What Is a Block Explorer?
Learn what a block explorer is, how it reads node data, indexes blocks and transactions, and why it matters for verification, analysis, and APIs.
Introduction
block explorer is the name for the software that makes blockchain data searchable, readable, and navigable. That sounds simple until you notice the underlying problem: blockchains are designed to be verifiable by machines, not pleasant for humans to inspect. A node can tell you that a transaction exists, that it was included in a block, that it emitted logs, or that an output was spent; but raw chain data is scattered across blocks, encoded in chain-specific formats, and exposed through low-level APIs. An explorer exists because verifiable is not the same thing as usable.
That is why explorers matter so much in practice. They are where users confirm a transfer actually landed, where developers inspect contract calls and emitted events, where researchers trace flows, and where operators monitor whether the network is healthy. They sit in an interesting middle layer: close enough to nodes to reflect on-chain truth, but opinionated enough to organize that truth into pages, search results, and APIs.
The key idea is this: a block explorer is not just a website showing blocks. It is an indexing system that continuously translates chain data into queryable views. Once that clicks, many details fall into place; why explorers need nodes, why they often maintain their own databases, why their results can be richer than a wallet UI, and why they can still be incomplete or misleading when they add labels, tags, or other context on top of raw chain data.
Why build a block explorer instead of querying the node directly?
A blockchain already stores its own history, so why build anything on top of it? Because the chain’s native data model is optimized for consensus and replay, not for ad hoc questions. If you ask a Bitcoin node, “show me everything this address has ever received and spent,” that is not a primitive the chain was designed around. If you ask an Ethereum node, “show me every token transfer involving this contract and decode the method names,” that requires stitching together blocks, transactions, receipts, and logs into a human-oriented answer.
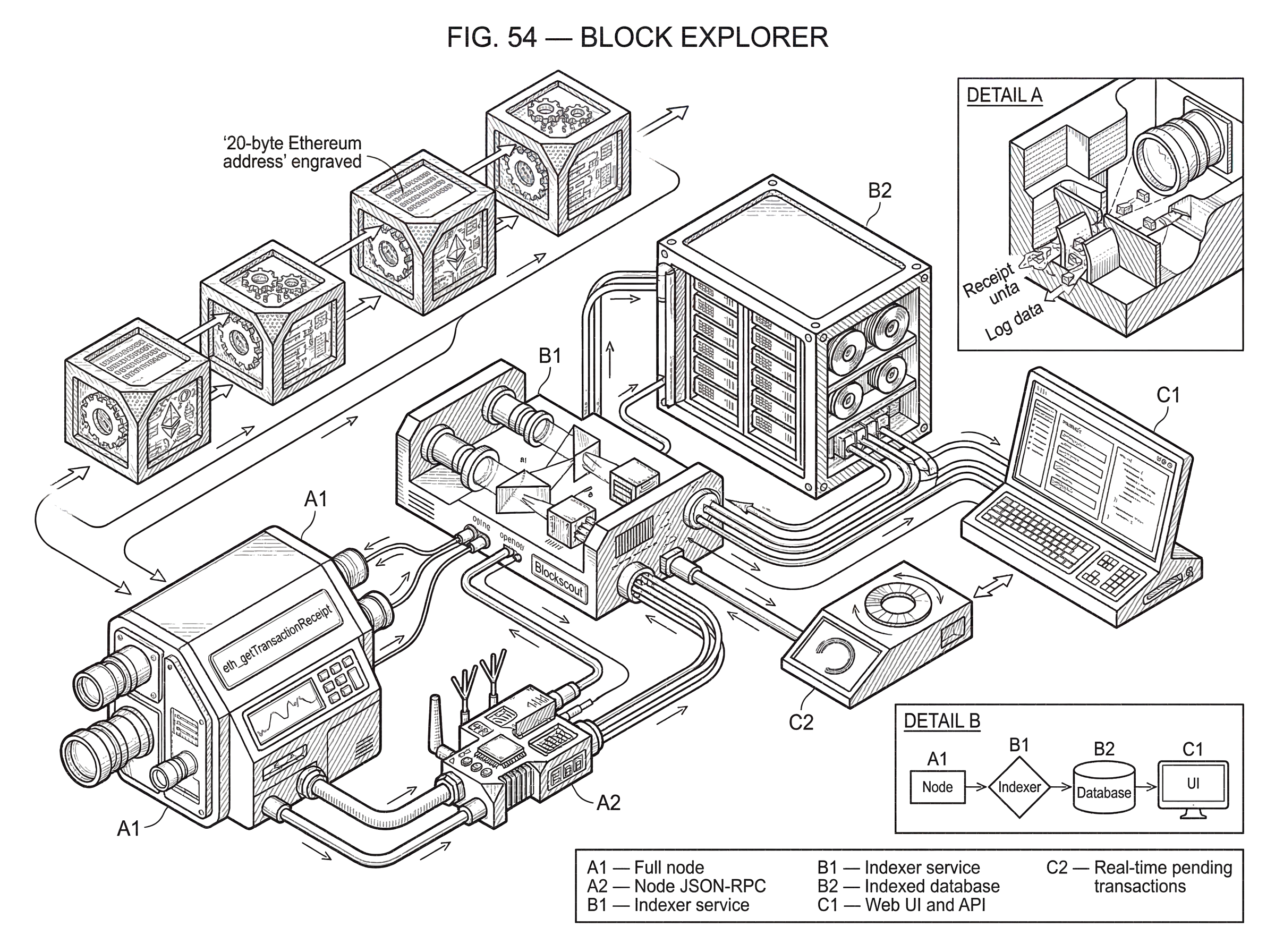
Here is the mechanism. Nodes expose interfaces such as Bitcoin Core RPC methods like getblock, getrawmempool, and getrawtransaction, or Ethereum JSON-RPC methods like eth_getBlockByNumber, eth_getTransactionByHash, eth_getTransactionReceipt, and eth_getLogs. Those methods are the raw reading surface. They let software fetch canonical chain objects or query recent state, but they do not by themselves provide the kind of indexed lookup people expect from a search engine. An explorer repeatedly calls or subscribes to these node interfaces, transforms the data into a structured database, and then serves that indexed data through a web UI or API.
That is why calling an explorer a “search engine for blockchain data” is more than a metaphor. Like a web search engine, it does not create the underlying content. It discovers, organizes, and ranks or formats it so queries become fast and intelligible. The analogy helps explain the job; it fails in one important way: unlike web pages, blockchain data has a strong notion of shared canonical history, so the explorer is usually trying to reflect a single network state rather than a messy open web of unrelated documents.
What node data and feeds does a block explorer consume?
At the foundation, an explorer reads from nodes. That dependency matters. The explorer is not independently deciding what happened on chain; it is consuming data from software that participates in or follows the network. On Bitcoin, the explorer may use Bitcoin Core’s RPC surface and possibly ZMQ notifications for live updates. On Ethereum, it may talk to an execution client such as Geth over JSON-RPC, using history methods for past blocks and filters or subscriptions for new blocks, pending transactions, and logs. On Solana, the same job may be done through validator-side streaming via Geyser plugins, which push accounts, transactions, slots, and blocks into external data stores.
This is the first distinction that trips people up: the explorer is usually not the blockchain client itself. Sometimes the same deployment bundles both roles together, but conceptually they are separate. The node maintains a view of the chain and exposes raw data. The explorer consumes that view and builds higher-level representations. Blockscout’s deployment model makes this separation explicit: it documents separate runtime modes for an indexer, a web UI, an API, or an all-in-one setup. That is not just a product detail; it reflects the architecture of explorers generally.
Once you see that split, the rest becomes easier to reason about. The node answers questions in the chain’s native terms. The explorer asks those questions repeatedly and stores the answers in a form optimized for different questions later. That is why explorers often have their own database even though the chain already exists. They are maintaining an index over chain data, not duplicating consensus for its own sake.
How does an explorer index blockchain data into searchable pages?
| Chain model | Primary objects | Event model | Receipt / outcome | Explorer outputs | Indexing challenge |
|---|---|---|---|---|---|
| UTXO (Bitcoin) | UTXOs, transactions, scripts | No native event logs | No receipts; infer from UTXOs | UTXO graph, spend/receive history | Linking spends and script decoding |
| Account (Ethereum) | Accounts, transactions, receipts | Logs/events emitted by contracts | Receipts include status and logs | Decoded calls and token transfers | Log-heavy indexing and ABI decoding |
| Solana account model | Accounts, slots, transactions | Account-change centric streams | No Ethereum-style receipts | Account deltas and program metadata | High throughput and ordering concerns |
The core mechanical step in an explorer is indexing. Indexing means walking through chain data as it arrives, extracting the pieces users care about, and writing them into tables or documents designed for quick retrieval.
On a UTXO chain such as Bitcoin, the explorer will ingest blocks and transactions, record transaction IDs, inputs, outputs, values, scripts, timestamps, confirmation state, and the relationships between outputs and later spending transactions. The chain itself cares that blocks are valid and outputs are spent at most once. The explorer adds the reverse links and summaries people want: which outputs remain unspent, which transaction spent a given output, how many confirmations a transaction has, what the mempool currently contains, and how recent blocks compare in size or fee pressure.
On an account-based chain such as Ethereum, the explorer ingests blocks, transactions, receipts, and logs. The crucial extra object here is the receipt: that is where the client exposes execution outcome, gas used, status, contract creation address, and emitted logs. If a user wants to know whether a contract call succeeded, the explorer is usually reading receipt data rather than inferring from the transaction alone. If the user wants token transfers or contract events, the explorer often gets there through eth_getLogs or equivalent indexed processing of receipts.
This is also where chain differences become visible. Bitcoin has no native concept of contract event logs, so an explorer for Bitcoin does not build the same event-centric interface as an Ethereum explorer. Solana’s account model and validator streams produce yet another style of indexing, often centered on account changes, slot progression, transaction metadata, and program-specific parsing. The point is not that every explorer shows the same fields. The point is that every explorer performs the same basic transformation: machine-native chain data becomes indexed human queries.
A worked example makes the mechanism concrete. Suppose you send ETH to a decentralized exchange contract and swap one token for another. Your wallet can show “submitted” and later maybe “confirmed,” but that is a narrow, app-specific interpretation. An explorer starts lower down. It sees the transaction hash appear, either through the mempool or after inclusion in a block. When the block arrives, it records the block number, sender, recipient contract, nonce, gas parameters, and input data. Then it fetches the receipt, which tells it whether execution succeeded and what logs were emitted. From those logs, the explorer can infer token transfers and display them as separate, human-readable effects of the transaction. If the contract source is verified, the explorer may further decode the function call and show the method name rather than only raw calldata. Nothing mystical happened here. The explorer did not “understand DeFi” in a general sense; it combined indexed transaction data, receipt data, logs, and optional verified metadata into a more legible narrative.
When should you trust a block explorer over a wallet view?
Users often notice that when something looks wrong, support asks for a transaction hash and tells them to check an explorer. That pattern exists for a structural reason. Wallets typically show a derived view tailored to the user’s assets and recent activity. They may depend on their own backend services, cache balances, hide failed attempts, or simplify edge cases. Explorers, by contrast, aim to show what was actually recorded on chain or what a node currently reports.
That does not mean explorers are infallible. It means they usually operate closer to the raw source of truth. If a wallet says your transfer is missing, the explorer may show that the transaction never propagated, is still pending, was dropped, or reverted after execution. If a wallet balance looks stale, the explorer may reveal that the wallet backend simply has not refreshed or is applying its own interpretation.
The important nuance is that an explorer is authoritative only about the data it truly derives from the chain or from nodes. As soon as it adds labels like “Binance 14,” “phishing,” or “sanctioned entity,” it is moving beyond pure chain data into curation. That can be extremely useful, but it is a different layer of truth.
How do explorers decode contracts and add labels or warnings?
Raw blockchain data is often too thin to answer the question users actually have. A transaction to a 20-byte Ethereum address tells you where it went, but not whether that address belongs to an exchange hot wallet, a bridge contract, or a scam. A call to a contract with opaque input bytes tells you what was executed at the byte level, but not which function name a human would recognize. Explorers bridge that gap by adding metadata.
Some metadata is relatively mechanical. Contract verification lets an explorer link deployed bytecode to published source code, so it can decode function signatures, constructor arguments, and ABI-structured inputs. Some metadata is social and curated. Etherscan, for example, documents public name tags, labels, and public notes that identify owners or purposes of addresses and categorize pages. It also notes that such tags are curated, can be incomplete, and may be revised or removed. That caveat matters because readers often slide from “this page has a label” to “this identity is proven.” Often it is not proven in the cryptographic sense; it is an explorer assertion backed by some policy and source material.
This is where explorers become more than neutral mirrors. They start to function as public directories, reputation systems, and risk surfaces. They may mark suspicious contracts, annotate sanctioned addresses, or flag notable entities. Those additions can make the chain legible to normal users, but they also introduce judgment calls, governance choices, and possible errors.
What infrastructure and pipeline do explorers need to run reliably?
| Component | Primary role | Bottleneck | Scaling method | Typical operator choice |
|---|---|---|---|---|
| Indexer | Ingests and indexes chain data | Node throughput and DB writes | Vertical sizing; DB tuning | Dedicated indexer process |
| API | Expose indexed data programmatically | Read traffic and rate limits | Caching; horizontal replicas | Rate-limited programmatic endpoints |
| Web UI | Human-facing pages and search | UI latency and cache misses | CDN and many replicas | Stateless UI servers |
To a casual user, an explorer looks like a website with a search bar. Operationally, it is closer to a pipeline.
First, it needs a chain data source. That might be its own full node, a cluster of nodes, a validator stream, or an upstream provider. Second, it needs an ingestion process that walks historical data and stays caught up with new data. Third, it needs storage tuned for the access patterns users actually want: transaction lookups by hash, address history queries, block pages, token transfer pages, event searches, and analytics. Finally, it needs serving layers such as a web app and APIs.
Blockscout’s separation of indexer, API, and web app is a clean illustration of those roles. The indexer consumes chain data and populates the database. The API exposes that indexed data programmatically. The web UI presents the same database to humans. These roles can run together or separately, and that matters because their bottlenecks differ. Indexing is limited by node throughput, parsing, and database write load. Serving a UI is limited more by read traffic and caching. An operator may therefore want one indexer writing to a shared database while multiple API or UI instances scale reads.
This also explains why explorers are hard to operate at large scale. The chain never stops moving. Re-indexing history is expensive. Rich features like decoded logs or token balances multiply storage and compute demands. And different chains stress different parts of the system. Ethereum event indexing can become log-heavy. Solana’s high throughput can push operators toward streamed externalization through Geyser because validators serving heavy RPC directly may fall behind.
A useful nearby concept is RPC. An explorer depends on RPC or equivalent node interfaces because that is how it obtains data in the first place. But an explorer is not just a thin RPC proxy. If every page request required live low-level RPC calls and chain-native recomputation, explorer performance would be poor and many higher-level queries would be impractical. The whole point of the explorer is to absorb that complexity ahead of time.
Why can an explorer's transaction status change after it appears?
| State | What it means | Data certainty | User signal | Explorer UI indicator |
|---|---|---|---|---|
| Pending | Seen in mempool or unfinalized head | Low certainty; may change | May be replaced, dropped, or reordered | Pending label or mempool tab |
| Latest / Confirmed | Included in newest block(s) | Medium certainty; reorg possible | Confirmation count indicates depth | Confirmation count shown |
| Finalized / Safe | Canonical finalized head | High certainty; unlikely reorg | Considered final for balances | Finalized or safe tag |
A smart reader might assume that once a transaction appears in an explorer, the answer is settled. That is only approximately true. Different chains expose different notions of pending, safe, confirmed, and finalized state.
Ethereum’s JSON-RPC explicitly distinguishes block tags such as latest, safe, finalized, and pending. That exists because there is a meaningful difference between the newest visible head and a more strongly confirmed state. Bitcoin has its own version of this problem through confirmations and the possibility of reorganization. Solana documentation for Geyser plugins even notes ordering subtleties around slot and transaction notifications, which indexers must handle carefully.
So the explorer must model time as well as data. A pending transaction may later disappear from the mempool, be replaced, or land with different relative ordering. A recently included transaction may sit in a block that is later orphaned or superseded. An account balance shown at one head may differ at a later finalized head. Good explorers communicate this through confirmation counts, pending tabs, safe/finalized indicators, and reorg-aware indexing logic.
This is one place where “explorers read directly from nodes” can mislead if stated too strongly. Yes, they are grounded in node data. But the node itself is exposing a moving view of network state, sometimes with explicit uncertainty. The explorer’s job is not just to read facts but to represent facts at the right stage of finality.
Why do multiple explorers exist and how do they differ?
If explorers are reading the same chain, why do multiple explorers exist? Because the chain supplies shared raw data, but explorers differ in what they index, how fast they update, what metadata they curate, what APIs they expose, and what business model they use.
Some are public and general-purpose, aimed at everyday lookups. Some are optimized for developers and offer powerful APIs. Some focus on contract verification, rich decoding, or multichain support. Some are self-hostable infrastructure, useful for teams that do not want to rely on a third-party explorer. The Graph shows a related but slightly different model: rather than a general explorer over every chain object, it offers indexing infrastructure where Graph Node serves indexed blockchain data through GraphQL queries, and Graph Explorer helps users discover public subgraphs. That is not a drop-in replacement for a canonical block explorer, but it reveals the same broad pattern: raw chain data becomes specialized query surfaces through indexing.
The existence of many explorers also matters for trust. If one explorer is stale, rate-limited, or applying questionable labels, users and developers can compare against another. Since the underlying chain is shared, disagreement between explorers often points to indexing lag, metadata choices, chain-specific parsing differences, or finality timing rather than different underlying history.
How do explorers affect privacy and deanonymization risk?
Explorers improve transparency, but they can reduce privacy in practice. Some of that loss is inherent to public chains: once addresses, transactions, and event logs are indexed and searchable, tracing becomes easier. Some of it is added by the web layer. Research on Web3 privacy has found that wallet addresses can leak to third parties, including JSON-RPC providers and explorer-related services, and that many such services may also collect IP addresses. The practical consequence is uncomfortable but important: a public chain only gives pseudonymity, and explorer infrastructure can make cross-context linkage easier.
There is another privacy tension inside explorer features themselves. Address labels, public notes, and public name tags help users understand the chain, but they also turn pseudonymous addresses into social objects. For investigations and safety, that can be valuable. For ordinary users who expected the address alone to conceal identity, it can be surprising.
So explorers sit at a tradeoff point. They make blockchains legible and auditable. They also make them easier to surveil, profile, and cluster. Neither side of that tradeoff is accidental; both follow from the same indexing power.
When do block explorers fail or show incomplete data?
The common misconception is that an explorer shows “everything on the blockchain.” In reality, it shows everything the explorer has chosen and managed to index, plus whatever context it knows how to decode.
If a chain exposes limited node APIs, if the operator runs a pruned rather than archival setup, if the explorer lags during heavy activity, or if metadata for a protocol is missing, the user experience becomes thinner. Pending transactions may be absent or delayed. Contract interactions may remain undecoded. Specialized protocols may look like raw bytes. chain reorganizations can temporarily create inconsistencies. And if the explorer depends on upstream infrastructure rather than its own nodes, upstream outages or policy changes can propagate into what users see.
Even the simplest search can hide assumptions. Address pages on one chain may represent a straightforward account history. On another, they may aggregate many token transfers inferred from logs rather than from balance state directly. A token page may rely on verified contract metadata and conventions rather than a universal chain primitive. The interface looks simple because the explorer hides those modeling choices.
That is why a good way to read explorer data is to ask: which parts are raw chain record, which parts are derived computation, and which parts are curated metadata? The transaction hash and block inclusion are usually raw. Confirmation counts and token transfer summaries are derived. Name tags and warnings are curated. Confusing those layers is how users give explorers either too little credit or too much.
Conclusion
A block explorer is the infrastructure that turns blockchain history from raw node output into searchable public knowledge. It exists because consensus data is not naturally organized for human questions, so explorers continuously ingest, index, decode, and serve that data through pages and APIs.
The memorable version is simple: nodes know the chain, explorers organize it. That is why explorers are indispensable for verification and analysis; and why their limits usually come from indexing choices, finality semantics, and the extra metadata they add on top of the chain itself.
How does this part of the crypto stack affect real-world usage?
Block explorers show what nodes report and how final a transaction is. Those details change whether you should fund, trade, or trust an on-chain event, so pair quick explorer checks with your Cube workflow before you move funds. Once the checks pass, use Cube to fund your account and execute trades on the correct network.
Frequently Asked Questions
A block explorer consumes the raw data a node exposes and builds an indexed, queryable view for humans and apps; the node maintains canonical chain state and exposes RPC/streaming methods while the explorer repeatedly reads those methods, transforms the data into its own database, and serves pages and APIs. Sometimes the two are bundled in one deployment, but conceptually they are separate roles.
Because blockchains are optimized for consensus and replay, not ad hoc lookups, explorers maintain their own databases to index blocks, transactions, receipts, and logs so queries like “everything this address received” can be answered quickly and in human-friendly form. The explorer’s database is an index over chain data rather than a second consensus store.
Explorers read transaction receipts (which include status, gas used, and emitted logs) to determine success or failure and use logs (eth_getLogs or similar) to infer token transfers and events; note receipts only exist after a transaction is included in a block, so pending transactions won’t have receipts yet.
Yes - labels, name tags, warnings, and AI-generated summaries are curated metadata layered on top of chain data and are not cryptographic proofs; explorers may document their sourcing or require public declarations for tags, but such annotations can be incomplete, revised, or wrong.
Explorers can disagree because they index different subsets of data, update at different speeds, use different node backends or sync modes, and apply different parsing or metadata policies; such disagreements often indicate indexing lag, metadata choices, or finality timing rather than two different blockchains.
Explorers must represent both data and finality: they surface pending transactions, confirmation counts, and finalized/safe indicators, and they implement reorg-aware indexing logic, but exact reorganization handling varies by implementation and the article notes it does not fully specify those mechanisms.
By making on-chain data searchable and adding indexes, explorers make tracing and linkage far easier than raw chain bytes alone; research shows wallets and third parties (including RPC providers and explorers) can collect addresses and telemetry that increase deanonymization risk, and public labels further reduce pseudonymity.
Operating an explorer at scale is resource-intensive because indexing is continuous, re-indexing history is expensive, rich decoding and token/event indexing multiplies storage and compute, and high-throughput chains may require validator-side streaming (e.g., Solana’s Geyser) rather than serving heavy RPC directly.
Indexing frameworks like The Graph provide a complementary model - developer-defined subgraphs exposed via GraphQL - so they are related but not a drop-in replacement for a general-purpose block explorer that aims to index every block/tx and present canonical pages; The Graph focuses on specialized, queryable subgraphs rather than a universal explorer UI.
Related reading