What is a Canonical Bridge?
Learn what a canonical bridge is, how official L1-L2 bridges work, why they define standard asset representations, and where their trust assumptions break.
Introduction
Canonical bridge is the name usually given to the official bridge for moving assets and messages into or out of a blockchain system, especially a rollup or sidechain. The important question is not whether it is popular, but what makes it canonical: the bridge is treated by the protocol, ecosystem, or chain operator as the default path whose state the chain itself understands and honors. That matters because bridging is where users ask one system to accept facts about another system, and that is exactly where trust assumptions become sharp.
If two chains cannot natively read each other’s state, some mechanism has to connect them. A bridge provides that mechanism. But many bridges can exist for the same pair of chains. Some are third-party networks with their own validators or guardians. Others are built into the lifecycle of the chain itself. A canonical bridge is the latter kind: the bridge that sits closest to the chain’s own security and accounting model.
For rollups, this is especially clear. A rollup can only really promise a secure withdrawal path if the path is anchored in the contracts that define the rollup on its parent chain. Optimism’s documentation describes a set of L1 smart contracts deployed on Ethereum “to bridge between the L1 and L2 domains and manage aspects of the rollup.” Its L1StandardBridge contract is explicitly responsible for transferring ETH and ERC-20 tokens between L1 and L2. Arbitrum’s Nitro contracts are similarly described as the core contracts deployed to the parent chain to host the rollup, while token bridge contracts live in a dedicated repository alongside that core system. In other words, for a rollup, the canonical bridge is not an accessory. It is part of how the rollup exists as a system.
The compression point is simple: a canonical bridge is canonical because the destination chain itself recognizes it as the authoritative source of bridged truth. That recognition can come from protocol contracts, standard predeploys, state roots posted to a parent chain, or a community-standard deployment of an interoperability protocol. Everything else follows from that.
Why does a blockchain need a canonical (official) bridge?
The underlying problem is easy to state and hard to solve. Assets do not literally move across chains. If you lock ETH on Ethereum and want “the same value” on a rollup, the rollup cannot inspect Ethereum directly and spontaneously decide to mint a representation. Some entity or mechanism must prove to the rollup that the lock happened, and some mechanism must prove back to Ethereum that a withdrawal on the rollup is legitimate.
Without an official path, every wallet, exchange, and application would have to choose among many competing representations of “bridged ETH” or “bridged USDC,” each backed by a different trust model. That fragmentation is not just inconvenient. It breaks a basic invariant users want: the chain should have a single, well-understood answer to what counts as the native bridged form of an asset coming from its home chain.
This is why canonical bridges tend to emerge wherever one chain is structurally subordinate to or anchored in another. Rollups settle to a parent chain, so there must be some standard route by which funds enter and exit that settlement relationship. Optimism makes this mechanical in code. Its L1 bridge escrows L1-native ERC-20 tokens on Ethereum when they are deposited toward L2. Withdrawals then return value in the opposite direction through finalization functions on L1. The bridge is not merely relaying messages; it is maintaining a conservation rule across domains: what appears on one side must be backed by lockup, burn, or provable release logic on the other.
Something similar appears in IBC-based ecosystems, though the form is different. Cosmos documentation describes IBC as a protocol that lets chains share arbitrary byte-encoded data securely and permissionlessly. It also mentions a canonical deployment of IBC v2, IBC Eureka, for connecting Cosmos chains and Ethereum. Here, “canonical” does not mean a single escrow contract blessed by a rollup team. It means a standard deployment path of a protocol whose semantics the connected systems agree to treat as authoritative. The common pattern is still there: some route becomes the route the ecosystem expects wallets and applications to build around.
How does a chain designate a bridge as canonical?
Calling a bridge canonical does not automatically mean it is trustless, immutable, or perfectly safe. It means something more precise: the bridge is the bridge the chain itself is designed around.
That can happen in a few ways. On a rollup, the canonical bridge is often encoded directly into the L1 and L2 contracts that manage deposits, withdrawals, and message passing. Optimism’s L1StandardBridge is initialized with a cross-domain messenger and linked to the L2_STANDARD_BRIDGE predeploy on L2. That linkage tells you something deeper than “these contracts talk to each other.” It tells you the protocol already has named endpoints for the official bridge path.
On other systems, canonical status can come from standardized protocol semantics rather than a single contract pair. In IBC, the critical structure is the light-client-based packet protocol plus relayers that submit proofs between chains. Cosmos documentation emphasizes that relayers are off-chain processes, but they do not decide truth; each chain uses a light client of the other to verify incoming packets. In that setting, what is canonical is less “this one bridge operator” and more “this standard, protocol-native way of proving cross-chain state.”
This also helps explain what canonical does not mean. Wormhole is a major interoperability protocol with messaging, token transfers, core contracts, VAAs, and guardians. It may be the dominant route for certain assets or applications, but dominance alone does not make something canonical for a rollup. If a chain’s own withdrawal logic does not treat Wormhole attestations as the authoritative source of truth for exiting the chain, then Wormhole is an important bridge, not the chain’s canonical bridge.
So the organizing principle is this: a bridge is canonical when protocol legitimacy, not market share, is what makes users rely on it.
How do canonical bridges handle deposits, token representation, and withdrawal finality?
A canonical bridge usually has to solve three linked problems. First, it must accept an asset or message on the source chain. Second, it must create or release the corresponding representation on the destination chain. Third, it must do so in a way that preserves a backing relationship users can audit.
For L1-to-L2 deposits on a rollup, the common mechanism is escrow plus message passing. Suppose a user deposits an L1-native token into the bridge contract on Ethereum. The token is transferred into escrow in the L1 bridge. A cross-domain message is then initiated toward the L2 bridge telling it that a deposit has occurred for a given user, token pair, and amount. When that message is accepted on L2, the corresponding representation is minted or credited there.
Optimism’s L1 bridge makes this pattern explicit. The contract exposes functions such as depositETH, depositETHTo, depositERC20, and depositERC20To. The ETH flow and ERC-20 flow share the same underlying logic: begin a cross-domain deposit on L1, then have the L2 side recognize and complete it. The bridge contract also supports a simpler path for externally owned accounts depositing ETH by sending ETH directly to the contract’s receive() function, which initiates a deposit to the sender’s L2 account.
Now consider the reverse direction. L2-to-L1 withdrawal cannot simply be “send a message and trust me.” The parent chain must be convinced that the withdrawal really follows from valid L2 state. In optimistic rollups, that depends on state roots posted to L1 and a challenge process. Optimism’s operator docs say the Proposer publishes the L2 state root to Ethereum, enabling user withdrawals, while the Challenger disputes invalid roots. The canonical bridge on L1 then finalizes withdrawals only after the system’s proof and finality rules have been satisfied.
This is the heart of the matter. A canonical bridge is often not primarily about transportation. It is about admission control. The destination chain needs a rule for which external claims it will accept. For deposits, that rule may be “this event happened in the official L1 bridge.” For withdrawals, it may be “this message is included in an L2 state root that has survived the dispute window.”
How does bridging ETH from Ethereum to an optimistic rollup work?
Imagine Alice holds ETH on Ethereum and wants to use an application on an optimistic rollup. She interacts with the rollup’s official bridge contract on Ethereum and sends 1 ETH along with a deposit call. At this moment, nothing has moved across space. What has happened is more precise: the L1 bridge contract has received custody of 1 ETH, and the rollup now has grounds to create a corresponding balance on L2.
The bridge system emits the deposit event and sends a cross-domain message toward the L2 side. Because this is a canonical bridge, the L2 side is not looking for arbitrary attestations from arbitrary bridges. It is looking for the message path and counterpart contract that the rollup itself recognizes. Once that message is processed, Alice receives 1 ETH worth of canonical L2 ETH representation on the rollup.
Later, Alice wants to withdraw back to Ethereum. On L2, she initiates a withdrawal transaction. That transaction changes L2 state: Alice’s L2 balance is reduced, and a withdrawal message becomes part of the rollup’s state. But Ethereum does not yet release funds. It waits until the rollup’s state root containing that withdrawal is posted to L1 and, in an optimistic system, survives the challenge period. Only then can the L1 bridge finalize the withdrawal and release 1 ETH from the bridge-controlled funds back to Alice’s Ethereum address.
Notice what is doing the real work here. Not branding, and not a multisig saying “looks good.” The mechanism is an accounting loop backed by the rollup’s own state commitment process. Escrow on the way in, provable state on the way out. That is why this path is canonical.
The analogy is a warehouse receipt system. You deposit a bar of gold into the official warehouse and receive a receipt that the local market accepts. When you redeem the receipt, the warehouse releases the gold. This analogy explains the backing relationship well. Where it fails is that bridges often rely on asynchronous proofs, challenge windows, and smart contract logic rather than a single physical custodian.
How do canonical bridges determine the official token contract on the destination chain?
| Token type | Compatibility | Risk to backing | Bridge handling |
|---|---|---|---|
| Standard ERC‑20 | Supported | Low if compliant | Escrow or burn/mint |
| Transfer‑fee tokens | Not compatible | Amount mismatch risk | Special gateway required |
| Rebasing tokens | Not compatible | Backing misaccounted | Avoid or wrap token |
| Blocklist‑enabled tokens | Not compatible | Unexpected freezes | Manual handling or exclude |
Canonical bridges matter not only because they move value, but because they define which token contract on the destination chain counts as the official representation of an origin-chain asset.
That distinction becomes important the moment multiple bridges exist. If Ethereum USDC can arrive on an L2 through the official bridge, a liquidity network, and a third-party validator bridge, the L2 may end up with several incompatible token contracts all claiming to represent Ethereum USDC. Applications then have to pick one. Liquidity fragments. Users are confused about what is “real.” The canonical bridge reduces this ambiguity by establishing the default mapping the ecosystem will usually treat as native for that route.
In practice, bridge systems often maintain explicit token-pair relationships. The inaccessible Arbitrum docs page metadata suggests coverage of ETH and ERC-20 token flows and gateway patterns, which is consistent with the broader rollup design pattern: ETH may have special handling, while ERC-20s often pass through token-specific gateway logic. Even without relying on the blocked page, the architecture signaled by Arbitrum’s separate token bridge contracts makes sense from first principles. Different token behaviors require different handling, but the chain still wants a canonical answer to “what is the proper bridged representation of this origin token?”
This is also where edge cases appear. Optimism’s L1StandardBridge explicitly warns that it is not intended to support all ERC-20 variants, including transfer-fee tokens, rebasing tokens, and tokens with blocklists. That warning is easy to miss, but conceptually it is crucial. Canonical bridges assume certain token invariants, such as “transferring x tokens really moves x tokens” and “balances change only through the expected transfer logic.” If a token violates those assumptions, the bridge’s accounting may no longer preserve the backing relationship cleanly.
So canonical does not mean universal compatibility. It means official handling under a defined set of assumptions.
What trust assumptions underpin canonical bridges?
People often hear “canonical bridge” and translate it to “most secure bridge.” That is too simple. The real statement is narrower: the trust model of a canonical bridge is usually the trust model of the chain itself, plus whatever bridge-specific control surfaces remain.
For an optimistic rollup, the canonical bridge inherits trust from Ethereum availability and settlement, from the correctness of the rollup contracts, from posted state roots, and from the dispute process that can invalidate bad roots. Optimism’s docs make this dependency explicit: the proposer posts state roots, and the challenger disputes invalid ones. If that machinery is broken or captured, the canonical withdrawal path is at risk because the bridge finalizes against that machinery.
For systems like IBC, trust is anchored differently. Cosmos documentation emphasizes that chains verify packets using light clients of one another, while relayers merely carry data. In that design, the bridge path is closer to direct cryptographic verification and further from trust in an external validator set. The protocol-native path is canonical because the connected chains themselves verify proofs according to a shared standard.
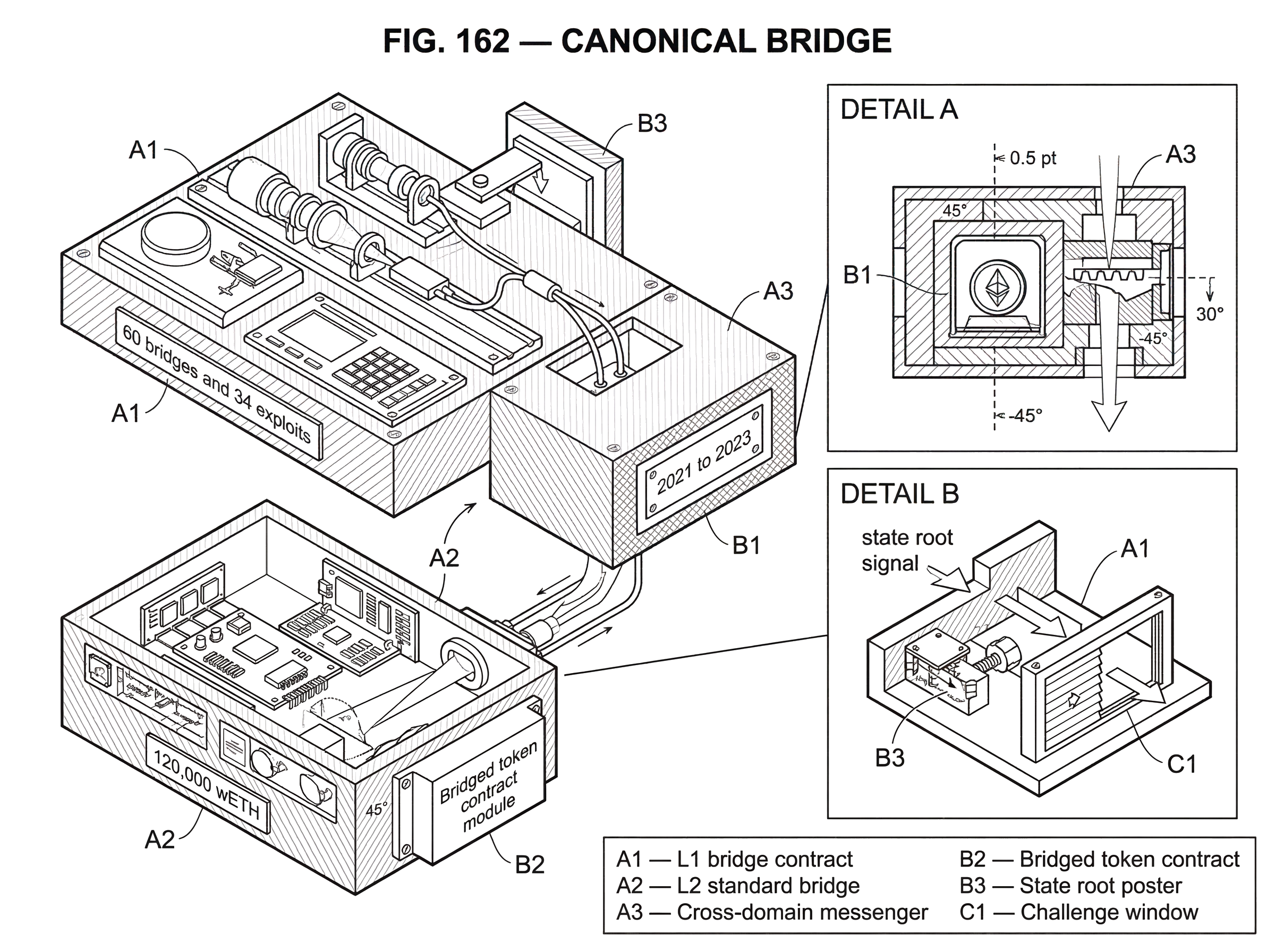
By contrast, validator or guardian bridges derive trust from an extra committee. Wormhole documentation highlights guardians and VAAs as core protocol components. That can be useful and scalable, but it creates a different security center. The Wormhole exploit analyzed by CertiK shows why this distinction matters. There, a failure in signature-verification logic on Solana allowed the attacker to create a malicious message and mint 120,000 wETH. The lesson is not “all non-canonical bridges are bad.” It is that when trust is concentrated in a separate attestation mechanism, that mechanism becomes the critical thing to audit and defend.
Canonical bridges can also fail catastrophically. They are not protected by the word “canonical.” Ronin’s bridge, which required 5-of-9 validator signatures for deposit and withdrawal recognition, was compromised when attacker-controlled keys forged withdrawals. The team later raised the threshold to 8-of-9 as a mitigation. This was, in practice, the official bridge for that ecosystem. Its failure shows that official status can increase stakes without removing risk.
What are the main failure modes for canonical bridges?
| Failure mode | What fails | Typical impact | Quick mitigation |
|---|---|---|---|
| Verification failure | Admission rules bypassed | Unauthorized mint or release | Harden verification checks |
| Key/governance compromise | Privileged controls abused | Large fraudulent withdrawals | Harden key governance |
| Bad token assumptions | Accounting mismatch | Loss or locked funds | Explicit token handling rules |
| Liveness failure | Relayers or dispute stalled | Withdrawals delayed | Add relayer redundancy |
The reason canonical bridges deserve careful explanation is that they compress many risks into a single pathway. If the whole ecosystem treats one bridge as the official route, any flaw in that route becomes systemically important.
One class of failure is verification failure: the bridge accepts a deposit or withdrawal claim that should have been rejected. The Wormhole exploit is a vivid example of this broader class. A validation step relied on a deprecated helper that failed to verify a critical account, allowing fake signature verification. The general lesson is larger than Wormhole itself: any canonical bridge lives or dies by the correctness of its admission rules.
A second class is key or governance compromise. If a bridge can be paused, upgraded, or operated by privileged roles, those roles become part of the trust model. Ronin’s incident shows how validator-key compromise can directly authorize fraudulent withdrawals. Even when a bridge is more protocol-native, upgradeability and configuration controls still matter. Optimism’s L1 bridge stores a systemConfig reference and exposes pause state through it, which tells you that bridge behavior can depend on system-level configuration rather than only immutable logic.
A third class is bad token assumptions. Fee-on-transfer, rebasing, or blocklist-enabled tokens can break bridge accounting because the amount that leaves one side may not equal the amount the bridge thinks it handled. Optimism’s explicit warning here is unusually useful because it states, in code comments, what many users otherwise discover only through loss.
A fourth class is liveness failure. A canonical bridge may be safe in the sense that invalid withdrawals cannot finalize, while still being painful in the sense that valid users cannot get funds out promptly. Optimistic rollups deliberately trade fast trust-minimized withdrawal for a delay tied to the dispute window. In IBC, relayers are off-chain and indispensable; if they fail to relay, interoperability stalls even though the verification model remains sound.
Research surveying 60 bridges and 34 exploits from 2021 to 2023 argues that bridges often provide weaker security guarantees than the underlying chains and identifies multiple recurring architectural flaws. Canonical bridges do not escape that pattern by definition. They mainly answer a different question: which bridge path should the ecosystem coordinate around?
Canonical bridge vs light-client and third-party bridges: what’s the difference?
| Bridge type | Verification | Canonicality | Trust anchor | Best for |
|---|---|---|---|---|
| Protocol-native | On-chain contracts/state | Usually canonical | Parent chain settlement | Default ecosystem route |
| Light-client | Cryptographic consensus proofs | Sometimes canonical | Light client of other chain | Low-assumption verification |
| Validator/guardian | External signatures (VAAs) | Rarely canonical | Guardian/validator committee | Broad asset coverage |
The cleanest comparison is with a light-client bridge. A light-client bridge is defined by how it verifies the other chain: it runs or checks a light client so that acceptance depends on cryptographic proof of consensus and state. A canonical bridge is defined by something different: it is the bridge path the protocol or ecosystem treats as official.
These categories can overlap. An IBC connection is often both protocol-native and light-client-based. In that case, canonical status and cryptographic verification reinforce each other. But they do not have to overlap. An official bridge for a sidechain might be validator-based and therefore canonical without being light-client-based. Conversely, a third-party light-client bridge can be highly trust-minimized without being canonical if the chain itself does not treat it as the standard withdrawal and asset-mapping path.
This distinction matters because users often ask the wrong question. They ask, “Which bridge is official?” when they really mean, “Which bridge minimizes the assumptions I care about?” Or they ask, “Which bridge is trustless?” when they really need, “Which token representation will every application on this chain accept as standard?” Canonicality answers the second kind of question more directly than the first.
Why do ecosystems converge on a canonical bridge despite alternatives?
Even when alternative bridges offer better speed, more chains, or lower fees, ecosystems still converge on canonical bridges because coordination is a hard problem. A shared bridge reduces ambiguity about asset identity, wallet support, exchange integration, and withdrawal guarantees. It gives developers a stable target.
You can see versions of this across architectures. Rollups expose official deposit and withdrawal contracts on the parent chain. IBC ecosystems rely on shared protocol semantics and relayer infrastructure so chains can interoperate through a common model. Polkadot’s XCM is not itself a delivery protocol, but it standardizes the message format and intent model so that cross-consensus communication can be expressed in a common language. In each case, the system benefits when there is a route or standard the ecosystem can treat as the default.
That said, the reason canonical bridges matter is also the reason they are dangerous to misunderstand. Once a bridge becomes the default, its assumptions become easy to ignore because the user experience feels native. But native feeling is not native existence. Assets are still being represented across trust boundaries, and some mechanism still decides which external facts to admit.
Conclusion
A canonical bridge is the official bridge path a blockchain system recognizes for moving assets or messages across domains. What makes it canonical is not popularity, but protocol legitimacy: the chain’s own contracts, standards, or settlement rules are built to honor that path.
That usually gives the ecosystem a default answer to two hard questions: which asset representation is standard here, and which withdrawal path is authoritative? But canonical does not mean risk-free. It means this is the bridge whose assumptions are closest to the chain’s own assumptions; and therefore the bridge whose failures matter most.
How do you move crypto safely between accounts or networks?
Moving crypto safely means verifying the asset, network, destination, and expected finality before you send. Use Cube Exchange’s standard fund-and-send workflow: deposit or transfer the asset into your Cube account, then initiate the outbound transfer while accounting for chain-specific confirmation or challenge windows.
- Confirm the exact asset and network: check the token contract address, chain ID, and whether the token has fee-on-transfer, rebasing, or blocklist behavior.
- Verify the destination address and network: copy the recipient address, confirm the destination chain ID (e.g., Ethereum L1 vs a specific L2), and ensure the receiving wallet or contract accepts that token representation.
- Fund your Cube account via an on-chain transfer or fiat on-ramp using the correct network and token; for ERC-20s, approve the token contract and amount from your sending wallet if required.
- Choose transfer parameters and submit: set an appropriate gas price or fee, select the correct network for the outbound transfer, and send. If you plan to use a canonical bridge path, check its expected finality (optimistic challenge window, IBC relayer needs, or other delays) before sending.
- Wait for the chain-specific confirmation or finality threshold (N confirmations or the bridge’s challenge/finality window), verify the on-chain receipt or event, then proceed to trade or further transfers.
Frequently Asked Questions
A bridge is canonical when the destination chain’s own protocol, contracts, or settlement rules treat that path as the authoritative source of cross‑chain facts - i.e., protocol legitimacy, not market share, makes it the default path the chain recognizes for deposits, withdrawals, and token mappings.
No - canonical status means the bridge’s assumptions are the ones the chain is built around, but it still inherits the chain’s and the bridge’s remaining trust surfaces; canonical bridges can have privileged roles, upgradeability, or protocol dependencies that produce real risks.
Typical canonical L1→L2 deposits use escrow on the origin chain plus a cross‑domain message that instructs the destination contract to mint or credit a representation; L2→L1 withdrawals require the rollup’s state root to be posted to L1 and (for optimistic designs) to survive the dispute/challenge window before the L1 bridge finalizes release of funds.
Common failure modes include verification failures (accepting bogus claims, as in the Wormhole incident), key or governance compromise (authorizing fraudulent withdrawals, as in Ronin), bad token assumptions (fee‑on‑transfer or rebasing tokens breaking accounting), and liveness problems (relayers or dispute processes delaying or stalling legitimate transfers).
Ecosystems converge on canonical bridges because a single, protocol‑endorsed path reduces ambiguity about which token contract counts as the official representation, aids wallet and exchange integration, and gives developers a stable target for integrations - coordination benefits that liquidity or fee advantages alone cannot fully replace.
Canonical and light‑client bridges are different concepts: canonicality is about which path the chain treats as authoritative, while light clients are a verification technique; they can coincide (e.g., IBC connections are often both canonical and light‑client‑based) but one does not imply the other.
No - canonical token mappings assume certain token invariants and are not universally compatible; for example, Optimism’s L1StandardBridge explicitly warns it is not intended to support transfer‑fee tokens, rebasing tokens, or tokens with blocklists because those behaviors break the bridge’s backing/accounting assumptions.
There is no universal answer; who can pause, upgrade, or control canonical bridge contracts varies by deployment and is often a critical part of the trust model - in practice many docs and repos do not always publish exact multisig, timelock, or governance addresses, so privileges and upgrade paths must be checked on the specific bridge’s on‑chain configuration and documentation.
Ask which assumptions matter to you: use the canonical bridge if you need the token representation and withdrawal path that the chain and most applications will accept by default; choose a third‑party or light‑client bridge if your priority is minimizing a particular trust assumption, but be aware that such bridges may not be accepted as the ‘official’ asset by every dApp on the destination chain.
Expect operational tradeoffs: optimistic rollup canonical withdrawals are deliberately delayed by the dispute/finality window before L1 funds are released, and protocol‑native setups like IBC depend on off‑chain relayers for liveness - so canonical paths can be more conservative in finality or dependent on external processes even when they are the protocol’s official route.
Related reading