What is Tokenized Treasuries?
Learn what tokenized Treasuries are, how they work, why institutions use them, and the legal, operational, and market risks behind them.
Introduction
Tokenized Treasuries are blockchain-based representations of exposure to U.S. Treasury bills, notes, bonds, or Treasury-heavy cash vehicles. They matter because they sit at the junction of two very different systems: the traditional dollar safe-asset market and the onchain world, which values continuous trading, programmable settlement, and assets that can move at software speed.
That combination creates an obvious question. If U.S. Treasuries already trade in one of the deepest and most efficient markets in the world, why tokenize them at all? The answer is not that blockchains magically make Treasuries better as credit instruments. A Treasury is still valuable because the U.S. government owes the cash flows. Tokenization changes something narrower but still important: how claims on those cash flows are recorded, transferred, settled, and integrated with other digital systems.
Seen from first principles, tokenized Treasuries are not mainly about inventing a new asset. They are about changing the rails on which an existing asset, or exposure to it, can travel. That distinction explains both the promise and the confusion. Some products represent direct or near-direct interests in underlying securities. Others are fund shares that hold Treasuries. Others still are third-party wrappers or notes that only reference Treasury exposure. These structures can look similar on a wallet screen while being legally and operationally quite different.
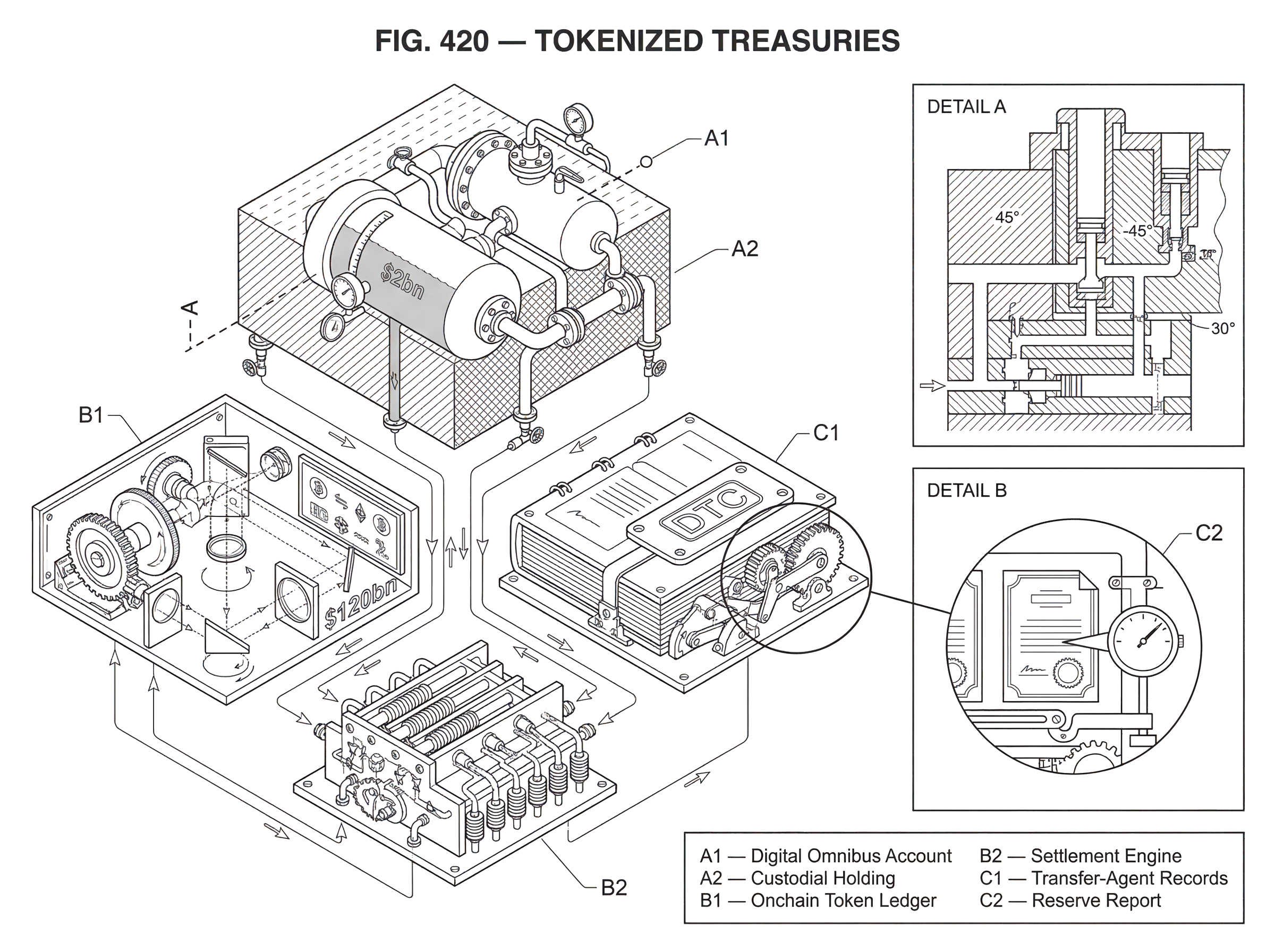
The practical stakes are larger than the current market size might suggest. Official review has described today’s tokenized Treasury fund market as still small, around $2bn, and mostly pilot-scale. At the same time, Treasury officials estimate roughly $120bn of stablecoin collateral is directly invested in Treasuries, which means the broader digital-asset ecosystem already has a meaningful Treasury connection even before full tokenization scales. Tokenized Treasuries are therefore best understood as part of a wider re-plumbing of cash, collateral, and settlement.
Which types of Treasury exposure are tokenized (direct securities, fund shares, or wrapped claims)?
| Model | Legal link | Onchain claim | Main risk | Best for |
|---|---|---|---|---|
| Direct registration | Direct on issuer books | Token = registered title | Operational/agent error | Highest legal certainty |
| Fund / account share | Beneficial via omnibus (DTC) | Token = fund share or entitlement | Indirect creditor exposure | Onchain fund liquidity |
| Third‑party wrapper | Issuer promise to token holders | Token = issuer note or wrapper | Bankruptcy / intermediary risk | Synthetic or bespoke exposure |
The core idea is straightforward: a token on a blockchain represents some claim related to U.S. Treasury exposure. But the phrase tokenized Treasury compresses several distinct possibilities, and most misunderstandings begin there.
At the most direct end, the token is meant to correspond to ownership of a security, with recordkeeping integrated so that moving the token updates the legally relevant ownership record. SEC staff describes this issuer-sponsored pattern as one in which the issuer or its agent integrates distributed ledger technology into the master securityholder file, so transfer on the crypto network results in transfer on the official record. In that model, the blockchain is not just a visual mirror. It is part of the ownership system.
A second pattern is less direct but common in practice: the token represents an interest in a fund or account that holds Treasuries. Franklin Templeton’s onchain government money fund and BlackRock’s BUIDL are examples often cited in official market reviews as part of today’s tokenized Treasury landscape. In these products, what sits onchain is typically not a specific Treasury bill with its own CUSIP traveling natively through a public blockchain. Instead, the token usually stands for a share or beneficial interest in a vehicle whose assets include Treasuries or Treasury-backed cash instruments.
A third pattern is a third-party wrapper. SEC staff distinguishes between securities tokenized by or on behalf of issuers and tokenized securities created by unaffiliated third parties. Those third-party products may be custodial claims, linked securities, or even synthetic exposures. Here the economic result may resemble Treasury exposure, but the holder may also face risks tied to the intermediary itself, including bankruptcy risk that a holder of the underlying Treasury would not necessarily face.
That is the first invariant worth remembering: a tokenized Treasury is only as direct as the legal and operational link between the token and the underlying asset. The token is not the Treasury merely because it references one. The mechanism that ties token balances to actual offchain holdings is what matters.
Why tokenize Treasuries if the traditional Treasury market is already efficient?
The puzzle is easier to resolve if we separate the underlying asset from the settlement environment around it. The Treasury market is already highly liquid, standardized, and deeply intermediated. So the case for tokenization is not that it will suddenly create a market where none existed. The case is that some activities around Treasuries may become cheaper, faster, or more programmable if claims can move on shared digital rails.
The clearest mechanism is atomic settlement. Treasury officials describe this as a process in which all parts of a transaction settle simultaneously across all parties, reducing settlement-failure risk. In ordinary markets, trade execution, collateral movement, and cash settlement often involve separate systems, messaging layers, cutoffs, and reconciliation steps. When an asset token and a payment token can move in one programmed transaction, the handoff becomes tighter: either both sides happen, or neither does.
That change matters most when Treasuries are not being bought simply to hold to maturity, but are being used as collateral, liquidity buffers, or programmable reserves. Smart contracts can automate movements of collateral after predefined events. Margining logic can react continuously rather than only during business hours. Treasury-like yield can be made available inside digital-asset venues without forcing investors to leave the onchain environment for every rebalance.
This is also why tokenized Treasuries are closely linked to stablecoins. A large share of stablecoin collateral is already invested in short-dated U.S. Treasuries. So there are really two related stories happening at once. One is Treasuries backing digital dollars. The other is Treasury exposure itself becoming natively usable in digital markets. The first creates demand for T-bills as reserve assets. The second tries to make those exposures tradable, transferable, and pledgeable in tokenized form.
Still, expected gains should not be overstated. The official Treasury market review is careful on this point: because the Treasury market is already efficient, many benefits will likely be incremental unless tokenization occurs on a sufficiently unified and interoperable ledger infrastructure. If every institution tokenizes in its own silo, some operational steps may become more modern without the market becoming much simpler overall.
How do tokenized Treasuries work in practice (mint/burn, omnibus accounts, and reconciliation)?
Mechanically, tokenized Treasuries usually rely on a simple discipline: immobilize or hold the underlying asset offchain, and mint only the corresponding onchain claims. This is how the system tries to prevent double counting.
A useful example comes from DTC’s tokenization pilot framework. The design does not put legal title to Treasury securities directly on a public blockchain in the first instance. Instead, DTC Participants can elect to have their security entitlements recorded using distributed ledger technology as Tokenized Entitlements, while legal title remains registered to Cede & Co. When a participant sends a conversion instruction, DTC debits the relevant securities from the participant’s ordinary account and credits them to a Digital Omnibus Account. Only then are corresponding tokens minted to the participant’s registered wallet.
The logic is important. If the original book-entry entitlement remained freely usable while the token also circulated, the system would have created two spendable claims on one asset. By moving the underlying position into an omnibus control account, the tokenized side and the traditional side are forced to reconcile to the same backing pool.
Now imagine the reverse direction. A participant wants to use the Treasury position again inside the traditional DTC environment. The token is returned and burned, and the underlying entitlement is moved back out of the omnibus account into the participant’s conventional account. Here the blockchain record is not standing alone; it is coupled to a centralized source of truth and a mint-burn discipline.
This same basic structure appears in many tokenized-asset systems even when the institutional names differ. An asset manager or custodian holds T-bills, notes, or Treasury fund shares. A tokenization platform mints tokens only against confirmed holdings. Redemptions burn tokens and release the corresponding offchain claim or cash. Everything depends on continuous reconciliation between the token supply and the assets held in custody.
That is why transparency and proof matter so much. A tokenized Treasury product needs some way to show that the quantity of tokens outstanding matches what is actually held. Sometimes this is done through transfer-agent-style records and official books. Sometimes through omnibus-account reconciliation. Sometimes through attestation or reserve-reporting designs. The exact method varies, but the economic requirement is the same: the token supply must stay anchored to verifiable backing.
Am I a direct owner, a beneficial owner, or a holder of a new security when I buy a tokenized Treasury?
Once the machinery is visible, the next question is what legal interest the holder actually has. Ondo’s policy roadmap lays out three pathways that are useful far beyond Ondo itself because they frame the whole design space.
The first is direct registration. Here the token corresponds to a holder’s direct legal interest on the issuer’s official books, typically through an issuer and transfer-agent system that treats onchain transfer as legally effective transfer. This is the cleanest conceptual version of tokenization because the token and the ownership record are tightly aligned.
The second is beneficial ownership, often linked to the existing DTC framework. In this model, the traditional issuer records and central securities depository structure remain in place. A book-entry position is moved to a control or omnibus account, and a corresponding token is minted. The token holder has an indirect beneficial interest rather than direct registered title. DTC’s pilot architecture fits this broad family.
The third is new security issuance. A party that holds underlying securities issues a new tokenized instrument that grants rights related to those holdings. This can be economically useful, but it is no longer merely a change in format. It is a new instrument with its own obligations, counterparty structure, and compliance consequences.
This distinction is not academic. It changes what breaks if something goes wrong. If the problem is a transfer-agent reconciliation error, that is different from a custodian shortfall. If the problem is bankruptcy of a third-party wrapper issuer, that is different from an error in recording beneficial ownership at a depository-linked intermediary. Two tokens may each claim to be “Treasury backed,” yet one may expose the holder mainly to sovereign risk while the other adds substantial intermediary risk on top.
Why are institutional tokenized Treasury systems often permissioned and subject to administrator controls?
A common intuition in crypto is that putting an asset onchain should mean fully open, permissionless circulation. But institutional tokenized Treasury designs often move in the opposite direction: registered wallets, approved blockchains, administrator powers, screening controls, and the ability to claw back or force-transfer tokens.
This is not an accident or a failure of imagination. It follows from the problem these systems are trying to solve. Treasury securities are embedded in legal, custody, sanctions-screening, reporting, and operational frameworks that large institutions already rely on. If the goal is not to create a censorship-resistant bearer asset but to make regulated securities move more efficiently, then the ledger is usually designed to preserve supervisory control and recoverability.
DTC’s framework is a concrete example. Participation is voluntary and limited to DTC Participants and their clients. Wallets must be registered. DTC performs checks on wallets and retains administrative rights over tokens, including adjustment, claw-back, and force-transfer powers. Its official books and records remain in offchain systems such as LedgerScan, even while token movements occur on approved blockchains.
This design sacrifices some of the purity of decentralized transfer, but it gains something institutions view as essential: operational control over error correction, compliance enforcement, and system resilience. The official Treasury review likewise notes that many policymakers and market participants favor permissioned or trusted ledger architectures for Treasury tokenization because of governance, scalability, and security concerns.
There is debate here. Some industry participants argue that public, permissionless chains can safely support tokenized securities if the legal link and control framework are well designed. Others are much more cautious. What is clear from the evidence is that widespread institutional adoption today is being built around controlled access and explicit governance, not around anonymous bearer-style transfer.
When do tokenized Treasuries deliver real efficiency gains (collateral, settlement, and programmability)?
| Use case | Primary benefit | When most valuable | Key limitation |
|---|---|---|---|
| Collateral movement | Automated collateral transfers | High-margin and repo flows | Requires legal enforceability |
| Atomic settlement | Simultaneous asset+payment | Complex multi‑party trades | Needs interoperable rails |
| Continuous trading | 24/7 transferability | Around‑the‑clock rebalancing | Offchain liquidity bottlenecks |
| Programmability | Automated triggers and margining | Dynamic collateral automation | Oracle and data dependence |
The strongest case for tokenized Treasuries appears when we focus on the frictions around use, not on the intrinsic value of the bond itself.
Consider collateral movement. In conventional systems, a Treasury position used as margin may pass through several institutions and messaging layers before everyone agrees who now controls it and when that control became final. If the collateral representation and the settlement asset both live in interoperable digital systems, transfers can be automated and synchronized. CFTC staff guidance on tokenized collateral reflects this attraction, encouraging efforts to focus on assets already eligible as regulatory margin, such as liquid assets with established haircuts. Treasuries fit that profile better than most assets.
Consider also time. Onchain systems run continuously. That does not eliminate every offchain dependency, but it can reduce dependence on batch windows and end-of-day cutoffs for some functions. DTC’s own service design allows free-of-value 24/7 movement of tokenized securities between registered wallets, even though those tokens initially do not receive collateral value or end-of-day settlement value within DTC’s traditional risk framework. That limitation matters, but so does the fact that the asset representation itself can circulate continuously.
Then there is programmability. Smart contracts can encode transfer restrictions, dividend or distribution logic, collateral triggers, and redemption conditions. That makes tokenized Treasuries attractive not only to asset managers but to venues building digital collateral markets. A Treasury-backed token can serve as a low-risk reserve asset within an onchain system in a way that ordinary offchain book-entry Treasuries cannot, because software can directly inspect balances and move them under defined conditions.
This is where neighboring ideas become relevant. Stablecoins need reserve assets. DeFi systems need high-quality collateral. Institutional treasury desks need ways to hold liquid instruments while remaining operationally connected to digital markets. Tokenized Treasuries exist because they are one of the few instruments that can plausibly satisfy all three needs at once: credit quality, liquidity, and digital portability.
What operational, legal, and reconciliation challenges matter after token issuance?
It is easy to focus on the visible act of token issuance. In reality, the difficult engineering lies in everything that must remain true after issuance.
The first requirement is reconciliation. The total onchain supply must always match the amount of underlying Treasury exposure actually set aside. If a conversion instruction fails halfway, if a burn is recorded onchain but not reflected offchain, or if a corporate action changes the underlying position, the system needs deterministic procedures for resolving the mismatch.
The second requirement is legal enforceability. CFTC staff emphasizes that tokenized collateral must be analyzed individually to ensure netting, collateral-interest, custody, and settlement-finality requirements are actually met. A token is easy to transfer technically. It is much harder to prove, under stress or in court, exactly what rights the holder has, how a security interest is perfected, and what happens if the intermediary fails.
The third requirement is operational resilience. DTC’s pilot architecture includes separation from key SCI systems, recovery objectives, limited touchpoints to centralized systems, and detailed quarterly reporting to regulators. These controls may look bureaucratic, but they reflect a real truth: once Treasuries become part of digital collateral chains, outages and reconciliation failures can have market consequences.
The fourth requirement is price and reserve integrity. If a tokenized fund share or Treasury-backed note is used in onchain systems, software may need timely net asset value, accrued yield, eligibility checks, and reserve confirmations. Secondary infrastructure such as oracles can therefore become part of the trust boundary. This is one reason tokenized Treasury systems often need more than a blockchain; they also need reliable data and reporting layers.
What are the main risks of tokenized Treasuries (intermediary, liquidity illusion, bridges, and keys)?
| Failure mode | Consequence | Mitigation |
|---|---|---|
| Intermediary risk | Loss from custodian or issuer default | Prefer direct registration; contractual protections |
| Liquidity illusion | Onchain liquidity not redeemable offchain | Align onchain/offchain windows; disclosure |
| Composability risk | Faster contagion and leverage | Limit composability; stress testing |
| Bridge / cross‑chain failure | Unauthorized minting; unbacked tokens | Avoid risky bridges; strict verification |
| Key management failure | Unauthorized transfers or theft | Threshold signatures; multi‑party custody |
The basic failure mode is simple: the token and the underlying asset drift apart. But that can happen through several different mechanisms.
One is intermediary risk. SEC staff warns that holders of third-party tokenized assets may face risks with respect to the third party, such as bankruptcy, that holders of the underlying security would not necessarily face. If your token is really a claim on an issuer who in turn holds Treasuries, then your exposure includes the structure around that issuer, not just the Treasuries.
Another is liquidity illusion. A token can trade 24/7, but the underlying Treasury market, money fund redemption process, or banking rails may not be equally continuous. In calm markets this mismatch may feel harmless. Under stress it matters. A tokenized claim may appear instantly liquid onchain while redemption into base money still depends on offchain windows, custodians, or counterparties.
Another is composability risk. The Treasury review notes that if tokenized markets grow large, composability and always-on trading could accelerate spillovers, leverage, and contagion. This is a different problem from credit risk. The Treasuries may remain high quality, but the ways they are used inside leveraged or automated structures can create new transmission channels for stress.
Cross-chain design adds an additional layer of fragility. Many teams are tempted to spread tokenized assets across multiple blockchains to reach more users and liquidity pools. But every bridge or wrapped representation creates another trust boundary. Bridge incidents show the danger clearly: if verification fails, unbacked tokens can be minted. Surveys of cross-chain hacks find that poor key management and lock-mint bridge designs have been major real-world sources of loss. For tokenized Treasuries, that means interoperability may increase convenience while simultaneously increasing the number of ways backing integrity can fail.
This is also where custody and key management become central. If minting, redemption, or reserve movement depends on a small set of operational keys, then the whole Treasury wrapper may be only as safe as that signing architecture. In threshold-signing systems, the goal is to remove single-key failure. A concrete real-world example is Cube Exchange’s 2-of-3 threshold signature scheme for decentralized settlement: the user, Cube Exchange, and an independent Guardian Network each hold one key share, no full private key is ever assembled in one place, and any two shares are required to authorize a settlement. The broader lesson for tokenized Treasury infrastructure is that key control is governance. Security often depends less on cryptographic branding than on who can actually authorize movement of assets or update critical contracts.
How does regulation change the treatment of tokenized Treasuries versus other crypto assets?
For many crypto-native assets, legal ambiguity is treated almost as part of the product. Tokenized Treasuries do not have that luxury. They are valuable precisely because they connect to an offchain asset with enforceable rights and established market conventions.
SEC staff’s position is conceptually simple: if the instrument is a security, changing the format to a crypto asset does not change the application of federal securities laws. Onchain versus offchain recordkeeping does not remove registration or compliance obligations. That sounds obvious, but it has an important consequence: tokenization is not a shortcut around the securities framework. It is an alternative technical format for instruments that remain legally regulated.
The same logic appears in derivatives and margin contexts. CFTC staff does not assume a tokenized asset remains eligible collateral merely because the underlying asset was eligible in conventional form. The tokenized structure itself must be examined for custody, legal enforceability, liquidity, and haircut appropriateness. In other words, regulators are not asking only, “Is this backed by Treasuries?” They are also asking, “What exactly is this instrument, and will it behave as expected under stress?”
This helps explain why pilot programs matter. DTC’s no-action relief is limited, conditional, and time-boxed. The service begins with narrow eligible assets, no collateral value in DTC risk management, and detailed reporting. That is how institutional tokenization is proceeding in practice: not through immediate full replacement of existing infrastructure, but through bounded experiments that preserve the old control structure while testing the new movement layer.
How do tokenized Treasuries bridge traditional dollar collateral and digital-market use cases?
The most important way to understand tokenized Treasuries is not as an isolated product category but as a bridge asset.
They connect traditional safe collateral to digital balance sheets. They let cash-management instruments appear inside blockchain-based systems without turning those systems entirely into bank deposits or stablecoins. They give investors a way to park value in something safer and yield-bearing than idle stablecoin balances, while remaining closer to onchain liquidity than a conventional brokerage account would allow.
That bridging role is why tokenized Treasuries keep appearing wherever digital-financial infrastructure becomes more serious. Asset managers want an onchain share class. Exchanges and prime brokers want programmable collateral. Stablecoin ecosystems want reserve transparency and yield-adjacent products. Market infrastructures such as DTCC and DTC want to test whether tokenized recordkeeping can coexist with established custody and settlement frameworks.
At the same time, the bridge metaphor explains the limits. Bridges inherit risks from both sides. From the Treasury side come settlement conventions, legal ownership questions, and existing market structure. From the blockchain side come smart-contract risk, key-management risk, oracle dependence, interoperability failures, and 24/7 market dynamics. Tokenized Treasuries succeed only if the bridge preserves the strengths of both systems without concentrating the weaknesses of each.
Conclusion
Tokenized Treasuries are digital representations of U.S. Treasury exposure carried on blockchain rails. Their purpose is not to reinvent the credit of the U.S. government, but to make Treasury-linked claims easier to transfer, settle, automate, and use as collateral inside digital systems.
The key thing to remember is this: the token matters less than the link. What defines a sound tokenized Treasury product is the quality of the connection between onchain balances and the real-world asset or entitlement underneath; legally, operationally, and technically. If that link is strong, tokenization can make a familiar safe asset newly useful. If that link is weak, the product may look like a Treasury while behaving like something much riskier.
What should an institutional allocator verify before taking exposure to tokenized Treasuries?
Before taking exposure, verify the token’s legal claim, custody arrangements, and operational controls; these determine whether you actually hold Treasury exposure or counterparty credit. Use Cube Exchange to centralize diligence and, when the instrument is tradable, to execute the exposure through standard funding and market flows.
- Request and review legal documentation that states whether the token conveys direct registration, beneficial ownership, or a new security, and note governing law and transfer-agent terms.
- Obtain and validate custody and reserve evidence: custody agreements, frequency and scope of attestations, omnibus-account controls, and the identity of the attestor or custodian.
- Confirm operational controls and key management: check wallet registration rules, any administrator powers (claw-back/force-transfer), and whether threshold-signing or multi‑party key custody is used.
- Verify regulatory and collateral status: confirm any limited pilot/no-action relief, whether the token is recognized for margin or collateral purposes, and applicable haircuts or settlement constraints.
- Execute the exposure on Cube Exchange: fund your Cube account in the settlement currency, open the token market or instrument, select an order type (limit for price control or market for immediacy), review fees and settlement instructions, and submit.
Frequently Asked Questions
Tokenized Treasuries can represent three distinct legal interests: direct registration (the token maps to your registered title on the issuer’s official books), beneficial ownership (the token represents an indirect claim via a depository/omnibus account such as DTC’s Tokenized Entitlements), or a new security (an issuer creates a separate tokenized instrument backed by Treasuries but with its own obligations). Which applies materially changes the holder’s rights and the intermediary risks they face.
Most institutional designs prevent double‑counting by immobilizing the off‑chain position (for example moving the book‑entry entitlement into a digital omnibus or custody account) and then minting on‑chain tokens against that set‑aside pool; redemptions burn tokens and return the underlying entitlement. DTC’s pilot and the article both describe this mint‑and‑burn plus omnibus control discipline as the core reconciliation mechanism.
Not automatically - regulators and market infrastructures require the tokenized structure itself to be analyzed for custody, enforceability, netting and liquidity before granting collateral or margin status, and DTC’s pilot explicitly does not give tokenized entitlements automatic collateral or end‑of‑day settlement value. CFTC and DTC guidance both make clear tokenized instruments must meet legal and operational tests before being treated as eligible collateral.
Institutional tokenized‑Treasury platforms are commonly permissioned because issuers and market infrastructures need operational controls for error correction, compliance screening, recoverability, and supervisor oversight; DTC’s service requires registered wallets and retains administrative powers like claw‑backs and forced transfers. These controls trade off some censorship resistance for legal and operational certainty that institutions and regulators favor.
Key failure modes include intermediary risk (holders exposed to the issuer or wrapper’s bankruptcy), liquidity illusion (on‑chain 24/7 trading can mask off‑chain redemption or settlement windows), composability/leverage amplification inside automated chains, and cross-chain bridge or key‑management failures that can enable unbacked minting or theft. The article and cited incident analyses (bridge hacks, Wormhole post‑mortem) highlight these specific risks.
Real efficiency gains show up in settlement and use cases: atomic settlement (simultaneous, programmatic exchange of tokenized asset and payment), continuous 24/7 movement for certain on‑chain actions, and programmability that automates collateral triggers, margining rules, or distribution logic - all of which reduce reconciliation and messaging frictions for collateral and onchain uses. These benefits are most meaningful when tokenization operates on interoperable rails rather than isolated silos.
Oracles, reserve attestations, and reconciliation systems are critical because the token supply must stay anchored to verifiable off‑chain holdings; failures in those layers (bad proofs, oracle outages, or bridge verification flaws) can create mismatches or allow unbacked tokens. The literature and incident postmortems cited in the evidence (e.g., bridge exploits) show these components are frequent sources of real loss or divergence.
No - tokenization changes the recordkeeping and transfer rails, not the underlying sovereign credit; a token does not make the U.S. government’s obligation any safer. The article stresses that the Treasury’s creditworthiness is unchanged and that the value of tokenization lies in how claims are recorded, transferred, settled, and integrated with digital systems, not in changing the bond’s intrinsic risk.
Related reading