What is MEV?
Learn what MEV is, how transaction ordering creates value in DeFi, why it leads to arbitrage and sandwich attacks, and why it matters for blockchain security.
Introduction
MEV is the value that can be extracted from controlling the order, inclusion, or exclusion of transactions in a block. It matters because blockchains do not just execute transactions; they also decide which transactions run first, which run later, and which never run at all. In DeFi, where prices, liquidations, and arbitrage opportunities change from one transaction to the next, that ordering right is often worth real money.
This is the point that makes MEV click: a blockchain is not only a settlement machine, but also an ordering machine. If two trades interact with the same liquidity pool, the result depends on sequence. If a loan becomes undercollateralized, the first liquidator wins. If two exchanges momentarily disagree on price, the first arbitrage transaction captures the spread. Once ordering affects outcomes, the party that can influence ordering has something scarce to sell or exploit.
That is why MEV shows up wherever smart contracts are stateful and composable. It is not a bug in one protocol, and it is not limited to Ethereum, even though Ethereum is where most of the early analysis and tooling emerged. It is a structural consequence of public transaction visibility, shared state, and privileged block construction.
Why does MEV exist and how does it arise?
To see why MEV exists, start with a simple contrast. In a traditional database, the operator controls transaction ordering by design. In a blockchain, we often talk as if ordering were neutral: users submit transactions, validators include them, and the chain advances. But that neutrality is only partial. Someone still has to assemble the next block, and that actor has discretion.
The formal definition used in Ethereum documentation is close to this: MEV is the maximum value extractable from block production beyond standard block rewards and gas fees by including, excluding, or reordering transactions. Earlier literature called it miner-extractable value because miners controlled block assembly under proof of work. Today, on proof-of-stake systems and other architectures, the term is usually expanded to maximal extractable value because the same logic applies to validators, block builders, sequencers, and other actors with ordering power.
Here is the mechanism. A pending transaction does not execute the moment a user signs it. It sits in some propagation layer (often called the mempool) while block producers decide what to include. During that waiting period, other actors can observe it, simulate what it will do, and ask a profitable question: if this transaction executes, does it create an opportunity for me if I act before it, after it, or instead of it?
That question has force because DeFi applications are state machines. A Uniswap swap changes reserves and therefore price. A lending protocol liquidation changes account solvency and available collateral. An NFT mint or token launch can change a market-clearing price within seconds. The chain is public, smart contracts are deterministic, and many opportunities can be simulated before they settle. So transaction ordering becomes a trading venue in its own right.
A useful analogy is an airport runway. Planes may all be ready to land, but the landing sequence still matters because each landing changes the conditions for the next. That explains why queue position has value. The analogy fails in one important way: on a blockchain, actors are not just waiting their turn. They can often bid to change the queue, insert themselves into it, or keep others off it entirely.
How can transaction ordering create profit? (sandwich and arbitrage examples)
Imagine a trader submits a large market buy on an automated market maker. The pool currently prices a token at 100, but the order is big enough to push the execution price materially higher as it consumes liquidity across the curve. That pending trade is visible before final inclusion.
A searcher (an actor running software to detect MEV opportunities) sees the trade in the public mempool and simulates its effect. The searcher realizes that buying the token before the user’s order and selling it after will be profitable. Why? Because the user’s own trade will move the price upward in the middle. The searcher can then submit two transactions: a buy that executes just before the victim transaction and a sell that executes just after. If both land in the right order, the searcher captures the user’s price impact.
This is the classic sandwich attack. The mechanism is not mysterious. The attacker is not predicting the future price in a broad market sense. The attacker is exploiting the fact that the victim transaction itself predictably moves the AMM price, and block ordering lets the attacker trade around that movement.
Now consider a less adversarial case. Suppose the same token trades at slightly different prices on two DEXes. A searcher can atomically buy on the cheaper venue and sell on the more expensive one within a single transaction. If the transaction succeeds, the profit is locked in; if conditions changed and profit vanished, the whole transaction reverts. This kind of DEX arbitrage is often described as “riskless” in the narrow sense that the strategy can be made atomic on-chain. It is still operationally competitive, but not exposed to ordinary execution risk in the same way as off-chain arbitrage.
These two examples feel morally different, and that distinction matters. Arbitrage often pushes prices back into line and improves market efficiency. Sandwiching usually worsens user execution and transfers value directly from the user to the extractor. Both are MEV because both depend on transaction ordering rights. But they do not have the same social consequences.
Who captures MEV? Searchers, builders, and validators explained
In theory, the final block producer captures all MEV, because only the party with final ordering authority can guarantee execution. In practice, MEV is usually produced through a supply chain.
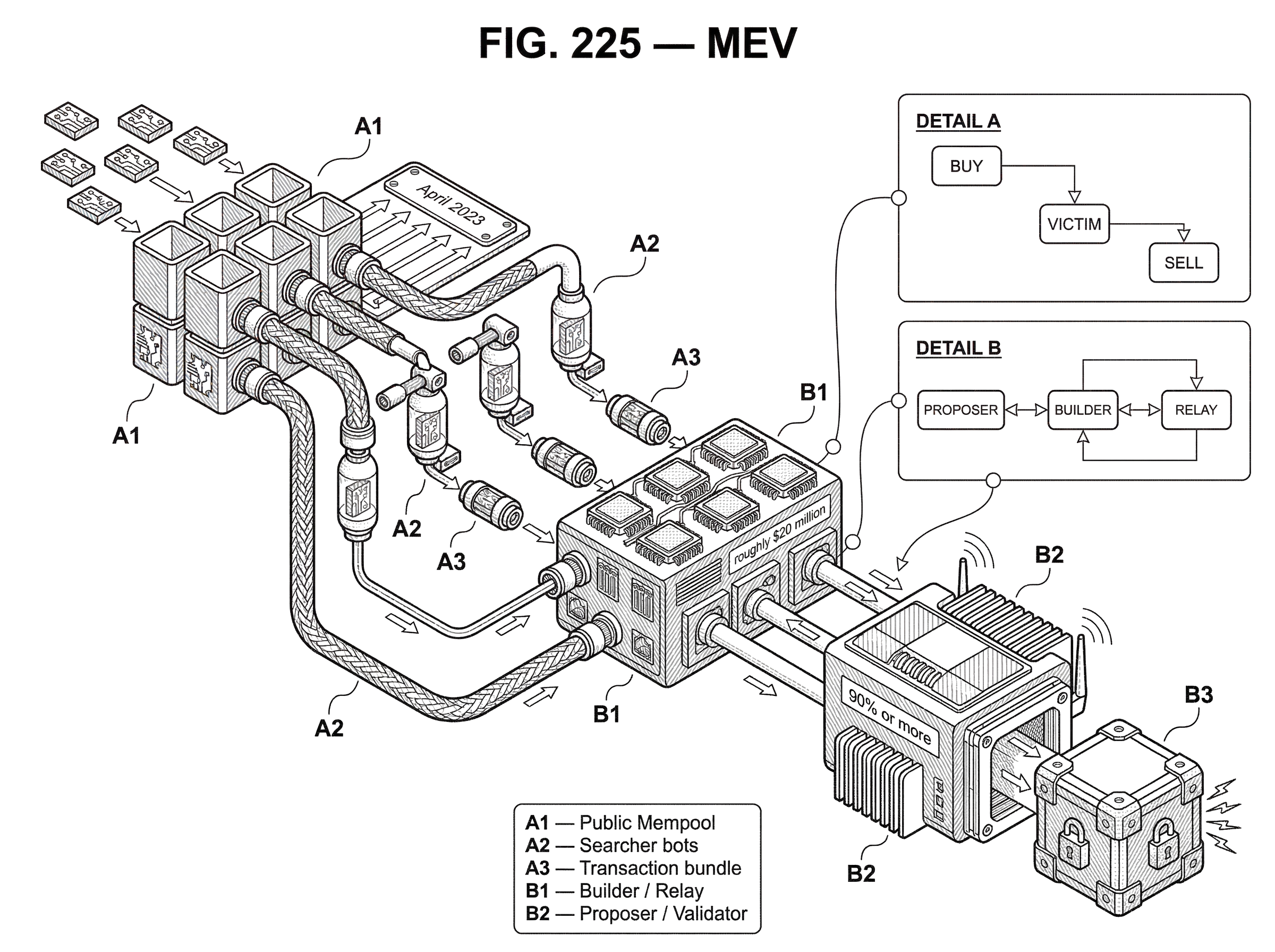
Searchers scan pending transactions and on-chain state for opportunities. They run bots, simulations, and pricing models. Builders assemble candidate blocks or bundles of transactions that maximize total extractable value. Relays or similar intermediaries may carry those blocks or bundles to proposers. Validators or proposers choose the most profitable available payload when it is their turn to produce a block.
This division exists because discovering opportunities and exercising ordering rights are different businesses. Searchers are specialized at finding profitable transaction sequences. Validators are specialized at consensus participation. Builders sit in between, combining orderflow, searcher bids, and user transactions into revenue-maximizing blocks.
This separation became especially visible on Ethereum after the rise of private relay systems and proposer-builder separation. Flashbots describes its role as mitigating the negative externalities of MEV rather than eliminating MEV outright. That framing is important. MEV is not something the ecosystem has removed; it is something the ecosystem has tried to structure.
Under MEV-Boost, validators run sidecar software that solicits bids from a market of builders through relays and then selects the most profitable block. The validator gives up direct control over block contents in exchange for a competitive market in block construction. This changes who captures value and how the auction is run, but it does not make the underlying ordering value disappear.
Why do priority gas auctions (PGAs) form and how do they work?
Once many actors can see the same opportunity, they compete for priority. Under public mempool conditions, that competition often takes the form of repeated fee bidding: the same opportunity is targeted by multiple bots, each resubmitting higher-fee transactions to outrank the others.
The early MEV literature called these contests priority gas auctions, or PGAs. The idea is simple. If winning an arbitrage is worth 1 ETH, a searcher may be willing to spend nearly that entire amount on fees to ensure inclusion ahead of competitors. If two or more searchers do this, the opportunity’s value gets bid away and transferred to the block producer or builder.
This explains a pattern that otherwise looks irrational. Why would a bot pay extremely high fees for what seems like a small trade? Because the fee is not being paid to make the trade itself worthwhile. The fee is being paid to win a race whose prize is the state transition created by being first.
Ethereum.org notes that in highly competitive cases, rational searchers may pay 90% or more of their expected MEV as gas fees. That is not an edge case in the logic of the system. It is the expected endpoint of competition when multiple actors can identify the same prize and only one can claim it.
The consequence is that public mempool MEV can create congestion and fee spikes that affect everyone else. A user who knows nothing about arbitrage bots may still pay more for blockspace because searchers are bidding aggressively against one another. So MEV is not only a transfer between extractors and victims; it also changes the price of access to the chain.
What kinds of strategies count as MEV beyond frontrunning?
| Strategy | Common goal | User harm | System effect | Atomic? |
|---|---|---|---|---|
| DEX arbitrage | Capture price spread | Low | Improves price alignment | Yes |
| Liquidations | Enforce undercollateralization | Medium | Maintains protocol solvency | Often |
| Sandwich attacks | Exploit victim slippage | High | Transfers value from users | Often |
| Transaction replay/copy | Steal pending profit | High | Increases front‑running pressure | Yes |
Many readers first meet MEV through sandwich attacks, so they associate the concept with predatory trading. That is understandable, but incomplete. The deeper idea is broader: MEV is any value created by discretionary transaction ordering.
That includes DEX arbitrage, liquidation races, NFT mint sniping, oracle-related strategies, and transaction replay or copy-trading attacks where a profitable pending transaction is imitated and submitted with higher priority. Research measuring blockchain extractable value on Ethereum found very large realized profits across arbitrage, liquidations, and sandwiches, while also emphasizing that any estimate is incomplete because the full strategy space is larger and private orderflow is hard to observe.
Liquidations make the ordering logic especially clear. In a lending protocol, once a borrower falls below the required collateralization threshold, the first eligible liquidator to act can often buy collateral at a discount or collect a fixed spread. This is not merely “competition in a market.” It is competition to be the transaction that updates protocol state first. That is why liquidations and arbitrage are structurally MEV opportunities even when they serve a protocol function.
A smart reader might object that this sounds like ordinary arbitrage or ordinary exchange priority. The distinction is that MEV depends specifically on blockspace control. Arbitrage exists in many markets. MEV is the part of arbitrage and related strategies that arises because one actor can influence execution order inside a block or submission pipeline.
How can MEV threaten blockchain consensus and finality?
The most important misunderstanding about MEV is to treat it as purely an application-layer annoyance. Sometimes it is that. But sometimes it becomes large enough to change validator or miner incentives at the consensus layer.
The key invariant in many blockchain security arguments is that honest participation should be more profitable than deviating from the protocol. Standard rewards and fees are supposed to make that true. MEV weakens this assumption because it adds a second revenue stream tied to specific blocks and specific orderings. If a past block contained unusually large MEV, a rational block producer may prefer not to accept history as settled. They may prefer to reorganize the chain and try to capture that value themselves.
The Flash Boys 2.0 paper made this risk explicit. It argued that when ordering-derived profits exceed ordinary block rewards, they can incentivize undercutting and time-bandit attacks; attempts to rewrite recent history to capture missed opportunities. The paper gave concrete examples where a single arbitrage transaction dwarfed the ordinary block reward in the same block.
This is the deeper reason the industry worries about MEV. Not because every MEV event is theft, but because sufficiently large MEV can invert the incentive structure that consensus relies on. A chain can tolerate many imperfect things. It cannot safely tolerate a world in which rewriting history is more profitable than extending it.
That risk is not confined to proof-of-work Ethereum circa 2019. The actor names change across architectures, but the mechanism persists. On Solana, for example, a single elected leader sequences transactions during its tenure, so the locus of ordering power is concentrated in the leader for that window. On rollups, a centralized sequencer often has even more direct ordering control. On any chain where ordering is privileged and state transitions are valuable, MEV appears in some form.
Different transaction models can change the shape of the opportunity surface. Account-based systems with globally shared mutable state make some interactions easy to compose and therefore easy to compete over. More constrained UTXO-style systems can reduce some categories of contention, though richer variants such as EUTXO still support expressive state-machine behavior. The fundamental point survives these variations: if multiple users compete to affect shared state, ordering retains value.
How do private relays and protected orderflow change MEV dynamics?
| Pipeline | Visibility | Predation risk | Trust model | Best for |
|---|---|---|---|---|
| Public mempool | Full public visibility | High | Permissionless, low trust | Open-market trading |
| Private relays / bundles | Restricted visibility | Lower public frontrunning | Relay/builder trust required | Shielded submissions |
| MEV-Share / redistribution | Selective visibility, commitments | Reduced capture for users | Protocol-mediated redistribution | Value-sharing flows |
A public mempool makes many MEV strategies easier because pending transactions are visible before they are finalized. Searchers can watch, simulate, and react. That is why the mempool is so central to discussions of frontrunning and sandwiching.
But the ecosystem’s response has often been to move orderflow out of the public mempool rather than to eliminate ordering advantages. Private relays, bundle submission systems, and private RPC endpoints let users or searchers send transactions directly into specialized pipelines. Flashbots Protect, for example, is presented as a way to shield users from public mempool frontrunning. MEV-Share aims to let value from certain backrunning opportunities be redistributed to users or orderflow providers instead of being captured entirely by searchers and builders.
This shift changes who sees what and who gets paid. It can reduce public copy-trading and obvious frontrunning. But it also creates new trust assumptions and market structure questions. Research on Ethereum’s block construction market has shown that MEV-Boost and related relay-builder systems became dominant quickly, moved substantial revenue, and introduced new concerns around relay trust, timing games, concentration, and censorship.
That trade-off is easy to miss. Private orderflow can be genuinely useful to users. It can also make the market less transparent and push more power into specialized intermediaries. In other words, some MEV mitigations are really MEV reallocations.
What real incidents reveal risks in MEV infrastructure?
MEV infrastructure is now important enough that its failures matter directly. A notable example is the April 2023 mev-boost relay incident described by Flashbots, where a malicious proposer exploited relay behavior to obtain block contents and steal roughly $20 million from sandwich bots. The technical details were specific to a commit-and-reveal flow and relay handling of invalid headers, but the broader lesson was general: when MEV markets rely on trusted middleware, bugs in that middleware can become very expensive.
Another Flashbots disclosure in August 2023 described a builder bug that erroneously included reverting transactions in blocks, costing users gas. Again, the details were implementation-specific. The important takeaway is that the MEV supply chain is not just a theory of incentives. It is a real operational system made of builders, relays, APIs, cutoffs, simulation engines, and software invariants. Each additional layer can solve one problem while introducing another.
This is where a real-world custody analogy helps. In decentralized settlement systems, splitting authority can reduce single points of failure. Cube Exchange, for example, uses a 2-of-3 threshold signature scheme for decentralized settlement: the user, Cube Exchange, and an independent Guardian Network each hold one key share, no full private key is ever assembled in one place, and any two shares are required to authorize a settlement. The analogy helps explain why the ecosystem likes separation of roles. But it also fails in an important way: in MEV infrastructure, role separation does not automatically remove trust. It often redistributes trust across relays, builders, and software paths rather than eliminating it.
When does MEV improve markets and when does it harm users?
The cleanest way to think about MEV’s mixed reputation is to ask what mechanism generates the profit and what consequence follows.
When MEV comes from arbitrage, the extractor usually profits by aligning prices across venues. That can improve price discovery and keep DeFi markets coherent. When MEV comes from liquidations, the extractor helps enforce lending protocol solvency, though the race for liquidation still imposes costs and may centralize around sophisticated operators. When MEV comes from sandwiching or some forms of frontrunning, the extractor profits by worsening a user’s execution. That is a transfer from users to insiders with ordering advantage.
So MEV is not uniformly malicious or uniformly beneficial. The same structural feature (valuable transaction ordering) can support market efficiency in one context and exploitation in another. This is why attempts to discuss MEV as simply “good” or “bad” usually stall. The mechanism is one thing; the welfare effects depend on the application.
Why can't protocols fully eliminate MEV?
| Approach | How it reduces MEV | Main trade-off | Maturity |
|---|---|---|---|
| Fair arrival ordering | Attempts time-based ordering | Hard to define global time; network latency | Low |
| Batch auctions | Clears races by batching transactions | Higher latency; changed UX | Medium |
| Encrypted / commit-reveal | Hides intent during ordering | Operational complexity; trust assumptions | Low |
| Proposer-Builder Separation (PBS) | Markets block-building to reduce proposer capture | New relay/builder trust and timing games | Deployed |
A tempting response is to ask why protocols do not just enforce fair ordering. The difficulty is that “fair” is not one single thing. Fair by arrival time sounds appealing, but arrival time is hard to define in a distributed system with network latency and no global clock. Batch auctions can reduce some races by clearing transactions together, but they change user experience and may create new strategy surfaces. Encrypting transactions before ordering can hide intent temporarily, but encrypted systems still need eventual decryption and can introduce operational complexity or trust assumptions.
A systemsatization of MEV countermeasures cataloged many proposed approaches and found no settled best answer. That is consistent with first principles. MEV is a byproduct of combining three features people usually want: public verifiability, composable shared state, and some actor who decides order. Remove any one of those aggressively enough and you reduce MEV; but you also give something up.
That is why most deployed solutions aim to mitigate, redistribute, or channel MEV rather than abolish it. Private orderflow reduces some visible predation. PBS tries to limit validator-level centralization by creating a specialized builder market. User-facing systems try to route transactions through paths less exposed to sandwiching. MEV-Share tries to send some extracted value back to users. These are engineering responses to an economic fact, not escapes from it.
MEV beyond Ethereum
Although Ethereum dominates the vocabulary, MEV is chain-agnostic wherever transaction sequencing matters. Solana’s architecture gives a leader direct sequencing authority during short windows, which changes the timing game but not the basic existence of ordering value. Rollups with centralized sequencers make the concentration even starker: one sequencer may control essentially all ordering for that domain. cross-chain routing systems can create additional opportunities when multi-step swaps and bridges expose intermediate state or timing dependencies.
What changes from chain to chain is not whether MEV exists, but where it concentrates and how it is contested. On one chain the key battle may be public mempool priority. On another it may be relationships with builders or relays. On another it may be privileged sequencer APIs or fast-lane auctions. The surface area is architectural; the principle is universal.
Conclusion
MEV is the economic value of transaction ordering. Once a blockchain lets different outcomes depend on who gets executed first, ordering becomes a scarce resource, and markets form around it.
That single idea explains a lot: arbitrage bots, sandwich attacks, liquidation races, private relays, builder markets, and even some consensus risks. The detail varies by chain and protocol, but the memorable truth is simple: where block order changes value, block order will be bought, sold, and fought over.
How do you trade through a DEX or DeFi market more effectively?
Trade through a DEX or DeFi market more effectively by focusing on liquidity, price impact, and order-type choice. On Cube Exchange, fund your account and use standard on-chain protections (limits, slippage tolerance, and order splitting) to reduce execution risk and limit avoidable MEV exposure.
- Check the trading pair’s on-chain liquidity and recent volume using a block explorer or market analytics; estimate expected price impact for your target size.
- Fund your Cube account with the asset you plan to use (fiat on‑ramp or a supported crypto transfer).
- Choose an order type: use a limit order to lock a maximum price or a market order for immediate execution; set a slippage tolerance (for example 0.5–1%) and a transaction deadline before submitting.
- For large trades, split the order into smaller chunks or stagger multiple limit orders to reduce price impact, then review estimated fees and submit.
Frequently Asked Questions
A sandwich attack sees an attacker observe a large pending swap, submit a buy that executes just before the victim to push price up, then submit a sell that executes just after the victim to capture the price impact; it works because mempool visibility plus discretionary block ordering lets the attacker place trades around the victim’s transaction.
Searchers find and simulate profitable sequences in the mempool, builders assemble blocks or bundles that maximize extractable value from those sequences, and validators or proposers ultimately choose which payload to include when producing a block, so MEV is typically realized through this searcher–builder–validator supply chain rather than by a single actor.
Priority gas auctions arise because multiple bots compete to be ordered first for the same opportunity and will outbid each other in fees; in extreme cases rational searchers may spend a large fraction (even 90% or more) of expected MEV on fees to win inclusion, effectively transferring the competition’s value to block producers.
MEV can undermine consensus incentives when ordering-derived profits exceed normal block rewards: research (Flash Boys 2.0) and the article explain that large block-level MEV can motivate reorgs or "time‑bandit" attacks where actors try to rewrite recent history to recapture missed value, threatening chain finality.
Moving transactions off the public mempool into private relays or bundle submission systems reduces visible frontrunning but does not eliminate ordering value; it often shifts power to relays, builders, or sequencers and introduces new trust and centralization trade‑offs instead of removing MEV outright.
Completely enforcing a single notion of fair ordering is difficult because distributed systems lack a canonical arrival time and countermeasures (batch auctions, encryption, blind ordering) each impose latency, usability, or trust trade‑offs, so most deployed solutions aim to mitigate or redistribute MEV rather than abolish it.
MEV exists on many architectures: on Solana a single elected leader sequences transactions within its slot, on rollups a centralized sequencer can concentrate ordering power, and account‑based composability generally increases the surface for ordering‑dependent opportunities - so the form changes by design but the underlying economic logic persists.
Real incidents show MEV infrastructure risks: in April 2023 a mev‑boost relay incident and related timing bugs enabled a proposer to learn block contents and facilitated roughly $20M of extraction from sandwich bots, and other builder bugs have accidentally included reverting transactions that cost users gas - illustrating that middleware failures can be costly.
Measuring MEV is hard and current estimates are conservative lower bounds because studies typically focus on a subset of strategies (e.g., pure arbitrage, sandwiches, fixed‑spread liquidations), rely on heuristics like same‑block inclusion, and cannot observe privately‑relayed or unbroadcasted transactions, so reported figures understate the full economy.
Common practical mitigations include private orderflow (Flashbots Protect), proposer‑builder separation and MEV‑Boost to auction block construction, and redistributive proposals like MEV‑Share, but these interventions mitigate visible harms and reallocate value rather than removing the underlying extraction incentives, and they introduce new questions about trust, centralization, and auditability.
Related reading