What Is an Oracle?
Learn what a blockchain oracle is, why smart contracts need it, how oracle systems work, and the main security tradeoffs behind onchain data feeds.
Introduction
Oracle is the name for the mechanism that brings external information into blockchain applications. That sounds simple, but it exists because blockchains are built around a hard constraint: every validating node must be able to re-execute the same transaction and arrive at the same result from the same onchain state. If a smart contract could freely call a website, query a database, or ask “what is the current ETH/USD price?” during execution, different nodes could see different answers at different times and consensus would break.
So the puzzle is this: smart contracts are most useful when they react to the outside world, but blockchains stay secure by refusing to look outside themselves during execution. Oracles are the workaround. They do not abolish that constraint. They package outside information into a form the chain can consume while preserving enough determinism for consensus to survive.
That is why oracles matter so much in practice. Lending markets need collateral prices. Derivatives need reference rates. Insurance contracts need event outcomes. Games may need randomness. Automated systems may need a trigger that says some condition in the world has been met. In each case, the blockchain by itself cannot know the answer. An oracle supplies it.
The important thing to understand from the start is that an oracle is not truth itself. It is a system for making some claim about the world usable onchain.
Everything that follows is really about one question: **why should a smart contract trust that claim enough to act on it?
- architecture
- decentralization
- security
- incentives
- delays
- aggregation
- proofs
- committees
- first-party publishers
**
Why do blockchains need oracles?
A blockchain is good at reaching agreement about data already inside the system. It can answer questions like whether an account signed a transaction, whether a token transfer happened, or whether a storage slot contains a certain value. These are consensus-friendly questions because every node can inspect the same chain state and verify the same rules.
External facts are different. The current weather in Tokyo, the final score of a match, a company’s API response, or the market price of an asset on an exchange all live outside the blockchain’s native state. Even if every node could technically fetch that information, it would not follow that they would fetch it at the same moment, from the same source, through the same network path, or under the same failure conditions. A deterministic execution environment cannot safely depend on that kind of open-ended input.
This is the core reason developer documentation describes oracles as necessary for smart contracts: blockchains restrict execution to onchain data so nodes can maintain deterministic consensus. Oracles exist to bridge that information gap. Once you see that, the role of the oracle becomes clear. It is not an optional convenience layer. It is the price of connecting an intentionally closed system to an open world.
That connection also explains the phrase hybrid smart contract. A purely onchain contract can only reason about chain-native facts. A hybrid contract combines onchain code with offchain infrastructure, typically an oracle system, so that it can respond to outside events or data. The contract still executes onchain. The oracle extends what the contract can know.
How does an oracle deliver external data to smart contracts?
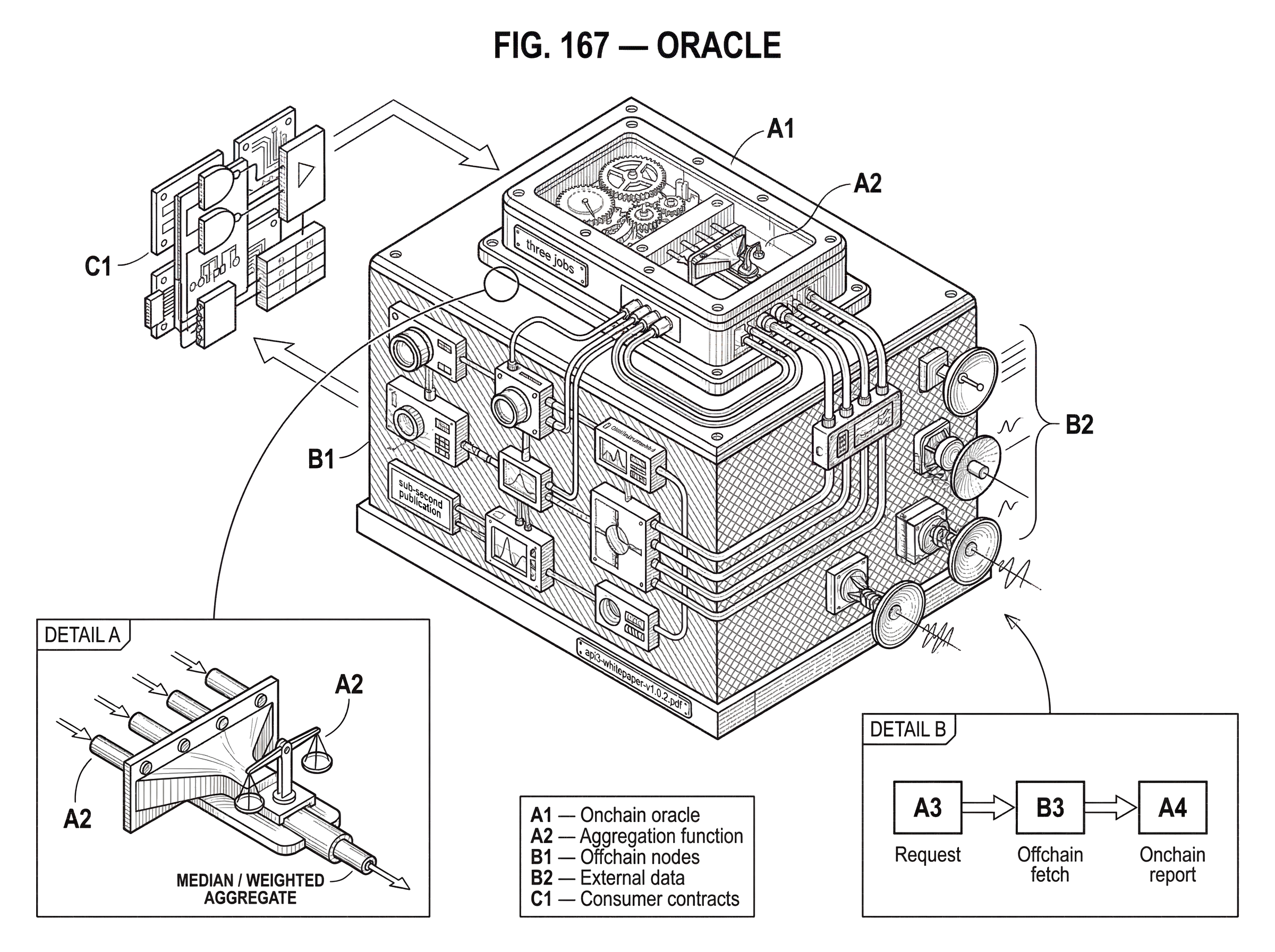
At a high level, an oracle performs three jobs: it sources data, it makes some claim about that data’s correctness or provenance, and it delivers the result onchain in a form contracts can read.
That broad definition matters because “oracle” can mean more than a price feed. Some oracles fetch data from web APIs. Some collect reports from exchanges or professional market makers. Some derive prices from onchain markets such as automated market makers. Some attest to randomness. Some trigger actions when time has passed or a condition has been met. Some move data across chains. These are different implementations of the same underlying idea: taking information or computation that is not natively available during contract execution and presenting it to the chain as consumable input.
Mechanically, many oracle systems have two parts. There is an onchain contract or program that accepts requests, stores reports, exposes current values, and defines how consuming contracts read them. Then there are offchain nodes or operators that listen for requests or update schedules, fetch or observe the relevant data, and submit reports back onchain. Ethereum documentation describes this as the typical oracle architecture: an onchain oracle contract paired with offchain oracle nodes.
A simple worked example makes this concrete. Imagine a lending protocol that needs the price of ETH in dollars to decide whether a borrower remains safely collateralized. The lending contract does not call an exchange website directly. Instead, it reads a value already written onchain by an oracle. Offchain oracle nodes have gathered pricing information from selected sources, perhaps multiple exchanges or data providers, combined it according to the oracle’s rules, and posted the result to the oracle contract. When the lending protocol checks a user’s health, it reads that stored price as part of normal deterministic execution. Every validator sees the same oracle value because the data has already been committed to chain state.
Notice what happened there. The nondeterministic part (observing the outside world) occurred before the smart contract execution that relies on it. The deterministic part (reading the committed result) happens during normal onchain execution. That separation is the key mechanism that makes oracles possible.
Continuous feeds vs on‑demand oracles: which pattern should you use?
| Pattern | Update cadence | Cost profile | Latency | Best for |
|---|---|---|---|---|
| Publish-subscribe (feed) | Continuous updates | Amortized across readers | Low | Shared prices, many readers |
| Request-response (on-demand) | Per request | Pay-per-request | Higher | One-off API responses |
Oracle systems usually organize data delivery around one of two patterns because there are really two different problems to solve.
The first problem is that some data is important to many contracts at many times. Asset prices are the classic case. Here, it is wasteful for every protocol to ask separately for the same ETH/USD value. The usual design is a publish-subscribe feed: the oracle keeps a value updated onchain, and consuming contracts read it whenever needed. This is what people often mean by a price feed. The feed behaves like shared infrastructure. The oracle bears the work of updating it; many contracts reuse the result.
The second problem is that some questions are irregular, custom, or too large to keep updating continuously. A contract might need a specific API response, a one-time proof, or the outcome of a less common event. That fits a request-response pattern. A client contract asks for a particular piece of data, offchain nodes fetch or compute it, and the oracle returns the result onchain later. This saves continuous storage and update costs at the expense of latency and per-request complexity.
The design choice follows from mechanism, not fashion. If the same value will be read repeatedly by many contracts, a standing feed makes sense because the cost of updating can be amortized across many readers. If the question is unique or sporadic, on-demand retrieval is often cheaper and more flexible. That is why oracle documentation presents these two patterns as the standard choices.
A related distinction is between push and pull updates. In a push model, oracle operators regularly write fresh values onchain. In a pull model, the data may exist elsewhere first and only be brought onchain when a consumer or relayer triggers an update. Pyth’s design is a useful example here: publishers submit pricing information to its oracle program, the program aggregates reports into an aggregate price and confidence interval, and those constructed prices are then transferred cross-chain for consumers on other blockchains. The integration consequence is subtle but important: in pull-style designs, applications must ensure prices are refreshed when they actually need freshness.
How is trust established in oracle systems?
| Model | Primary trust assumption | Main strength | Main weakness | Best for |
|---|---|---|---|---|
| Single operator | Trust operator honesty | Simple and fast | Single point of failure | Prototypes, low-risk apps |
| Multi-node aggregation | Majority honest reporters | Fault tolerant | Higher coordination latency | General DeFi price feeds |
| First-party publication | Source publishes directly | Clear attribution | Requires provider buy-in | Market data from exchanges |
| Authenticity proofs | Cryptographic or TEE attest | Strong source evidence | Depends on crypto/hardware | High-integrity APIs |
| Economic staking | Slashing/rewards deter lies | Economic deterrence | Can be outpriced | High-value protections |
The hard part of an oracle is not moving bytes. It is creating a trust model that is good enough for the value at risk.
If a single operator reads a single API and posts the answer onchain, the mechanism is easy to understand, cheap, and often fast. But the trust assumption is also obvious: the operator could lie, go offline, be coerced, or simply make a mistake. A perfectly deterministic blockchain would then deterministically execute against bad data.
That is why the “oracle problem” is usually framed around three pressures: correctness, availability, and incentive compatibility. Correctness asks whether the reported value genuinely reflects the intended real-world fact. Availability asks whether the oracle continues to deliver updates when needed. Incentive compatibility asks whether the actors involved are rewarded for honesty and penalized for harmful behavior strongly enough that honest service is the rational strategy.
These pressures trade off against each other. A highly decentralized reporting network may improve fault tolerance, but coordination becomes harder and latency may rise. A very fast system may rely on a narrower trust base. A strong staking model may deter some attacks, but staking by itself does not prove that operators have actually validated the underlying data carefully. Even the developer-facing primers are careful on this point: economic mechanisms can reduce some attacks without eliminating lazy validation or governance concentration.
So when people ask whether an oracle is “decentralized,” the useful follow-up is: decentralized in what sense? Data sources may be concentrated even if reporters are numerous. Node operators may be numerous even if governance remains controlled by a small group. Updates may be aggregated from many parties but still depend on a single cryptographic attestation technology or a small set of maintainers. Decentralization here is a spectrum of trust distribution, not a binary badge.
What techniques do oracles use to prove data authenticity?
There are several broad ways oracle designs try to justify belief in their outputs, and each starts from a different first principle.
One approach is source authenticity. Instead of asking users to trust that an operator honestly copied a website or API, the oracle tries to produce evidence that the data really came from the claimed source and was not modified in transit. Ethereum’s oracle documentation points to authenticity proofs such as TLS-based methods and TEE attestations. Town Crier is an influential example of the TEE path: it used Intel SGX as a trusted-hardware backend to retrieve HTTPS data and attest it to smart contracts. The advantage is clear: if the proof system works, consumers can place less trust in the relay operator. The limitation is equally clear: the trust has shifted into cryptographic or hardware assumptions, which themselves can fail.
Another approach is multi-source, multi-node aggregation. Instead of relying on one observer, the oracle collects reports from several operators and often several underlying sources, then combines them according to a rule such as median or weighted aggregation. The underlying idea is that it should be expensive or difficult for an attacker to corrupt enough of the reporting surface at once. Chainlink’s decentralized oracle network model fits this family, with committees of nodes maintaining oracle functions and producing aggregated reports.
A third approach is first-party publication. API3’s dAPI design argues that the cleanest path is often for the data provider itself to operate the oracle infrastructure rather than having third-party middlemen resell its API onto chain. Pyth follows a related intuition in market data: it has multiple publishers, often market participants themselves, submit prices directly to the oracle program, which then computes an aggregate and a confidence interval. The attraction of this model is attribution. You know more directly who is speaking. The tradeoff is that adoption depends on the willingness and operational ability of source providers to participate.
A fourth approach is economic security. Reporters stake assets, accumulate reputation, or face slashing, disputes, or loss of future income if they misbehave. This does not make a false statement physically impossible. It tries to make dishonesty economically irrational. Chainlink’s whitepaper emphasizes staking and broader implicit incentives; Tellor’s materials center incentivized reporters and dispute mechanisms; BandChain restricts data submission to validators with stake and uses weighted median aggregation. But economics only works against attacks whose expected gain is lower than the expected cost. If a protocol secures billions of dollars using an oracle whose security budget is much smaller, incentives can be overwhelmed.
The deeper lesson is that oracle security is never just about one layer. A robust design usually combines who reported, how the data was authenticated, how many independent parties were involved, and what happens if they lie or disappear.
How do oracles aggregate reports and handle outliers?
| Method | Outlier resistance | Freshness | On-chain cost | Manipulation risk |
|---|---|---|---|---|
| Median / Weighted median | Strong | Fast | Moderate | Moderate (needs many corruptors) |
| Time-weighted average (TWAP) | Good (smooths spikes) | Slower (windowed) | Low | Lower as window length grows |
| DEX spot (onchain market) | Low | Instant | Low | High (easy to push) |
| Aggregate + confidence (Pyth) | Moderate | Fast | Moderate | Lower if publishers diverse |
Once multiple reports exist, the oracle must decide how to compress them into a value contracts can actually use. This is where abstract trust assumptions become operational rules.
For market prices, aggregation often aims to remove outliers without becoming too sluggish. Median-style methods are attractive because a few extreme reports do not move the output much unless they control enough weight. BandChain, for example, describes a weighted median of validator reports, with weighting tied to validator voting power and recency rules. Pyth combines publisher submissions into a single aggregate price and a confidence interval, which gives consumers not just a point estimate but also some indication of uncertainty.
That confidence idea is worth pausing on. An oracle does not always know one exact true price waiting to be discovered. Real markets are fragmented and moving. Different venues may quote slightly different values, and the answer may depend on timing and liquidity. A confidence interval acknowledges that the output is an estimate with dispersion, not pure revelation. For some applications, that is the right shape of honesty.
Oracle aggregation can also happen entirely onchain from market activity rather than from offchain reporters. This is the logic of DEX-based price oracles. But here the mechanism creates a different vulnerability: if the oracle reads a manipulable onchain spot price, an attacker may temporarily move that price and exploit protocols that trust it. Research on DeFi oracle attacks stresses exactly this point. Raw spot prices from automated market makers are dangerous because they can be pushed around within a transaction or over a small number of blocks. Time-weighted average prices, or TWAPs, raise the attack cost by forcing the manipulation to persist over time, though the protection depends on window length and market structure.
This is a good example of a likely misunderstanding. People sometimes hear “onchain oracle” and infer “therefore trustless.” But if the onchain value is just the recent output of a thin market, the oracle can still be economically fragile. Moving the trust boundary from offchain APIs to onchain liquidity does not remove the problem; it changes the attack surface.
What are the trade‑offs between oracle freshness and safety?
Oracle users want fresh data, but freshness is not the only thing that matters. Fast updates can improve responsiveness while also making manipulation or operator mistakes propagate more quickly into protocol behavior.
MakerDAO’s Oracle Security Module shows a different design instinct: sometimes the right answer is to delay adoption of a new oracle value on purpose. The OSM reads from an upstream price source, stores a current and next value, and ensures that newly propagated prices are not used until a configured delay has passed. The reason is straightforward. If a malicious or obviously broken value appears, governance or designated actors have time to intervene before the system acts on it.
That delay is not a free lunch. It increases safety against sudden bad updates, but it also means the protocol may temporarily operate on stale prices. In a rapidly moving market, stale prices create their own risks. The point is not that delay is universally better. The point is that oracle design is always about which failure you are choosing to make less likely.
The same tension appears in low-latency oracle products. BandChain emphasizes sub-second publication on an oracle-specific chain. Switchboard emphasizes millisecond-scale or sub-second latency modes and pull feeds that reduce constant streaming costs. These choices make sense for applications such as perpetuals or fast-moving trading systems. But they also mean the consumer must think carefully about what kind of mistakes can spread at that speed, and what assumptions are being made about the secure execution or attestation environment.
What additional services do modern oracle networks provide?
As oracle networks have matured, some have evolved from “data relays” into broader offchain service layers for smart contracts.
Chainlink’s whitepaper describes decentralized oracle networks, or DONs, as committees of nodes that provide not just data delivery but also networking, storage, and computation for offchain executables paired with onchain contracts. In that view, the oracle is no longer merely answering a question like “what is the price?” It may also be computing, sequencing, automating, or preserving confidentiality on behalf of a hybrid application.
That broader role helps explain features such as verifiable randomness, automation, confidential data retrieval, and fair sequencing services. The common thread is still the same one from the beginning: blockchains cannot natively perform certain tasks without compromising their design constraints, so an external-but-integrated service layer does those tasks and returns results in contract-usable form.
At that point the boundary between “oracle” and neighboring concepts starts to blur. If a network attests to data from another blockchain, it starts to resemble an interoperability protocol. If it continuously publishes values, it is producing a data feed. If it specializes in prices, it becomes a price oracle. These are not separate universes so much as different ways of looking at the same bridge between chain execution and external information.
What can go wrong if an oracle is compromised?
Oracle failures are so consequential because many protocols treat oracle outputs as if they were objective facts. A lending market liquidates positions. A derivatives platform settles a trade. A stablecoin system accepts collateral. An insurance contract pays out. If the oracle is wrong, the contract can still behave exactly as coded and yet produce the wrong real-world outcome.
That is why oracle manipulation has been one of the most common incident classes in DeFi research. The usual pattern is not that the smart contract’s arithmetic fails. The arithmetic works. The protocol simply reasons from a bad premise, such as a manipulable price or a compromised feed, and then executes economically harmful logic perfectly.
There are several ways this can happen. The source may be wrong. The relay may be dishonest. The aggregation rule may be too easy to game. The update cadence may allow stale or missing values at the worst moment. Governance may have excessive power over feed configuration. Cross-chain delivery may introduce delay or verification assumptions. A TEE may depend on hardware trust that later proves weaker than expected. A staking model may be secure only up to a lower dollar value than the protocol actually places at risk.
This is also why many robust systems add secondary controls around the oracle rather than treating the oracle as a single point of final truth. They may cap how fast prices can move, reject values outside expected bands, require freshness checks, apply delays, or use fallback feeds. The contract then trusts the oracle conditionally rather than absolutely.
How should a protocol choose an oracle for its risk profile?
If you are trying to evaluate an oracle, the practical question is not “which design is best in the abstract?” It is which assumptions am I willing to inherit for this application?
For some use cases, a highly specialized first-party feed may be the best fit because source attribution matters most. For others, a committee-based decentralized network may offer a better balance of resilience and broad coverage. For still others, a DEX-derived TWAP may be acceptable if liquidity is deep enough and the protocol’s economic parameters make manipulation unprofitable. A game may prioritize verifiable randomness; a lending protocol may prioritize conservative pricing and delay buffers; a high-frequency market may prioritize low latency and fast updates.
Here the mechanism should drive the decision. Ask where the data originates, how it is authenticated, how many independent parties are involved, how the final answer is aggregated, how updates are triggered, what happens if updates stop, what governance can change, and whether the oracle’s security budget is large relative to the value your contract puts behind it.
That last point is easy to underappreciate. Oracle security is not a static property of the oracle alone. It depends on the economic relationship between the oracle and the protocol using it. A feed that is adequate for a small application may be inadequate for a system whose failure would unlock a much larger payout to an attacker.
Conclusion
An oracle is the bridge that makes external information usable by smart contracts without letting nondeterministic data access break blockchain consensus. The essential move is simple: observe or compute something outside the chain, then commit the result onchain so contracts can read it deterministically.
Everything difficult about oracles follows from that bridge role. The problem is not merely getting data in; it is deciding why the chain should trust the data enough to act on it. That is why oracle design revolves around source authenticity, aggregation, incentives, availability, delay, and failure handling. If you remember one thing tomorrow, remember this: an oracle does not eliminate trust; it restructures it into a form a blockchain can use.
What should you understand about oracles before trading or depositing?
Understand the oracle assumptions that matter for your trade or deposit: where the data comes from, how often it is updated, how reports are aggregated, and what fallback protections exist. On Cube Exchange, combine that checklist with conservative execution choices to reduce the risk that a bad feed or stale price causes an unwanted liquidation or a bad fill.
- Fund your Cube account with fiat or a supported crypto transfer.
- Before placing an order, check the oracle feed metadata for the asset: last update time, reported confidence interval or spread, aggregation rule (median/TWAP), and any configured delay or OSM-like buffer.
- Open the market on Cube and choose an order type that fits the oracle characteristics: use a limit order if feeds are thin or delayed, or a market order only when the feed shows fresh, low‑confidence spreads.
- Add execution protections: set a stop‑loss or take‑profit and, for large trades, break into limit orders to reduce slippage and exposure to transient oracle anomalies.
Frequently Asked Questions
Oracles observe or compute facts offchain, commit a deterministic representation of that result onchain, and then smart contracts read the committed value during normal execution; the nondeterministic observation happens before execution so node consensus is preserved.
Continuous (publish–subscribe) feeds keep a value updated onchain and are efficient when many contracts reuse the same data (e.g., asset prices), while request–response oracles fetch or compute a specific, often one-off answer only when asked, trading higher latency per request for lower ongoing cost; choose the pattern based on reuse, freshness needs, and cost tradeoffs.
Decentralization is a spectrum: evaluate who controls data sources, who runs reporter nodes, what cryptographic or hardware attestations are required, and what governance powers can reconfigure the feed - many networks are decentralized in some dimensions but centralized in others.
Trusted Execution Environments (TEEs) and authenticated-fetch methods can produce strong source-authenticity evidence, but they shift trust into hardware or cryptographic assumptions and have known vulnerabilities (Town Crier and SGX are canonical examples), so they reduce some risks while introducing others.
Economic security (staking, slashing, reputation) tries to make dishonesty unprofitable but cannot physically prevent false reporting and is effective only insofar as the oracle’s economic security budget and incentive design outweigh attackers’ expected gains.
Aggregation rules such as medians or weighted medians reduce the influence of outliers and give robustness against some reporters, and confidence intervals can convey uncertainty, but aggregation cannot fix fundamentally manipulable underlying sources (for example thin onchain AMM prices) and its protection depends on the weighting, windowing, and underlying liquidity.
If an oracle supplies wrong data, smart contracts still execute correctly from their coded perspective but based on a false premise, causing liquidations, incorrect settlements, or other economic harm; robust systems therefore add secondary controls like bounds, freshness checks, delays, or fallback feeds rather than treating a feed as absolute truth.
First‑party publication (data providers operating their own publishers) improves attribution because the source speaks directly, making it attractive where source credibility matters, but it requires providers to onboard and operate infrastructure and can face legal/compliance and participation barriers.
Pick an oracle by asking which assumptions you are willing to inherit: where the data originates, how it is authenticated, how many independent parties are involved, how values are aggregated and refreshed, what governance can change, how failures are handled, and whether the oracle’s security budget is large relative to the value your protocol places at risk.
Push models have operators regularly write fresh values onchain; pull or on‑demand models bring data onchain only when a consumer triggers it - Pyth is an example of a pull-oracle that requires integrators to refresh onchain prices - and the choice affects freshness guarantees, costs, and who must ensure updates occur when needed.
Related reading