What is a Utility Token?
Learn what utility tokens are, how they work, what gives them real value, and why use, speculation, and legal treatment often overlap.
Introduction
Utility tokens are blockchain-based tokens whose core purpose is to let someone use a product, service, or network function. That sounds straightforward, but it turns difficult the moment the token can also be traded, hoarded, or promoted as something that might rise in value. The central question is not whether a token is called a utility token, but what the token actually does in the system and why someone would reasonably want to hold it.
That question matters for three different reasons at once. It matters technically, because a token has to connect to some mechanism; access control, payment for computation, entitlement to a service, or another function the network can enforce. It matters economically, because the token only has a durable role if holding or spending it solves a real coordination problem that ordinary database entries or fiat payments do not solve as well. And it matters legally, because in many jurisdictions a token marketed as a utility can still be treated like a security or another regulated instrument if buyers are really relying on others to increase its value.
The idea becomes much easier once you separate use from investment. A utility token is strongest when people acquire it mainly because they need it for something now or very soon: to consume computation, unlock a feature, redeem a service, post collateral for an in-network action, or interact with an application in a way the protocol recognizes. The idea weakens when the token is mostly a fundraising chip for a future platform, especially if buyers are counting on a team to build the thing that will make the token valuable later.
How does a token grant the right to perform actions in a protocol?
At first principles, a token is just a digitally scarce entry in a ledger. By itself, that entry means nothing. It becomes meaningful only when some rule says, in effect, “if you control this token, you are allowed to do X.” The X is the utility.
That utility can take several forms, but the underlying mechanism is the same. The network, application, or service checks whether you hold the required token balance or whether you spend a token as part of an action. If the condition is met, the system allows the action to proceed. Without that link between token state and permitted behavior, there is no real utility; only a tradable object with a story attached to it.
This is why utility tokens are often compared to digital tickets, prepaid credits, or API keys. Those analogies help explain the access function: a ticket gets you into a venue, a prepaid credit lets you consume a service, an API key lets software call a platform. But the analogy fails in an important way. A blockchain token is usually more transferable, more programmable, and more easily traded on secondary markets than an ordinary ticket or account credit. That extra transferability is useful for interoperability, yet it also creates speculation, and speculation can overwhelm the original purpose.
A simple example makes the mechanism concrete. Imagine a decentralized storage network. Users want data stored; providers want to be paid for storage capacity. The network could require users to pay for storage in a native token. In that design, the token is not representing equity in the storage company, and it is not inherently a claim on profits. Its immediate role is narrower: it is the unit the protocol accepts for buying storage and perhaps for posting deposits or paying for retrieval. If the service is live and people need the token to use it, the token has a genuine utility anchor.
Now change one assumption. Suppose the storage network is not operational yet, but the team sells the token early to fund development, telling buyers the token may appreciate as adoption grows. The token may still be intended for future utility, but economically the buyer is no longer mainly purchasing access to storage. The buyer is financing a venture in hopes that others will make the token more valuable later. That is the point where the idea of “utility” becomes contested.
Why do projects issue utility tokens instead of using fiat or accounts?
If an application can simply charge dollars by credit card, why introduce a token? That is the right question, because many token designs fail precisely here. A token is justified only if it solves a coordination problem that the application would otherwise struggle with.
One common problem is shared infrastructure without a central operator. In a public blockchain system, there may be no single company maintaining user accounts, billing relationships, and access permissions for everyone. A token can provide a native unit that the protocol itself can verify and transfer. This allows strangers to transact under common rules without needing each pair of users to set up separate payment and settlement arrangements.
Another problem is aligning supply and demand for a scarce network resource. Ethereum is the canonical example. Executing transactions consumes computation by the network, so execution is not free. Users pay fees denominated in Ether for that computational effort, measured through gas. In that setting, the token is not merely decorative. It is the economic meter for a shared resource. The mechanism matters: because each operation imposes costs on validators and on the network as a whole, attaching a token-denominated fee discourages spam and allocates scarce execution capacity to those willing to pay for it.
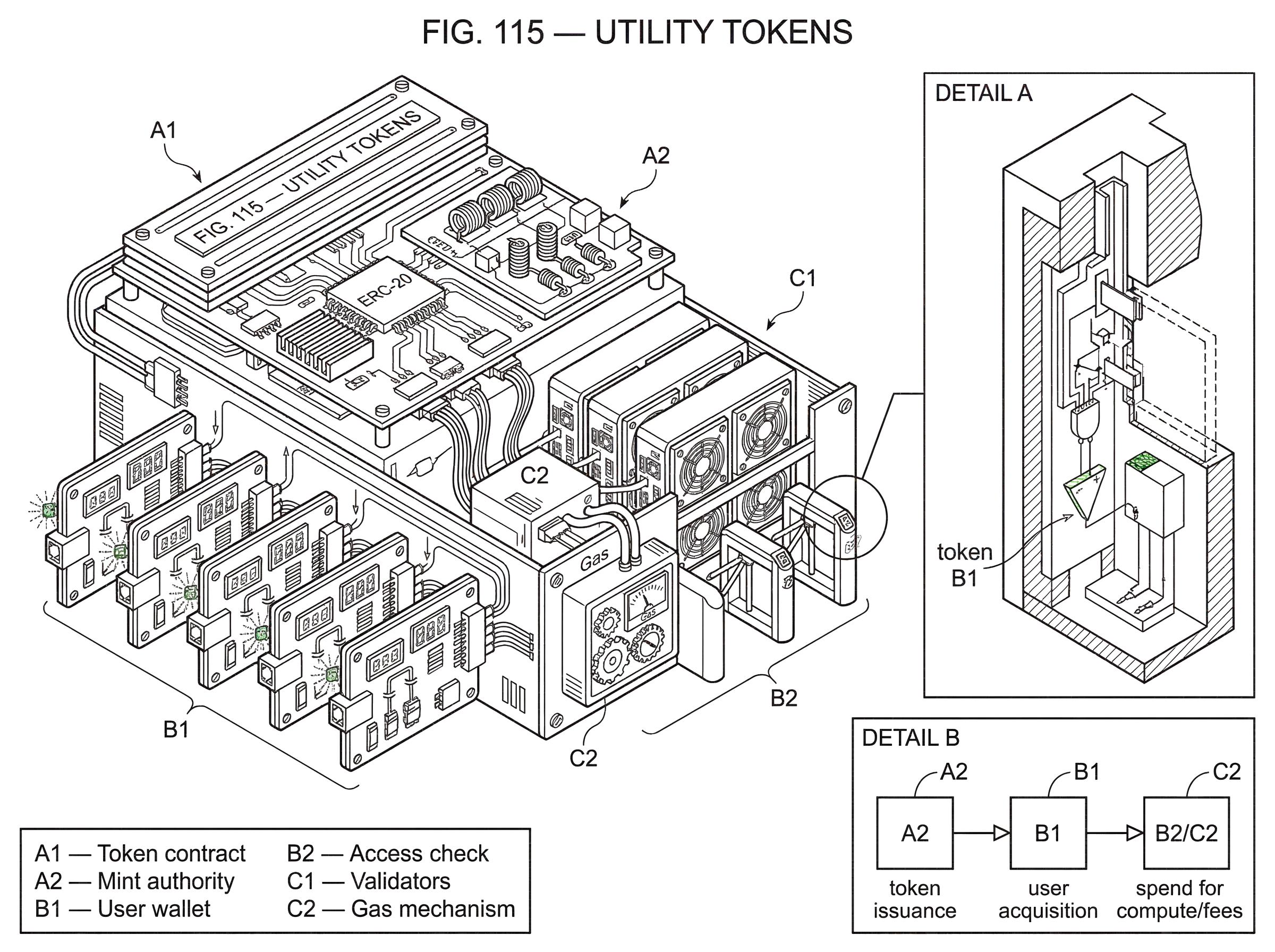
A third problem is programmable interoperability. When access rights are encoded as standard tokens, wallets, applications, and smart contracts can all recognize and handle them. On Ethereum, many utility-like tokens are implemented using the ERC-20 interface, which standardizes functions such as transfer, balanceOf, approve, and transferFrom. That standard does not make a token a utility token by itself. It simply makes the token easier for other software to understand. The utility comes from the surrounding application logic that says what possession or spending of the token enables.
This distinction is easy to miss. A token standard defines how tokens move; it does not define why they matter. An ERC-20 token can represent prepaid service credits, governance power, a speculative asset, a stablecoin, or something that behaves economically like a security. The same is true on other chains. On Solana, for example, a token is anchored by a Mint Account, with balances held in Token Accounts or Associated Token Accounts. Those structures tell the network how the asset is represented and transferred. They do not by themselves tell us whether the token is giving access to storage, in-game functionality, governance rights, or nothing meaningful at all.
What technical and economic features make a token genuinely useful?
A utility token becomes real when the token is tied to an enforceable bottleneck in the system. In plain language, there has to be something users cannot do unless they hold or spend the token, and that requirement must be more than arbitrary decoration.
Sometimes the bottleneck is consumption. A user spends tokens to obtain computing time, storage, bandwidth, AI inference, marketplace placement, or another service. Sometimes the bottleneck is admission. Holding the token unlocks features, access tiers, or participation in a closed environment. Sometimes the bottleneck is protocol behavior. A token may be required to register a name, create a resource, submit a transaction class, or bond against misuse.
The strongest designs make the token’s role hard to remove without changing the application’s architecture. If the team could quietly replace the token with a conventional database entry or a fiat checkout flow without affecting the system, then the token’s “utility” may be superficial. That does not automatically make it worthless, but it suggests the token is serving branding or financing more than mechanism.
This is also where transferability becomes a tradeoff. Transferable tokens make secondary markets possible, and secondary markets can be useful. They let users who no longer need access sell to users who do. They can help price discovery and reduce friction for new entrants. But once a token trades freely, many holders will buy not to consume a service but to speculate on future demand. A utility token can therefore be technically functional and still economically dominated by investment behavior.
That tension explains why regulators often focus on substance over labels. Both the UK FCA and Switzerland’s FINMA explicitly describe utility tokens in functional terms (tokens intended to provide access to an application, product, or service) while also warning that classification depends on the rights actually conferred and the economic role the token plays. A whitepaper calling something a utility token does not settle the matter.
How can a token be used to meter and pay for network resources?
Consider how a token can support a decentralized compute platform. The platform lets developers run code across many independent nodes. Those nodes contribute resources and expect compensation; users want predictable access to computing power; the protocol needs a way to meter demand and prevent abuse.
If the system requires payment in a native token for each unit of computation, several things happen at once. First, the user must obtain the token in order to consume compute. That creates direct demand tied to actual use. Second, the protocol can charge more for more expensive operations, so resource allocation is not arbitrary. Third, node operators can be compensated in the same unit the protocol collects, which reduces the need for an off-chain billing layer. The token is acting as a native accounting instrument for a resource that the protocol itself can verify.
Ethereum’s gas model illustrates this logic, even though Ether also has broader monetary and ecosystem roles. Each transaction requires computational effort. Gas measures that effort, and fees are paid in Ether. The important point is causal: the fee is not there because tokens are fashionable; the fee is there because computation on a shared state machine is scarce and costly, and the network needs a way to price and ration that scarcity.
But the same example also shows the limit of the utility-token idea. People do not hold Ether only to buy computation. They may hold it as collateral, as a reserve asset within crypto markets, or as a speculative investment. So a token can have genuine utility and still derive much of its market behavior from something else. Utility is often one layer of a token’s identity, not the whole thing.
How are utility tokens implemented on different blockchains (ERC‑20, Solana)?
| Platform | Token object | Balance storage | Access enforcement | Trust risks |
|---|---|---|---|---|
| Ethereum (ERC-20) | Contract token | Contract storage balances | Smart contracts verify ownership | Mint/owner authority common |
| Solana (Mint + ATA) | Mint account + ATA | Associated Token Accounts | On-chain programs or off-chain apps check ATA | Mint/freeze authorities possible |
| Cosmos SDK (bank) | Denom + supply module | Native account balances | Module-level permission checks | Module authorities control supply |
Mechanically, most utility tokens are just fungible token contracts or native chain assets plus surrounding rules. On Ethereum, a common route is ERC-20. The standard defines a minimal interface so wallets and applications know how to query balances and move tokens. The contract exposes functions like totalSupply() and balanceOf(account), and transfer functions such as transfer(to, value). That interoperability is why ERC-20 became so widely used for application tokens.
However, the standard also shows that utility lives above the interface layer. The ERC-20 specification says nothing about what service the token unlocks. It only standardizes movement and allowances. A developer still has to build the application logic that checks token balances or requires token payments before performing a service. If a project says “our token gives access to premium features,” the actual access control usually sits in another contract or in an off-chain service that verifies on-chain ownership.
The same pattern appears on Solana, though the account model is different. A Mint Account defines the token itself, including supply and authorities. User balances sit in Token Accounts, often via Associated Token Accounts whose addresses are deterministically derived from owner and mint. That design changes data layout and developer workflow, but the conceptual structure is familiar: the token program handles issuance and transfer, while the application determines what owning or spending the token entitles you to do.
Across architectures, a few implementation choices matter because they affect trust. Who can mint more tokens? Can transfers be frozen? Is supply capped? Can metadata or permissions change? These are not secondary details. If a utility token is meant to be a stable access right, holders care whether an admin can arbitrarily dilute supply, blacklist users, or rewrite conditions. Technical centralization can undercut the promise of neutral utility even when the token’s advertised function sounds straightforward.
What common mistakes lead people to mislabel tokens as utility tokens?
The most common misunderstanding is to think that a token is a utility token because it has some use somewhere. That bar is too low. Almost any token can be given a nominal use after the fact. The real question is whether the use is central enough that it explains why the token should exist and why users would demand it independently of speculation.
A second misunderstanding is to confuse utility with governance. Governance tokens give holders the ability to propose or vote on changes. Utility tokens give access to a service or network function. In practice, many projects blur the two by using one token for both. That can be efficient, but it also muddles incentives. Someone who buys to influence protocol rules is not the same as someone who buys to consume bandwidth or storage. When one token tries to be access key, governance right, reward asset, and speculative vehicle all at once, each role can distort the others.
A third misunderstanding is to assume that being tradable makes a token non-utility. Not necessarily. The FCA explicitly notes that utility tokens may trade on secondary markets and may be used speculatively without automatically becoming regulated securities. Tradability alone does not determine economic substance. What matters is the overall design: what rights the token gives, whether the network is usable, whether the token is sold for consumption or investment, and how much the buyer’s hoped-for gain depends on a managerial team.
Why do regulators sometimes treat utility tokens like securities?
The legal difficulty exists because utility and investment can coexist. A token can genuinely unlock a service and still be sold in a way that looks like fundraising for a venture.
In the United States, the SEC’s framework for digital assets applies the Howey “investment contract” analysis: whether there is an investment of money in a common enterprise with a reasonable expectation of profits derived from the efforts of others. For utility-token discussions, the decisive pressure point is usually the last part. If purchasers are relying on an active participant (a promoter, sponsor, or development team) to build, operate, support, and increase the value of the network, then the token may look less like a consumptive instrument and more like a security.
The same framework also explains what tends to push a token in the opposite direction. The SEC staff noted that the presence of actual use or consumption makes a token less likely to satisfy the test: a fully developed and operational network, immediate functionality, token value correlated with the cost of goods or services, limited transferability, and weaker prospects for appreciation. None of these factors is individually decisive, but together they show the logic. The more a token behaves like something bought to be used, the less it resembles an investment contract.
FINMA expresses a similar idea in a different legal vocabulary. A token intended solely to confer digital access to an application or service is not treated as a security only if it is already usable in that way at issuance; if it functions wholly or partly as an investment, FINMA may treat it as a security. That is a notably strict formulation because it focuses on present usability, not merely future intent.
The SEC’s DAO Report remains a useful cautionary example even though DAO tokens are not the same thing as classic utility tokens. The report emphasized that automation through smart contracts does not remove an arrangement from securities law, and that token-holder voting did not negate reliance on the managerial efforts of others where a core group still shaped success. The broader lesson is simple: code does not erase economic reality.
What design failures commonly cause utility‑token projects to fail?
| Failure mode | What happens | Red flag | Mitigation |
|---|---|---|---|
| Fake utility | Token not needed for service | Users prefer fiat checkout | Add enforceable bottleneck |
| Timing (prelaunch) | Token sold before network live | Buyers fund development | Delay sale until usable |
| Unstable incentives | Price vs usage conflict | Rising price harms users | Use dual-token or burns |
Most failures come from one of three places: the utility is fake, the timing is wrong, or the incentives are unstable.
The first failure is fake utility. The token is inserted into a product that does not need it. Users would rather pay with ordinary money, and the token adds friction without adding coordination benefits. In that case, token demand depends mostly on marketing and exchange listings, not on service usage. Once speculation fades, the token’s reason for existing becomes hard to defend.
The second failure is timing. The network is not live when the token is sold. Buyers are told the token will later unlock a service, but for now the token mainly finances development. This is precisely the scenario where legal and economic skepticism grows, because the buyer is depending on future efforts by a team rather than current consumptive use. A token can move over time from a security-like fundraising instrument toward a more utility-like consumptive asset if the network matures, but that transition is not automatic and must be assessed on actual facts.
The third failure is unstable incentives. If a token must simultaneously remain cheap enough for users to spend and expensive enough to reward operators and attract investors, those goals can clash. A rising token price can make the service costly; a falling price can make providers or developers undercompensated. Designers often try to manage this with burns, emissions, staking, or dual-token structures, but these add complexity rather than eliminating the underlying tension.
The broader token market offers cautionary evidence for designs where narrative outruns mechanism. The collapse of TerraUSD was not a utility-token failure in the narrow sense (it was an algorithmic stablecoin crisis) but it illustrated a general lesson about token systems: if the core economic loop depends on confidence and market reflexivity more than on robust underlying demand, stress can cause the mechanism to fail violently. Utility tokens are safer when their value proposition rests on boring, repeated use rather than on self-reinforcing expectations.
How do you assess whether a claimed utility token is credible?
| Question | Yes → utility | No → fundraising |
|---|---|---|
| Enables action? | Required for access/use | Mostly tradable/speculative |
| Network live? | Fully operational service | Prelaunch promise of future use |
| Buyer intent? | Majority buy to consume | Buyers expect appreciation |
| Issuer control? | Limited admin discretion | Can dilute or freeze supply |
The most useful test is to ask a sequence of causal questions. What concrete action does the token enable? Why must that action be token-mediated rather than handled by ordinary payment rails or a centralized account balance? Is the service already live? Are users buying the token mainly to consume something now, or mainly because they expect others to make it more valuable later? And how much discretion remains in the hands of a team that can alter supply, pricing, permissions, or market support?
You can also look for evidence that use is not merely decorative. Does demand for the token plausibly rise with service usage rather than only with exchange speculation? Is token pricing related to the cost of the service it unlocks, or is it untethered from consumption? Are there mechanisms that reduce purely passive holding and encourage actual use? None of these questions gives a mechanical yes-or-no answer, but together they reveal whether the token is anchored to a functioning system.
A practical clue is whether the system still makes sense after you remove the token price chart from view. If the product, service, or network rule would still be coherent and valuable to users, then there may be a real utility layer. If the whole story collapses without reference to market appreciation, the token is likely operating more as a speculative instrument than as a useful one.
Conclusion
A utility token is, at base, a token whose job is to let its holder do something inside a blockchain-based system. That idea is simple; what complicates it is that access rights are often bundled with transferability, speculation, governance, and fundraising. The label matters less than the mechanism.
The durable version of the idea is easy to remember: a real utility token is bought because it is needed for use, not merely because it might go up. The farther a token moves from present, enforceable utility and toward dependence on a team’s future efforts, the less secure the “utility token” description becomes; economically, technically, and often legally.
How do you evaluate a token before using or buying it?
Evaluate a token’s mechanics and on‑chain behavior before you buy or approve it. These checks reveal whether a token’s value comes from real, enforceable utility or from speculation; if you choose to trade, fund your Cube Exchange account and execute the order on Cube.
- Inspect the token contract on a block explorer (Etherscan, Solscan): confirm the source is verified and note roles and functions such as totalSupply(), owner/minter, mint/burn, and any pause or freeze methods.
- Review tokenomics and vesting schedules: find the distribution table in the whitepaper or contract, record team/treasury allocations, and note exact unlock dates and cliffs.
- Check liquidity and holder concentration on‑chain: view DEX pool reserves, daily transfer volume, and the percent held by top addresses; flag high concentration (e.g., top 10 > 20%) or thin pool depth relative to your planned trade.
- Fund your Cube account with fiat or a supported crypto so you can act on your decision.
- Open the token market on Cube and place a limit order for larger buys (use a market order only for small, immediate fills); set conservative slippage (for example 0.5–2%), review estimated fees, then submit.
Frequently Asked Questions
Transferability makes secondary markets possible and can improve interoperability and resale, but it also encourages speculation that can overwhelm the token’s access function; regulators stress that tradability alone does not determine whether a token is a utility or a security - substance and how the token is used matter.
A credible utility requires an enforceable bottleneck: the system must check token ownership or spending before permitting an action, and the token’s role should be hard to remove without redesign; implementation details that matter include who can mint or freeze tokens, whether supply is capped, and whether permissions can be changed.
Selling tokens before the network is live turns the purchase into financing of future development rather than immediate consumption, which raises economic and legal scrutiny because buyers may be relying on a team to create value rather than on present use.
Yes, a single token can be used for both access and governance, but combining roles often muddles incentives because buyers seeking governance influence are different from users buying to consume a service, and those mixed incentives can distort both functions.
Ask causal questions: what specific action does the token enable; why must that action be token-mediated rather than handled off‑chain; is the service already live; are buyers mainly acquiring tokens to consume now or to profit later; and how much issuer discretion exists over supply, pricing, or permissions?
U.S. regulators apply the Howey framework - analyzing whether there is an investment of money in a common enterprise with a reasonable expectation of profits from the efforts of others - and have said the presence of actual, usable consumption reduces the likelihood a token is a security, though no single factor is dispositive.
No; token standards like ERC‑20 only standardize how tokens move and how balances are queried - utility depends on the surrounding application logic that enforces what holding or spending the token actually entitles you to do.
Design failures fall into a few patterns: fake utility (the token isn’t needed), bad timing (tokens sold before usable service), and unstable incentives (tokens that must be both cheap to spend and valuable to reward providers); when a token’s economics depend more on market confidence than repeated consumptive use, the system becomes fragile, as illustrated by high‑profile collapses cited as cautionary examples.
Related reading