What is Canton Network?
Learn what Canton Network is, how its privacy-preserving sync domains and Daml contracts work, and why institutions use it for interoperable assets.
Introduction
For the token explainer, see CC.
Canton Network is a blockchain-style network built for a problem that ordinary public chains handle poorly: how do many institutions share applications, assets, and workflows without exposing all of their business data to everyone else on the network? That tension matters in finance because the value of a shared ledger comes from coordination, but the practical reality of markets is that most transactions are not meant to be globally visible. Canton exists to make those two facts coexist.
The usual public-chain answer is radical transparency: every validator sees the same state transition, even if the payload is encrypted or hidden behind additional cryptography. The usual enterprise-chain answer is fragmentation: each consortium or application runs its own silo, and interoperability becomes a bridge problem. Canton takes a different route. It is designed as a network of networks, where different applications and subnets can keep their own privacy, permissions, and governance, while still participating in a broader interoperable system.
That design is why Canton is interesting. It is not trying to be a general-purpose, retail-oriented chain in the style of Ethereum or Solana. Its target is multi-party institutional workflows, especially where assets, obligations, and approvals move across firms that cannot simply reveal their full transaction history to every other participant. The network’s core claim is that you can get composability and atomic coordination without universal data visibility.
The idea only makes sense if privacy is treated as part of the execution model, not as an add-on. That is the key to understanding Canton. Instead of starting from a globally replicated ledger and then trying to hide parts of it, Canton starts from the premise that different parties should receive different verifiable views of the same transaction. Everything else in the architecture follows from that choice.
Why do institutions need Canton Network’s privacy-preserving shared ledger?
A shared ledger is useful because it gives multiple parties a common way to agree on state. If Alice transfers an asset to Bob, everyone who needs to rely on that fact should be able to treat it as settled. But traditional public blockchains get this property by making the transaction ordering process global and widely replicated. That is powerful, but it creates an immediate privacy problem for institutions. A bank, custodian, or trading venue often cannot place all of its positions, counterparties, and workflows into a system where every validating node can inspect the complete transaction graph.
You can try to solve that with permissioning, private chains, or application-specific ledgers. But then another problem appears: fragmentation. If each workflow lives in its own isolated environment, moving an asset or coordinating a state change across applications becomes difficult. In practice this often leads to brittle integrations, trusted intermediaries, or bridges that weaken the security model.
Canton is built around the observation that these are not two separate problems. Privacy and interoperability are linked. If the only way to compose applications is through a single globally visible state machine, privacy will remain awkward. If the only way to preserve privacy is to split applications into isolated silos, interoperability will remain awkward. So Canton changes the basic unit of replication: not every node gets everything; each node gets only the contracts and transaction fragments relevant to the parties it hosts.
That shift helps with scaling too. If every node need not execute and store every transaction, the network avoids the bottleneck of a monolithic global state machine. The whitepaper and repository materials describe this as partitioning the global state. In practical terms, Canton trades the simplicity of “everyone sees everything” for a more selective form of coordination, where consistency is preserved only among the parties who actually share an economic or legal relationship in a contract.
How does Canton provide shared state without revealing all transaction data?
The simplest way to picture Canton is this: imagine a ledger where the important thing is not that everyone sees the same full document, but that each participant sees the correct pages, can verify the parts relevant to them, and can rely on the fact that conflicting updates will not both go through. That is roughly what Canton is doing.
Its smart contract model comes from Daml, a language and execution model built around explicit parties and explicit authorization. A contract in Daml is not just “some code at an address.” It specifies who must authorize its creation or archival, who can observe it, and who can exercise particular choices on it. That sounds like an implementation detail, but it is actually the foundation of Canton’s privacy model. If authorization and visibility are first-class parts of the contract itself, the runtime can determine who needs to learn what.
This leads to what the whitepaper calls sub-transaction privacy. A transaction may have several moving parts, but a given party does not need the entire transaction graph in order to validate the portion that affects its rights and obligations. Instead, that party receives a partial view (a sub-transaction) that is sufficient for verification. In other words, Canton does not merely hide data from uninvolved parties after execution. It arranges execution and distribution so uninvolved parties never need to process that data in the first place.
That is the main compression point for the whole network. Once you see that Canton is built around party-specific, verifiable views, many of its other design choices stop looking unusual. Privacy is not bolted onto a public ledger. Consensus, storage, and interoperability are all redesigned around selective disclosure.
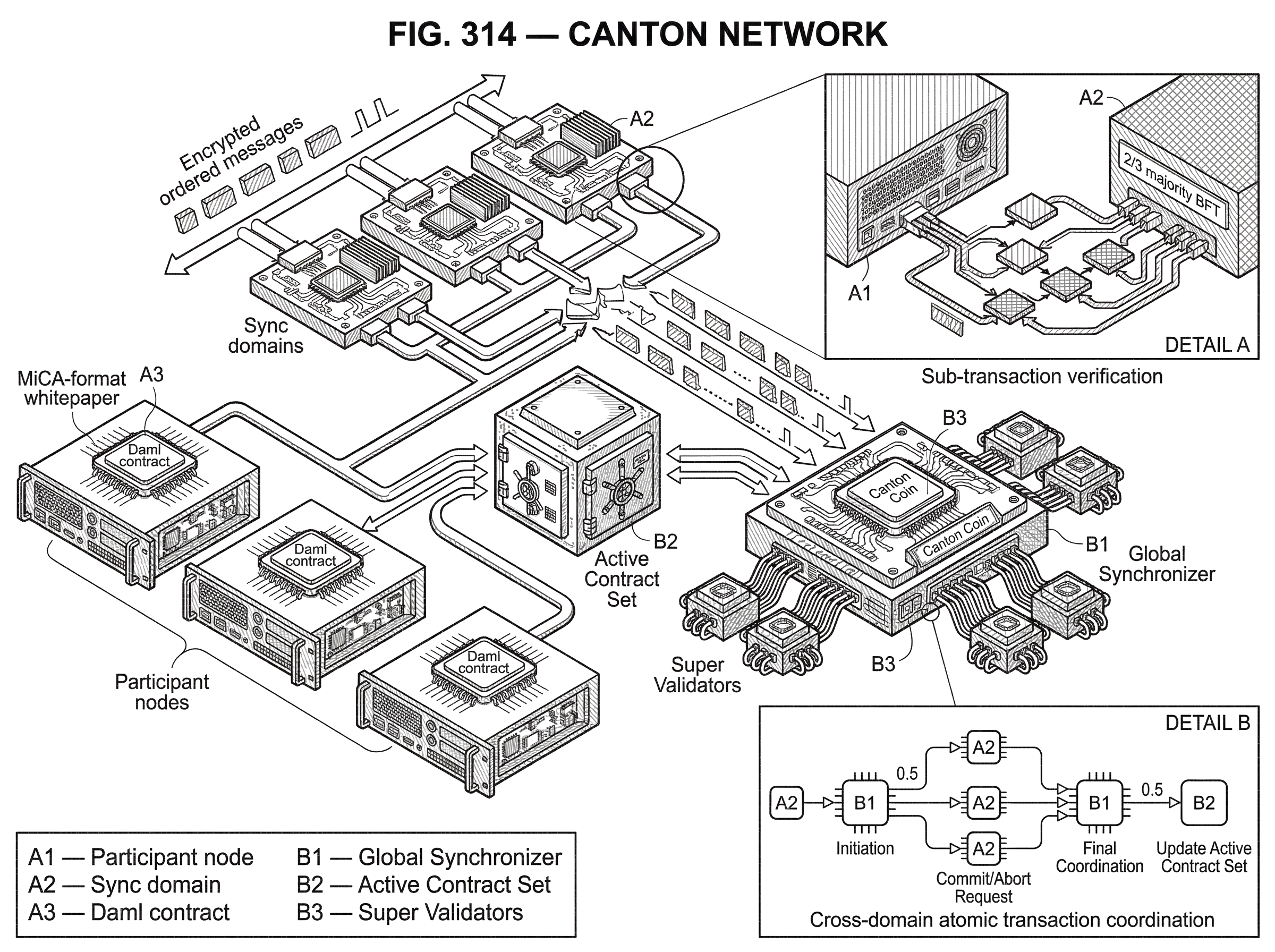
How does Canton model and manage contract state (Active Contract Set)?
Canton’s ledger model is contract-centric. The whitepaper describes the state of active contracts as the Active Contract Set, often shortened to ACS. A contract is active after it has been created and remains active until a consuming action archives it. This is somewhat analogous to a UTXO-style model in the sense that active objects exist until consumed, but the analogy has limits. Daml contracts can also support non-consuming choices, which means some actions can update workflow state or trigger effects without destroying the underlying contract.
That matters for real business processes. Many institutional workflows are not just simple transfers. They involve approvals, delegated actions, amendments, observations by third parties, and controlled interventions. A strict UTXO model can make these workflows awkward because everything tends to collapse into spend-or-don’t-spend semantics. Daml’s contract model gives Canton more room to encode who is entitled to act and what should remain visible after that action.
Suppose a custodian, an issuer, and an investor are involved in a tokenized asset position. The investor should know the position exists. The custodian may need to know custody terms and settlement status. A regulator or service provider might have observer rights for some facts but not others. On a monolithic public chain, the common answer is to put a compressed or encrypted representation on-chain and manage the rest elsewhere. In Canton, the contract itself can specify who sees it, and participant nodes only store and process the relevant contracts for the parties they host.
The security posture document makes this explicit: participant nodes do not see, store, or process contracts for which they are not involved. This is a stronger architectural statement than “data is encrypted on-chain.” It means the system reduces data exposure by limiting distribution at the protocol level.
What are Canton participant nodes and sync domains and how do they interact?
| Component | Role | Operator | Data visible | Ordering responsibility | Best for |
|---|---|---|---|---|---|
| Participant node | Host parties; run Daml runtime | Individual institution or operator | Contracts for hosted parties only | Participates in sub-transaction coordination | Local party execution and custody |
| Sync domain | Transport, timestamp, sequence messages | Canton Service Providers or consortium | Sequences encrypted requests | Assigns per-domain order | Cross-party coordination within a domain |
| Global Synchronizer | Decentralized interoperability backbone | Super Validators committee | Minimal public metadata; business data private | BFT total ordering for cross-domain commits | Cross-domain atomicity and public-permissioned interop |
Once state is partitioned, the network needs a way to coordinate updates among the parties who do matter. Canton’s basic architecture has two major pieces: participant nodes and synchronization domains, often shortened to sync domains or described in some materials as synchronizers.
A participant node is the ledger node that hosts parties and runs the Daml runtime for them. Applications connect to participant nodes through the Ledger API. If an institution operates on Canton, this is the component that represents its local view of contracts, permissions, and workflows.
A sync domain is the coordination layer. Its job is to transport messages, order them, timestamp them, and help participant nodes agree on the outcome of transactions that involve parties connected to that domain. The whitepaper describes sync domains as being operated by Canton Service Providers, and the repository materials emphasize that synchronizers can be deployed in different ways to meet different trust and operational requirements.
The key design move is that Canton does not require one universal ordering service for the entire world. Different applications or groups of participants can connect to different sync domains. Some can be private. Some can be public. Some can be more centrally trusted. Others can use Byzantine fault tolerant replication. This gives applications room to choose their own operating environment while still participating in a wider network.
That is why Canton is called a network of networks. The unit of composition is not a single global chain, but many application or domain-specific environments that can interoperate when connected through shared synchronization infrastructure.
How does Canton achieve consensus and prevent conflicts without one global ledger?
| Layer | Scope | Function | Fault model | Visibility |
|---|---|---|---|---|
| Stakeholder commit | Contract stakeholders only | Two‑phase commit for contract replication | Stakeholder quorum / application-level safety | Stakeholders see contract contents |
| Sequencing layer | Per sync domain | Assign timestamps and resolve conflicting requests | Varies by deployment (DB or BFT) | Orders encrypted requests; not business payloads |
| Global Synchronizer (BFT) | Public interoperability layer | Provide total order across domains for interop | 2/3 Byzantine Fault Tolerant | Minimal metadata public; business data remains private |
At first glance, selective visibility seems to make consensus harder. If not everyone sees the same transaction, how can the network still ensure consistency? Canton’s answer is a layered design the whitepaper calls proof-of-stakeholder.
The first layer is about the contracts themselves. Contracts are replicated to their stakeholders; the parties who need to rely on them. When a transaction changes a contract, the relevant stakeholders participate in confirming that change. The whitepaper describes this layer as a kind of two-phase commit among stakeholders.
The second layer is the sequencing layer. Sync domains receive encrypted transaction information and assign ordering information, such as timestamps or vector-clock-style ordering data, so conflicting requests can be resolved consistently. In distributed deployments, this sequencing can itself be backed by Byzantine fault tolerant consensus. The Global Synchronizer materials describe a 2/3 majority BFT model for message ordering and governance in that public interoperability layer.
The important principle is that consistency is scoped to where it is needed. Canton does not force all parties to agree on all application state. It forces the relevant parties to agree on the contracts and transitions they share, while sync domains provide enough common ordering to avoid double-spends or conflicting updates.
A worked example helps. Imagine an investor holds a tokenized treasury position in one application and wants to use it in a financing workflow in another. The investor’s participant node already hosts the contracts proving ownership. The financing application has its own contracts and logic. If the relevant parties are connected to a common sync domain, Canton can coordinate an atomic transaction: the collateral lock in one application and the financing state change in the other either both happen or neither happens. The custodian or issuer need only see the pieces relevant to their role. The ordering service need not inspect the business data in the clear; it sequences encrypted requests and helps the involved participant nodes converge on the same committed outcome.
That is the mechanism behind Canton’s claim of cross-application composability with privacy. The system is trying to preserve the economic property users care about (atomic state transition across workflows) without requiring a globally transparent state machine.
What is the Global Synchronizer and how does it enable cross-domain interoperability?
Canton existed first as a protocol and family of limited-access subnets. The more recent network story centers on the Global Synchronizer, which the official materials describe as the decentralized interoperability backbone of the Canton Network. This is the piece meant to make separate Canton-based applications and domains part of a broader public-permissioned environment.
Mechanically, the Global Synchronizer is a sync domain operated by a set of independent organizations called Super Validators. The official Global Synchronizer page says it uses a 2/3 majority Byzantine fault tolerant protocol for message ordering and confirmation, and the Canton Foundation materials present the Foundation as providing governance and oversight for this shared infrastructure.
This tells you what kind of openness Canton is aiming for. It is not permissionless in the Bitcoin sense, where anyone can anonymously join block production under the same rules as everyone else. Several sources instead describe a public permissioned or committee-style model. The public aspect is that the network is meant to be common infrastructure rather than a private silo; the permissioned aspect is that the operators of the key interoperability layer are selected, organized, and governed.
That design fits Canton’s institutional target market, but it also defines the tradeoff. You get more predictable governance, operator identity, and operational coordination. You give up some of the open validator-market properties that characterize more permissionless chains.
When can Canton applications compose atomically across domains, and what are the limits?
| Topology | Atomicity possible | Required action | Typical latency | Main limitation |
|---|---|---|---|---|
| Shared sync domain | Yes | None beyond connectivity | Sync-domain sequencing delay | Requires domain trust and ops |
| Separate domains, no overlap | No | Reassign contract or add common domain | Higher due to migration/coordination | Operational overhead; not automatic |
| Reassigned contract | Conditional | Signatories move contract between domains | Migration plus sequencing time | Needs signer cooperation and governance |
Canton’s strongest technical promise is atomic interoperability across applications. But this promise is not unlimited, and the limit is worth understanding because it reveals how the system works.
The whitepaper states that cross-subnet atomic transactions are possible only when all transaction participants share at least one common sync domain. That condition is easy to miss, but it is fundamental. Atomicity requires some shared coordination point. Canton avoids global ordering, but it does not avoid the need for common ordering where a single atomic transaction spans multiple participants or applications.
So if two applications live in entirely separate coordination worlds with no shared sync domain among the relevant parties, Canton cannot simply conjure atomic composition out of nothing. A contract can also be reassigned between sync domains by its signatories, which gives the network a way to move state into a topology where future compositions are possible. But that is still an operational step, not magic.
This is a good example of Canton’s general pattern. It relaxes the assumptions of a monolithic chain, but in return it introduces topological conditions. The network is more flexible than “everyone must be on one chain,” yet less unconstrained than “any two applications can always compose.” Whether a workflow composes atomically depends on how the parties and domains are connected.
How does Canton balance privacy, auditability, and data deletion (right to be forgotten)?
Canton’s privacy story is not only about who sees live transactions. It also extends to history. Traditional public blockchain culture treats immutable, fully replicated history as almost sacred. Institutions often do not. They may need long audit trails, but they may also need data minimization, locality controls, and removal of personal information.
Canton explicitly supports history pruning and redaction. The whitepaper and security materials say nodes can prune archived contracts and move historical data to offline storage, and that this can support GDPR-style compliance and auditable removal of PII. The system continues to exchange cryptographic commitments about shared state, so a malicious party cannot easily repudiate the past simply because some detailed local records were pruned.
This is not the same thing as public-chain immutability. It is a different balance. Canton keeps enough cryptographic evidence and shared commitments to preserve trust in state transitions, while allowing local operators to reduce retained history. For institutions, this may be a feature. For readers coming from Bitcoin-style design, it may feel like a weakening of one of blockchain’s core promises. In truth it is a modeling choice: Canton prioritizes controlled auditability over universal permanent replication.
Why does Canton use Daml, and how does Daml enable party-specific visibility?
It would be easy to describe Canton as just an interoperability layer with privacy, but that would miss how tightly it depends on Daml’s contract model. Canton is not a generic execution environment where arbitrary virtual-machine bytecode happens to be routed privately. Its privacy and authorization properties are tied to a smart contract language that makes parties, observers, signatories, and controllers explicit.
That gives developers a more natural way to represent multi-party workflows than account-based systems usually do. If a workflow requires one party to sign, another to observe, and a third to exercise a specific contingent right, those roles are directly represented in the contract. Canton can then faithfully implement those semantics across distributed participants.
This also means Canton is not maximally general in the sense some chain ecosystems are. Its design is optimized around a certain kind of application: structured, institutional, multi-party agreements with explicit rights and obligations. That is a strength when the application fits. It is less obviously the right tool for highly open-ended, adversarially composable consumer crypto environments.
What real-world workflows and applications are built on Canton Network?
The official materials consistently point to asset tokenization, synchronized financial markets, custody and wallet integrations, and validator or application operator onboarding. That is abstract until you look at concrete workflows.
One documented example is the USDC xReserve flow. A user sends USDC on Ethereum to Circle’s xReserve contract with metadata specifying the Canton party that should receive the funds. After Ethereum finality and Circle’s attestation, the xReserve operator writes the corresponding contract on Canton. Withdrawals reverse the process by burning on Canton and releasing on the destination chain after validation. This example is useful because it shows Canton in contact with another ledger environment, not as a sealed universe. The cross-system bridge still has operational dependencies and latency, but the Canton side preserves the party-based model and contract semantics.
The ecosystem materials also mention tokenization, bridges and oracles, analytics, DeFi, and network-as-a-service tooling. The homepage highlights a DTCC initiative to tokenize a subset of DTC-custodied U.S. Treasuries using ComposerX and Canton’s privacy-preserving layer. That should be read as evidence of institutional engagement, not proof that every market-level claim is already fully realized. But it does show what kind of users Canton is trying to attract: firms that want programmable shared infrastructure without broadcasting sensitive state to the world.
How is Canton governed and what role does Canton Coin play?
Canton’s shared interoperability layer is not only technical infrastructure; it also has governance and economics around it. The Global Synchronizer page says Super Validators operate the infrastructure and govern changes through on-chain voting. The Canton Foundation site frames the Foundation as the body providing governance and oversight for the Global Synchronizer.
There is also a native utility token, Canton Coin, tied specifically to the Global Synchronizer. According to the MiCA-format whitepaper, it is used to pay for Global Synchronizer usage and is minted by participants who provide utility to the network, such as Super Validators, validators, and application providers. The design uses a burn-mint equilibrium: users burn tokenized fee units to consume network resources, and service providers mint tokens for supplying infrastructure or applications.
Two points matter here. First, the token is described as optional for users of the Global Synchronizer; participants can also arrange third-party or fiat-denominated traffic balances. That lowers the extent to which using Canton requires speculative token exposure. Second, governance power over protocol parameters and Super Validator actions sits with a 2/3 majority of Super Validators rather than with token holders broadly. So this is not a token-governed public chain in the usual crypto sense. It is much closer to governed infrastructure with a native utility and incentive layer.
What are Canton Network’s main tradeoffs and potential failure modes?
Canton is best understood through its tradeoffs, because each one follows directly from the problem it is solving.
The first tradeoff is operator structure versus open decentralization. Canton’s public interoperability layer relies on identifiable operators and formal governance. That suits institutions that care about accountability and controlled evolution. It also introduces concentration risk. If governance is committee-driven and onboarding new key operators requires approval, resilience and neutrality depend on how that committee behaves in practice.
The second tradeoff is topological composability versus universal composability. Applications can compose atomically when the relevant parties share a sync domain. That is powerful, but it is not the same as saying every application on the network can automatically compose with every other. Network topology matters.
The third tradeoff is privacy and regulatory fit versus universal auditability. Canton deliberately limits who sees and stores transaction data, and it allows pruning and redaction. That makes sense for regulated institutions. It is less aligned with the public-chain ideal that anyone should be able to reconstruct all history from full node data.
The fourth tradeoff is language-specific strength versus ecosystem breadth. By building closely around Daml, Canton gets a precise model of authorization and visibility. But this also means its design center is narrower than that of general-purpose virtual-machine chains with huge developer communities and looser execution assumptions.
None of these tradeoffs are accidental. They are the price of aiming at a world where privacy, legal accountability, and cross-firm workflow automation matter more than maximal openness.
Conclusion
Canton Network is a privacy-preserving network of interoperable Smart Contracts environments built for institutional workflows. Its central idea is simple but powerful: parties should be able to share state transitions and compose applications without forcing the whole network to see the full transaction. From that idea flow its contract model, selective data distribution, sync domains, and committee-operated Global Synchronizer.
If you remember one thing, remember this: Canton changes blockchain coordination by making verifiable partial views, not global transparency, the default. That makes it a distinctive design for tokenized assets and multi-party finance; and it also explains exactly why its governance, interoperability conditions, and decentralization model differ from the public chains most crypto users already know.
How do you get Canton Network exposure?
You can get Canton Network exposure by buying the network’s tradable token or listed market on Cube Exchange. Fund your Cube account, open the Canton spot market (for example CANTON/USDC if listed), and place a spot order; the steps below show the exact funding and execution actions.
- Deposit fiat or a supported crypto (USD, USDC) into your Cube account using the fiat on-ramp or a direct transfer.
- Search for the Canton market on Cube (e.g., CANTON/USDC) or the listed token pair and open the spot trading page.
- Choose an order type: use a limit order for price control or a market order for immediate execution; enter the token amount or quote currency to spend.
- Review estimated fill, fees, and slippage, then submit the order and optionally set a stop-loss or take-profit.
Frequently Asked Questions
Canton gives each participant a verifiable, party-specific view (a “sub-transaction”) so uninvolved nodes never need to see or process confidential parts of a transaction, while synchronizers (sync domains) provide encrypted sequencing and coordination so the involved parties can still complete atomic cross-application workflows. However, atomic cross-domain composition requires the relevant parties to share at least one common sync domain.
Double-spend and conflict-safety are handled by scoping consistency to stakeholders: contracts are replicated and confirmed among the parties who need them (a stakeholder-level two‑phase commit), and sync domains supply ordering (timestamps/vector-clock style data) - the Global Synchronizer can use a 2/3 BFT ordering layer for cross-domain sequencing.
No - Canton only guarantees atomic cross-subnet transactions when all participants share at least one common sync domain; if participants are connected to entirely separate coordination domains, atomic composition is not automatic (contracts can be reassigned between domains by signatories as an operational workaround).
Daml is core to Canton’s model: contracts declare parties, signatories, observers, and controllers, enabling selective disclosure and authorization-aware execution; because Canton is tightly coupled to Daml’s party-centric model, it is optimized for structured institutional multi‑party workflows rather than for maximally general EVM-style, open-ended smart‑contract composition.
Canton supports history pruning and redaction so nodes can remove or move historical records (supporting GDPR-style needs), while retaining cryptographic commitments and shared evidence so past state transitions cannot be trivially repudiated - this is a deliberate tradeoff versus public‑chain-style universal immutability.
The Global Synchronizer is run by a committee of identified Super Validators under a public‑permissioned, foundation‑backed governance model (the Canton Foundation/Global Synchronizer Foundation), so it is not permissionless in the Bitcoin sense; this yields accountable operator identity and predictable governance at the cost of greater centralization risk compared with open permissionless chains.
Key tradeoffs include: a committee/operator structure (predictable governance) versus open decentralization; topological rather than universal composability (atomicity depends on shared sync domains); privacy and data minimization versus global permanent auditability; and Daml‑centric strengths versus a narrower developer ecosystem. These are intentional design choices aimed at institutional use cases.
Participant nodes only host and execute contracts for parties they represent and do not see, store, or process contracts for which they are not involved, which reduces protocol-level data exposure compared with encrypting all data on a globally replicated chain.
Many governance and operational specifics remain underspecified in public materials - for example, exact Super Validator selection/onboarding rules, detailed Canton Coin tokenomics, and low‑level cryptographic primitives for privacy and redaction are described at a high level but lack full public technical or governance specifications. These are open or partially documented questions rather than settled facts.
Related reading