leaves authentication, transport security, and key management outside the protocol standard, which means real deployments must solve those operationally.
Client docs such as Prysm and Teku show the same pattern at an implementation level. They provide the runbooks for installing beacon nodes and validator clients, monitoring them, importing keys, exporting slashing-protection data, migrating to new machines, and integrating remote signers. These are not side concerns. They are where many validator failures actually happen, because protocol correctness depends on operator setups that avoid downtime and, more importantly, avoid contradictory signing.
How can Ethereum scale to hundreds of thousands of validators?
One design goal stated in the consensus specs is to allow large participation of validators. That is harder than it sounds. If every validator had to independently flood the entire network with every vote, or if every validator required heavyweight hardware, Ethereum would push toward centralization.
Several mechanisms work together to avoid that outcome. BLS signatures make aggregation efficient. Committees and attestation subnets localize message propagation before global aggregation. The protocol structures time so validators mostly attest rather than constantly propose. Hardware goals are kept intentionally modest. And validator admission is rate-limited through churn, which helps the protocol manage changes to the active set.
This is also where Ethereum differs from some other proof-of-stake systems in emphasis. Many PoS chains have validators, but not all aim for Ethereum’s combination of very large validator counts, signature aggregation, and client-diverse, consumer-accessible operation. The general idea of “stake as collateral for block production and voting” is shared across chains. The specific machinery of BLS attestation aggregation, withdrawal credentials, deposit-contract onboarding, and consensus/execution separation is distinctively Ethereum.
There are also alternative operational models built around the same base validator concept. Pooled staking systems such as Lido rely on node operators to run validator infrastructure on behalf of a broader staking pool, while distributed-validator approaches such as SSV use key-splitting across operators to reduce single-operator risk. Those models do not redefine what a validator is at the protocol level. They change who operates the validator and how the key material is managed.
What operational risks cause validator failures in practice?
The clean protocol story is that a validator is rewarded for correct participation and penalized for absence or equivocation. In practice, several assumptions have to hold.
The first is that the software stack behaves consistently across forks.
The Ethereum consensus specs are maintained per upgrade because validator behavior is not frozen forever.
- Phase 0
- Altair
- Bellatrix
- Capella
- Deneb
- Electra
- Fulu
- so on
Duties and data structures evolve. Operators therefore do not run “Ethereum validator software” in the abstract; they run specific client versions that implement the current fork rules.
The second is that signing infrastructure is disciplined. Running two active instances of the same validator key, restoring an old backup without current slashing history, or migrating clients carelessly can create slashable behavior even when each machine seems individually healthy. This is why slashing protection is not just a nice feature. It is the memory that makes a validator identity safe across time and across software boundaries.
The third is that access to rewards and withdrawals depends on correct credential management. The separation between validator signing keys and withdrawal credentials is powerful, but it also introduces irreversible steps, especially around BLSToExecutionChange. A carefully designed separation of duties can reduce risk; a poorly documented key ceremony can permanently strand funds or route them incorrectly.
So the idea of “just stake 32 ETH and run a node” is directionally true, but mechanically incomplete. Ethereum validators are secure only when the protocol rules, client implementations, and operator procedures line up.
Conclusion
An Ethereum validator is a staked protocol identity that signs timed consensus messages.
Everything else exists to support that identity safely at scale.
- deposits
- clients
- remote signers
- withdrawals
- slashing protection
The memorable version is this: validators are how Ethereum turns ETH into credibility. By requiring collateral, assigning duties, aggregating signatures, and punishing contradictions, the protocol makes each validator’s signature costly enough to trust and cheap enough to use thousands of times per minute across a very large network.
How do I get practical exposure to Ethereum (ETH) after learning about validators?
Buy ETH on Cube Exchange to get direct exposure to the protocol after you learn about validators. The simplest path is to acquire spot ETH on Cube and either hold it as exposure to the network or withdraw it to an external wallet if you want to run or delegate to a validator.
- Fund your Cube account with fiat via the on‑ramp or by transferring a supported stablecoin (for example, USDC) to your Cube deposit address.
- Open the ETH/USDC market on Cube and pick an order type; use a limit order to control price or a market order for immediate execution.
- Enter the ETH amount or USDC spend, review the estimated fees and slippage, then submit the order.
- If you need staking exposure, withdraw ETH to your external wallet and deposit it to the staking service or validator setup you choose, or trade your ETH for a listed liquid staking token on Cube if available.
Frequently Asked Questions
Ethereum uses BLS12-381 signatures so many validators’ signatures on the same message can be aggregated into a single compact proof, which greatly reduces bandwidth and verification costs and makes very large validator sets practical.
There is no fixed delay; a deposit must be observed by the beacon chain and activation is further rate-limited by the protocol’s churn limits and Eth1-related follow distances, so activation latency is variable and can be slow depending on queue length and finality.
Being absent (offline or missing duties) incurs penalties that reduce rewards and hurt liveness, while slashing is applied for contradictory or equivocal signatures (double-signing or surround votes) and leads to larger stake burns and ejection; slashing exists to make equivocation economically costly.
Yes - after Capella and EIP-4895 withdrawals are produced by the consensus layer and pushed into the execution layer as unconditional Withdrawal objects processed in execution payloads; note that withdrawals only reach an execution address when withdrawal_credentials point to an execution address or after you submit a one‑time BLSToExecutionChange using the withdrawal BLS key.
Running the same validator key on two machines can cause slashable double-signing; operators prevent this by using persistent slashing-protection records and exporting/importing them when migrating keys - EIP-3076 defines a slashing-protection interchange format to help with safe client changes.
The protocol treats validator participation in fixed-size chunks (commonly discussed as 32 ETH) so deposits for the same public key are aggregated until the validator’s effective balance reaches the maximum effective balance threshold before activation.
A remote signer is a separate process that holds BLS keys and signs on demand; the remote-signer API (EIP-3030 and implementations) standardizes signing calls but intentionally omits authentication and key lifecycle management, so operators must provide transport security and access controls themselves.
Attestations are produced by committee members for slots, gossiped on attestation subnets, and some validators selected as aggregators combine compatible attestations into a single SignedAggregateAndProof to compress bandwidth and enable scalable verification.
Yes - the signing key used for attestations/proposals can be different from where withdrawals go; the withdrawal_credentials field encodes the withdrawal destination and operators often keep a hot signing key separate from a more protected withdrawal authority, but switching from BLS withdrawal credentials to an execution address requires a one-time BLSToExecutionChange signed by the withdrawal BLS key and is irreversible.
Related reading